Client-Side Security Module (8.0.0)
FortiWeb 8.0.0 introduces a major architectural update with the new Client Side Security module under Web Protection. This design consolidates several browser-side enforcement mechanisms—both new and existing—into a unified, modular framework. The new module improves policy clarity, ensures consistent protection coverage, and aligns FortiWeb’s capabilities with a layered defense strategy designed to address modern client-side threats.
The module is purpose-built to address evolving client-side threats such as JavaScript drift, third-party script injection, DOM-based cross-site scripting (XSS), credential harvesting via form hijacking, unauthorized data exfiltration, and supply chain compromise. These attacks operate within the browser—after the server has delivered its response—and are increasingly used to bypass traditional network- and server-side defenses.
For detailed use cases and examples of how Client Side Security features are applied to real-world threats, see WAF Solutions against OWASP Top 10 Client-Side Security Risks.
Design Goals and Benefits
The Client-Side Security module enhances FortiWeb’s ability to enforce in-browser security by:
-
Unifying related protections into a dedicated interface, improving visibility, simplifying configuration, and reducing policy fragmentation.
-
Clarifying interdependencies between client-side controls, such as Content-Security-Policy (CSP), Subresource Integrity (SRI), and runtime monitoring.
-
Aligning each component with FortiWeb’s layered defense model, enabling targeted protection at different phases of the browser-side attack lifecycle: pre-delivery prevention, runtime detection, and post-compromise mitigation.
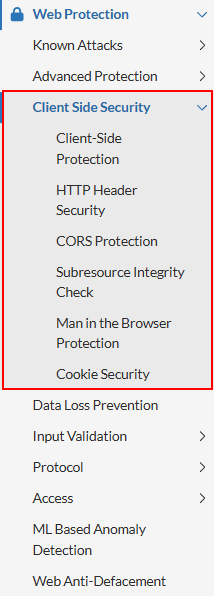
Component Overview and Functional Reorganization
The new Client-Side Security module consolidates key security features related to in-browser protections and restructures existing capabilities to align with FortiWeb’s layered client-side defense model. This design improves policy coherence, reduces configuration fragmentation, and enhances browser-side threat mitigation.
The following components are included:
Client-Side Protection (New)
A dynamic inspection engine that uses either JavaScript-based telemetry collection or passive HTML analysis to monitor unauthorized client-side behaviors such as script injection, DOM manipulation, and unauthorized third-party access. Operates in Monitor or Block mode, offering granular visibility and enforcement options.
HTTP Header Security (Redesigned and Enhanced)
Previously located under Web Protection > Advanced Protection, this module has been redesigned and expanded to include additional headers such as Content-Security-Policy-Report-Only, Cross-Origin-Opener-Policy, and Clear-Site-Data. These headers reinforce browser-layer isolation, data hygiene, and secure execution contexts.
CORS Protection (Migrated)
Now located under Client-Side Security, this module was formerly under Web Protection > Access. It enforces origin-based access controls by validating allowed origins, HTTP methods, and headers in cross-origin requests, helping mitigate data exfiltration via CORS misconfigurations.
Subresource Integrity Check (New)
Subresource Integrity (SRI) Check allows administrators to specify cryptographic hashes for externally hosted JavaScript or CSS resources. FortiWeb injects corresponding integrity and crossorigin attributes into response HTML, enabling browser-level enforcement that prevents tampered or unauthorized third-party resources from executing.
Man-in-the-Browser (MitB) Protection (Migrated)
Formerly part of Web Protection > Advanced Protection, this feature secures client-side data entry by encrypting sensitive form inputs, obfuscating HTML field names, and defending against keystroke interception and script-based field manipulation within compromised browsers.
Cookie Security (Migrated)
Previously a standalone module, Cookie Security is now integrated into the client-side framework. It enforces secure cookie attributes such as HttpOnly, Secure, and SameSite, and can cryptographically sign cookies to detect or block tampering.
Layered Defense Strategy
FortiWeb structures its client-side protections into a three-stage defense model, securing the application at multiple browser touchpoints:
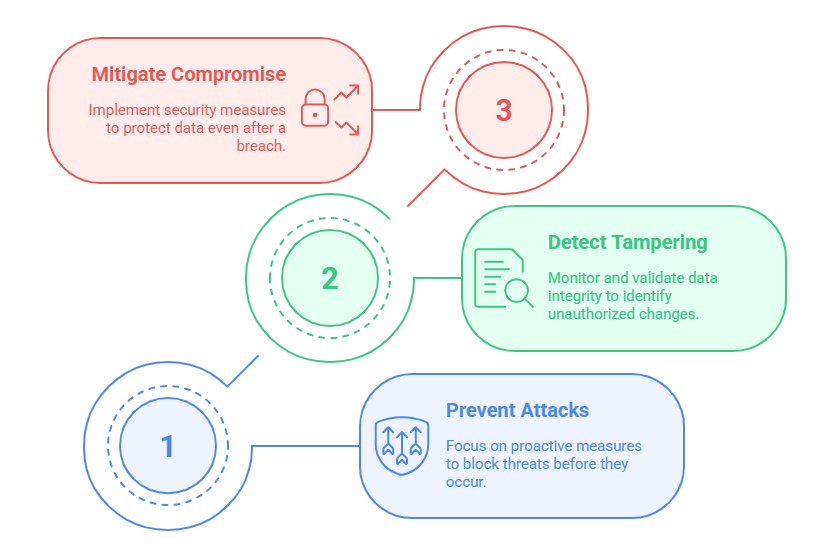
Stage 1: Prevent Attacks Before They Happen
-
HTTP Header Security: Enforces browser behavior by inserting security headers such as CSP, CORP, COEP, and Referrer-Policy. These headers control script execution, restrict cross-origin access, and limit data leakage through browser features.
-
CORS Protection: Enforces server-side origin validation for incoming cross-origin requests.
-
Client-Side Protection: Prevents known threats at the WAF level using request and response inspection.
OWASP Risks Addressed:
DOM-based XSS, sensitive data leakage, outdated components, third-party origin control, lack of browser security controls, proprietary client-side data exposure.
Stage 2: Detect Tampering at Runtime
-
Subresource Integrity Check: Validates that external JavaScript and CSS files match expected cryptographic hashes before execution. Protects against compromised CDNs and unauthorized library changes.
-
Client-Side Protection: Secures data exchanges using headers like HTTP Strict Transport Security (HSTS), Content-Security-Policy, and SRI.
OWASP Risks Addressed:
Vulnerable and outdated components, JavaScript drift, lack of third-party origin control.
Stage 3: Mitigate After the Browser Is Compromised
-
Cookie Security: Automatically enforces security attributes like HttpOnly, Secure, and SameSite, and signs cookies to prevent tampering.
-
MitB Protection: Encrypts form inputs, obfuscates field names, and includes anti-keylogging mechanisms to secure sensitive data in compromised browsers.
-
CORS Protection: Inspects and enforces origin and method constraints for cross-origin traffic.
-
Client-Side Protection: Provides runtime monitoring and enforcement against threats that materialize post-delivery.
OWASP Risks Addressed:
Broken client-side access control, sensitive data stored client-side, monitoring failures, proprietary information leakage.
Real-Time Visibility and Control
Client-Side Protection provides a comprehensive overview of third-party services executing in the browser. It identifies external domains, categorizes resource types, flags risk levels, and logs usage frequency. Administrators can approve, block, or annotate services, with FortiWeb generating an optimized CSP header for enforcement.
Unified Enforcement Model
All features under Client-Side Security are fully integrated with FortiWeb protection profiles. Administrators can configure each policy individually and apply them as part of a broader security strategy through server policies—across inline, reverse proxy, or WCCP deployment modes.
This modular, layered approach to browser-side security gives organizations complete control over the client surface, helping to safeguard modern web applications against advanced client-side threat vectors.
For more information, see Client Side Security.

