Per-IP traffic shaper
With per-IP traffic shaping, you can limit each IP address's behavior to avoid a situation where one user uses all of the available bandwidth. In addition to controlling the maximum bandwidth used per IP address, you can also define the maximum number of concurrent sessions for an IP address. For example, if you apply a per-IP shaper of 1 Mbps to your entire network, FortiOS allocates each user/IP address 1 Mbps of bandwidth. Even if the network consists of a single user, FortiOS allocates them 1 Mbps. If there are ten users, each user gets 1 Mbps of bandwidth, totaling 10 Mbps of outgoing traffic.
For shared shapers, all users share the set guaranteed and maximum bandwidths. For example, if you set a shared shaper for all PCs using an FTP service to 10 Mbps, all users uploading to the FTP server share the 10 Mbps.
Shared shapers affect upload speed. If you want to limit the download speed from the FTP server in the example, you must configure the shared shaper as a reverse shaper. Per-IP shapers apply the speed limit on both upload and download operations. Only traffic through forward traffic shapers will be included in FortiView; reverse and per-IP shapers are not included.
The following example shows how to apply a per-IP shaper to a traffic shaping policy. This shaper assigns each user a maximum bandwidth of 1 Mbps and allows each user to have a maximum of ten concurrent connections to the FTP server. In the example, FortiOS communicates with users using port10 and the FTP server using port9.
To configure a per-IP traffic shaper in the GUI:
- Create a firewall policy:
- Go to Policy & Objects > IPv4 Policy and click Create New.
- Set the Name to FTP Access.
- Set the Incoming Interface to port10.
- Set the Outgoing Interface to port9.
- Set the Source to all.
- Set the Destination to FTP_Server.
- Set the Schedule to always.
- Set the Service to ALL.
- Click OK.
- Create the per-IP traffic shaper:
- Go to Policy & Objects > Traffic Shapers and click Create New.
- Set Type to Per IP Shaper.
- Set the Name to FTP_Max_1M. This shaper is for VoIP traffic.
- Enable Max Bandwidth and enter 1000.
- Enable Max Concurrent Connections and enter 10. This means that each user can have up to ten concurrent connections to the FTP server.
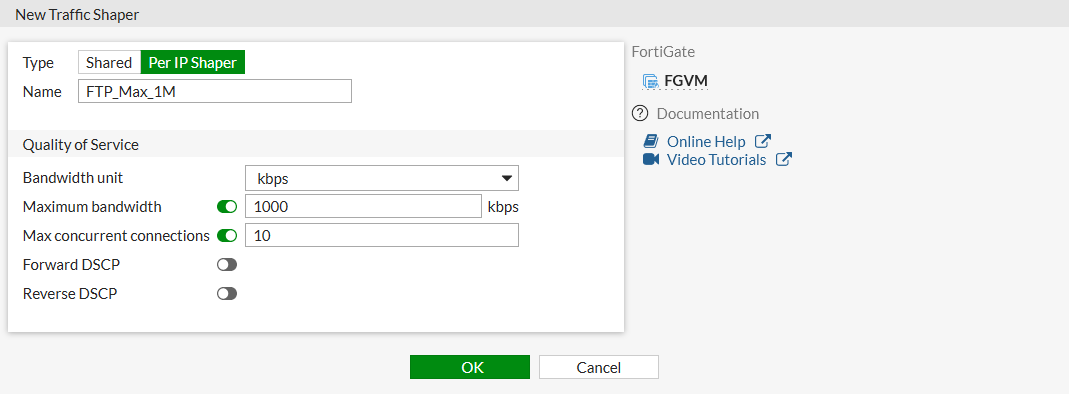
- Click OK.
- Create a firewall shaping policy:
- Go to Policy & Objects > Traffic Shaping Policy and click Create New.
- Set the Name to FTP speed 1M.
- Set the Source to the addresses and users that require access to the FTP server.
- Set the Destination to FTP_Server.
- Set the Service to ALL.
- Set the Outgoing Interface to port9.
- Enable Per-IP shaper and select FTP_Max_1M.
- Click OK.
To configure a per-IP traffic shaper in the CLI:
- Create a firewall policy:
config firewall policy
edit 1
set name "FTP Access"
set srcintf "port10"
set dstintf "port9"
set srcaddr "all"
set dstaddr "FTP_Server"
set action accept
set schedule "always"
set service "ALL"
set fsso disable
set nat enable
next
end
- Create the per-IP traffic shaper:
config firewall shaper per-ip-shaper
edit "FTP_Max_1M"
set max-bandwidth 1000
set max-concurrent-session 10
next
end
- Create a firewall shaping policy:
config firewall shaping-policy
edit 1
set name "FTP speed 1M"
set service "ALL"
set dstintf "port9"
set per-ip-shaper "FTP_Max_1M"
set srcaddr "PC1" "WinPC" "PC2"
set dstaddr "FTP_Server"
next
end
To troubleshoot per-IP traffic shapers:
- To check if specific traffic is attached to the correct traffic shaper, run the
diagnose firewall iprope list 100015command. The example output shows the traffic attached to the FTP_Max_1M shaper:# diagnose firewall iprope list 100015
policy index=3 uuid_idx=0 action=accept
flag (0):
shapers: per-ip=FTP_Max_1M
cos_fwd=0 cos_rev=0
group=00100015 av=00000000 au=00000000 split=00000000
host=2 chk_client_info=0x0 app_list=0 ips_view=0
misc=0 dd_type=0 dd_mode=0
zone(1): 0 -> zone(1): 38
source(3): 10.1.100.11-10.1.100.11, uuid_idx=30, 10.1.100.143-10.1.100.143, uuid_idx=32, 10.1.100.22-10.1.100.22, uuid_idx=31,
dest(1): 172.16.200.55-172.16.200.55, uuid_idx=89,
service(1):
[0:0x0:0/(0,65535)->(0,65535)] helper:auto
- To check if the correct traffic shaper is applied to the session, run the
diagnose sys session listcommand. The example output shows that the FTP_Max_1M shaper is applied to the session:# diagnose sys session list
session info: proto=6 proto_state=01 duration=36 expire=3567 timeout=3600 flags=00000000 sockflag=00000000 sockport=0 av_idx=0 use=4
origin-shaper=
reply-shaper=
per_ip_shaper=FTP_Max_1M
class_id=0 shaping_policy_id=3 ha_id=0 policy_dir=0 tunnel=/ helper=ftp vlan_cos=0/255
state=may_dirty per_ip npu npd mif route_preserve
statistic(bytes/packets/allow_err): org=506/9/1 reply=416/6/1 tuples=2
tx speed(Bps/kbps): 0/0 rx speed(Bps/kbps): 0/0
orgin->sink: org pre->post, reply pre->post dev=39->38/38->39 gwy=172.16.200.55/0.0.0.0
hook=post dir=org act=snat 10.1.100.11:58275->172.16.200.55:21(172.16.200.1:58275)
hook=pre dir=reply act=dnat 172.16.200.55:21->172.16.200.1:58275(10.1.100.11:58275)
pos/(before,after) 0/(0,0), 0/(0,0)
misc=0 policy_id=1 auth_info=0 chk_client_info=0 vd=2
serial=0000211a tos=ff/ff app_list=0 app=0 url_cat=0
rpdb_link_id = 00000000
dd_type=0 dd_mode=0
npu_state=0x100000
npu info: flag=0x00/0x00, offload=0/0, ips_offload=0/0, epid=0/0, ipid=0/0, vlan=0x0000/0x0000
vlifid=0/0, vtag_in=0x0000/0x0000 in_npu=0/0, out_npu=0/0, fwd_en=0/0, qid=0/0
no_ofld_reason: offload-denied helper
- To check statuses of per-IP traffic shapers, run the
diagnose firewall shaper per-ip-shaper listcommand. The output should resemble the following:# diagnose firewall shaper per-ip-shaper list
name FTP_Max_1M
maximum-bandwidth 125 KB/sec
maximum-concurrent-session 10
tos ff/ff
packets dropped 0
bytes dropped 0
addr=10.1.100.11 status: bps=0 ses=3

