External malware blocklist for antivirus
External Malware Blocklist is a new feature introduced in FortiOS 6.2.0 which falls under the umbrella Outbreak Prevention.
This feature provides another means of supporting the AV Database by allowing users to add their own malware signatures in the form of MD5, SHA1, and SHA256 hashes.
This feature provides a mechanism for Antivirus to retrieve an external malware hash list from a remote server and polls the hash list every n minutes for updates.
Support and limitations
Malware detection using External Malware Blocklist can be used in both proxy-based and flow-based policy inspections.
Just like FortiGuard Outbreak Prevention, External Dynamic Block List is not supported in AV quick scan mode.
Using different types of hash simultaneously may slow down the performance of malware scanning. For this reason, users are recommended to only using one type of hash (either MD5, SHA1, or SHA256), not all three simultaneously.
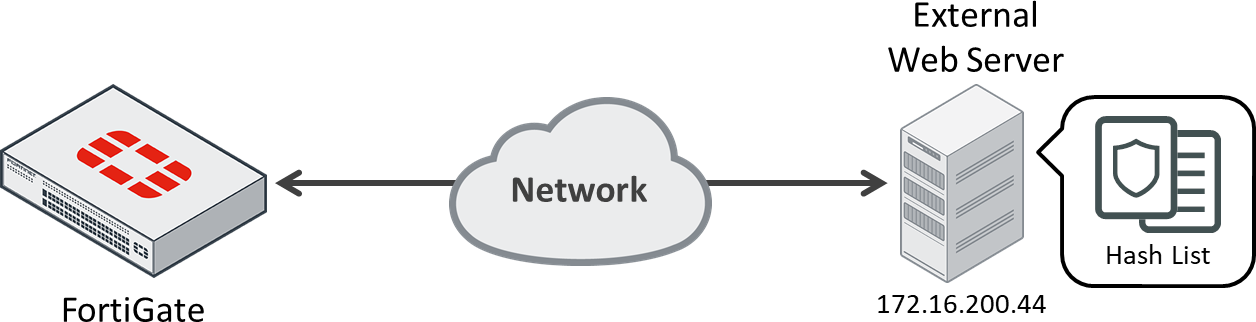
Network topology example
Configuring the feature
To configure antivirus to work with External Block List:
- Creating the Malware Hash List
- Configure External Malware Blocklist source:
- Create a new external source on Global > Security Fabric > Fabric Connectors page.

- Select Malware Hash.

- Fill out the fields as shown. The URI should point to the malware hashlist on the remote server.

- Click OK.
The malware hash source object is now created.

The user can view entries inside the malware blocklist by clicking the View Entries button:

The Malware Has Threatfeed hash_list is shown.

- Create a new external source on Global > Security Fabric > Fabric Connectors page.
- Enable External Malware Blocklist in antivirus profile:
- Enable External Malware Blocklist on the antivirus profile and apply the change

Antivirus is now ready to use the external malware blocklist.
- Enable External Malware Blocklist on the antivirus profile and apply the change
The malware hash list follows a strict format in order for its contents to be valid. Malware hash signatures entries must be separated into each line. A valid signature needs to follow the format below:
# MD5 Entry with hash description aa67243f746e5d76f68ec809355ec234 md5_sample1 # SHA1 Entry with hash description a57983cb39e25ab80d7d3dc05695dd0ee0e49766 sha1_sample2 # SHA256 Entry with hash description ae9bc0b4c5639d977d720e4271da06b50f7c60d1e2070e9c75cc59ab30e49379 sha256_sample1 # Entry without hash description 0289b0d967cb7b1fb1451339c7b9818a621903090e0020366ab415c549212521 # Invalid entries 7688499dc71b932feb126347289c0b8a_md5_sample2 7614e98badca10b5e2d08f8664c519b7a906fbd5180ea5d04a82fce9796a4b87sha256_sample3
Diagnostics and debugging
Check if the scanunit daemon has updated itself with the external hashes:
FGT_PROXY # config global FGT_PROXY (global) # diagnose sys scanunit malware-list list md5 'aa67243f746e5d76f68ec809355ec234' profile 'hash_list' description 'md5_sample1' sha1 'a57983cb39e25ab80d7d3dc05695dd0ee0e49766' profile 'hash_list' description 'sha1_sample2' sha256 '0289b0d967cb7b1fb1451339c7b9818a621903090e0020366ab415c549212521' profile 'hash_list' description '' sha256 'ae9bc0b4c5639d977d720e4271da06b50f7c60d1e2070e9c75cc59ab30e49379' profile 'hash_list' description 'sha256_sample1'

