Multiple dynamic header count
Multiple dynamic headers are supported for web proxy profiles, as well as Base64 encoding and the append/new options.
Administrators only have to select the dynamic header in the profile. The FortiGate will automatically display the corresponding static value. For example, if the administrator selects the $client-ip header, the FortiGate will display the actual client IP address.
The supported headers are:
|
$client-ip |
Client IP address |
|
$user |
Authentication user name |
|
$domain |
User domain name |
|
$local_grp |
Firewall group name |
|
$remote_grp |
Group name from authentication server |
|
$proxy_name |
Proxy realm name |
To configure dynamic headers using the CLI:
Since authentication is required, FSSO NTLM authentication is configured in this example.
- Configure LDAP:
config user ldap edit "ldap-kerberos" set server "172.18.62.220" set cnid "cn"a set dn "dc=fortinetqa,dc=local" set type regular set username "CN=root,CN=Users,DC=fortinetqa,DC=local" set password ********** next end - Configure FSSO:
config user fsso edit "1" set server "172.18.62.220" set password ********** next end - Configure a user group:
config user group edit "NTLM-FSSO" set group-type fsso-service set member "FORTINETQA/FSSO" next end - Configure an authentication scheme:
config authentication scheme edit "au-sch-ntlm" set method ntlm next end - Configure an authentication rule:
config authentication rule edit "au-rule-fsso" set srcaddr "all" set active-auth-method "au-sch-ntlm" next end - Create a web proxy profile that adds a new dynamic and custom
Viaheader:config web-proxy profile edit "test" set log-header-change enable config headers edit 1 set name "client-ip" set content "$client-ip" next edit 2 set name "Proxy-Name" set content "$proxy_name" next edit 3 set name "user" set content "$user" next edit 4 set name "domain" set content "$domain" next edit 5 set name "local_grp" set content "$local_grp" next edit 6 set name "remote_grp" set content "$remote_grp" next edit 7 set name "Via" set content "Fortigate-Proxy" next end next end - In the proxy policy, append the web proxy profile created in the previous step:
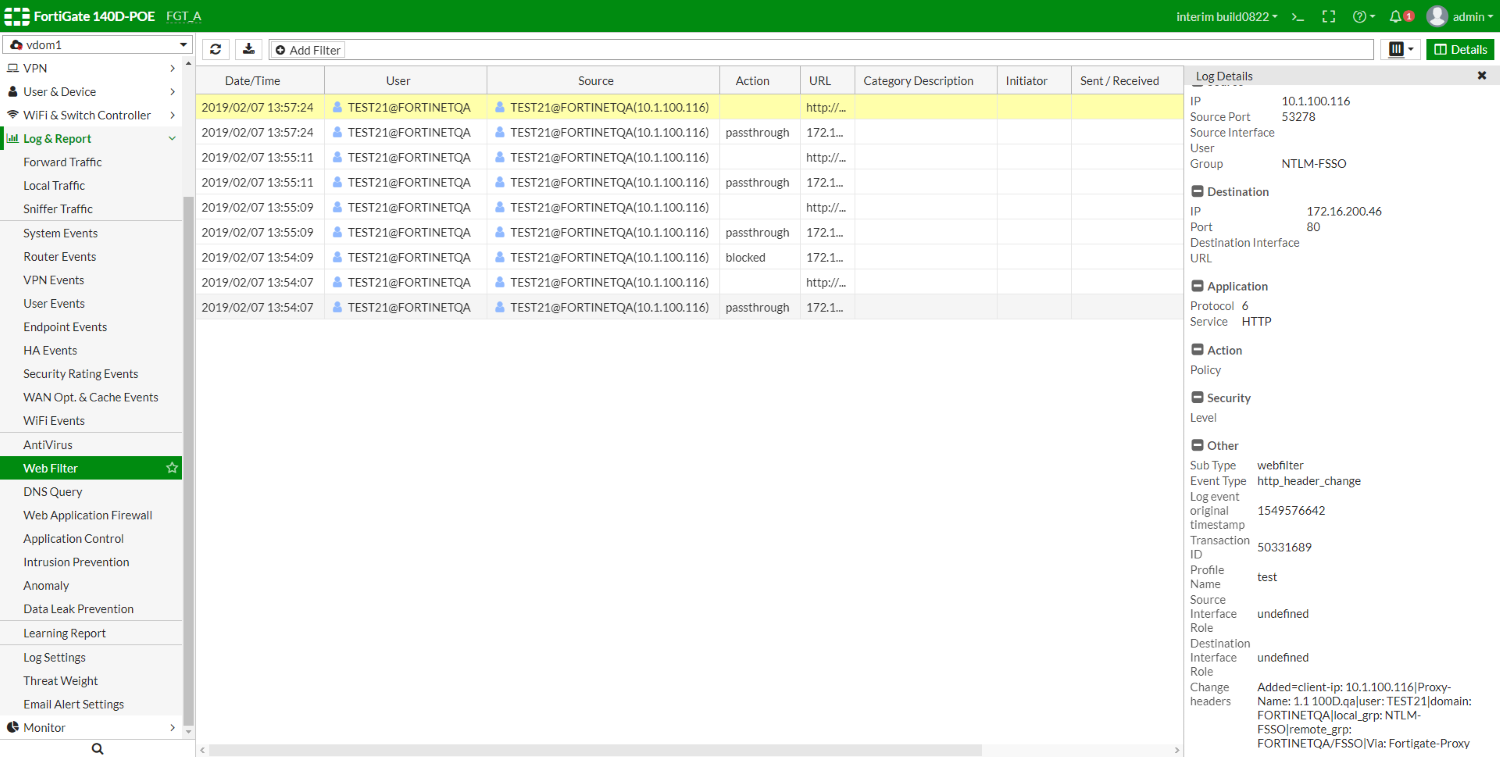
config firewall proxy-policy edit 1 set uuid bb7488ee-2a6b-51e9-45c6-1715bdc271d8 set proxy explicit-web set dstintf "port1" set srcaddr "all" set dstaddr "all" set service "web" set action accept set schedule "always" set logtraffic all set groups "NTLM-FSSO" set webproxy-profile "test" set utm-status enable set av-profile "av" set webfilter-profile "content" set ssl-ssh-profile "deep-custom" next end - Once traffic is being generated from the client, look at the web filter logs to verify that it is working.
The corresponding values for all the added header fields displays in the Change headers section at the bottom of the Log Details pane.
1: date=2019-02-07 time=13:57:24 logid="0344013632" type="utm" subtype="webfilter" eventtype="http_header_change" level="notice" vd="vdom1" eventtime=1549576642 policyid=1 transid=50331689 sessionid=1712788383 user="TEST21@FORTINETQA" group="NTLM-FSSO" profile="test" srcip=10.1.100.116 srcport=53278 dstip=172.16.200.46 dstport=80 srcintf="port2" srcintfrole="undefined" dstintf="port1" dstintfrole="undefined" proto=6 service="HTTP" url="http://172.16.200.46/" agent="curl/7.22.0" chgheaders="Added=client-ip: 10.1.100.116|Proxy-Name: 1.1 100D.qa|user: TEST21|domain: FORTINETQA|local_grp: NTLM-FSSO|remote_grp: FORTINETQA/FSSO|Via: Fortigate-Proxy"