Dual stack IPv4 and IPv6 support for SSL VPN
Dual stack IPv4 and IPv6 support for SSL VPN servers and clients enables a client to establish a dual stack tunnel to allow both IPv4 and IPv6 traffic to pass through. FortiGate SSL VPN clients also support dual stack, which allows it to establish dual stack tunnels with other FortiGates.
Users connecting in web mode can connect to the web portal over IPv4 or IPv6. They can access bookmarks in either IPv4 or IPv6, depending on the preferred DNS setting of the web portal.
Example
In this example, FortiGate B works as an SSL VPN server with dual stack enabled. A test portal is configured to support tunnel mode and web mode SSL VPN.

FortiGate A is an SSL VPN client that connects to FortiGate B to establish an SSL VPN tunnel connection. It attempts to access www.bing.com and www.apple.com via separate IPv4 and IPv6 connections. Two addresses are configured on FortiGate B:
- bing.com uses IPv4 FQDN and resolves to 13.107.21.200 and 204.79.197.200.
- apple_v6 uses IPv6 FQDN and resolves to 2600:140a:c000:385::1aca and 2600:140a:c000:398::1aca.
The server certificate used is fgt_gui_automation, and the CN is *.fos.automation.com.
A PC serves as a client to connect to FortiGate B in SSL VPN web mode. The PC can connect to the SSL VPN server over IPv4 or IPv6. Based on the preferred DNS setting, it will access the destination website over IPv4 or IPv6.
|
|
Dual stack tunnel mode support requires a supported client. In 7.0.0, a FortiGate in SSL VPN client mode can support dual stack tunnels. FortiClient 7.0.1 and later releases support dual stack. |
To configure an SSL VPN server in tunnel and web mode with dual stack support in the GUI:
-
Create a local user:
-
Go to User & Authentication > User Definition and click Create New. The Users/Groups Creation Wizard opens.
-
Set the User Type to Local User and click Next.
-
Enter the Username (client2) and password, then click Next.
-
Optionally, configure the contact information and click Next.
-
Click Submit.
-
-
Configure the addresses:
-
Go to Policy & Objects > Addresses and click Create New > Address.
-
Enter the following for the IPv4 address:
Category
Address
Name
bing.com
Type
FQDN
FQDN
www.bing.com
-
Click OK.
-
Click Create New > Address and enter the following for the IPv6 address:
Category
IPv6 Address
Name
apple_v6
Type
FQDN
FQDN
www.apple.com
-
Click OK.
-
-
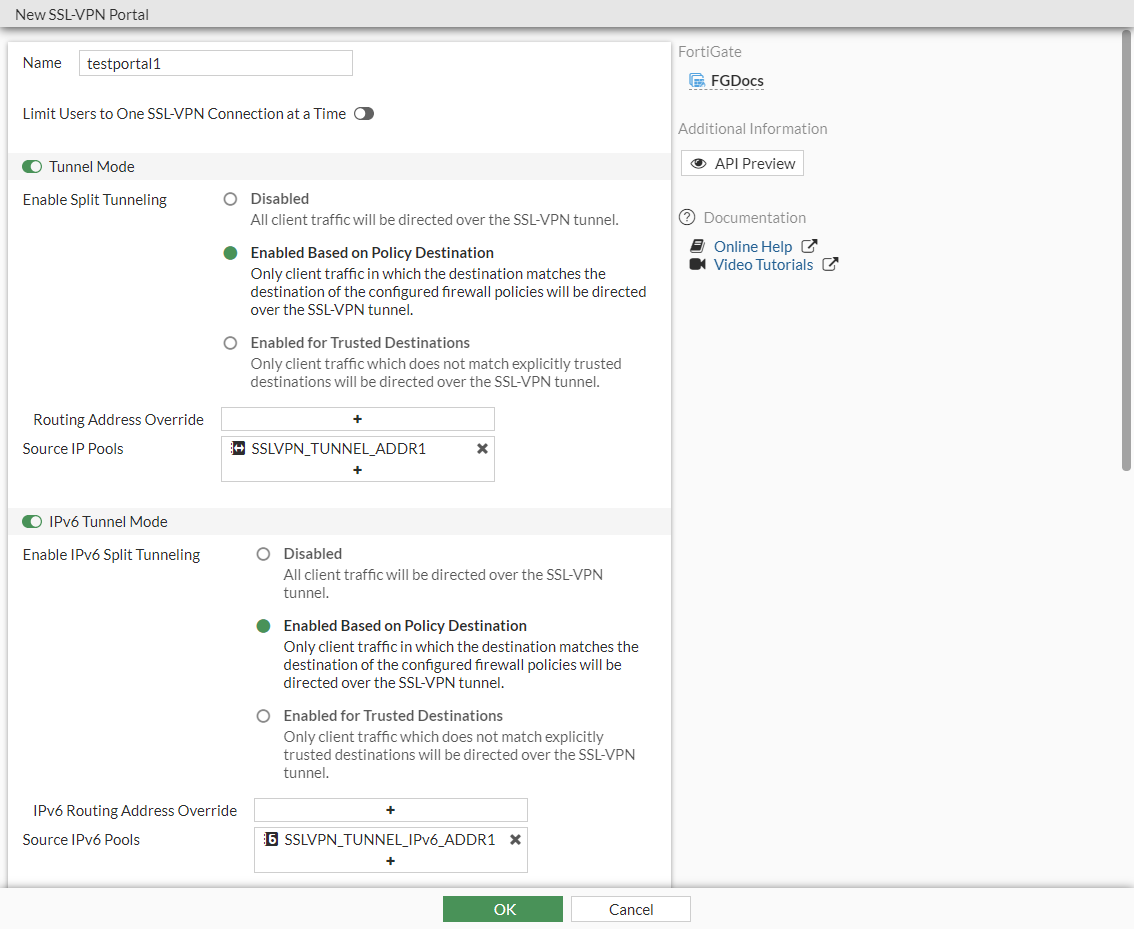
Configure the SSL VPN portal:
-
Go to VPN > SSL-VPN Portals and click Create New.
-
Enter a name (testportal1).
-
Enable Tunnel Mode and for Enable Split Tunneling, select Enable Based on Policy Destination.
-
For Source IP Pools, add SSLVPN_TUNNEL_ADDR1.
-
Enable IPv6 Tunnel Mode and for Enable Split Tunneling, select Enable Based on Policy Destination.
-
For Source IP Pools, add SSLVPN_TUNNEL_IPv6_ADDR1.
-
Enable Enable Web Mode.
-
Click OK.
-
-
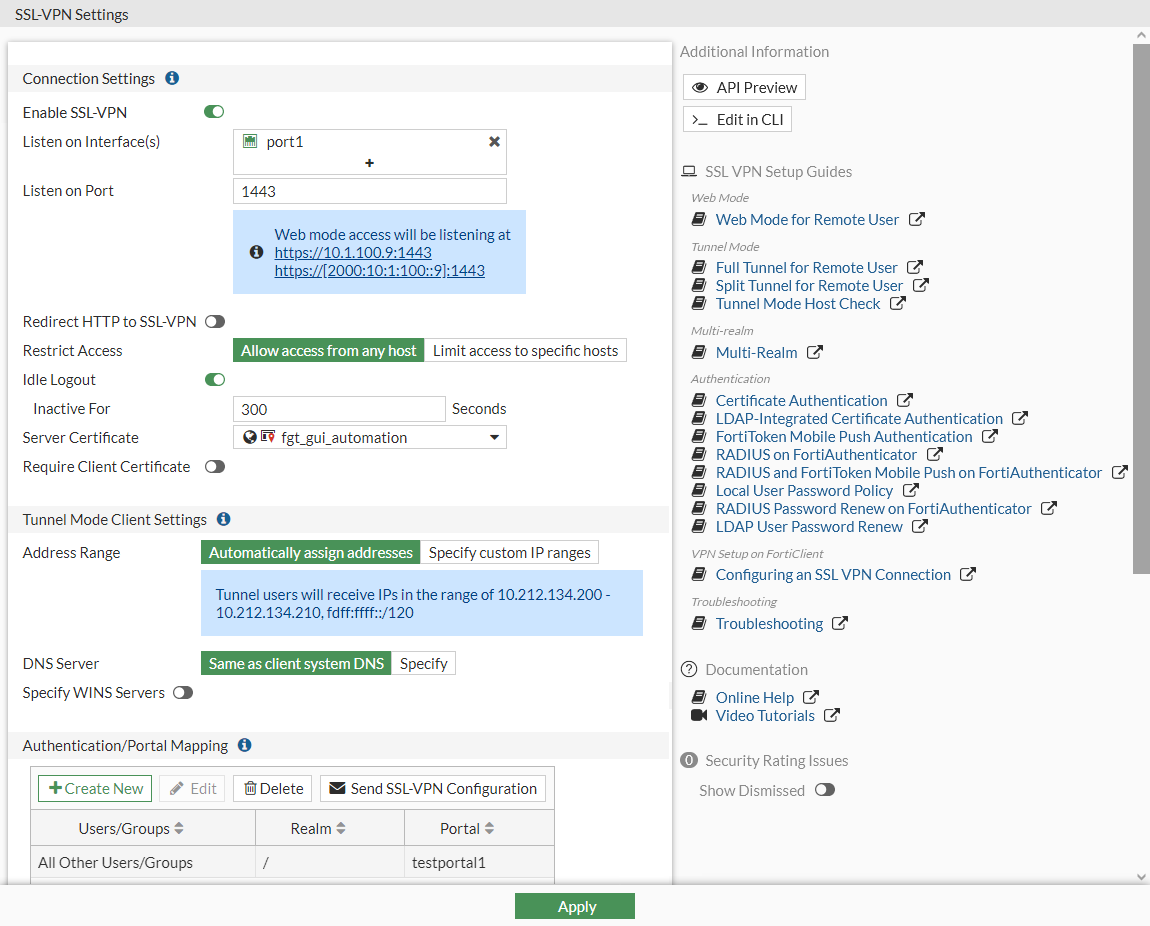
Configure the SSL VPN settings:
-
Go to VPN > SSL-VPN Settings and configure the following:
Listen on Interface(s)
port1
Listen on Port
1443
Restrict Access
Allow access from any host
Server Certificate
fgt_gui_automation
Address Range
Automatically assign addresses
DNS Server
Same as client system DNS
Authentication/Portal Mapping
Edit the All Other Users/Groups entry to use testportal1.
-
Click Apply.
-
Enable dual stack in the CLI:
config vpn ssl settings set dual-stack-mode enable end
-
-
Configure the firewall policy:
-
Go to Policy & Objects > Firewall Policy and click Create New.
-
Enter the following:
Name
sslvpn
Incoming Interface
ssl.root
Outgoing Interface
port2
Source
all (IPv4), all (IPv6), client2
Destination
bing.com, apple_v6
Schedule
Always
Service
All
NAT
Enabled
-
Click OK.
-
To configure FortiGate A as an SSL VPN client in the GUI:
-
Create a peer to verify the server certificate:

The PKI menu is only available in the GUI (User & Authentication > PKI) after a PKI user has been created using the CLI, and a CN can only be configured in the CLI.
If the CA is not known or is public, import the CA that signed the server certificate.
-
Go to User & Authentication > PKI and click Create New.
-
Set the Name to fgt_gui_automation.
-
Set CA to the CA certificate that is used to verify the server certificate.
-
Click OK.
-
In the CLI, specify the CN that must be matched:
config user peer edit "fgt_gui_automation" set ca "GUI_CA" set cn "*.fos.automation.com" next end
-
-
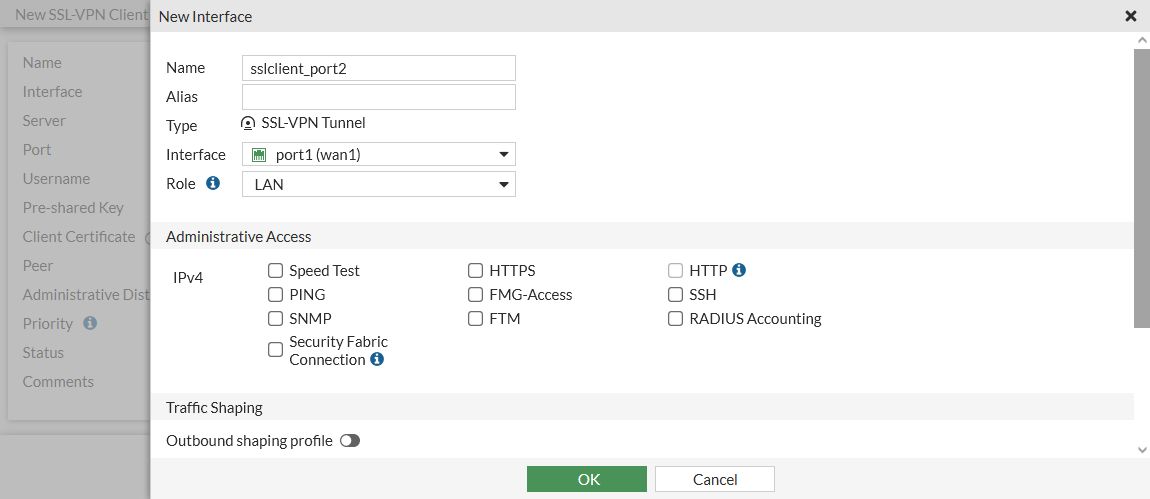
Configure the SSL VPN client:
-
Go to VPN > SSL-VPN Clients and click Create New.
-
In the Interface dropdown, click Create.
-
Enter a Name (sslclient_port2).
-
Set Interface to port2.
-
Set Role to LAN.
-
Click OK.
-
-
Configure the SSL VPN client:
Name
sslclientTo9
Interface
sslclient_port2
Server
Either IPv4 address 10.1.100.9 or IPv6 address 2000:10:1:100::9 can be used and will have the same results.
Port
1443
Username
client2
Pre-shared Key
******
Peer
fgt_gui_automation
Status
Enabled
-
Click OK.
-
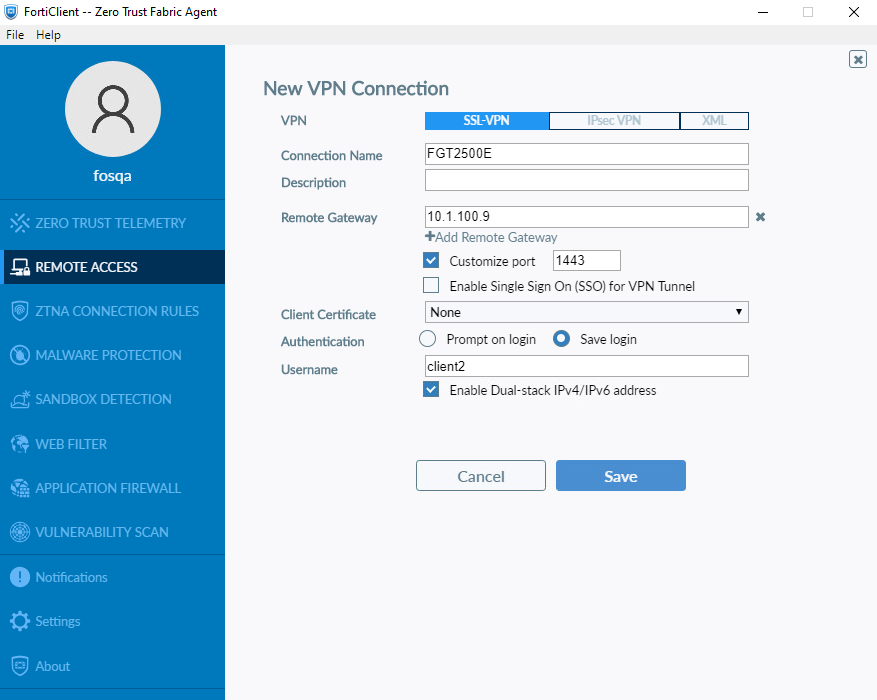
To configure FortiClient and connect to the VPN:
-
On the Remote Access tab and click Configure VPN, or if other connections have already been configured, click the sandwich icon and select Add a new connection.
-
Set Connection Name to FGT2500E, and Remote Gateway to 10.1.100.9.
-
Enable Customize port and enter the port number 1443.
-
Set Username to client2.
-
Enable Enable Dual-stack IPv6/IPv6 address.
-
Click Save.
-
Enter the password, then click Connect.
To configure an SSL VPN server in tunnel and web mode with dual stack support in the CLI:
-
Create a local user:
config user local edit "client1" set type password set passwd ****** next end -
Configure the addresses:
config firewall address edit "bing.com" set type fqdn set fqdn "www.bing.com" next endconfig firewall address6 edit "apple_v6" set type fqdn set fqdn "www.apple.com" next end -
Configure the SSL VPN portal:
config vpn ssl web portal edit "testportal1" set tunnel-mode enable set ipv6-tunnel-mode enable set web-mode enable set ip-pools "SSLVPN_TUNNEL_ADDR1" set ipv6-pools "SSLVPN_TUNNEL_IPv6_ADDR1" set split-tunneling enable set ipv6-split-tunneling enable next end -
Configure the SSL VPN settings:
config vpn ssl settings set servercert "fgt_gui_automation" set tunnel-ip-pools "SSLVPN_TUNNEL_ADDR1" set tunnel-ipv6-pools "SSLVPN_TUNNEL_IPv6_ADDR1" set port 1443 set source-interface "port1" set source-address "all" set source-address6 "all" set default-portal "testportal1" set dual-stack-mode enable end -
Configure the firewall policy:
config firewall policy edit 1 set name "sslvpn" set srcintf "ssl.root" set dstintf "port2" set srcaddr "all" set dstaddr "bing.com" set srcaddr6 "all" set dstaddr6 "apple_v6" set action accept set schedule "always" set service "ALL" set nat enable set users "client2" next end
To configure FortiGate A as an SSL VPN client in the CLI:
-
Create a peer to verify the server certificate:
config user peer edit "fgt_gui_automation" set ca "GUI_CA" set cn "*.fos.automation.com" next end -
Configure the interface:
config system interface edit "sslclient_port2" set vdom "vdom1" set type ssl set role lan set snmp-index 46 set interface "port2" next end -
Configure the SSL VPN client. Either IPv4 address 10.1.100.9 or IPv6 address 2000:10:1:100::9 can be used and will have the same results:
config vpn ssl client edit "sslclientTo9" set interface "sslclient_port2" set user "client2" set psk ****** set peer "fgt_gui_automation" set server {10.1.100.9 | 2000:10:1:100::9} set port 1443 next end
Testing dual stack with tunnel mode
To verify the SSL VPN tunnel connection in the GUI:
-
On FortiGate B, go to Dashboard > Network.
-
Expand the SSL-VPN widget.

To verify the SSL VPN tunnel connection in the CLI:
-
On FortiGate B, verify that the client is assigned with both IPv4 and IPv6 addresses:
(root) # get vpn ssl monitor SSL VPN Login Users: Index User Group Auth Type Timeout Auth-Timeout From HTTP in/out HTTPS in/out Two-factor Auth 0 client2 1(1) 292 2147483647 10.1.100.2 0/0 0/0 0 SSL VPN sessions: Index User Group Source IP Duration I/O Bytes Tunnel/Dest IP 0 client2 10.1.100.2 5427 1756/1772 10.212.134.200,fdff:ffff::1
-
On FortiGate A, verify the routing tables.
-
IPv4 with resolved addresses for www.bing.com:
(vdom1) # get router info routing-table database ... Routing table for VRF=0 S *> 0.0.0.0/0 [10/0] via 172.16.200.254, port1 C *> 10.0.1.0/24 is directly connected, link_11 C *> 10.1.100.0/24 is directly connected, port2 C *> 10.212.134.200/32 is directly connected, sslclient_port2 S *> 13.107.21.200/32 [10/0] is directly connected, sslclient_port2 C *> 172.16.200.0/24 is directly connected, port1 S *> 204.79.197.200/32 [10/0] is directly connected, sslclient_port2
-
IPv6 with resolved addresses for www.apple.com:
(vdom1) # get router info6 routing-table database ... S *> ::/0 [10/0] via 2000:172:16:200::254, port1, 01:57:23, [1024/0] C *> ::1/128 via ::, vdom1, 06:12:54 C *> 2000:10:0:1::/64 via ::, link_11, 06:12:54 C *> 2000:10:1:100::/64 via ::, port2, 06:12:54 C *> 2000:172:16:200::/64 via ::, port1, 06:12:54 S *> 2600:140a:c000:385::1aca/128 [10/0] via ::, sslclient_port2, 01:33:08, [1024/0] S *> 2600:140a:c000:398::1aca/128 [10/0] via ::, sslclient_port2, 01:33:08, [1024/0] C *> fdff:ffff::/120 via ::, sslclient_port2, 01:33:08 C *> fe80::/64 via ::, port2, 06:12:54
-
To test the address connections using ping:
-
On FortiGate A, ping www.bing.com using IPv4 ping:
# execute ping www.bing.com PING www-bing-com.dual-a-0001.a-msedge.net (13.107.21.200): 56 data bytes 64 bytes from 13.107.21.200: icmp_seq=0 ttl=117 time=1.8 ms ...
-
On FortiGate B, sniff for IPv4 ICMP packets and observe the results:
# diagnose sniffer packet any icmp 4 interfaces=[any] filters=[icmp] 9.675101 ssl.root in 10.212.134.200 -> 13.107.21.200: icmp: echo request 9.675219 port2 out 172.16.200.9 -> 13.107.21.200: icmp: echo request 9.676698 port2 in 13.107.21.200 -> 172.16.200.9: icmp: echo reply 9.676708 ssl.root out 13.107.21.200 -> 10.212.134.200: icmp: echo reply ...
-
On FortiGate A, ping www.apple.com using IPv6 ping:
# execute ping6 www.apple.com PING www.apple.com (2600:140a:c000:385::1aca): 56 data bytes 64 bytes from 2600:140a:c000:385::1aca: icmp_seq=1 ttl=52 time=1.88 ms ...
-
On FortiGate B, sniff for IPv6 ICMP packets and observe the results:
# diagnose sniffer packet any icmp6 4 interfaces=[any] filters=[icmp6] 3.564296 ssl.root in fdff:fff::1 -> 2600:140a:c000:385::1aca: icmp6: echo request seq 1 3.564435 port2 out 2000:172:16:200::9 -> 2600:140a:c000:385::1aca: icmp6: echo request seq 1 3.565929 port2 in 2600:140a:c000:385::1aca -> 2000:172:16:200::9: icmp6: echo reply seq 1 [flowlabel 0x1fdff] 3.565953 ssl.root out 2600:140a:c000:385::1aca -> fdff:fff::1: icmp6: echo reply seq 1 [flowlabel 0x1fdff] ...
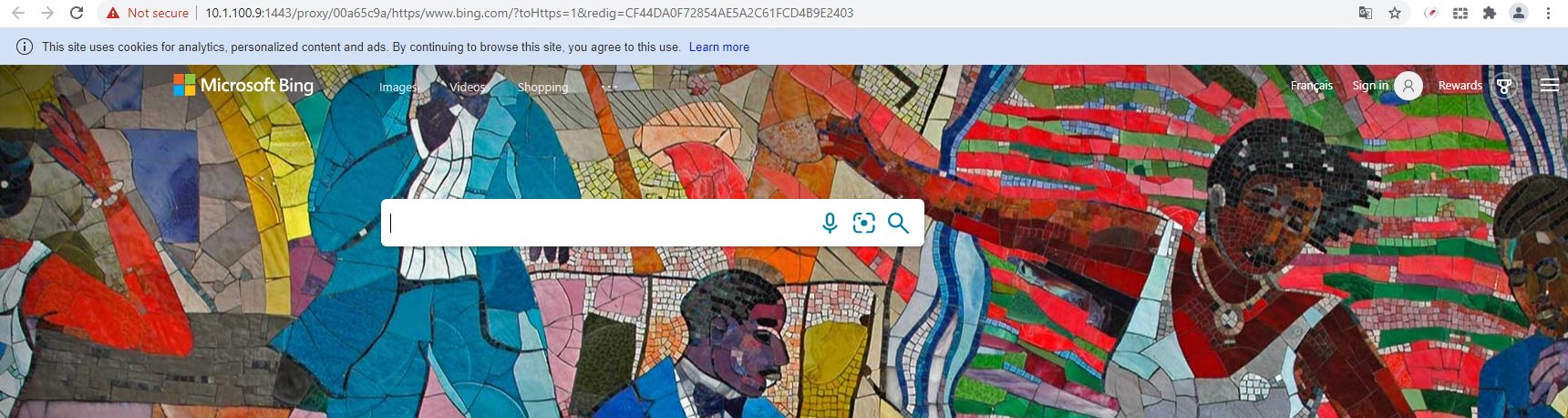
Testing dual stack with web mode
In SSL VPN web mode, users can access both IPv4 and IPv6 bookmarks in the portal. The attribute, prefer-ipv6-dns can be enabled to prefer querying IPv6 DNS first, or disabled to prefer querying IPv4.
To test an IPv4 connection to the web portal and access www.bing.com over IPv6:
-
On FortiGate B, prioritize resolving IPv6 addresses:
config vpn ssl web portal edit "testportal1" set prefer-ipv6-dns enable next end -
Log in to the web portal in the browser over the IPv4 address 10.1.100.9.
-
Create a new HTTP/HTTPS bookmark named bing for the URL www.bing.com.
-
Click the bing bookmark. The bing page will open over IPv6.
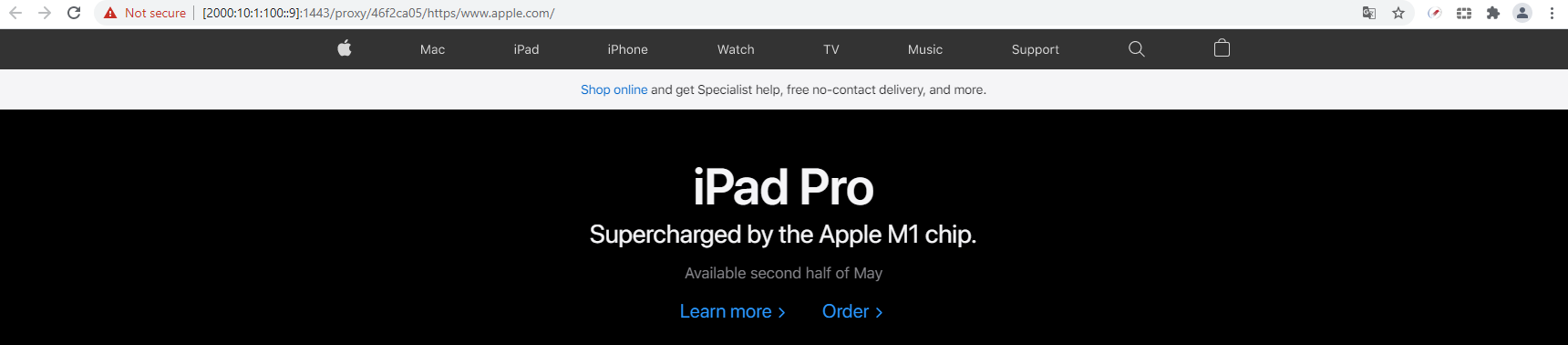
To test an IPv6 connection to the web portal and access www.apple.com over IPv4:
-
On FortiGate B, prioritize resolving IPv4 addresses:
config vpn ssl web portal edit "testportal1" set prefer-ipv6-dns disable next end -
Log in to the web portal in the browser over the IPv6 address [2000:10:1:100::9].
-
Create a new HTTP/HTTPS bookmark named apple for the URL www.apple.com.
-
Click the apple bookmark. The apple page will open over IPv4.