FortiClient as dialup client
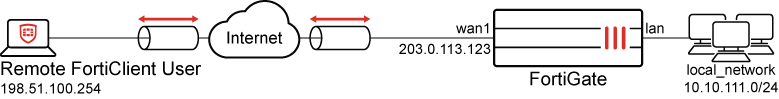
When FortiGate is configured as a dial-up VPN server, remote FortiClient users with dynamic or unknown IP addresses can establish secure connections over the Internet to access private resources protected by FortiGate.
|
|
This topic demonstrates using the Remote Access template to configure FortiClient as a dialup client. The FortiClient Secure Internet Access (SIA) template for the VPN Wizard also enables the GUI configuration of a remote access IPsec VPN to ensure all FortiClient traffic is routed through the FortiGate IPsec VPN tunnel for security inspection. For more information, see Configure FortiClient SIA for IPsec VPN tunnels. |
Example
In this example, the FortiGate protects a local network (10.10.111.0/24) that a remote FortiClient user needs to securely access over the Internet using a VPN connection. The FortiGate is configured as a dialup VPN server on wan1, and the FortiClient is the dialup IPsec VPN client.
This example uses IKE version 1. For remote user authentication, a local user is configured to be a part of a local user group on the FortiGate. After completing the initial tunnel configuration using VPN Wizard, the VPN mode is switched to use Aggressive mode so that the FortiGate can utilize Peer IDs for selecting a specific IPsec tunnel when multiple dial-up IPsec tunnels are configured on the same WAN interface.
|
|
In IKE version 1 Aggressive mode, FortiGate utilizes peer IDs as unique identifiers to distinguish and manage multiple dialup tunnels configured on the same WAN interface. During the IPsec negotiation process, FortiClient transmits its configured Local ID, which FortiGate matches against the defined peer IDs to identify the appropriate tunnel. The local ID configured on FortiClient must align with the corresponding peer ID set on FortiGate to successfully establish an IPsec tunnel. |
|
|
Starting with FortiClient 7.4.4, IKEv1 is no longer supported on the client. Therefore, plan accordingly when choosing your IKE version. Use IKEv2 if you plan on deploying FortiClient 7.4.4 and later. Also, FortiClient 7.4.4 does not support IPv6. |
To configure IPsec VPN with FortiClient as the dialup client in the GUI:
-
Configure a local user:
-
Go to User & Authentication > User Definition and click Create New.
-
Set the User Type to Local User, then click Next.
-
Set the Login Credentials, then click Next:
-
Username: vpnuser1
-
Password: Enter a suitable password
-
-
Disable Two-factor Authentication, then click Next.
-
Set User Account Status to Enabled and disable User Group, then click Submit.
-
-
Configure a local user group:
-
Go to User & Authentication > User Groups and click Create New.
-
Configure the following:
Field
Value
Name
vpngroup
Type
Firewall
Members
vpnuser1
-
Click OK.
For other types of authentication, such as LDAP, PKI, or SAML, see User & Authentication.
-
-
Go to VPN > VPN Wizard.
-
Enter a name for the VPN in the Tunnel name field. In this example, for_client
-
Set Select a template to Remote Access.
-
Click Begin.
-
Configure the VPN tunnel settings:
Field
Value
VPN client type
FortiClient
Authentication method
Pre-shared key
Pre-shared key
Enter a suitable key.
The same pre-shared key is used by the remote user on the FortiClient to connect to the dialup VPN.
IKE
Version 1
NAT traversal
Enable
Set Keepalive frequency to 10.
User authentication method
Phase 1 interface
Select vpngroup from the drop-down list.
Optionally, if you have multiple user groups configured, select Inherit from policy and then specify the groups. See Using single or multiple user groups for user authentication for details.
DNS Server
Use System DNS
Enable IPv4 Split Tunnel
Enable
-
Click Next.
-
Configure the Remote Endpoint settings:
Field
Value
Addresses to assign to connected endpoints
10.10.2.1-10.10.2.200
Subnet for connected endpoints
255.255.255.255
Security posture gateway matching Disable EMS SN verification Disable Save password
Enable
Auto Connect
Disable
Always up (keep alive)
Disable
-
Click Next.
-
Configure the Local FortiGate settings:
Field
Value
Incoming interface that binds to tunnel
wan1
Disable Create and add interface to zone.
Local interface
lan
Local address
local_network
Click + to create a new address object with Type set to Subnet and IP/Netmask set to 10.10.111.0/24, if not already configured.
-
Click Next.
-
Review the configuration and, if everything is correct, click Submit.
- Go to VPN > VPN Tunnels and edit the for_client VPN.
- On the Tunnel Settings tab, under Authentication, set Accepted peer ID to Specific peer ID.
- Set Peer ID to dialup1.
- Click OK.
|
|
The DNS suffix can be configured in the phase 1 configuration using the command |
To configure IPsec VPN with FortiClient as the dialup client in the CLI:
-
Configure a local user:
config user local edit "vpnuser1" set type password set passwd ****** next end -
Configure a local user group:
config user group edit "vpngroup" set member "vpnuser1" next end -
Configure the internal interface.
The LAN interface connects to the corporate internal network. Traffic from this interface routes out the IPsec VPN tunnel. Creating an address group for the protected network behind this FortiGate causes traffic to this network group to go through the IPsec tunnel.
config system interface edit "lan" set vdom "root" set ip 10.10.111.1 255.255.255.0 next endconfig firewall address edit "local_subnet_1" set subnet 10.10.111.0 255.255.255.0 next endconfig firewall addrgrp edit "local_network" set member "local_subnet_1" next end -
Configure the WAN interface.
The WAN interface is the interface connected to the ISP. It can be configured in static mode (as shown here), DHCP, or PPPoE mode. It is recommended to configure it with a static IP address to ensure that the IPsec VPN configuration on the on the FortiClient stays unchanged if the WAN IP changes on the FortiGate. The IPsec tunnel is established over the WAN interface.
config system interface edit "wan1" set vdom "root" set ip 203.0.113.123 255.255.255.0 next end -
Configure the client address pool.
You must create a firewall address to assign an IP address to a client from the address pool.
config firewall address edit "client_range" set type iprange set comment "VPN client range" set start-ip 10.10.2.1 set end-ip 10.10.2.200 next end -
Configure the IPsec phase1-interface.
PSK is used as the authentication method in this example. Signature authentication is also an option.
config vpn ipsec phase1-interface edit "for_client" set type dynamic set interface "wan1" set mode aggressive set peertype one set peerid "dialup1" set net-device enable set mode-cfg enable set proposal aes128-sha256 aes256-sha256 aes128-sha1 aes256-sha1 set dpd on-demand set dpd-retryinterval 20 set xauthtype auto set authusrgrp "vpngroup" set assign-ip-from name set ipv4-name "client_range" set dns-mode auto set ipv4-split-include "local_network" set save-password enable set psksecret ***** next end -
Configure the IPsec phase2-interface:
config vpn ipsec phase2-interface edit "for_client" set phase1name "for_client" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 next end -
Configure a firewall policy to allow client traffic flow over the IPsec VPN tunnel to the FortiGate’s lan interface:
config firewall policy edit 1 set name "inbound" set srcintf "for_client" set dstintf "lan" set srcaddr "client_range" set dstaddr "local_network" set action accept set schedule "always" set service "ALL" next end
|
|
One or more user groups for user authentication can be configured under a single IPsec VPN tunnel. See Using single or multiple user groups for user authentication for details. |
To configure FortiClient:
-
In FortiClient, go to Remote Access and click Add a new connection.
-
Set VPN to IPsec VPN and specify a Connection Name.
-
Set Remote Gateway to the FortiGate wan1 IP address.
-
Set Authentication Method to Pre-Shared Key and enter the key.
-
Expand Advanced Settings > Phase 1 and set Local ID to dialup1.
-
Configure the remaining settings as needed, then click Save.
-
Go to the Remote Access tab, select the VPN, enter the username and password, then clickConnect.
|
|
To establish an IPsec tunnel, the Phase 1 and Phase 2 configurations of the dial-up IPsec VPN on FortiGate must precisely match the corresponding settings on FortiClient. |
To verify the tunnel status in the GUI:
-
On the FortiGate, go to Dashboard > Network and expand the IPsec widget.
-
Find the new tunnel, for_client_0 in this example, and check the statuses of the Phase 1 and Phase 2 selectors.

Successfully established dialup IPsec VPN tunnels are displayed using a parent name followed by an index, creating a structured and organized association with the parent tunnel. For example, the parent name for_client results in tunnel names such as for_client_0, for_client_1, and so on.
-
Hover the cursor over the tunnel name to see additional details.
To verify the tunnel status in the CLI:
-
Verify the IPsec Phase 1 tunnel status on the FortiGate:
FortiGate# diagnose vpn ike gateway list name for_client_0 vd: root/0 name: for_client_0 version: 1 interface: wan1 15 addr: 203.0.113.123:4500 ->198.51.100.254:64916 created: 37s ago xauth-user: vpnuser1 assigned IPv4 address: 10.10.2.1/255.255.255.255 nat: me peer IKE SA: created 1/1 established 1/1 time 10/10/10 ms IPsec SA: created 1/1 established 1/1 time 0/0/0 ms id/spi: 1 b40a32d878d5e262/8bba553563a498f4 direction: responder status: established 37-37s ago = 10ms proposal: aes256-sha256 key: f4ad7ec3a4fcfd09-787e2e9b7bceb9a7-0dfa183240d838ba-41539863e5378381 lifetime/rekey: 86400/86092 DPD sent/recv: 00000000/00000a0e
Note that FortiGate acts as the responder, establishes the IPsec tunnel with remote FortiClient user with IP 198.51.100.254 over UDP NAT-T port 4500 on its wan1 interface, and dynamically assigns a VPN IP of 10.10.2.1 to FortiClient endpoint. The authenticated username is also displayed in
xauth-userfield. -
Verify the IPsec Phase 2 tunnel status on the FortiGate:
FortiGate # diagnose vpn tunnel list name for_client_0 list all ipsec tunnel in vd 0 ------------------------------------------------------ name=for_client_0 ver=1 serial=3 203.0.113.123:4500->198.51.100.254:64916 tun_id=198.51.100.254 bound_if=15 lgwy=static/1 tun=intf/0 mode=dial_inst/3 encap=none/984 options[03d8]=npucreate_dev no-sysctlrgwy-chgrport-chg frag-rfcaccept_traffic=1 parent=for_client index=0 proxyid_num=1 child_num=0 refcnt=12 ilast=3 olast=3 ad=/0 stat: rxp=1 txp=0 rxb=16402 txb=0 dpd: mode=on-idle on=1 idle=20000ms retry=3 count=0 seqno=0 natt: mode=keepalive draft=32 interval=10 remote_port=64916 proxyid=for_client proto=0 sa=1 ref=2 serial=1 add-route src: 0:0.0.0.0-255.255.255.255:0 dst: 0:10.10.2.1-10.10.2.1:0 SA: ref=4 options=2a6 type=00 soft=0 mtu=1422 expire=42867/0B replaywin=2048 seqno=1 esn=0 replaywin_lastseq=00000001 itn=0 life: type=01 bytes=0/0 timeout=43189/43200 dec: spi=36274d14 esp=aes key=16 e518b84b3c3b667b79f2e61c64a225a6 ah=sha1 key=20 9cceaa544ed042fda800c4fe5d3fd9d8b811984a enc: spi=8b154deb esp=aes key=16 9d50f004b45c122e4e9fb7af085c457c ah=sha1 key=20 f1d90b2a311049e23be34967008239637b50a328 dec:pkts/bytes=1/16330, enc:pkts/bytes=0/0 npu_flag=02 npu_rgwy=198.51.100.254 npu_lgwy=203.0.113.123 npu_selid=0 dec_npuid=2 enc_npuid=0 ------------------------------------------------------ name=for_clientver=1 serial=2 203.0.113.123:0->0.0.0.0:0 bound_if=15 lgwy=static/1 tun=intf/0 mode=dialup/2 encap=none/536 options[0218]=npucreate_dev frag-rfcaccept_traffic=1 proxyid_num=0 child_num=1 refcnt=11 ilast=350 olast=350 ad=/0 stat: rxp=0 txp=0 rxb=0 txb=0 dpd: mode=on-idle on=0 idle=20000ms retry=3 count=0 seqno=0 natt: mode=none draft=0 interval=0 remote_port=0Note the decryption, encryption, and authentication keys negotiated in Phase 2 to protect subnets under the
srcanddstfields. FortiOS also automatically adds the dynamically assigned VPN IP of 10.10.2.1 to its traffic selectors for dialup tunnel for_client_0.
To verify traffic through the IPsec tunnel:
-
On the remote FortiClient user with IP 198.51.100.254, initiate ICMP traffic to a machine in the 10.10.111.0/24 network and verify that traffic goes through:
# ping 10.10.111.3 PING 10.10.111.3 (10.10.111.3) 56(84) bytes of data. 64 bytes from 10.10.111.3: icmp_seq=1 ttl=62 time=9.84 ms 64 bytes from 10.10.111.3: icmp_seq=2 ttl=62 time=0.808 ms
-
On FortiGate, run a sniffer trace for ICMP packets destined to 10.10.111.3:
# diagnose sniffer packet any 'host 10.10.111.3’ 4 0 l Using Original Sniffing Mode interfaces=[any] filters=[host 10.10.111.3] 2024-11-05 12:06:05.509711 for_client_0 in 10.10.2.1 -> 10.10.111.3: icmp: echo request 2024-11-05 12:06:05.509791 lan out 10.10.2.1 -> 10.10.111.3: icmp: echo request 2024-11-05 12:06:05.518809 lan in 10.10.111.3 -> 10.10.2.1: icmp: echo reply 2024-11-05 12:06:05.518899 for_client_0 out 10.10.111.3 -> 10.10.2.1: icmp: echo reply
The ICMP request packets are received on for_client_0 tunnel interface and routed to the lan interface. ICMP reply packets are received on the lan interface and routed back out on for_client_0 tunnel interface.
For more information, see Performing a sniffer trace or packet capture.
-
Optionally, run real time IKE debug using appropriate filters for troubleshooting if the IPsec tunnel does not come up:
FortiGate # diagnose vpn ike log filter rem-addr4 198.51.100.254 FortiGate # diagnose debug application ike -1 FortiGate # diagnose debug enable
For more information, see VPN IPsec troubleshooting.

