SAML authentication in a proxy policy
SAML user authentication can be used in explicit web proxies and transparent web proxies with the FortiGate acting as a SAML SP. SAML can be used as an authentication method for an authentication scheme that requires using a captive portal.
Topology
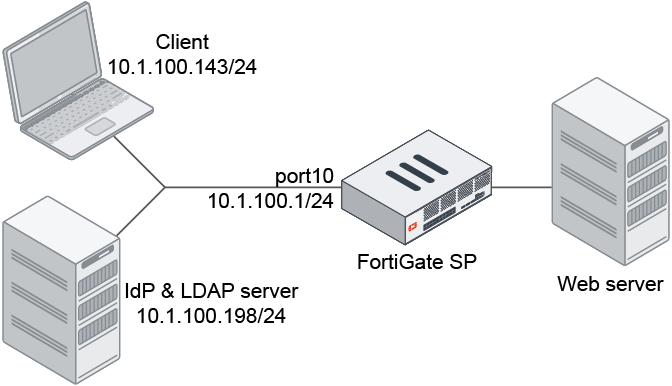
In this configuration, SAML authentication is used with an explicit web proxy. The IdP is a Windows 2016 server configured with ADFS. The LDAP and IdP servers are on the same server. The LDAP server is used as the user backend for the IdP to perform authentication; however, they are not required to be on the same server.
The authentication and authorization flow is as follows:

- The client opens a browser and visits https://www.google.com.
- The browser is redirected by the web proxy the captive portal.
- The request is redirected to the IdP's sign-in page.
- If the user signs in, the IdP authenticates the user and sends back a SAML assertion message to the FortiGate with the user group information.
- If the FortiGate authentication scheme has a user database configured, the FortiGate will query the LDAP server for the user group information and ignore the user group information from the SAML message.
- The user group information is returned. The FortiGate matches the user group information against the LDAP group in the proxy policy group settings. If there is a match, the request is authorized and the proxy policy is matched.
- If all policy criteria match successfully, then the webpage is returned to the client.
To configure SAML authentication with an explicit web proxy:
- Enable the web proxy:
config web-proxy explicit set status enable set http-incoming-port 8080 end - Enable the proxy captive portal:
config system interface edit "port10" set vdom "vdom1" set ip 10.1.100.1 255.255.255.0 set allowaccess ping https ssh snmp http telnet set type physical set explicit-web-proxy enable set explicit-ftp-proxy enable set proxy-captive-portal enable set snmp-index 12 next end - Configure the LDAP server:
config user ldap edit "ldap-10.1.100.198" set server "10.1.100.198" set cnid "cn" set dn "dc=myqalab,dc=local" set type regular set username "cn=fosqa1,cn=users,dc=myqalab,dc=local" set password ************ set group-search-base "dc=myqalab,dc=local" next end - Configure the user group:
config user group edit "ldap-group-saml" set member "ldap-10.1.100.198" next end - Configure SAML:
config user saml edit "saml_user" set cert "Fortinet_CA_SSL" set entity-id "https://fgt9.myqalab.local:7831/XX/YY/ZZ/saml/metadata/" set single-sign-on-url "https://fgt9.myqalab.local:7831/XX/YY/ZZ/saml/login/" set single-logout-url "https://fgt9.myqalab.local:7831/XX/YY/ZZ/saml/logout/" set idp-entity-id "http://MYQALAB.LOCAL/adfs/services/trust" set idp-single-sign-on-url "https://myqalab.local/adfs/ls" set idp-single-logout-url "https://myqalab.local/adfs/ls" set idp-cert "REMOTE_Cert_4" set digest-method sha256 set adfs-claim enable set user-claim-type name set group-claim-type group next end - Configure the authentication scheme, rule, and setting:
config authentication scheme edit "saml" set method saml set saml-server "saml_user" set user-database "ldap-10.1.100.198" next endconfig authentication rule edit "saml" set srcaddr "all" set active-auth-method "saml" next endconfig authentication setting set captive-portal "fgt9.myqalab.local" end - Configure the proxy policy:
config firewall proxy-policy edit 3 set proxy explicit-web set dstintf "port9" set srcaddr "all" set dstaddr "all" set service "webproxy" set action accept set schedule "always" set logtraffic all set groups "ldap-group-saml" set utm-status enable set profile-protocol-options "protocol" set ssl-ssh-profile "deep-custom" set av-profile "av" next endWhen a user goes to www.google.com in a browser that is configured to use the FortiGate as a proxy, the IdP sign-in page appears.

Sample log
7: date=2021-03-16 time=21:11:19 eventtime=1615954279072391030 tz="-0700" logid="0000000010" type="traffic" subtype="forward" level="notice" vd="vdom1" srcip=10.1.100.143 srcport=53544 srcintf="port10" srcintfrole="undefined" dstcountry="United States" srccountry="Reserved" dstip=173.194.219.99 dstport=443 dstintf="port9" dstintfrole="undefined" sessionid=1751272387 service="HTTPS" wanoptapptype="web-proxy" proto=6 action="accept" policyid=3 policytype="proxy-policy" poluuid="052ae158-7d40-51eb-c1d8-19235c4500c2" trandisp="snat" transip=172.16.200.1 transport=14844 duration=268 user="test1@MYQALAB.local" group="ldap-group-saml" authserver="ldap-10.1.100.198" wanin=345633 rcvdbyte=345633 wanout=13013 lanin=5098 sentbyte=5098 lanout=340778 appcat="unscanned"

