SNMP examples
This topic includes examples that incorporate several SNMP settings:
-
Example 1: SNMP traps for monitoring interface status using SNMP v3 user
-
Example 2: SNMP traps and query for monitoring DHCP pool using SNMP v3 user
-
Example 5: Enabling non-management VDOMs to send queries using SNMP v3
Example 1: SNMP traps for monitoring interface status using SNMP v3 user
This configuration enables the SNMP manager (172.16.200.55) to receive notifications when a FortiGate port either goes down or is brought up. The SNMP manager can also query the current status of the FortiGate port.
To configure SNMP for monitoring interface status in the GUI:
-
Configure interface access:
-
Go to Network > Interfaces and edit port1.
-
In the Administrative Access options, enable SNMP.
-
Click OK.
-
-
Configure the SNMP agent:
-
Go to System > SNMP.
-
Enable SNMP Agent and enter the following:
Description
Branch
Location
Burnaby
Contact Info
Jane Doe
-
Click Apply.
-
-
Configure an SNMP v3 user:
-
Go to System > SNMP.
-
In the SNMP v3 table, click Create New.
-
Configure the following:
User Name
Interface_Status
Security Level
Authentication
Authentication Algorithm
SHA1
Password
*******
Hosts IP Address
172.16.200.55
-
Click OK.
-
To configure SNMP for monitoring interface status in the CLI:
-
Configure interface access:
config system interface edit port1 append allowaccess snmp next end -
Configure the SNMP agent:
config system snmp sysinfo set status enable set description Branch set contact-info Jane Doe set location Burnaby end -
Configure an SNMP v3 user:
config system snmp user edit "Interface_Status" set notify-hosts 172.16.200.55 set security-level auth-no-priv set auth-proto sha set auth-pwd ******************** next end
Verification
-
Start the packet capture on interface port1 with the filter set to port 162. See Using the packet capture tool for more information.
-
Turn off one of the FortiGate interface statuses to down, in this case, port2.
-
Save the packet capture.
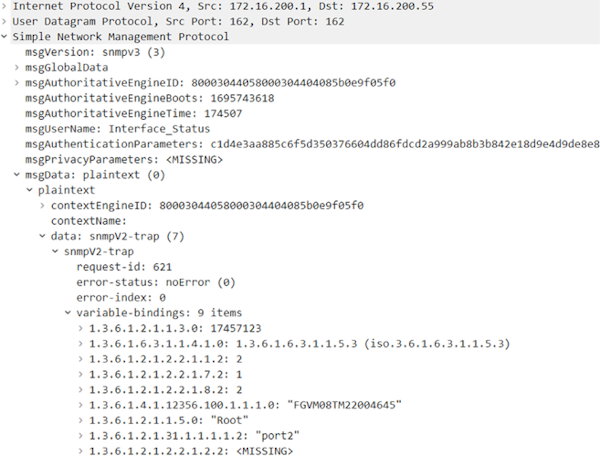
The SNMP v3 trap is transmitted from port1 to the SNMP manager. Note that
msgAuthenticationParametersis configured, indicating that authentication is active. The absence ofmsgPrivacyParameterssuggests that encryption is not configured. This is further confirmed byplaintextinmsgData. -
Verify that the SNMP manager has received the trap. See Important SNMP traps for an example of a trap.
-
Verify that the SNMP manager can successfully query and receive receive a response on the current status of the FortiGate ports:
# snmpwalk -v3 -u Interface_Status -l authNoPriv -a SHA -A xxxxxxxx 172.16.200.1 1.3.6.1.2.1.2.2.1.8 iso.3.6.1.2.1.2.2.1.8.1 = INTEGER: 1 iso.3.6.1.2.1.2.2.1.8.2 = INTEGER: 2 iso.3.6.1.2.1.2.2.1.8.3 = INTEGER: 1 iso.3.6.1.2.1.2.2.1.8.4 = INTEGER: 1 iso.3.6.1.2.1.2.2.1.8.5 = INTEGER: 1 iso.3.6.1.2.1.2.2.1.8.6 = INTEGER: 1 iso.3.6.1.2.1.2.2.1.8.7 = INTEGER: 1 iso.3.6.1.2.1.2.2.1.8.8 = INTEGER: 1 iso.3.6.1.2.1.2.2.1.8.9 = INTEGER: 1 iso.3.6.1.2.1.2.2.1.8.10 = INTEGER: 1
Example 2: SNMP traps and query for monitoring DHCP pool using SNMP v3 user
This configuration enables the SNMP manager (172.16.200.55) to receive DHCP-related notifications from FortiGate.
The SNMP DHCP event contains three traps and one query.
Traps are sent when:
-
DHCP server IP pool usage reaches 90%
-
DHCP server detect an IP address that is already in use
-
DHCP client receives DHCP NAK
SNMP queries are accepted for DHCP lease usage information (OID = 1.3.6.1.4.1.12356.101.23). The query result is based on the leased out percentage.
To configure SNMP for monitoring DHCP pool in the GUI:
-
Configure interface access:
-
Go to Network > Interfaces and edit port1.
-
In the Administrative Access options, enable SNMP.
-
Click OK.
-
-
Configure the SNMP agent:
-
Go to System > SNMP.
-
Enable SNMP Agent and enter the following:
Description
Branch
Location
Burnaby
Contact Info
Jane Doe
-
Click Apply.
-
-
Configure an SNMP v3 user:
-
Go to System > SNMP.
-
In the SNMP v3 table, click Create New.
-
Configure the following:
User Name
DHCP_Status
Security Level
Authentication
Authentication Algorithm
SHA384
Password
*******
Private
Enabled
Encryption Algorithm
AES256
Password
*******
Hosts IP Address
172.16.200.55
-
Click OK.
-
To configure SNMP for monitoring the DHCP pool in the CLI:
-
Configure interface access:
config system interface edit port1 append allowaccess snmp next end -
Configure the SNMP agent:
config system snmp sysinfo set status enable set description Branch set contact-info Jane Doe set location Burnaby end -
Configure an SNMP v3 user:
config system snmp user edit "DHCP_Status" set notify-hosts 172.16.200.55 set security-level auth-priv set auth-proto sha384 set auth-pwd ******************** set priv-proto aes256 set priv-pwd ********************* next end
Verification
-
Start the packet capture on interface port1 with the filter set to port 162. See Using the packet capture tool for more information.
-
Overload the DHCP server IP pool.
-
Save the packet capture.
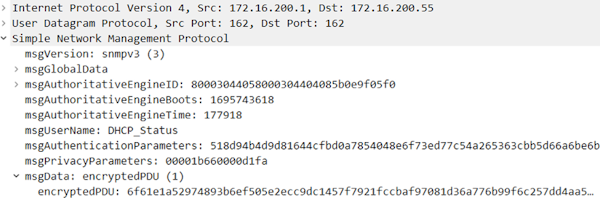
The SNMP v3 trap is transmitted from port1 to the SNMP manager. Note that both
msgAuthenticationParametersandmsgPrivacyParametersare set up, indicating that authentication and encryption are active. This is further confirmed byencryptedPDUinmsgData. -
Verify that the SNMP manager has received the trap. See Important SNMP traps for an example of a trap.
-
Verify that the SNMP manager can successfully query and receive DHCP lease usage information for FortiGate:
# snmpwalk -v3 -u DHCP_Status -l authPriv -a SHA384 -A xxxxxxxx -x AES256 -X xxxxxxxx 172.16.200.1 1.3.6.1.4.1.12356.101.23 iso.3.6.1.4.1.12356.101.23.1.1.0 = INTEGER: 6 iso.3.6.1.4.1.12356.101.23.2.1.1.2.1.1 = INTEGER: 0 iso.3.6.1.4.1.12356.101.23.2.1.1.2.1.2 = INTEGER: 0 iso.3.6.1.4.1.12356.101.23.2.1.1.2.1.3 = INTEGER: 0 iso.3.6.1.4.1.12356.101.23.2.1.1.2.1.4 = INTEGER: 0 iso.3.6.1.4.1.12356.101.23.2.1.1.2.1.5 = INTEGER: 0 iso.3.6.1.4.1.12356.101.23.2.1.1.2.1.6 = INTEGER: 100
Example 3: Enabling the INDEX extension
In the following example, the same IP address will be set on different ports in two VDOMs. The ipAddrTable SNMP Tree output will then be reviewed before and after enabling the append-index command.
When the append-index command is enabled:
-
VDOM and interface indexes are appended as the INDEX extension in RFC tables.
-
In multi-VDOM mode, duplicated IP addresses in different VDOMs will result in multiple entries in the RFC table.
When the append-index command is disabled:
-
VDOM and interface indexes are not appended in RFC tables.
-
In multi-VDOM mode, duplicated IP addresses in different VDOMs will only be presented once in the RFC table.
To enable the INDEX extension:
-
In two different VDOMs, set the same address on two different ports.
config system interface edit "port3" set vdom "vdom1" set ip 10.1.1.1 255.255.255.0 set type physical set snmp-index 5 next end config system interface edit "port4" set vdom "root" set ip 10.1.1.1 255.255.255.0 set type physical set snmp-index 6 next end -
Configure the SNMP information but do not enable the INDEX extension.
config system snmp sysinfo set status enable set description "REGR-SYS" end -
On your PC, review the ipAddrTable SNMP Tree (OID 1.3.6.1.2.1.4.20). The IP address 10.1.1.1 is only displayed once.
snmpwalk -v2c -c REGR-SYS 172.16.200.1 1.3.6.1.2.1.4.20 IP-MIB::ipAdEntAddr.10.1.1.1 = IpAddress: 10.1.1.1 IP-MIB::ipAdEntAddr.10.255.1.1 = IpAddress: 10.255.1.1 IP-MIB::ipAdEntAddr.172.16.200.1 = IpAddress: 172.16.200.1 IP-MIB::ipAdEntAddr.192.168.1.99 = IpAddress: 192.168.1.99 IP-MIB::ipAdEntIfIndex.10.1.1.1 = INTEGER: 5 IP-MIB::ipAdEntIfIndex.10.255.1.1 = INTEGER: 39 IP-MIB::ipAdEntIfIndex.172.16.200.1 = INTEGER: 3 IP-MIB::ipAdEntIfIndex.192.168.1.99 = INTEGER: 2 IP-MIB::ipAdEntNetMask.10.1.1.1 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntNetMask.10.255.1.1 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntNetMask.172.16.200.1 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntNetMask.192.168.1.99 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntBcastAddr.10.1.1.1 = INTEGER: 1 IP-MIB::ipAdEntBcastAddr.10.255.1.1 = INTEGER: 1 IP-MIB::ipAdEntBcastAddr.172.16.200.1 = INTEGER: 1 IP-MIB::ipAdEntBcastAddr.192.168.1.99 = INTEGER: 1 IP-MIB::ipAdEntReasmMaxSize.10.1.1.1 = INTEGER: 65535 IP-MIB::ipAdEntReasmMaxSize.10.255.1.1 = INTEGER: 65535 IP-MIB::ipAdEntReasmMaxSize.172.16.200.1 = INTEGER: 65535 IP-MIB::ipAdEntReasmMaxSize.192.168.1.99 = INTEGER: 65535
-
Enable the INDEX extension.
config system snmp sysinfo set status enable set description "REGR-SYS" set append-index enable end -
Review the ipAddrTable SNMP Tree (OID 1.3.6.1.2.1.4.20) again. The IP address 10.1.1.1 is now displayed twice.
snmpwalk -v2c -c REGR-SYS 172.16.200.1 1.3.6.1.2.1.4.20 IP-MIB::ipAdEntAddr.10.1.1.1.1 = IpAddress: 10.1.1.1 IP-MIB::ipAdEntAddr.10.1.1.1.2 = IpAddress: 10.1.1.1 IP-MIB::ipAdEntAddr.10.255.1.1.1 = IpAddress: 10.255.1.1 IP-MIB::ipAdEntAddr.172.16.200.1.2 = IpAddress: 172.16.200.1 IP-MIB::ipAdEntAddr.192.168.1.99.1 = IpAddress: 192.168.1.99 IP-MIB::ipAdEntIfIndex.10.1.1.1.1 = INTEGER: 6 IP-MIB::ipAdEntIfIndex.10.1.1.1.2 = INTEGER: 5 IP-MIB::ipAdEntIfIndex.10.255.1.1.1 = INTEGER: 39 IP-MIB::ipAdEntIfIndex.172.16.200.1.2 = INTEGER: 3 IP-MIB::ipAdEntIfIndex.192.168.1.99.1 = INTEGER: 2 IP-MIB::ipAdEntNetMask.10.1.1.1.1 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntNetMask.10.1.1.1.2 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntNetMask.10.255.1.1.1 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntNetMask.172.16.200.1.2 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntNetMask.192.168.1.99.1 = IpAddress: 255.255.255.0 IP-MIB::ipAdEntBcastAddr.10.1.1.1.1 = INTEGER: 1 IP-MIB::ipAdEntBcastAddr.10.1.1.1.2 = INTEGER: 1 IP-MIB::ipAdEntBcastAddr.10.255.1.1.1 = INTEGER: 1 IP-MIB::ipAdEntBcastAddr.172.16.200.1.2 = INTEGER: 1 IP-MIB::ipAdEntBcastAddr.192.168.1.99.1 = INTEGER: 1 IP-MIB::ipAdEntReasmMaxSize.10.1.1.1.1 = INTEGER: 65535 IP-MIB::ipAdEntReasmMaxSize.10.1.1.1.2 = INTEGER: 65535 IP-MIB::ipAdEntReasmMaxSize.10.255.1.1.1 = INTEGER: 65535 IP-MIB::ipAdEntReasmMaxSize.172.16.200.1.2 = INTEGER: 65535 IP-MIB::ipAdEntReasmMaxSize.192.168.1.99.1 = INTEGER: 65535
Example 4: Ethernet Statistics Group
FortiOS supports the Ethernet Statistics Group for Remote Network Monitoring (RMON), which provides detailed statistics about the traffic that passes through the Ethernet interface, such as drop events and collisions. This enhancement enables comprehensive monitoring and management of network performance, helping to ensure optimal operation and quickly identify any potential issues.
The Ethernet Statistics Group consists of the etherStatsTable .1.3.6.1.2.1.16.1.1 and can be leveraged using the following:
config system snmp rmon-stat
edit 1
set source <data source of the Ethernet statistics entry>
set owner <owner of the Ethernet statistics entry>
next
end
To enable entries to the Ethernet Statistics Group:
-
Configure the RMON group on the FortiGate:
config system snmp rmon-stat edit 1 set source "port2" set owner "test" next endAn etherStatsEntry is created in the rmon-statistics table.
-
Query the etherStatsTable .1.3.6.1.2.1.16.1.1 on the SNMP server:
# snmpwalk -v2c -c REGR-SYS 172.16.200.1 etherStatsTable RMON-MIB::etherStatsIndex.1 = INTEGER: 1 RMON-MIB::etherStatsDataSource.1 = OID: IF-MIB::ifIndex.8 RMON-MIB::etherStatsDropEvents.1 = Counter32: 0 RMON-MIB::etherStatsOctets.1 = Counter32: 39388877 Octets RMON-MIB::etherStatsPkts.1 = Counter32: 125770 Packets RMON-MIB::etherStatsBroadcastPkts.1 = Counter32: 0 Packets RMON-MIB::etherStatsMulticastPkts.1 = Counter32: 84212 Packets RMON-MIB::etherStatsCRCAlignErrors.1 = Counter32: 0 Packets RMON-MIB::etherStatsUndersizePkts.1 = Counter32: 0 Packets RMON-MIB::etherStatsOversizePkts.1 = Counter32: 0 Packets RMON-MIB::etherStatsFragments.1 = Counter32: 0 Packets RMON-MIB::etherStatsJabbers.1 = Counter32: 0 Packets RMON-MIB::etherStatsCollisions.1 = Counter32: 0 Collisions RMON-MIB::etherStatsPkts64Octets.1 = Counter32: 0 Packets RMON-MIB::etherStatsPkts65to127Octets.1 = Counter32: 0 Packets RMON-MIB::etherStatsPkts128to255Octets.1 = Counter32: 0 Packets RMON-MIB::etherStatsPkts256to511Octets.1 = Counter32: 0 Packets RMON-MIB::etherStatsPkts512to1023Octets.1 = Counter32: 0 Packets RMON-MIB::etherStatsPkts1024to1518Octets.1 = Counter32: 0 Packets RMON-MIB::etherStatsOwner.1 = STRING: "test" RMON-MIB::etherStatsStatus.1 = INTEGER: valid(1)
Example 5: Enabling non-management VDOMs to send queries using SNMP v3
Although non-management and management VDOMs can perform queries using SNMP v3, this example shows how to enable non-management VDOMs to send queries.

PC1 connects to the port on FortiGate for the non-management VDOM, and SNMP v3 queries from non-management VDOMs are enabled. PC5 connects to the port on FortiGate for the management VDOM. With this configuration, SNMP queries are performed by both the non-management and the management VDOMs
To enable non-management VDOM SNMPv3 queries:
-
On FortiGate, enable non-management VDOM queries:
config system snmp sysinfo set status enable set engine-id-type text set engine-id '' set description '' set contact-info '' set location '' set trap-high-cpu-threshold 80 set trap-low-memory-threshold 80 set trap-log-full-threshold 90 set trap-free-memory-threshold 5 set trap-freeable-memory-threshold 60 set append-index disable set non-mgmt-vdom-query enable end -
Check the SNMP information:
This example uses the SNMP walk application to confirm that both management and non-management VDOMs are performing SNMP queries to PC1 and PC5.
pc01:~$ snmpwalk -v3 -u v3user 10.1.100.1 1.3.6.1.4.1.12356.101.5.1.2.1.1.1 FORTINET-FORTIGATE-MIB::fgFwPolID.1.0 = INTEGER: 0 FORTINET-FORTIGATE-MIB::fgFwPolID.1.1 = INTEGER: 1 FORTINET-FORTIGATE-MIB::fgFwPolID.2.0 = INTEGER: 0 pc05~$ snmpwalk -v3 -u v3user 172.16.200.1 1.3.6.1.4.1.12356.101.5.1.2.1.1.1 FORTINET-FORTIGATE-MIB::fgFwPolID.1.0 = INTEGER: 0 FORTINET-FORTIGATE-MIB::fgFwPolID.1.1 = INTEGER: 1 FORTINET-FORTIGATE-MIB::fgFwPolID.2.0 = INTEGER: 0

