Cloud application view
To see different cloud application views, set up the following:
-
A FortiGate with a firewall policy that uses the Application Control security profile.
-
A FortiGate with log data from the local disk or FortiAnalyzer.
-
Optional but highly recommended: SSL Inspection set to deep-inspection in the related firewall policies.
Viewing cloud applications
All cloud applications require SSL Inspection set to deep-inspection on the firewall policy. For example, Facebook_File.Download can monitor Facebook download behavior which requires SSL deep-inspection to parse the deep information in the network packets.
To view cloud applications:
-
Go to Security Profiles > Application Control.
-
Select an Application Control profile that is used by the firewall policy and click Edit.
-
On the Edit Application Sensor page, click View Application Signatures.
-
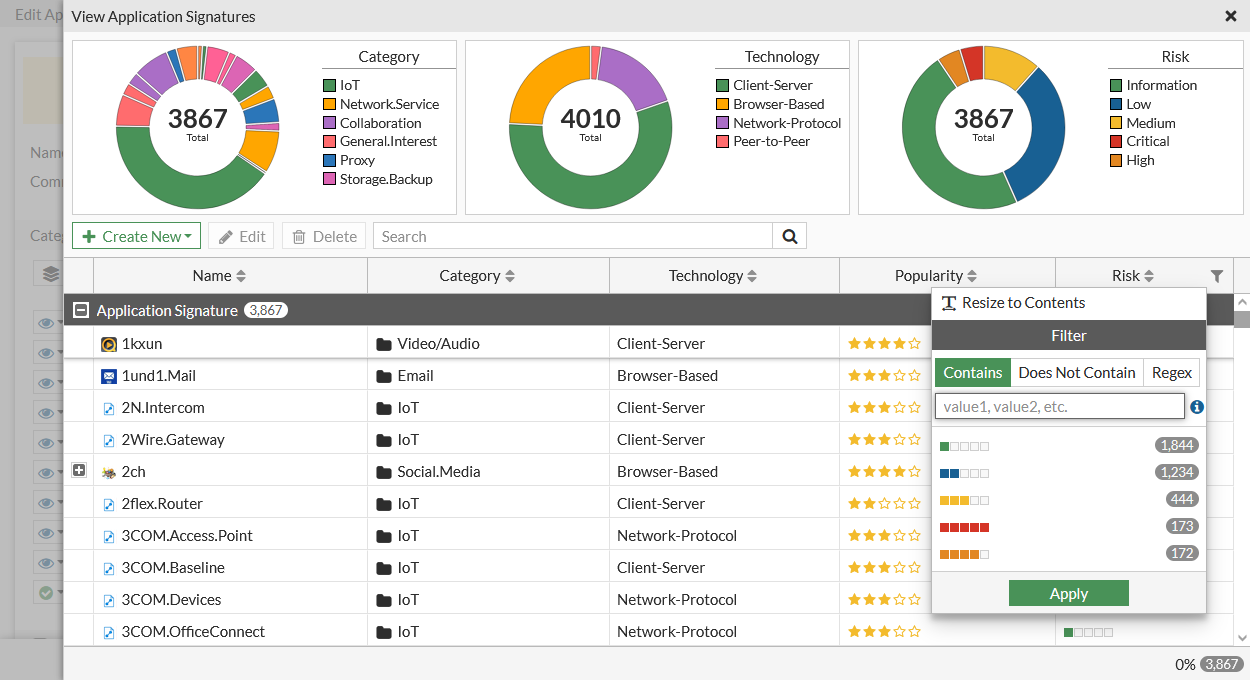
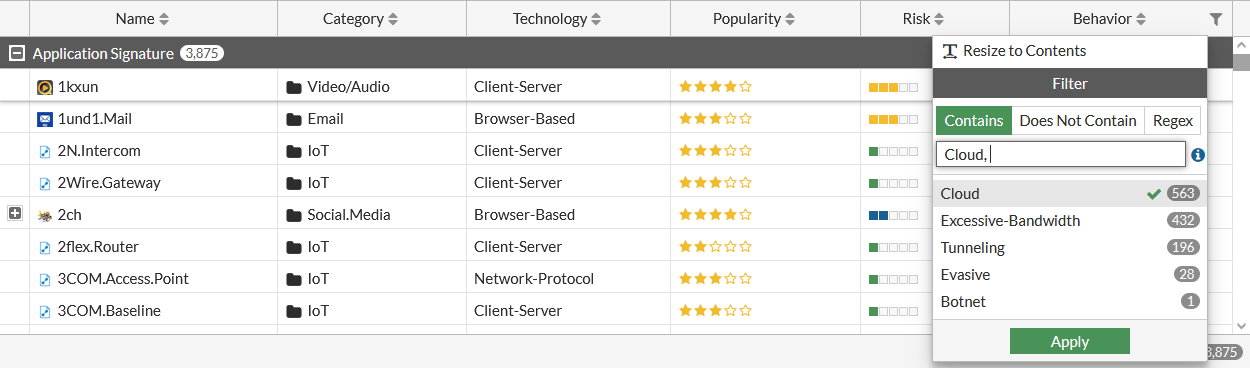
Hover over a column heading or the Application Signature bar. On the right, click the filter icon to filter the applications.
Cloud applications have a cloud icon next to them. The lock icon indicates that the application requires SSL deep inspection.
-
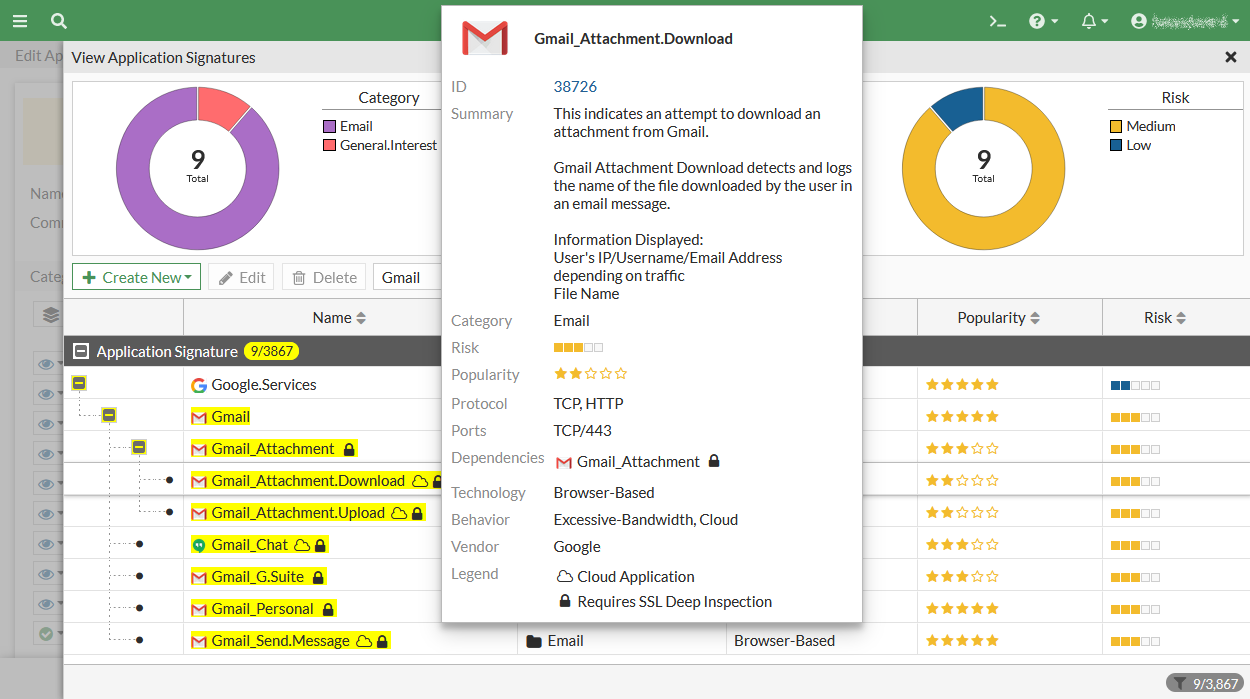
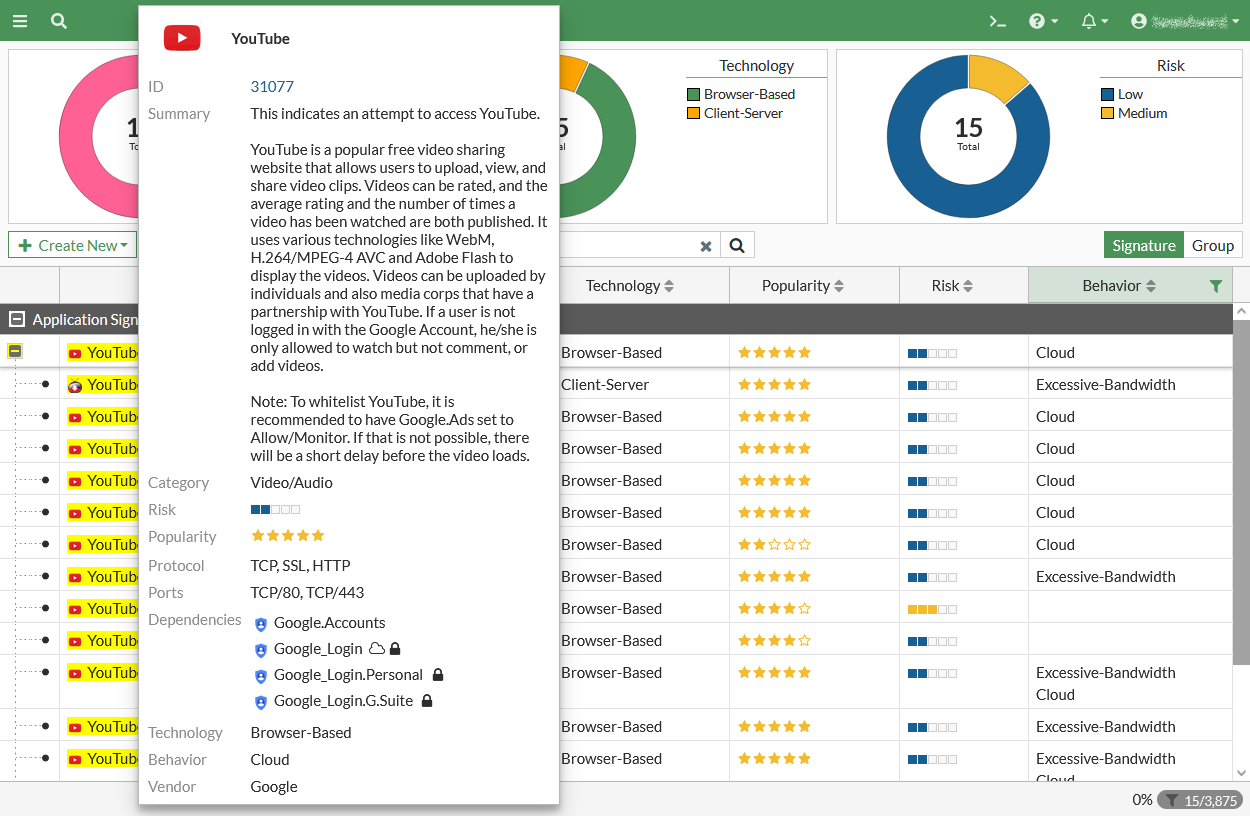
Hover over an item to see its details.
This example shows Gmail_Attachment.Download, a cloud application signature based sensor which requires SSL deep inspection. If any local network user behind the firewall logs into Gmail and downloads a Gmail attachment, that activity is logged.
Applications with cloud behavior
Applications with cloud behavior is a superset of cloud applications.
Some applications do not require SSL deep inspection, such as Facebook, Gmail, and YouTube. This means that if any traffic trigger application sensors for these applications, there is a FortiView cloud application view for that traffic.
Other applications require SSL deep inspection, such as Gmail attachment, Facebook_Workplace, and so on.
To view applications with cloud behavior:
-
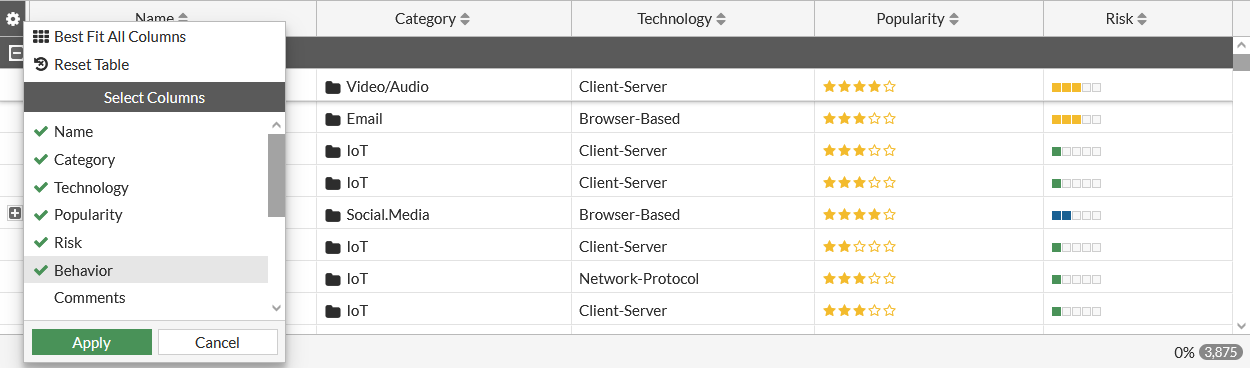
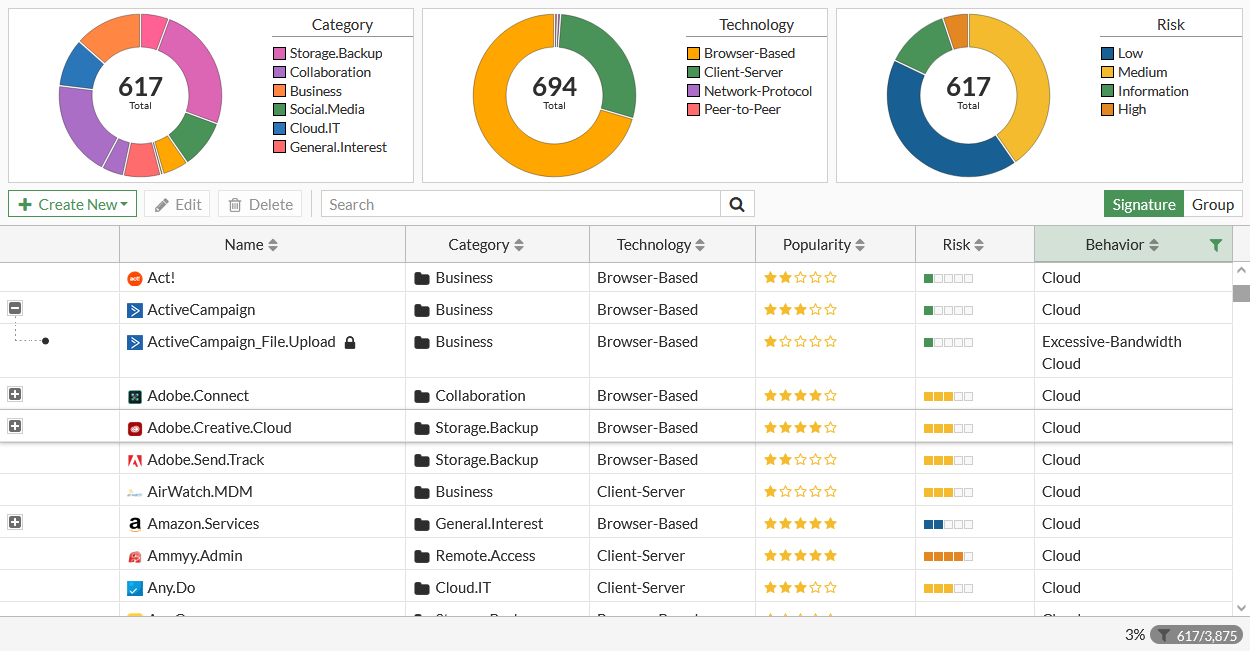
In the Application Signature page, ensure the Behavior column is displayed. If necessary, add the Behavior column.
-
Hover over the left side of the table column headings to display the Configure Table icon.
-
Click Configure Table and select Behavior.
-
Click Apply.
-
-
Click the filter icon in the Behavior column and select Cloud to filter by Cloud. Then click Apply.
-
The Application Signature page displays all applications with cloud behavior.
-
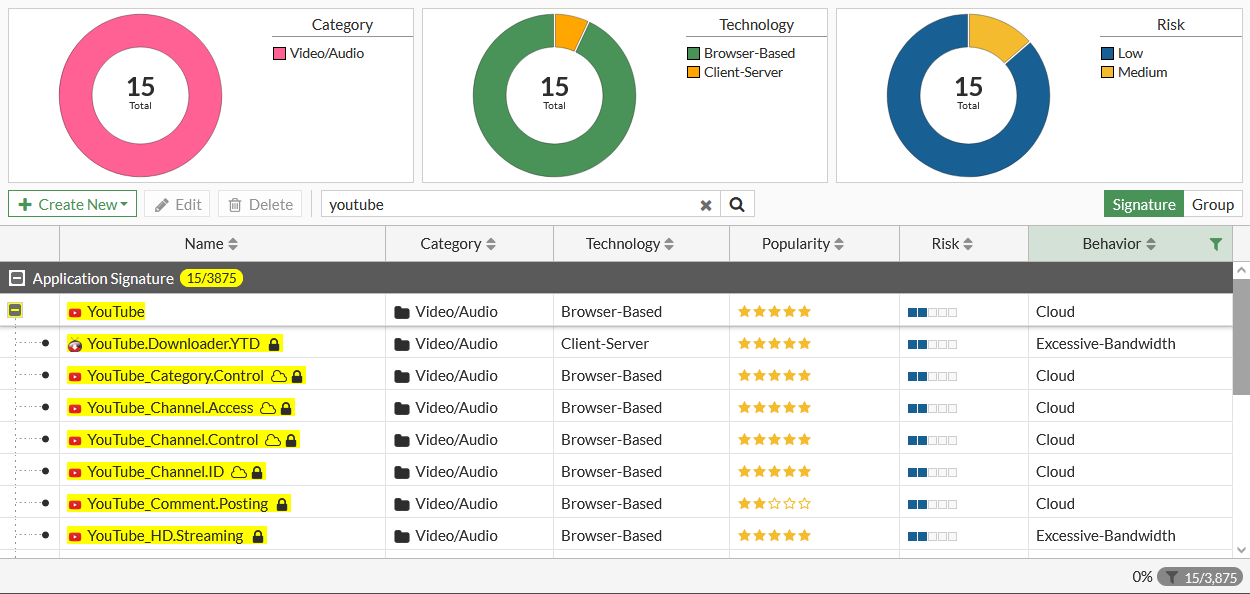
Use the Search box to search for applications. For example, you can search for youtube.
-
Hover over an item to see its details.
This example shows an application sensor with no lock icon which means that this application sensor does not require SSL deep inspection. If any local network user behind the firewall tries to navigate to the YouTube website, that activity is logged.
Configuring the Cloud Applications monitor
Go to Security Profiles > Application Control and edit a profile. On the Edit Application Sensor page in the Categories section, the eye icon next to a category means that category is monitored and logged.
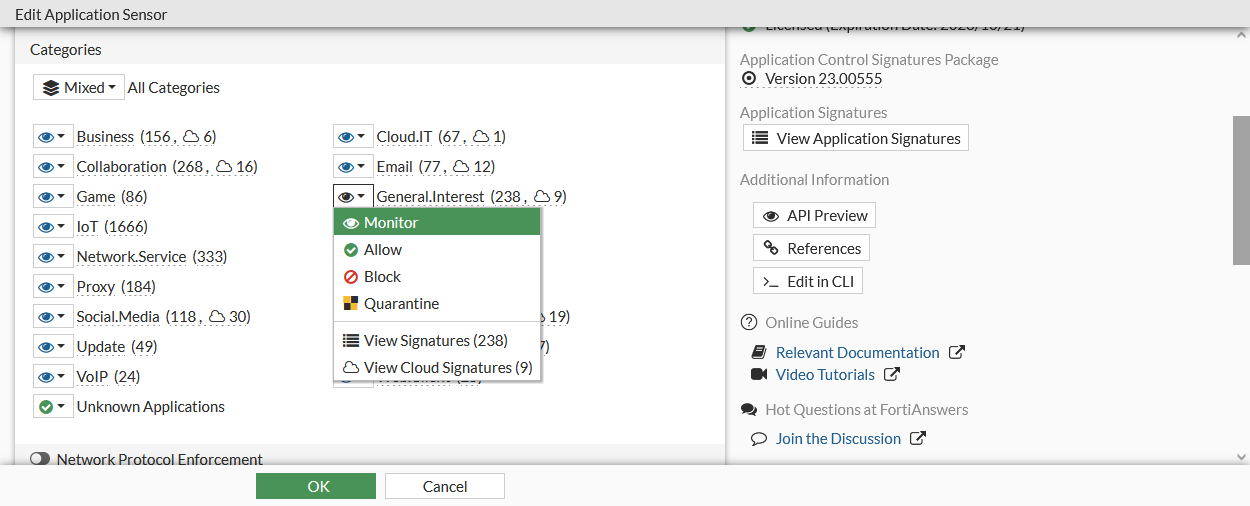
To add the Cloud Applications monitor in the GUI:
-
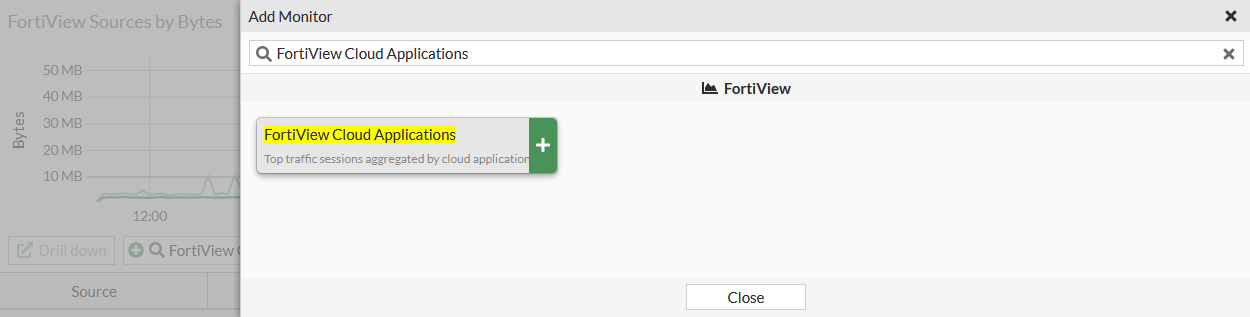
Click Add Monitor. The Add monitor window opens.
-
In the Search field, enter FortiView Cloud Applications and click the Add button next to the monitor.
-
In the FortiGate area, select the FortiGate(s) from the dropdown.
-
In the Data Source area, click Best Available Device or Specify to select a device in the security fabric.
-
From the Time Period dropdown, select a time period greater than Now.
-
From the Sort By dropdown, select Bytes, Sessions, Files (Up/Down), or Videos Played.
-
Click OK. The monitor is added to the tree menu.
-
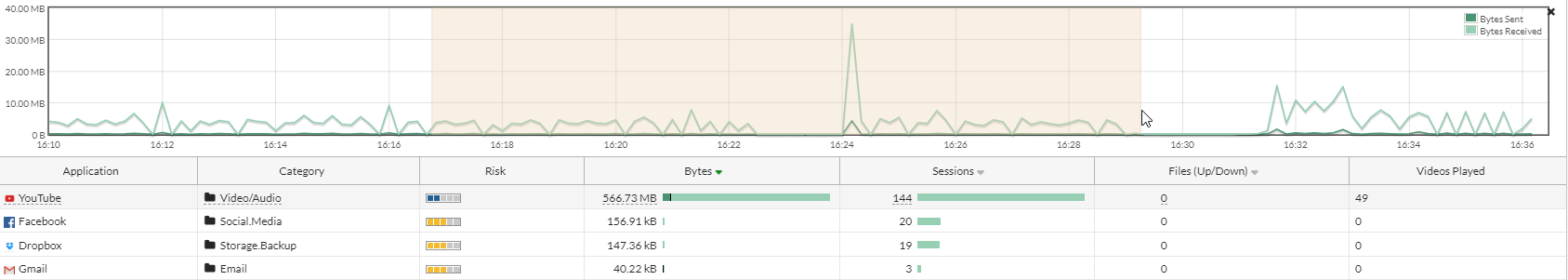
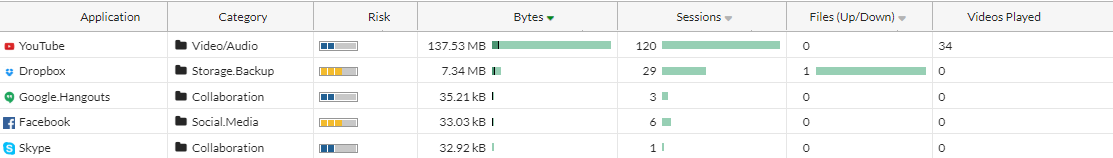
Open the monitor. If SSL deep inspection is enabled in the related firewall policy, then the monitor shows the additional details that are logged, such as Files (Up/Down) and Videos Played.
-
For YouTube, the Videos Played column is triggered by the YouTube_Video.Play cloud application sensor. This shows the number of local network users who logged into YouTube and played YouTube videos.
-
For Dropbox, the Files (Up/Down) column is triggered by Dropbox_File.Download and Dropbox_File.Upload cloud application sensors. This shows the number of local network users who logged into Dropbox and uploaded or downloaded files.
-
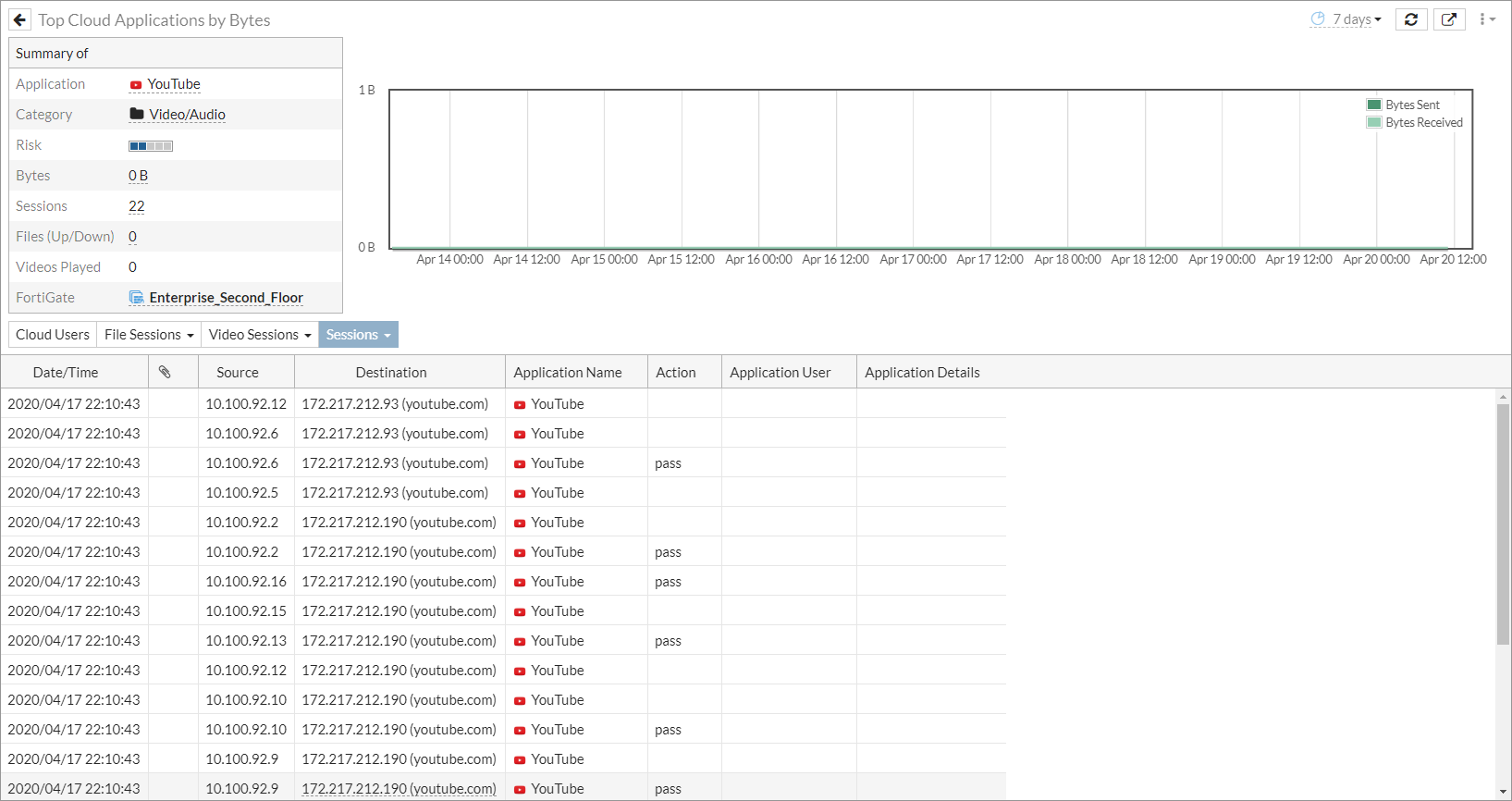
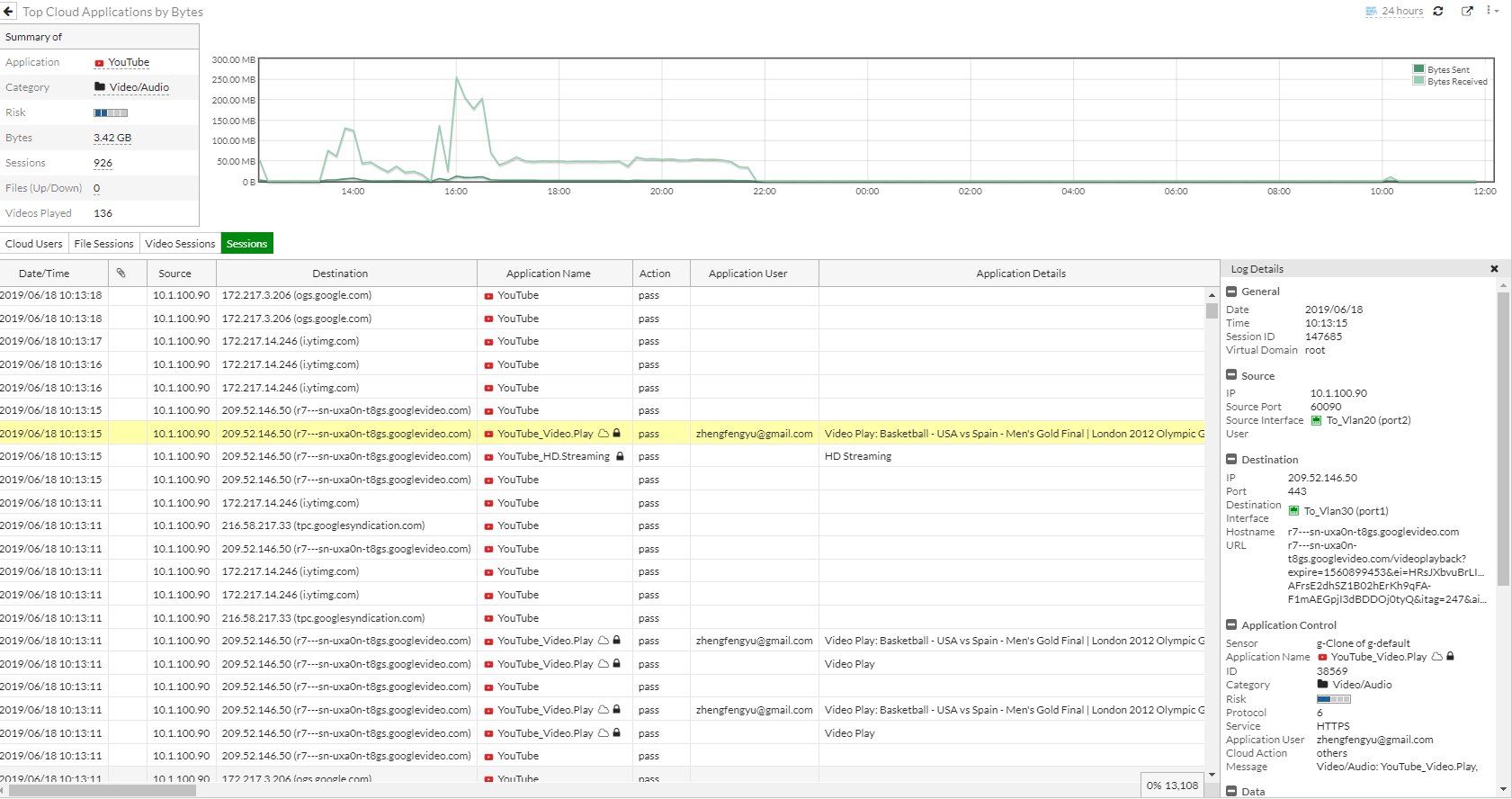
Using the Cloud Applications monitor
To see additional information in the Cloud Applications monitor:
-
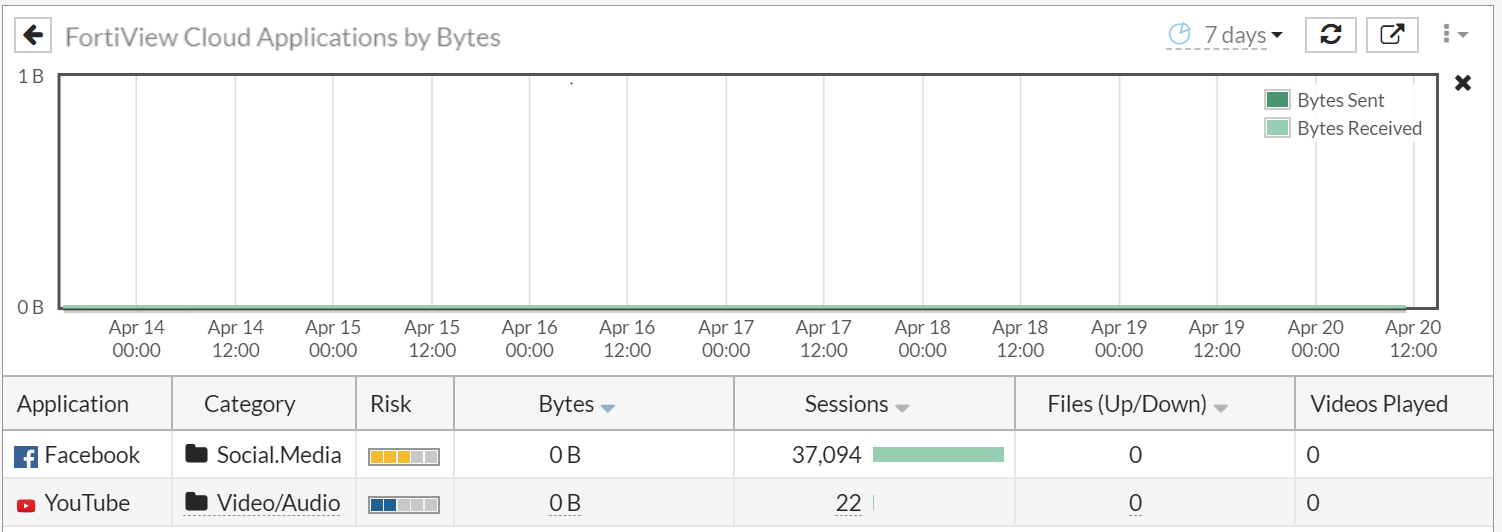
In the tree menu, click the FortiView Cloud Applications monitor to open it.
-
For details about a specific entry, double-click the entry or right-click the entry and select Drill Down to Details.
-
To see all the sessions for an application, click Sessions.
In this example, the Application Name column shows all applications related to YouTube.
-
To view log details, double-click a session to display the Log Details pane.
Sessions monitored by SSL deep inspection (in this example, Youtube_Video.Play) captured deep information such as Application User, Application Details, and so on. The Log Details pane also shows additional deep information such as application ID, Message, and so on.
Sessions not monitored by SSL deep inspection (YouTube) did not capture the deep information.
-
To display a specific time period, select and drag in the timeline graph to display only the data for that time period.