MAP-E support
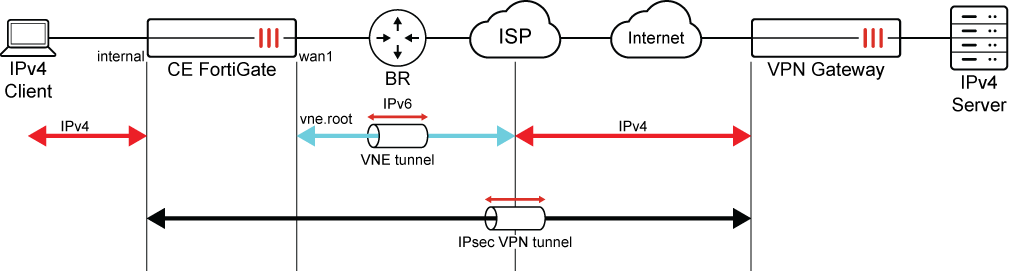
On a customer edge (CE) FortiGate, an IPv4-over-IPv6 (MAP-E) tunnel can be created between the FortiGate and the border relay (BR) operating in an IPv6 network. A tunnel interface is created between the FortiGate and BR, which can be applied to firewall policies and IPsec VPN.
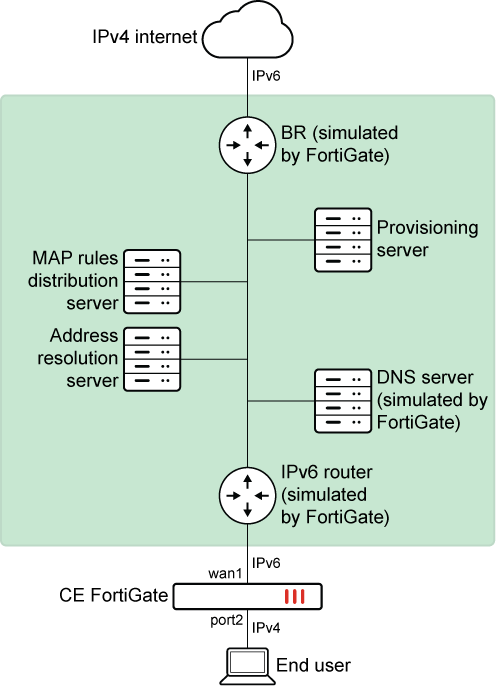
To configure a MAP-E tunnel between the FortiGate and the BR:
-
Configure fixed IP mode.
-
Configure IPv6 on the interface:
config system interface edit "wan1" config ipv6 set autoconf enable set unique-autoconf-addr enable set interface-identifier ::6f:6c1f:3400:0 end next endThe
interface-identifieris an IPv6 address. Its last 64-bit will be kept and the rest will be cleared automatically. It will combine with the IPv6 prefix it gets from the IPv6 router to generate the IPv6 address of the interface.By default,
unique-autoconf-addris disabled. It must be enabled so it can handle IPv6 prefix changing. -
Configure the VNE tunnel:
config system vne-interface edit vne1 set interface "wan1" set mode fixed-ip set ipv4-address 10.10.81.81 255.255.255.255 set br 2001:160::82 set update-url http://qa.forosqa.com/update?user=xxxx&pass=yyyy next end
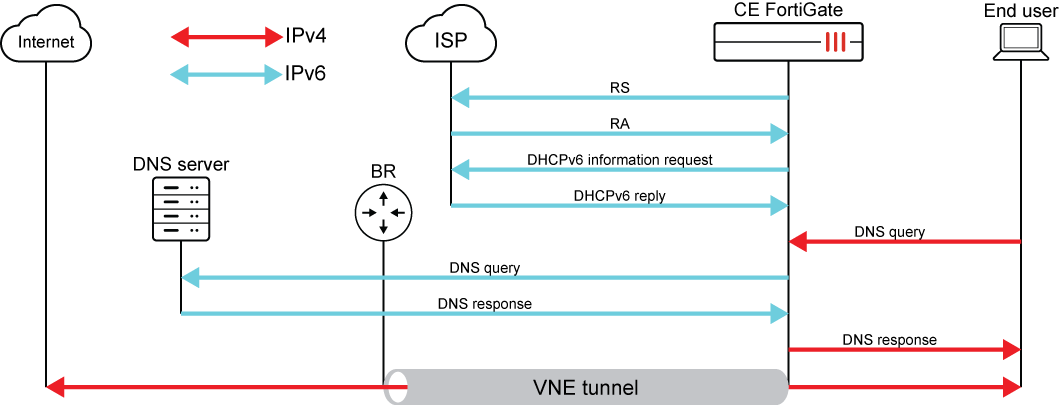
Initial sequence overview of VNE tunnel under fixed IP mode:
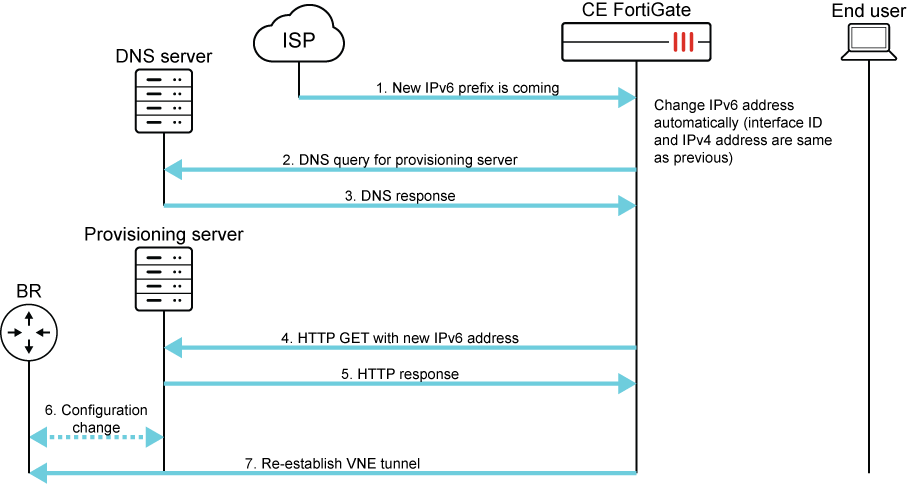
Once the IPv6 address of the FortiGate changes, the tunnel will be down because the BR does not know the FortiGate's new IPv6 address. The FortiGate uses
update-urlto update the new IPv6 address to the provisioning server. The provisioning server updates the FortiGate’s IPv6 address to the BR so the VNE tunnel can be re-established.Communication sequence overview of re-establishing VNE tunnel:
-
-
Configure the VNE tunnel to use MAP-E mode:
config system vne-interface edit vne1 set interface 'wan1' set ssl-certificate "Fortinet_Factory" set bmr-hostname ******** set auto-asic-offload enable set mode map-e next endInitial sequence overview of VNE tunnel under MAP-E mode:
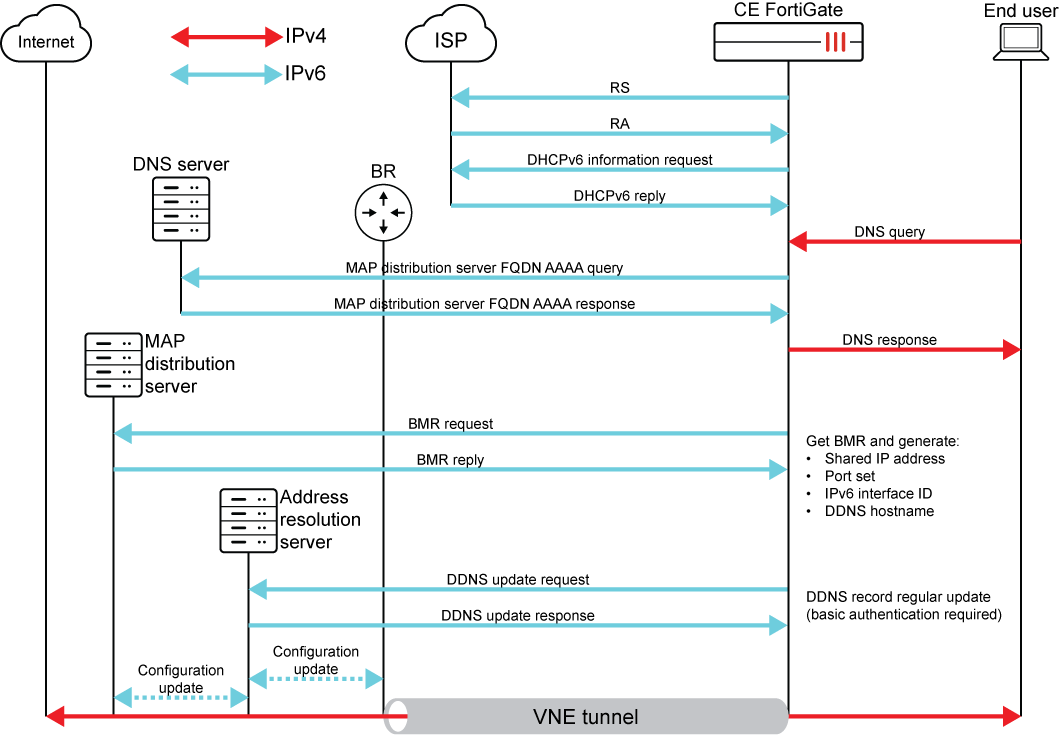
The FortiGate sends a MAP rule request to the MAP distribution server once the IPv6 address is configured on the FortiGate by RS/RA. Next, the FortiGate will send an AAAA query to get the IPv6 address of the MAP distribution server. After sending the BMR request to the MAP distribution server, the FortiGate will get the IPv4 address, port set, BR IPv6 address, and hostname of the address resolution server from the BMR reply. The VNE tunnel between the FortiGate and BR is now established.
The address resolution server is actually a dynamic DNS. The hostname is used for the FortiGate to maintain an IPv6 address when it changes.
The FortiGate updates the DDNS server with its IPv6 address whenever it updates, which in turn provides the update to the MAP distribution server and BR so they know how to resolve the FortiGate by hostname.
Once the VNE tunnel is established, an IPv4-over-IPv6 tunnel is set up between the FortiGate and BR. The route, firewall policy, and DNS server can now be configured to let the traffic go through the VNE tunnel and protect the end-user. The VNE tunnel can also be used in IPsec phase 1.
-
Configure the route:
config router static edit 1 set device "vne1" next end -
Configure the firewall policy:
config firewall policy edit 111 set name "ff" set srcintf "port2" set dstintf "vne1" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" set utm-status enable set ssl-ssh-profile "certificate-inspection" set av-profile "default" set nat enable next end -
Configure the DNS server:
config system dns-server edit "port2" next end
MAP-E can also operate in DHCPv6-PD environments; see DHCP-PD support for MAP-E for more information.
IPsec over VNE and offloading
In some scenarios, after the VNE tunnel is established, users might want to build IPsec tunnels over VNE for end-to-end encryption. This allows IPsec traffic to be encapsulated within the VNE tunnel to pass through the IPv6 ISP infrastructure and stay encrypted as it reaches the VPN Gateway and final destination.
In these scenarios, NP-offloading (NP7 and NP7Lite) is supported over the IPsec tunnel when the following criteria are met:
-
The interface settings of the IPsec phase1-interface must be either a physical, trunk, or npu-vlink interface, or a VLAN on one of these interfaces.
-
The interface setting of the IPsec phase1-interface cannot be set to the VNE tunnel interface.
-
If the npu-vlink is used, the VNE and IPsec tunnels must be in different VDOMs.

