Configuring the SD-WAN interface
First, SD-WAN must be enabled and member interfaces must be selected and added to a zone. The selected FortiGate interfaces can be of any type (physical, aggregate, VLAN, IPsec, and others), but must be removed from any other configurations on the FortiGate.
In this step, two interfaces are configured and added to the default SD-WAN zone (virtual-wan-link) as SD-WAN member interfaces. This example uses a mix of static and dynamic IP addresses; your deployment could also use only one or the other.
Once the SD-WAN members are created and added to a zone, the zone can be used in firewall policies, and the whole SD-WAN can be used in static routes.
To configure SD-WAN members:
- Configure the wan1 and wan2 interfaces. See Interface settings for details.
- Set the wan1 interface Addressing mode to DHCP and Distance to 10.

By default, a DHCP interface has a distance of 5, and a static route has a distance of 10. It is important to account for this when configuring your SD-WAN for 50/50 load balancing by setting the DHCP interface's distance to 10.
- Set the wan2 interface IP/Netmask to 10.100.20.1 255.255.255.0.
- Set the wan1 interface Addressing mode to DHCP and Distance to 10.
- Go to Network > SD-WAN Zones. Routing for each SD-WAN interface is defined here.
- Click Create New > SD-Member.
- Set the Interface to wan1.
- Leave SD-WAN Zone as virtual-wan-link.
- As wan1 uses DHCP, leave Gateway set to 0.0.0.0.
If IPv6 visibility is enabled in the GUI, an IPv6 gateway can also be added for each member. See Feature visibility for details.
- Leave Cost as 0.
The Cost field is used by the Lowest Cost (SLA) strategy. The link with the lowest cost is chosen to pass traffic. The lowest possible Cost is 0.
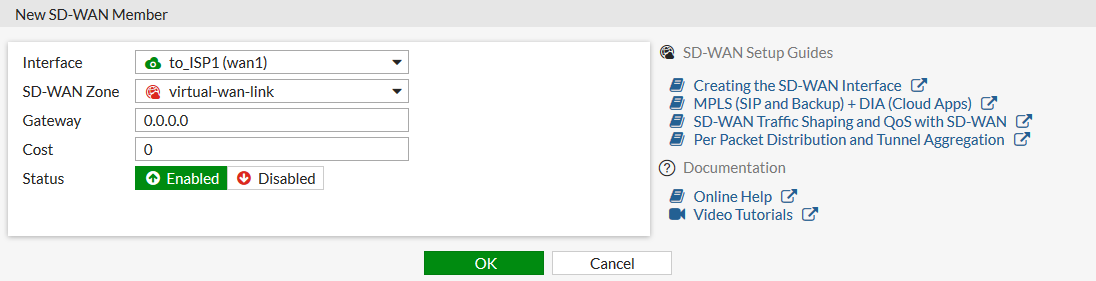
- Set Status to Enable, and click OK.
- Repeat the above steps for wan2, setting Gateway to the ISP's gateway: 10.100.20.2.

Next: Adding a static route

