Adding a security posture tag
To add a security posture tag:
- Go to Security Posture Tags > Tags, and click Create.
- In the Name field, enter the desired tag name.
- In the User Notification Message field, enter a message that explains to the end user why FortiOS denied their access. In FortiOS in Policy & Objects > ZTNA > Security Posture Tags, the Comments column displays the configured user notification message for a tag.
- Toggle Enabled on or off to enable or disable the rule.
- (Optional) In the Comments field, enter any desired comments.
- Click Add Rule.
- Configure the rules:
- For OS, select the desired OS. This affects what rule types are available.
- From the Rule Type dropdown list, select the rule type and configure the related options. Ensure that you click the + button after entering each criterion. See Security posture tagging rule types for descriptions of the rule types.
- Click Save.
- Configure additional rules as desired.
- By default, an endpoint must satisfy all configured rules to be eligible for the tag. You may want to apply the tag to endpoints that satisfy some, but not all, of the configured rules. In this case, you can modify the rule set logic. For example, consider that you want to apply the same tag to endpoints that fulfill one of the following criteria:
- Running Windows 10
- Running FortiClient 7.4.2 and antivirus (AV) software is installed and running
With the default logic, an endpoint would be eligible for the rule set if it is running Windows 10 and FortiClient 7.4.2 and has AV software installed and running. To modify the rule set logic, do the following:
- Click Edit Logic.
- Clicking Edit Logic assigns numerical values to each configured rule. In the Rule Logic field, enter the desired logic for the rule set using the numerical values. You can use
andandorto define the rule logic. You cannot usenotwhen defining the rule logic. You can also use parentheses to group rules. For this example, you would enter(1 and 3) or 2, to indicate that endpoints that satisfy both the AV and FortiClient 7.4.2 rules (rules 1 and 3) or only the Windows 10 rule (rule 2) satisfy the rule set. To restore the default logic, you can click Default Logic.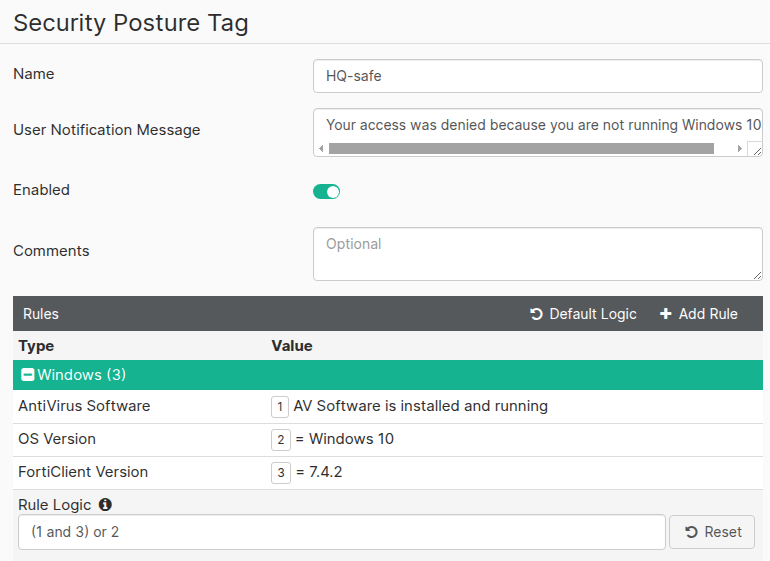
- Click Save.
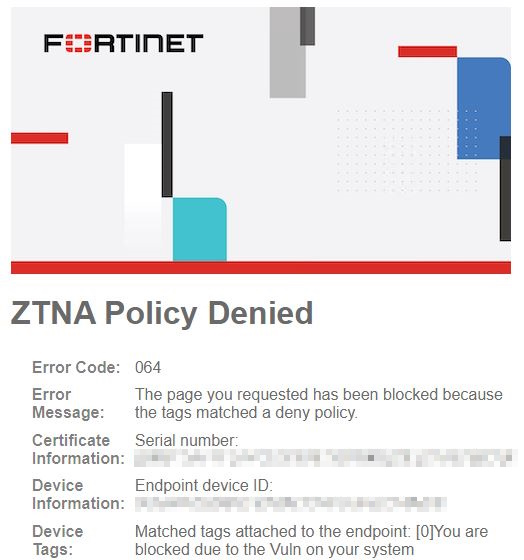
The following shows a ZTNA Policy Denied page. It shows the user notification message in the Device Tags field.