Post-Quantum Cryptography for IPsec key exchange
IPsec key exchange supports Post-Quantum Cryptography (PQC) to enhance security with algorithms that protect against quantum computer attacks. This update ensures future-proof encryption and addresses vulnerabilities in traditional methods, aligning with upcoming security standards.
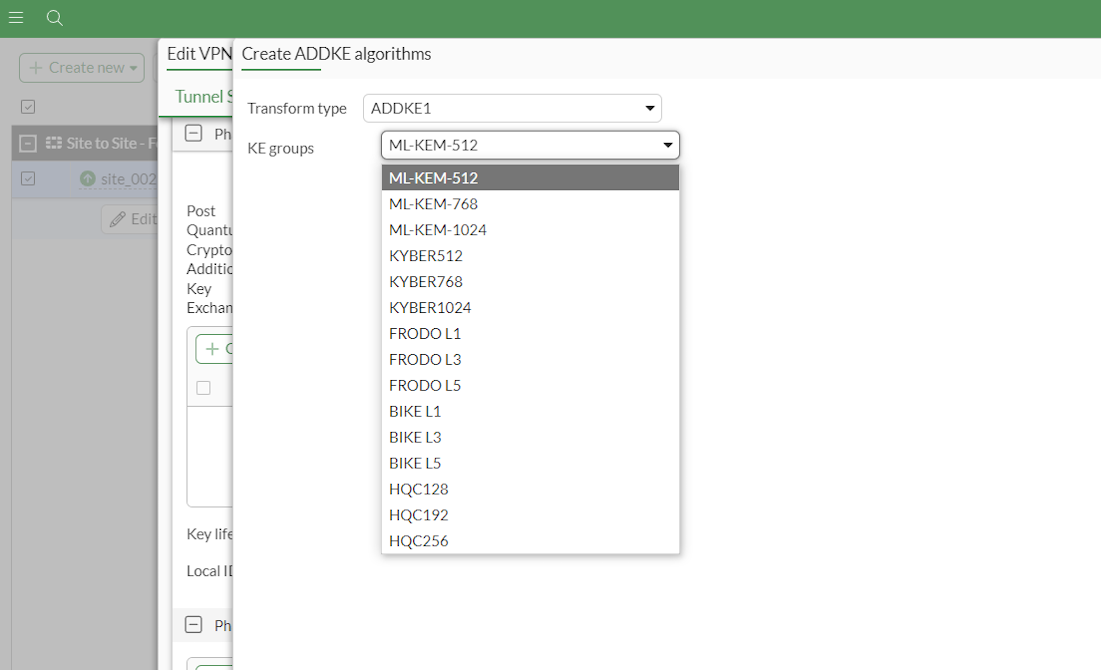
FortiOS allows users to specify various KE groups; however, only the following KE groups are standardized by NIST and are FIPS 203 compliant:
-
ML-KEM-512
-
ML-KEM-768
-
ML-KEM-1024
FIPS 203, also known as the Module-Lattice-Based Key-Encapsulation Mechanism (ML-KEM) Standard, is a set of guidelines established by the National Institute of Standards and Technology (NIST). These guidelines specify the use of lattice-based cryptographic algorithms for key encapsulation mechanisms, which are crucial for secure communication in various applications.
The three parameter sets offer different levels of security and performance:
| ML-KEM-512 | Provides a balance between security and efficiency, suitable for environments where moderate security is sufficient. |
| ML-KEM-768 | Offers a higher level of security compared to ML-KEM-512, making it suitable for more sensitive applications. |
| ML-KEM-1024 | Delivers the highest level of security among the three, ideal for highly sensitive data and critical applications. |
See FIPS203 and Module-Lattice-Based Key-Encapsulation Mechanism Standard for more information.
CLI configuration
The following commands can be used to enable and configure PQC:
config vpn ipsec phase1-interface
edit <name>
set addke1 <option1>, <option2>, <option3>
set addke2 <option1>, <option2>, <option3>
set addke3 <option1>, <option2>, <option3>
set addke4 <option1>, <option2>, <option3>
set addke5 <option1>, <option2>, <option3>
set addke6 <option1>, <option2>, <option3>
set addke7 <option1>, <option2>, <option3>
set childless-ike enable
next
end
config vpn ipsec phase2-interface
edit <name>
set addke1 <option1>, <option2>, <option3>
set addke2 <option1>, <option2>, <option3>
set addke3 <option1>, <option2>, <option3>
set addke4 <option1>, <option2>, <option3>
set addke5 <option1>, <option2>, <option3>
set addke6 <option1>, <option2>, <option3>
set addke7 <option1>, <option2>, <option3>
next
end
Example
A financial institution uses IPsec VPN to move sensitive customer data, such as account numbers, social insurance numbers, and credit card information. The current encryption used is based on traditional algorithms, which could be vulnerable to attacks from quantum computers in the future. By implementing Post-Quantum Cryptography, the financial institution can ensure that their data remains secure even as technology advances, protecting themselves and their customers from potential breaches due to advancements in computing power. This ensures compliance with regulatory requirements and maintains customer trust.

To enable PQC in the GUI:
|
|
This is a site-to-site VPN setup. Only the new configuration is being demonstrated in the GUI for this example. For more information, see Basic site-to-site VPN with pre-shared key. |
-
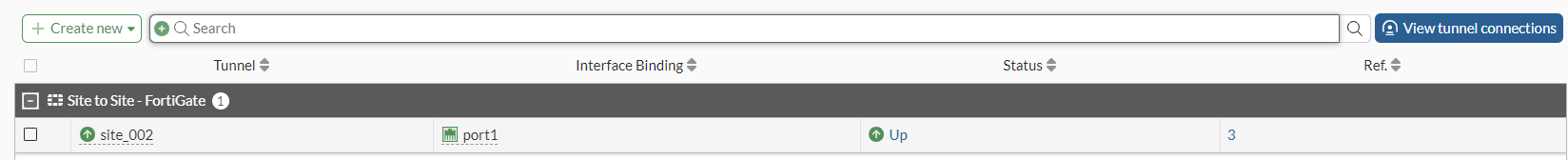
Go to VPN > VPN Tunnels.
-
Double-click the VPN Tunnel to open it for editing.
-
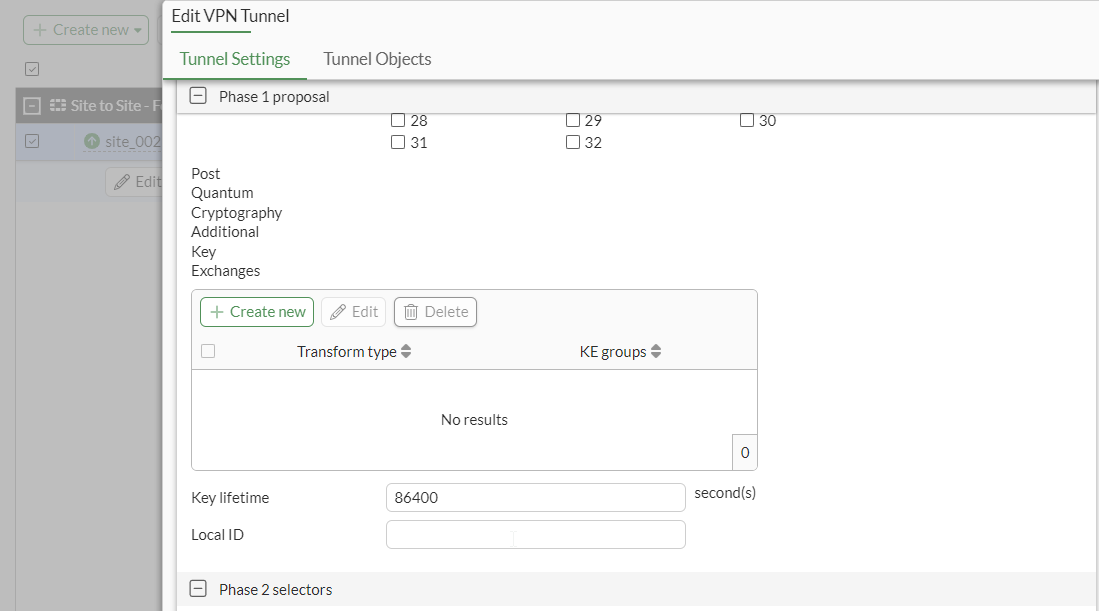
Scroll down to Post Quantum Cryptography Additional Key Exchanges, and click Create new.
-
Set Transform type, select up to three KE groups, and click OK.
-
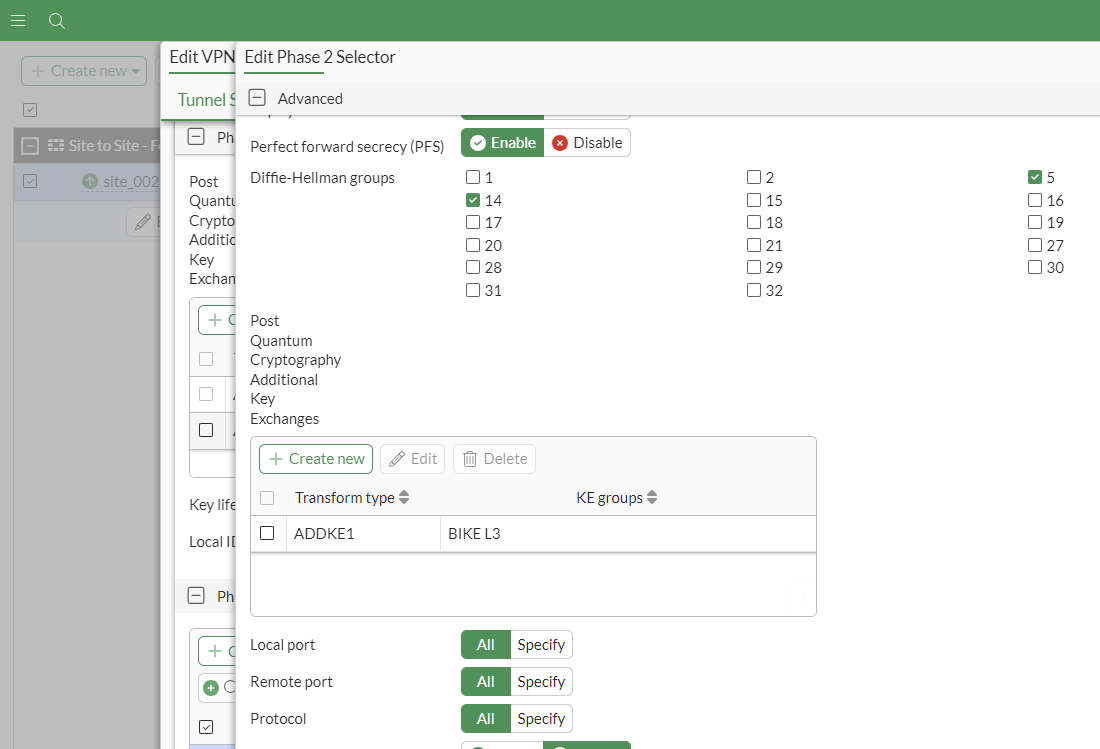
In Phase 2 selectors, click Create new and repeat the steps above.
-
Click OK to save the tunnel.
To enable PQC key exchange for an IPsec tunnel in the CLI:
-
Configure FGT-C:
config vpn ipsec phase1-interface edit "site_002" set interface "port1" set ike-version 2 set peertype any set net-device disable set proposal aes128-sha256 aes256-sha256 aes128gcm-prfsha256 aes256gcm-prfsha384 chacha20poly1305-prfsha256 set addke1 35 36 37 set addke2 1083 set childless-ike enable set transport auto set remote-gw 172.16.200.9 set psksecret XXXXXX next end config vpn ipsec phase2-interface edit "site_002" set phase1name "site_002" set addke1 1090 set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 next end -
Configure FGT-D:
config vpn ipsec phase1-interface edit "site_001" set interface "port1" set ike-version 2 set peertype any set net-device disable set proposal aes128-sha256 aes256-sha256 aes128gcm-prfsha256 aes256gcm-prfsha384 chacha20poly1305-prfsha256 set addke1 35 36 37 set addke2 1083 set childless-ike enable set transport auto set remote-gw 172.16.200.8 set psksecret XXXXXX next end config vpn ipsec phase2-interface edit "site_001" set phase1name "site_001" set addke1 1090 set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 next end -
Verify the IPsec VPN tunnel state on FGT-D:
#diagnose vpn ike gateway list vd: root/0 name: site_001PPPPPP1 version: 2 interface: port1 9 addr: 172.16.200.9:500 -> 172.16.200.8:500 tun_id: 172.16.200.8/::172.16.200.8 remote_location: 0.0.0.0 network-id: 0 transport: UDP created: 88s ago peer-id: 172.16.200.8 peer-id-auth: no pending-queue: 0 PPK: no IKE SA: created 1/1 established 1/1 time 0/0/0 ms IPsec SA: created 1/1 established 1/1 time 0/0/0 ms id/spi: 111 7316ebc639a46c4b/4be2fd15d7304333 direction: responder status: established 88-88s ago = 0ms proposal: aes128-sha256 child: no SK_ei: 5a81d7880641e298-3c6cd9753e62c482 SK_er: b52ad6f1590ca132-86245f3df596eb32 SK_ai: 00d051d432556218-5708374c8496c37e-aef06d7d0457bebd-506bd9034bdd1c30 SK_ar: 15dac6f288163198-2c34b87dda107af7-6db98a53b29cf757-0d6d5b8020cc8d47 PPK: no message-id sent/recv: 0/6 QKD: no PQC-KEM (IKE): yes PQC-KEM (all IPsec): yes lifetime/rekey: 86400/86041 DPD sent/recv: 00000000/00000000 peer-id: 172.16.200.8
-
Verify the IKE debug output:
#diagnose debug enable #diagnose debug application ike -1 ike V=root:0:site_002PPPPPP1:14: initiator received SA_INIT response ike V=root:0:site_002PPPPPP1:14: processing notify type NAT_DETECTION_SOURCE_IP ike V=root:0:site_002PPPPPP1:14: processing NAT-D payload ike V=root:0:site_002PPPPPP1:14: NAT not detected ike V=root:0:site_002PPPPPP1:14: process NAT-D ike V=root:0:site_002PPPPPP1:14: processing notify type NAT_DETECTION_DESTINATION_IP ike V=root:0:site_002PPPPPP1:14: processing NAT-D payload ike V=root:0:site_002PPPPPP1:14: NAT not detected ike V=root:0:site_002PPPPPP1:14: process NAT-D ike V=root:0:site_002PPPPPP1:14: processing notify type FRAGMENTATION_SUPPORTED ike V=root:0:site_002PPPPPP1:14: processing notify type CHILDLESS_IKEV2_SUPPORTED ike V=root:0:site_002PPPPPP1:14: processing notify type INTERMEDIATE_EXCHANGE_SUPPORTED ike V=root:0:site_002PPPPPP1:14: incoming proposal: ike V=root:0:site_002PPPPPP1:14: proposal id = 1: ike V=root:0:site_002PPPPPP1:14: protocol = IKEv2: ike V=root:0:site_002PPPPPP1:14: encapsulation = IKEv2/none ike V=root:0:site_002PPPPPP1:14: type=ENCR, val=AES_CBC (key_len = 128) ike V=root:0:site_002PPPPPP1:14: type=INTEGR, val=AUTH_HMAC_SHA2_256_128 ike V=root:0:site_002PPPPPP1:14: type=PRF, val=PRF_HMAC_SHA2_256 ike V=root:0:site_002PPPPPP1:14: type=DH_GROUP, val=MODP2048. ike V=root:0:site_002PPPPPP1:14: type=ADDKE1, val=ML-KEM-512. ike V=root:0:site_002PPPPPP1:14: type=ADDKE2, val=FRODO L1. ike V=root:0:site_002PPPPPP1:14: matched proposal id 1 ike V=root:0:site_002PPPPPP1:14: proposal id = 1: ike V=root:0:site_002PPPPPP1:14: protocol = IKEv2: ike V=root:0:site_002PPPPPP1:14: encapsulation = IKEv2/none ike V=root:0:site_002PPPPPP1:14: type=ENCR, val=AES_CBC (key_len = 128) ike V=root:0:site_002PPPPPP1:14: type=INTEGR, val=AUTH_HMAC_SHA2_256_128 ike V=root:0:site_002PPPPPP1:14: type=PRF, val=PRF_HMAC_SHA2_256 ike V=root:0:site_002PPPPPP1:14: type=DH_GROUP, val=MODP2048. ike V=root:0:site_002PPPPPP1:14: type=ADDKE1, val=ML-KEM-512. ike V=root:0:site_002PPPPPP1:14: type=ADDKE2, val=FRODO L1. ike V=root:0:site_002PPPPPP1:14: lifetime=86400 ike V=root:0:site_002PPPPPP1:14: compute DH shared secret request pending ike 0:site_002PPPPPP1:14: IKE SA 1d7b30eb8916377b/bcc3ac86051fd55c SK_ei 16:636BFFEC63FB7B02AC3C55CBC2A615ED ike 0:site_002PPPPPP1:14: IKE SA 1d7b30eb8916377b/bcc3ac86051fd55c SK_er 16:EBA51E65F2E101A6922C728D8507B1D6 ike 0:site_002PPPPPP1:14: IKE SA 1d7b30eb8916377b/bcc3ac86051fd55c SK_ai 32:146F21B8D780175B7CF3C13475754B5296D11E0658695F77E7688C33681AA8A6 ike 0:site_002PPPPPP1:14: IKE SA 1d7b30eb8916377b/bcc3ac86051fd55c SK_ar 32:ADA3A9275B35CD2309B73FCE7A17AD0A75DC5F98A4D4FF008D7503CD6A69EA94 ike V=root:0:site_002PPPPPP1:14: initiator preparing INTERMEDIATE msg ike V=root:0:site_002PPPPPP1:14: generating KE for group 35 ike 0:site_002PPPPPP1:14: enc ike V=root:0:site_002PPPPPP1:14: initiator received INTEREMDIATE response ike V=root:0:site_002PPPPPP1:14: processing KE group 35 ike V=root:0:site_002PPPPPP1:14: KEM decapsulate okay ike 0:site_002PPPPPP1:14: IKE SA 1d7b30eb8916377b/bcc3ac86051fd55c SK_ei 16:7D54A38F71768F91B32EA828521E56D7 ike 0:site_002PPPPPP1:14: IKE SA 1d7b30eb8916377b/bcc3ac86051fd55c SK_er 16:AC66EF35E670D558A5704519E348BFD2 ike 0:site_002PPPPPP1:14: IKE SA 1d7b30eb8916377b/bcc3ac86051fd55c SK_ai 32:39DED1A07EF0D0A37D2FA51AF478EC981E17D4092FA1DE3CF3A46EC8E28DD9E9 ike 0:site_002PPPPPP1:14: IKE SA 1d7b30eb8916377b/bcc3ac86051fd55c SK_ar 32:3E8BB857F90943DD289DDCDE742AC18DFBF0DA7590F9CEA5E413B02463BE4303 ike V=root:0:site_002PPPPPP1:14: initiator preparing INTERMEDIATE msg ike V=root:0:site_002PPPPPP1:14: generating KE for group 1083 ike V=root:0:site_002PPPPPP1:14: splitting payload len=9624 into 10 fragments ike V=root:0:site_002PPPPPP1:14:site_002:17: phase2 matched by subset ike V=root:0:site_002PPPPPP1:14:site_002:17: accepted proposal: ike V=root:0:site_002PPPPPP1:14:site_002:17: TSr_0 0:10.1.100.0-10.1.100.255:0 ike V=root:0:site_002PPPPPP1:14:site_002:17: TSi_0 0:10.1.200.0-10.1.200.255:0 ike V=root:0:site_002PPPPPP1:14:site_002:17: autokey ike V=root:0:site_002PPPPPP1:14:site_002:17: incoming child SA proposal: ike V=root:0:site_002PPPPPP1:14:site_002:17: proposal id = 1: ike V=root:0:site_002PPPPPP1:14:site_002:17: protocol = ESP: ike V=root:0:site_002PPPPPP1:14:site_002:17: encapsulation = TUNNEL ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ENCR, val=AES_CBC (key_len = 128) ike V=root:0:site_002PPPPPP1:14:site_002:17: type=INTEGR, val=SHA ike V=root:0:site_002PPPPPP1:14:site_002:17: type=DH_GROUP, val=MODP2048 ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ESN, val=NO ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=BIKE L3. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=BIKE L5. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=HQC128. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=HQC192. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=HQC256. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=1090. ike V=root:0:site_002PPPPPP1:14:site_002:17: matched proposal id 1 ike V=root:0:site_002PPPPPP1:14:site_002:17: proposal id = 1: ike V=root:0:site_002PPPPPP1:14:site_002:17: protocol = ESP: ike V=root:0:site_002PPPPPP1:14:site_002:17: encapsulation = TUNNEL ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ENCR, val=AES_CBC (key_len = 128) ike V=root:0:site_002PPPPPP1:14:site_002:17: type=INTEGR, val=SHA ike V=root:0:site_002PPPPPP1:14:site_002:17: type=DH_GROUP, val=MODP2048 ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ESN, val=NO ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=BIKE L3. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=BIKE L5. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=HQC128. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=HQC192. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=HQC256. ike V=root:0:site_002PPPPPP1:14:site_002:17: type=ADDKE1, val=1090. ike V=root:0:site_002PPPPPP1:14:site_002:17: lifetime=43200 ike V=root:0:site_002PPPPPP1:14:site_002:17: ADDKE negotiated ike V=root:0:site_002PPPPPP1:17: initiator preparing FOLLOWUP_KE message (CHILD_SA) ike V=root:0:site_002PPPPPP1:17: construct KE grp (1090) payload ike V=root:0:site_002PPPPPP1:14: splitting payload len=3103 into 3 fragments

