Enhancing SIP reliability in 464XLAT environments
FortiGate can now disable IP address translation within the SIP payload in 464XLAT environments as needed. This ensures SIP packets with IPv4 information reach user equipment without translation, which addresses an issue where the customer-side translator (CLAT) component does not revert the IPv6 address to IPv4 within the SIP header and body, which leads to RTP connection issues in 464XLAT environments. By preventing unnecessary translation, FortiGate ensures seamless communication and robust connectivity to improve the reliability of SIP-based services in complex network scenarios.
|
|
FortiGate only uses this feature as needed. A flag is added to each |
Scope and limitations
Only one TCP connection is used between each SIP client and the SIP server, and the TCP connection remains up (in other words, doesn't tear down).
All SIP traffic between each SIP client and the SIP server must use the same TCP connection.
Because of the above requirements, SIP pinhole is not created.
The SIP server must offer its own IP address. The twin case for hnt_464xlat is not supported.
Only SIP/TCP-5060 is supported, and session-helper must be configured:
config system session-helper
edit 13
set name sip
set protocol 6
set port 5060
next
end
Example
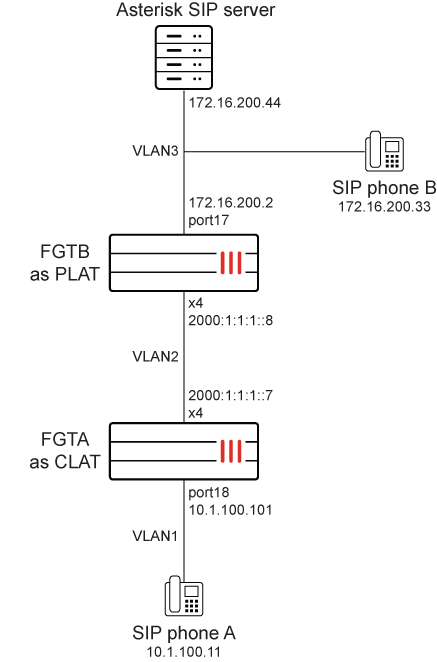
The example uses the following topology:
-
The CLAT component run insides the user equipment (UE) and performs a one-to-one (IPv4 to IPv6) stateless translation. The CLAT component translates traffic with an IPv4 destination to IPv6. While the IPv4 address is converted to IPv6 in the IP header, the IP information within the payload, including the SIP header and body, remains unchanged (IPv4).
-
FortiGate as PLAT performs many-to-one (IPv6 to IPv4) stateful translation to translate the IP address within the IP header from IPv6 to IPv4. Furthermore, SIP-ALG modifies the IP address within the payload in the SIP header and body by substituting the IPv4 address with a publicly NATed IP address.
-
For traffic returning from SIP server, FortiGate stops NAT46 on the SIP payload and only translates the IPv4 addresses in the IP header into an IPv6 address. Thus, the IP address contained within the SIP header and body remains IPv4, which the user equipment can recognize, and RTP connections can be successfully established.
-
The packet reaches UE, and the CLAT component translates the IP address of the IP header from IPv6 to IPv4. The CLAT component does not function as an ALG and does not modify the IP address within the SIP header and body.
-
The UE receives the packet but cannot establish RTP connection with the IPv6 destination.
To check the SIP calls when phone A (10.1.100.11) and phone B (172.16.200.33) are registering to the SIP server (172.16.200.44):
-
View the SIP proxy SIP calls:
# diagnose sys sip-proxy calls sip calls vdom 1 (vdom1) vrf 0 call 7fc9eb265000 call-id: QFwxzc1FTIYZQJsQZW3-kKofMxJUcxaB txn 7fc9eb250e00 (REGISTER) cseq 49308 dir 0 state 5 status 200 expiry 903 HA 0 i_session: 7fc9eb250000 r_session: 7fc9eb250000 register: present from: sip:1001@172.16.200.44 to: sip:1001@172.16.200.44 src: [2000:1:1:1::1:6e0c]:49555 dst: 172.16.200.44:5060 vdom 1 (vdom1) vrf 0 call 7fc9eb265000 call-id: QFwxzc1FTIYZQJsQZW3-kKofMxJUcxaB txn 7fc9eb250700 (REGISTER) cseq 49307 dir 0 state 7 status 401 expiry 23 HA 0 i_session: 7fc9eb250000 r_session: 7fc9eb250000 register: present from: sip:1001@172.16.200.44 to: sip:1001@172.16.200.44 src: [2000:1:1:1::1:6e0c]:49555 dst: 172.16.200.44:5060
To check the SIP calls and session lists when phone A (10.1.100.1) is calling phone B (172.16.200.33):
-
View the SIP proxy SIP calls:
# diagnose sys sip-proxy calls sip calls vdom 1 (vdom1) vrf 0 call 7fc9eb265100 call-id: mNcOPU8ul76A1ihupFMNU78kePJYEfr3 txn 7fc9eb251c00 (INVITE) cseq 102 dir 1 state 11 status 200 expiry 297 HA 0 i_session: 7fc9eb250000 r_session: 7fc9eb250000 register: not-present from: sip:1003@172.16.200.44 to: sip:1001@172.16.200.44 src: 172.16.200.44:5060 dst: [2000:1:1:1::1:6e0c]:49555 vdom 1 (vdom1) vrf 0 call 7fc9eb265100 call-id: mNcOPU8ul76A1ihupFMNU78kePJYEfr3 txn 7fc9eb250700 (INVITE) cseq 22155 dir 0 state 11 status 200 expiry 296 HA 0 i_session: 7fc9eb250000 r_session: 7fc9eb250000 register: not-present from: sip:1001@172.16.200.44 to: sip:1003@172.16.200.44 src: [2000:1:1:1::1:6e0c]:49555 dst: 172.16.200.44:5060 vdom 1 (vdom1) vrf 0 call 7fc9eb265100 call-id: mNcOPU8ul76A1ihupFMNU78kePJYEfr3 txn 7fc9eb251500 (INVITE) cseq 22154 dir 0 state 11 status 200 expiry 296 HA 0 i_session: 7fc9eb250000 r_session: 7fc9eb250000 register: not-present from: sip:1001@172.16.200.44 to: sip:1003@172.16.200.44 src: [2000:1:1:1::1:6e0c]:49555 dst: 172.16.200.44:5060 vdom 1 (vdom1) vrf 0 call 7fc9eb265000 call-id: QFwxzc1FTIYZQJsQZW3-kKofMxJUcxaB txn 7fc9eb250e00 (REGISTER) cseq 49308 dir 0 state 5 status 200 expiry 871 HA 0 i_session: 7fc9eb250000 r_session: 7fc9eb250000 register: present from: sip:1001@172.16.200.44 to: sip:1001@172.16.200.44 src: [2000:1:1:1::1:6e0c]:49555 dst: 172.16.200.44:5060 -
View the IPv6 session list:
# diagnose sys session6 list ... orgin->sink: org pre->post, reply pre->post dev=34->43/43->34 hook=pre dir=org act=dnat 2000:1:1:1::1:6e0c:34143->2000:172:16:200::44:5060(2000:172:16:200::44:5060) hook=post dir=reply act=snat 2000:172:16:200::44:5060->2000:1:1:1::1:6e0c:34143(2000:172:16:200::44:5060) peer=172.16.200.6:34143->172.16.200.44:5060 naf=1 hook=pre dir=org act=noop 172.16.200.6:34143->172.16.200.44:5060(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.44:5060->172.16.200.6:34143(0.0.0.0:0) ... orgin->sink: org pre->post, reply pre->post dev=34->43/43->0 hook=post dir=org act=noop 2000:1:1:1::1:6e0c:9117->2000:172:16:200::44:64446(:::0) hook=pre dir=reply act=noop 2000:172:16:200::44:64446->2000:1:1:1::1:6e0c:9117(:::0) peer=172.16.200.6:64444->172.16.200.44:18764 naf=1 hook=pre dir=org act=noop 172.16.200.6:64444->172.16.200.44:18764(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.44:18764->172.16.200.6:64444(0.0.0.0:0) ... orgin->sink: org pre->post, reply pre->post dev=34->43/43->34 hook=pre dir=org act=dnat 2000:1:1:1::1:6e0c:9117->2000:172:16:200::33:64448(2000:172:16:200::33:64448) hook=post dir=reply act=snat 2000:172:16:200::33:64448->2000:1:1:1::1:6e0c:9117(2000:172:16:200::33:64448) peer=172.16.200.6:9117->172.16.200.33:64448 naf=1 hook=pre dir=org act=noop 172.16.200.6:9117->172.16.200.33:64448(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.33:64448->172.16.200.6:9117(0.0.0.0:0) ... orgin->sink: org pre->post, reply pre->post dev=34->43/43->34 hook=post dir=org act=noop 2000:1:1:1::1:6e0c:9118->2000:172:16:200::44:64447(:::0) hook=pre dir=reply act=noop 2000:172:16:200::44:64447->2000:1:1:1::1:6e0c:9118(:::0) peer=172.16.200.6:64445->172.16.200.44:18765 naf=1 hook=pre dir=org act=noop 172.16.200.6:64445->172.16.200.44:18765(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.44:18765->172.16.200.6:64445(0.0.0.0:0) ... orgin->sink: org pre->post, reply pre->post dev=34->43/43->34 hook=pre dir=org act=dnat 2000:1:1:1::1:6e0c:9118->2000:172:16:200::33:64449(2000:172:16:200::33:64449) hook=post dir=reply act=snat 2000:172:16:200::33:64449->2000:1:1:1::1:6e0c:9118(2000:172:16:200::33:64449) peer=172.16.200.6:9118->172.16.200.33:64449 naf=1 hook=pre dir=org act=noop 172.16.200.6:9118->172.16.200.33:64449(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.33:64449->172.16.200.6:9118(0.0.0.0:0) ...
-
View the IPv6 expectation session list:
# diagnose sys session6 list expectation ... orgin->sink: org pre->post, reply pre->post dev=34->0/43->0 hook=post dir=org act=noop 2000:1:1:1::1:6e0c:0->2000:172:16:200::44:64448(:::0) peer=172.16.200.6:64444->172.16.200.33:4000 naf=1 ... orgin->sink: org pre->post, reply pre->post dev=34->0/43->0 hook=post dir=org act=noop 2000:1:1:1::1:6e0c:0->2000:172:16:200::44:64448(:::0) peer=172.16.200.6:64444->172.16.200.33:4000 naf=1 ... orgin->sink: org pre->post, reply pre->post dev=34->0/43->0 hook=post dir=org act=noop 2000:1:1:1::1:6e0c:0->2000:172:16:200::44:64449(:::0) peer=172.16.200.6:64445->172.16.200.33:4001 naf=1 ... orgin->sink: org pre->post, reply pre->post dev=34->0/43->0 hook=post dir=org act=noop 2000:1:1:1::1:6e0c:0->2000:172:16:200::44:64449(:::0) peer=172.16.200.6:64445->172.16.200.33:4001 naf=1 ...
-
View the IPv4 session list:
# diagnose sys session list ... orgin->sink: org pre->post, reply pre->post dev=43->23/23->43 gwy=172.16.200.33/172.16.200.6 hook=pre dir=org act=noop 172.16.200.6:9117->172.16.200.33:64448(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.33:64448->172.16.200.6:9117(0.0.0.0:0) peer=2000:172:16:200::33:64448->2000:1:1:1::1:6e0c:9117 naf=2 hook=pre dir=org act=dnat 2000:1:1:1::1:6e0c:9117->2000:172:16:200::33:64448(2000:172:16:200::33:64448) hook=post dir=reply act=snat 2000:172:16:200::33:64448->2000:1:1:1::1:6e0c:9117(2000:172:16:200::33:64448) ... orgin->sink: org pre->post, reply pre->post dev=43->23/23->43 gwy=172.16.200.33/172.16.200.6 hook=pre dir=org act=noop 172.16.200.6:9118->172.16.200.33:64449(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.33:64449->172.16.200.6:9118(0.0.0.0:0) peer=2000:172:16:200::33:64449->2000:1:1:1::1:6e0c:9118 naf=2 hook=pre dir=org act=dnat 2000:1:1:1::1:6e0c:9118->2000:172:16:200::33:64449(2000:172:16:200::33:64449) hook=post dir=reply act=snat 2000:172:16:200::33:64449->2000:1:1:1::1:6e0c:9118(2000:172:16:200::33:64449) ... orgin->sink: org pre->post, reply pre->post dev=43->23/23->43 gwy=172.16.200.44/172.16.200.6 hook=pre dir=org act=noop 172.16.200.6:34143->172.16.200.44:5060(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.44:5060->172.16.200.6:34143(0.0.0.0:0) peer=2000:172:16:200::44:5060->2000:1:1:1::1:6e0c:34143 naf=2 hook=pre dir=org act=dnat 2000:1:1:1::1:6e0c:34143->2000:172:16:200::44:5060(2000:172:16:200::44:5060) hook=post dir=reply act=snat 2000:172:16:200::44:5060->2000:1:1:1::1:6e0c:34143(2000:172:16:200::44:5060) ... orgin->sink: org pre->post, reply pre->post dev=43->23/23->0 gwy=172.16.200.44/0.0.0.0 hook=pre dir=org act=noop 172.16.200.6:64444->172.16.200.44:18764(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.44:18764->172.16.200.6:64444(0.0.0.0:0) peer=2000:172:16:200::44:64446->2000:1:1:1::1:6e0c:9117 naf=2 hook=post dir=org act=noop 2000:1:1:1::1:6e0c:9117->2000:172:16:200::44:64446(:::0) hook=pre dir=reply act=noop 2000:172:16:200::44:64446->2000:1:1:1::1:6e0c:9117(:::0) ... orgin->sink: org pre->post, reply pre->post dev=43->23/23->43 gwy=172.16.200.44/172.16.200.6 hook=pre dir=org act=noop 172.16.200.6:64445->172.16.200.44:18765(0.0.0.0:0) hook=post dir=reply act=noop 172.16.200.44:18765->172.16.200.6:64445(0.0.0.0:0) peer=2000:172:16:200::44:64447->2000:1:1:1::1:6e0c:9118 naf=2 hook=post dir=org act=noop 2000:1:1:1::1:6e0c:9118->2000:172:16:200::44:64447(:::0) hook=pre dir=reply act=noop 2000:172:16:200::44:64447->2000:1:1:1::1:6e0c:9118(:::0) ...
-
View the IPv4 expectation session list:
# diagnose sys session list expectation ... orgin->sink: org pre->post, reply pre->post dev=43->0/23->0 gwy=0.0.0.0/0.0.0.0 hook=pre dir=org act=noop 172.16.200.6:0->172.16.200.33:4001(0.0.0.0:0) peer=:::0->:::0 naf=2 ... orgin->sink: org pre->post, reply pre->post dev=43->0/23->0 gwy=0.0.0.0/0.0.0.0 hook=pre dir=org act=noop 172.16.200.6:0->172.16.200.33:4001(0.0.0.0:0) peer=:::0->:::0 naf=2 ... orgin->sink: org pre->post, reply pre->post dev=43->0/23->0 gwy=0.0.0.0/0.0.0.0 hook=pre dir=org act=noop 172.16.200.6:0->172.16.200.33:4000(0.0.0.0:0) peer=:::0->:::0 naf=2 ... orgin->sink: org pre->post, reply pre->post dev=43->0/23->0 gwy=0.0.0.0/0.0.0.0 hook=pre dir=org act=noop 172.16.200.6:0->172.16.200.33:4000(0.0.0.0:0) peer=:::0->:::0 naf=2 ...

