Log settings and targets
Log settings determine what information is recorded in logs, where the logs are stored, and how often storage occurs. Log settings can be configured in the GUI and CLI. In the GUI, Log & Report > Log Settings provides the settings for local and remote logging.
Log & Report > Log Settings is organized into tabs:
Global Settings
Settings available in the Global Settings tab include:
|
UUIDs in Traffic Log |
||
|
|
Policy |
Define the use of policy UUIDs in traffic logs:
|
|
|
Address |
Define the use of address UUIDs in traffic logs:
|
|
Log Settings |
||
|
|
Event Logging |
Define the allowed set of event logs to be recorded:
|
|
|
Local Traffic Log |
Define the allowed set of traffic logs to be recorded:
|
|
GUI Preferences |
||
|
|
Resolve Hostnames |
Define the translation of IP addresses to host names:
|
|
|
Resolve Unknown Applications |
Define the resolution of unknown applications:
|
Local Logs
Settings available in the Local Logs tab include:
| Local Logs | ||
| Disk logging |
Define local log storage on the FortiGate:
|
|
| Local Reports |
Define log reporting on the FortiGate:
|
|
| Historical FortiView |
Define the presentation of log information on FortiView:
|
|
|
|
Disk Usage |
Presents the disk space used and the total disk space available on the disk. |
Threat Weight
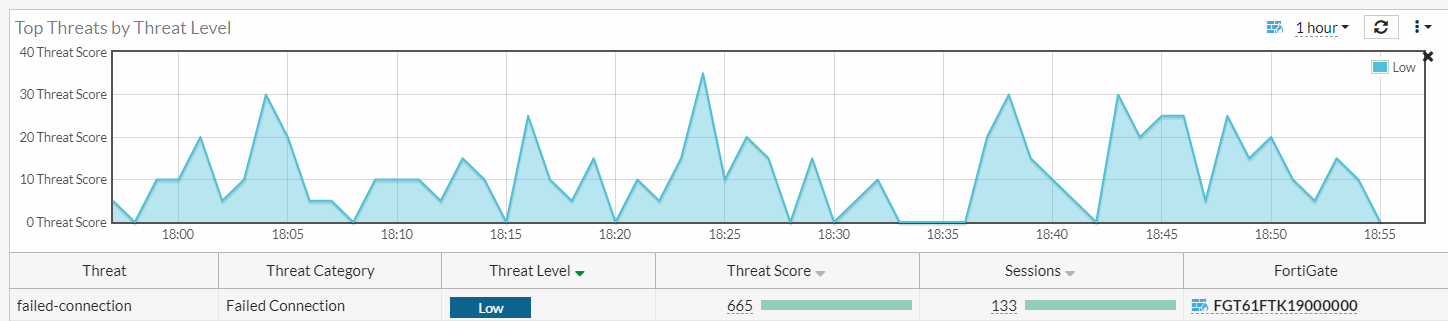
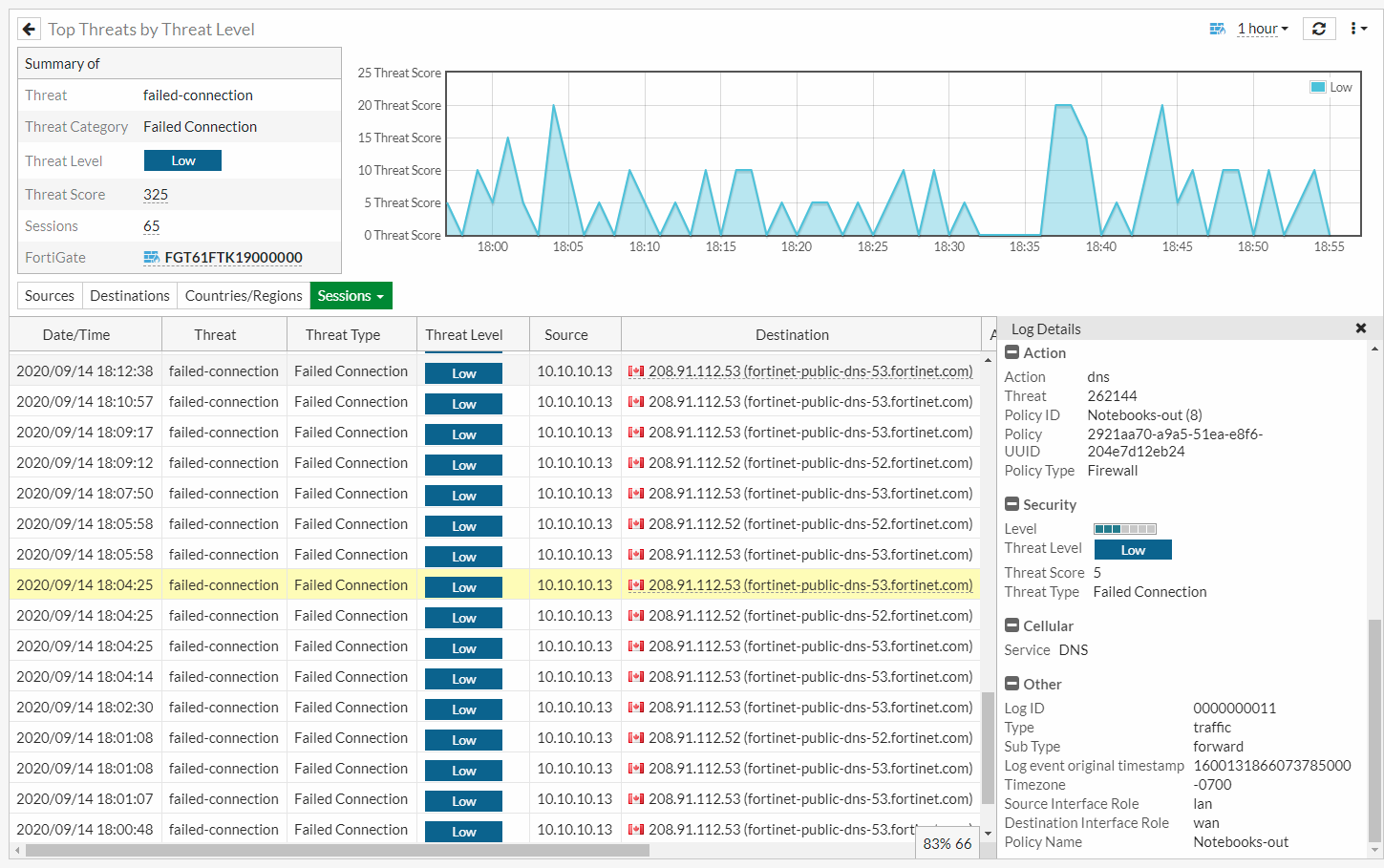
Threat weight helps aggregate and score threats based on user-defined severity levels. It adds several fields such as threat level (crlevel), threat score (crscore), and threat type (craction) to traffic logs. Threat weight logging is enabled by default and the settings can be customized. Threats can be viewed from the Top Threats FortiView dashboard.
To configure threat weight settings:
- Go to Log & Report > Log Settings and select the Threat Weight tab.
- Adjust the settings as needed, such as individual weights per threat type and risk level values.
- Click Apply.
To add the Top Threats monitor to the dashboard:
- In the tree menu, click Dashboard and in the FortiView section, click the + sign (Add Monitor).
- In the Security section, enable Show More and click Top Threats.
- Configure the settings as needed.
- Click Add Monitor.
- Go to Dashboard > Top Threats. The Top Threats monitor displays threats based on the scores in the traffic logs.
- Double-click a threat to view the summary.
- Click Sources, Destinations, Countries/Regions, or Sessions to view more information. Double-click an entry to view the log details.
Configuring logs in the CLI
The FortiGate can store logs locally to its system memory or a local disk. Logs can also be stored externally on a storage device, such as FortiAnalyzer, FortiAnalyzer Cloud, FortiGate Cloud, or a syslog server.
Disk logging
Disk logging must be enabled for logs to be stored locally on the FortiGate. By default, logs older than seven days are deleted from the disk. Log age can be configured in the CLI. Approximately 75% of disk space is available for log storage. Log storage space can be determined using the diagnose sys logdisk usage command.
To configure local disk logging:
config log disk setting
set status enable
set maximum-log-age <integer>
set max-log-file-size <integer>
end
Remote logging
The process to configure FortiGate to send logs to FortiAnalyzer or FortiManager is identical. Remote logging to FortiAnalyzer and FortiManager can be configured using both the GUI and CLI. When using the CLI, use the config log fortianalyzer setting command for both FortiAnalyzer and FortiManager.
If VDOMs are configured on the FortiGate, multiple FortiAnalyzers and syslog servers can be added globally. See Configuring multiple FortiAnalyzers (or syslog servers) per VDOM and Configuring multiple FortiAnalyzers on a FortiGate in multi-VDOM mode for more information.
To configure remote logging to FortiAnalyzer:
config log fortianalyzer setting
set status enable
set server <server_IP>
set upload option {store-and-upload | realtime | 1-minute | 5-minute}
end
Remote logging can also be configured to FortiCloud, FortiSIEM, and syslog servers. Up to four syslog servers or FortiSIEM devices can be configured using the config log syslogd command and can send logs to syslog in CSV and CEF formats.
To configure remote logging to FortiCloud:
config log fortiguard setting
set status enable
set source-ip <source IP used to connect FortiCloud>
end
To configure remote logging to a syslog server:
config log syslogd setting
set status enable
set server <syslog_IP>
set format {default | csv | cef | rfc5424 | json}
end
Log filters
Log filter settings can be configured to determine which logs are recorded to the FortiAnalyzer, FortiManager, and syslog servers. This allows certain logging levels and types of logs to be directed to specific log devices.
To configure log filters for FortiAnalyzer:
config log fortianalyzer filter
set severity <level>
set forward-traffic {enable | disable}
set local-traffic {enable | disable}
set multicast-traffic {enable | disable}
set sniffer-traffic {enable | disable}
end
To configure log filters for a syslog server:
config log syslogd filter
set severity <level>
set forward-traffic {enable | disable}
set local-traffic {enable | disable}
set multicast-traffic {enable | disable}
set sniffer-traffic {enable | disable}
end
Email alerts
FortiGate events can be monitored at all times using email alerts. Email alerts send notifications to up to three recipients and can be triggered based on log event and severity level. Email alerts will be sent every five minutes by default but this can be configured in the CLI.
To configure email alerts:
config alertemail setting
set username <name>
set mailto1 <email>
set filter-mode {category | threshold}
set email-interval <integer>
set IPS-logs {enable | disable}
set HA-logs {enable | disable}
set antivirus-logs {enable | disable}
set webfilter-logs {enable | disable}
set log-disk-usage-warning {enable | disable}
end

