Results
The following sections show the function of the FortiGate and specifically of secure SD-WAN with respect to DSCP tagged traffic steering, and can be used to confirm that it is setup and running correctly:
- Verifying the DSCP tagged traffic on FortiGate
- Verifying service rules
- Verifying traffic steering as per the defined SD-WAN rules
- Verifying steered traffic leaving the required interface
Verifying the DSCP tagged traffic on FortiGate
To verify the incoming DSCP tagged traffic, we used packet sniffing and converting the sniffed traffic to a desired format. For more information about packet sniffing, see Using the FortiOS built-in packet sniffer on the Fortinet Knowledge Base.
For VoIP traffic that is marked with DSCP tag 0x70:
# diagnose sniffer packet any '(ip and ip[1] & 0xfc == 0x70)' 6 0 l
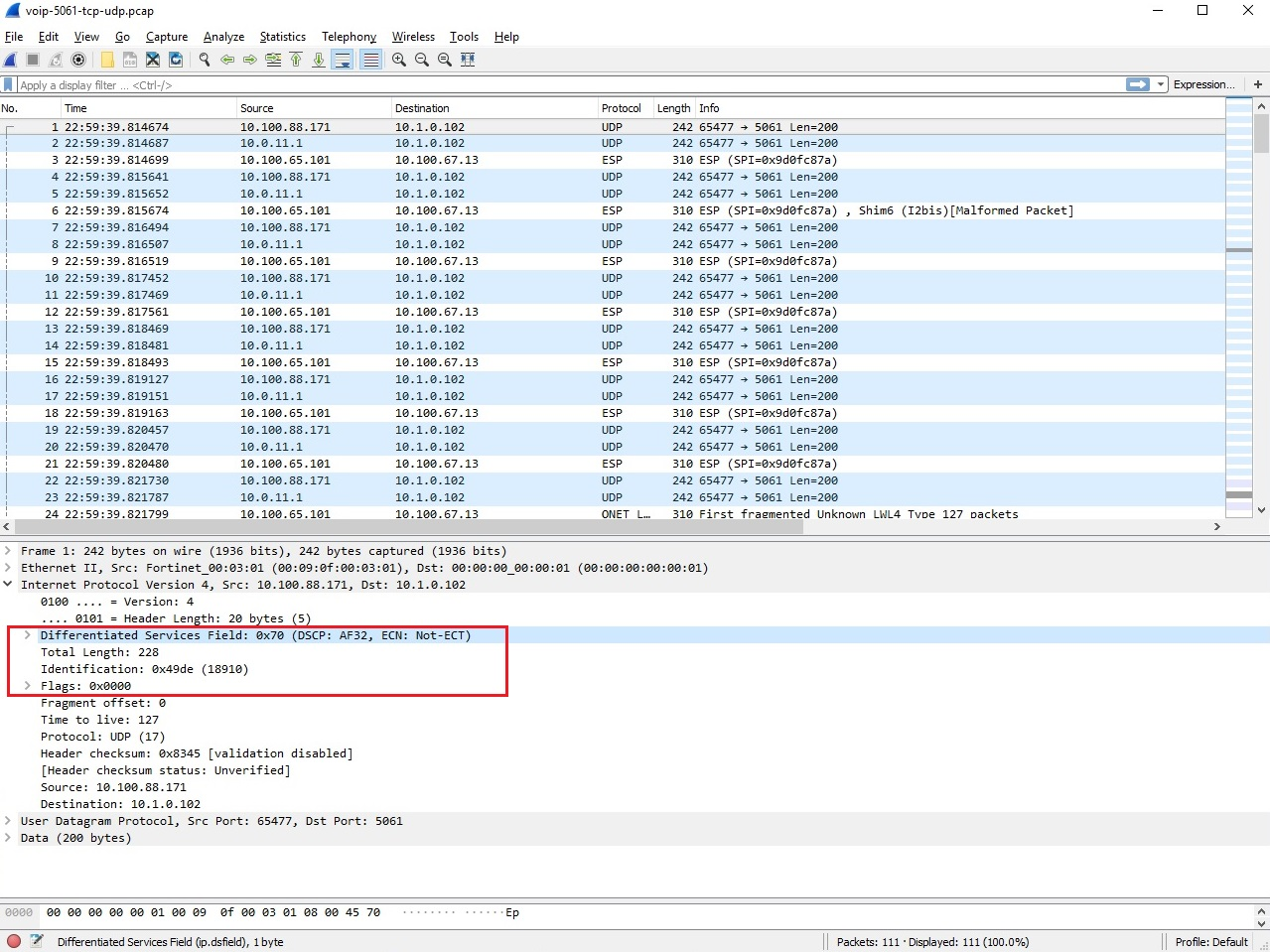
We used the open-source packet analyzer Wireshark to verify that VoIP traffic is tagged with the 0x70 DSCP tag.
For web traffic marked with DSCP tag 0x30:
# diagnose sniffer packet any '(ip and ip[1] & 0xfc == 0x30)' 6 0 l
We used the open-source packet analyzer Wireshark to verify that web traffic is tagged with the 0x30 DSCP tag.

Verifying service rules
The following CLI commands show the appropriate DSCP tags and the corresponding interfaces selected by the SD-WAN rules to steer traffic:
# diagnose sys sdwan service
Service(5): Address Mode(IPV4) flags=0x0
Gen(1), TOS(0x70/0xf0), Protocol(0: 1->65535), Mode(manual)
Members:
1: Seq_num(4 Branch-HQ-B), alive, selected
Dst address:
0.0.0.0-255.255.255.255
Service(3): Address Mode(IPV4) flags=0x0
Gen(1), TOS(0x30/0xf0), Protocol(0: 1->65535), Mode(manual)
Members:
1: Seq_num(2 port5), alive, selected
Dst address:
0.0.0.0-255.255.255.255
Service(2): Address Mode(IPV4) flags=0x0
Gen(1), TOS(0x0/0x0), Protocol(0: 1->65535), Mode(sla), sla-compare-order
Members:
1: Seq_num(1 port1), alive, sla(0x1), cfg_order(0), cost(0), selected
2: Seq_num(2 port5), alive, sla(0x1), cfg_order(1), cost(10), selected
Dst address:
0.0.0.0-255.255.255.255
Verifying traffic steering as per the defined SD-WAN rules
Go to Network > SD-WAN and select the SD-WAN Rules tab to review the Hit Count on the appropriate SD-WAN interfaces.

Verifying steered traffic leaving the required interface
Go to Dashboard > Top Policies to confirm that web traffic (port 443) flows through the right underlay interface members, and VoIP traffic flows through the right overlay interface member.
Web traffic leaves either Interface_A(port1) or Interface_B(port5):

VoIP traffic leaves the preferred VPN_B_Tunnel(Branch-HQ-B) interface:


