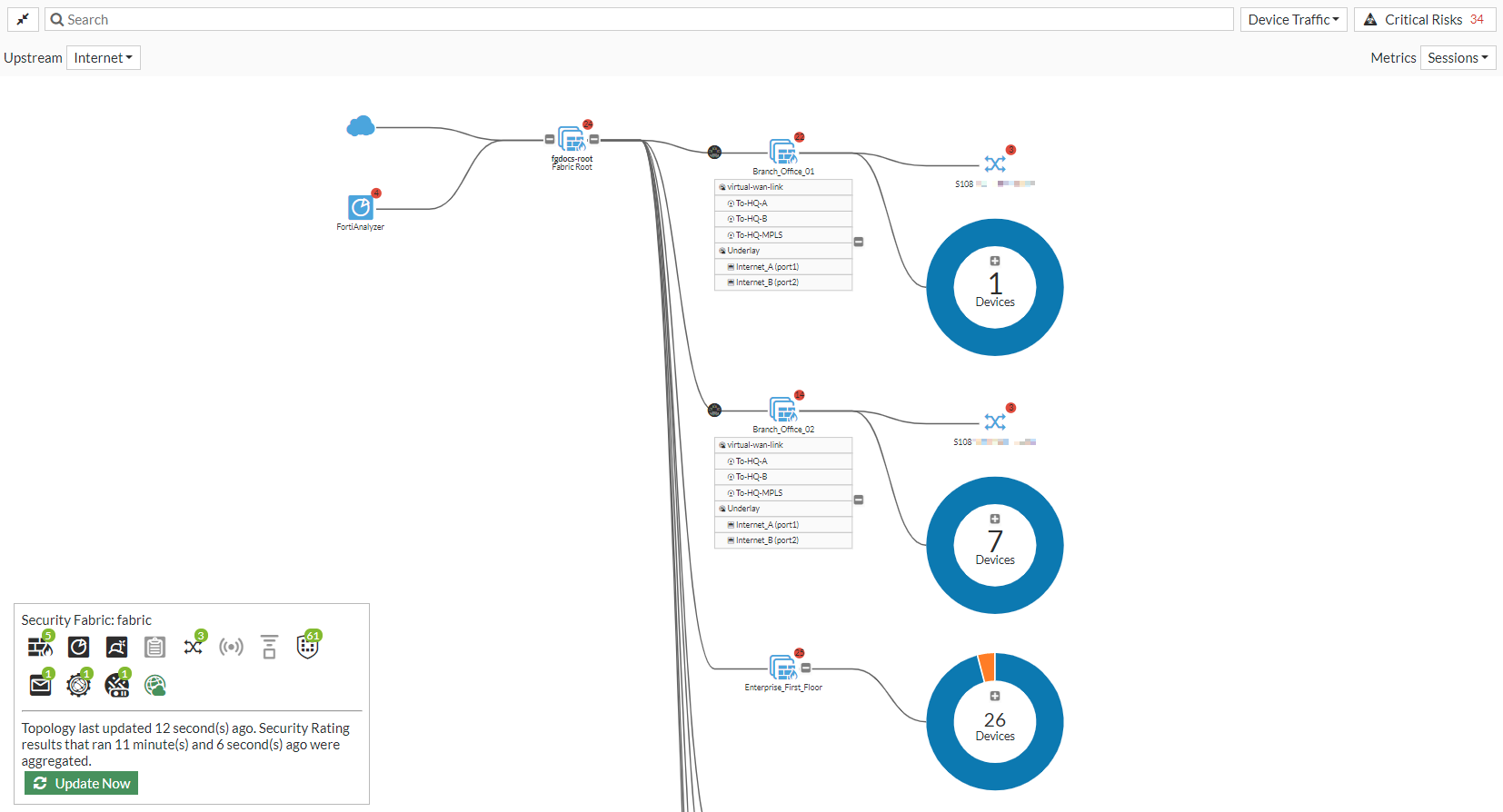
Topology
The full Security Fabric topology can be viewed on the root FortiGate. Downstream FortiGate devices' topology views do not include upstream devices.
The Physical Topology page shows the physical structure of your network, including all connected devices and the connections between them. The Logical Topology page shows information about the interfaces that connect devices to the Security Fabric.
In both topology pages, you can use filtering and sorting options to control the information that is shown. Hover the cursor over a device icon, port number, or endpoint to open a tooltip that shows information about that specific device, port, or endpoint. Right-click on a device to log into, configure, or deauthorize it. Right-click on an endpoint to perform various tasks, such as drilling down for more details in FortiView, quarantining the host, and banning the IP address.
The small number that might be shown in the top right corner of a device icon is the number of security ratings recommendations or warnings for that device. The circle color indicates the severity of the highest security rating check that failed. Clicking it opens the Security Rating page. See Security rating for more information.
Views
From the dropdown list beside the search bar, select one of the following views:
- Device Traffic: organize devices by traffic.
- Device Count: organize devices by the number of devices connected to it.
- Device Operating System: organize devices by operating system.
- Device Hardware Vendor: organize devices by hardware vendor.
- Risk: only include devices that have endpoints with medium, high, or critical risk values of the specified type: All, Compromised Host, Vulnerability, or Threat Score.
- No Devices: do not show endpoints.
Endpoint groups
The Device Traffic and Device Count views display endpoint groups as donut charts, with the total number of endpoints in the group in the center of the chart. Each sector of the donut chart represents a different endpoint operating system.
To zoom in on a donut chart, click any chart sector. Each sector represents a different endpoint OS. Hovering over each sector allows you to see the OS that the sector represents and the number of endpoints that have that OS installed.

In this example, the endpoint group contains a total of nine endpoints, with the following OSes installed:
| Donut sector color | OS | Number of endpoints |
|---|---|---|
| Orange | Linux | 2 |
| Green | FortiMail | 1 |
| Red | FortiManager | 1 |
| Blue | Other | 5 |
To view the endpoint group in a bubble pack display, click the + button in the center of the donut chart. You can view each individual endpoint in the bubble pack view.
FortiAP and FortiSwitch devices
Newly discovered FortiAP and FortiSwitch devices are initially shown in the topologies with gray icons to indicate that they have not been authorized. To authorize a device, click on the device icon or name and select Authorize. Once authorized, the device icon will turn blue.
Right-click on an authorized FortiAP device to Deauthorize or Restart the device. Right-click on a FortiSwitch device to Deauthorize, Restart, or Upgrade the device, or to Connect to the CLI.
FortiAP and FortiSwitch links are enhanced to show link aggregation groups for the inter-switch link (ISL-LAG). To differentiate them from physical links, ISL-LAG links are shown with a thicker line. The endpoint circles can also be used as a reference to identify ISL-LAG groups that have more than two links.
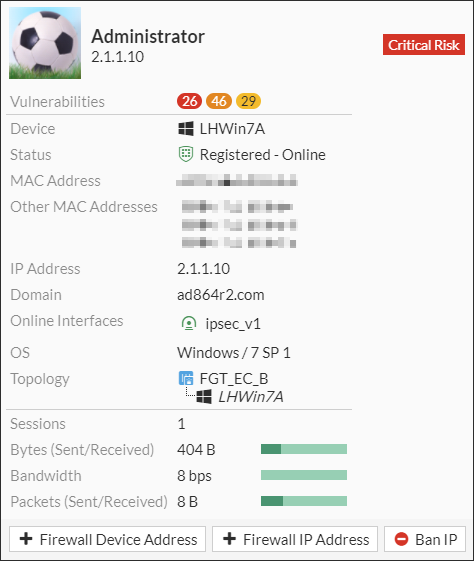
Managed clients connected over a VPN
When managed clients are connected over a VPN, EMS collects user information about these registered clients, such as the VPN connection information. The FortiGate can synchronize this user information from EMS and display it in the logical topology view to provide a detailed picture of clients and their associated VPN interfaces.
Client using an IPsec VPN interface:
Client using an SSL VPN interface:

Critical risks
Click the Critical Risks button to see a list of endpoints that are deemed critical risks, organized by threat severity. These are the red endpoints in the current topology view.
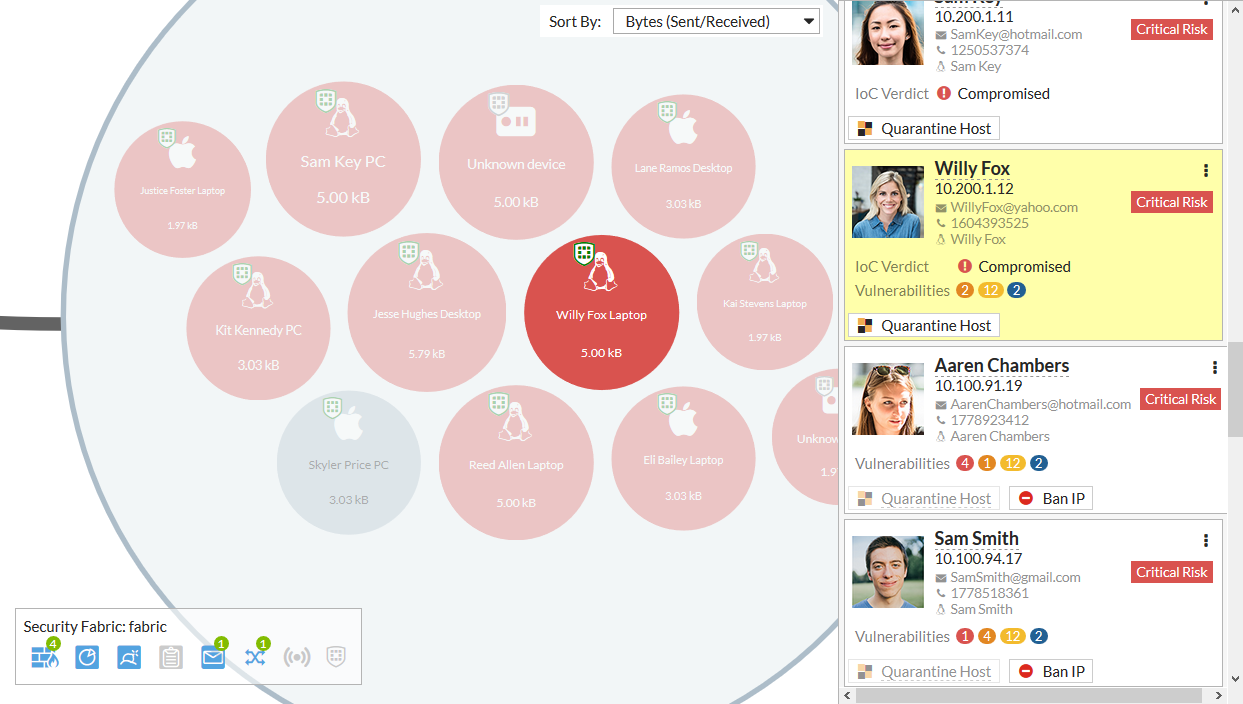
For each endpoint, the user's photo, name, IP address, email address, and phone number are shown. The number of vulnerabilities of each severity is shown, and if the IoC verdict is that the endpoint is compromised.
If applicable, the endpoint's host can be quarantined (click Quarantine Host) or their IP address can be banned (click Ban IP).
The dropdown menu also provides options to drill down to more information on compromised hosts or endpoint vulnerabilities.
Consolidated risk view
The consolidated Risk view mode displays different risks within the Security Fabric topology. You can use the Risk view mode to filter threats by Compromised Hosts, Vulnerability, and Threat Score.
To access the consolidated risk view mode:
-
On one of the topology pages, in the view option dropdown list beside the search bar, select Risk.

-
Select one of the following options from the Risk Type dropdown menu:
-
All
-
Compromised Hosts
-
Vulnerability
-
Threat Score
-
-
When devices fit into the risk metric, they will appear in the endpoint groups. Click the + in the endpoint group to display the devices in a bubble chart.
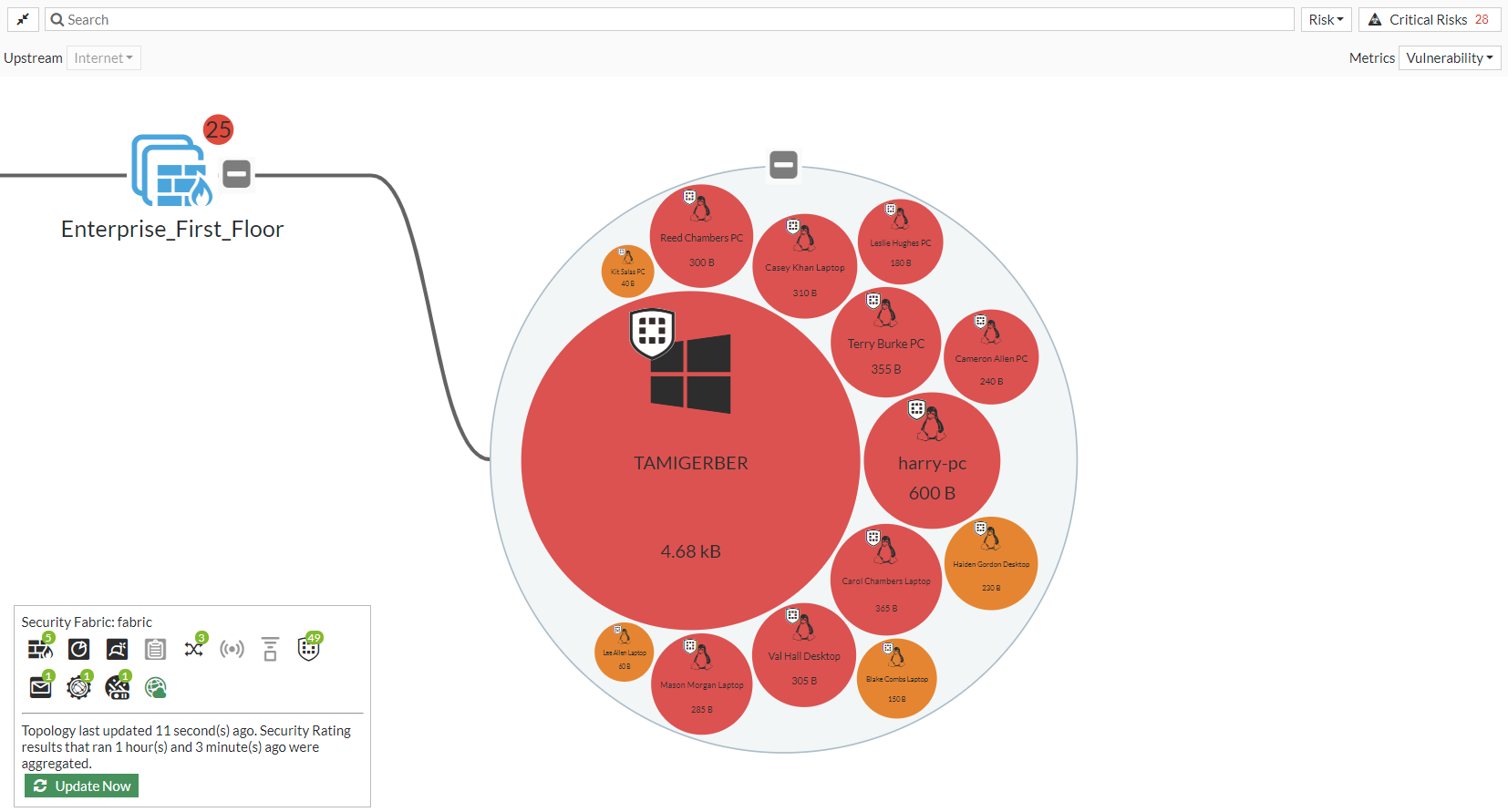
Viewing and controlling network risks in topology view
On the physical and logical topology pages, you can view and control compromised hosts. Compromised hosts behind a FortiSwitch or FortiAP can be quarantined.
To view a compromised endpoint host:
- Test that FortiGate detects a compromised endpoint host by opening a browser on the endpoint host and entering a malicious website URL. The browser displays a Web Page Blocked! warning and does not allow access to the website.
- On the root FortiGate, go to Security Fabric > Physical Topology or Security Fabric > Logical Topology. Expand the endpoint group connected to a FortiSwitch or FortiAP.
The endpoint host connected to the switch is highlighted in red. Mouse over the endpoint host to view a tooltip that shows the IoC verdict. The endpoint host is compromised.

To quarantine a compromised endpoint host:
-
On the Physical Topology or Logical Topology page, right-click the endpoint host and select Quarantine Host.
A dialog displays the FortiGate, host MAC address, and description of the host to be quarantined. Quarantine entries for each MAC address will be created on the FortiGate that the FortiSwitch or FortiAP is connected to.
-
Click OK.
-
Go to Dashboard > User & Devices and click the Quarantine widget to expand it.
-
In the top-right corner, use the dropdown to select the FortiGate in which this host was quarantined. In this example, it is the Enterprise_Second_Floor FortiGate.

-
On the endpoint host, open a browser and visit a website such as https://www.fortinet.com/. If the website cannot be accessed, this confirms that the endpoint host is quarantined.
To show the quarantined device from the CLI:
-
Log in to the downstream device where the host was quarantined (Enterprise_Second_Floor).
-
Enter the following show command:
Enterprise_Second_Floor # show user quarantine config user quarantine set firewall-groups "QuarantinedDevices" config targets edit "Erin Malone PC" set description "Manually quarantined" config macs edit **:**:**:**:**:** set description "manual-qtn Hostname: Erin Malone PC" next end next end end

