ZTNA HTTPS access proxy with basic authentication example
This example expands on the previous example (ZTNA HTTPS access proxy example), adding LDAP authentication to the ZTNA rule. Users are allowed based on passing the client certificate authentication check, user authentication, and security posture check.
Users that are in the AD security group ALLOWED-VPN are allowed access to the access proxy. Users that are not part of this security group are not allowed access.
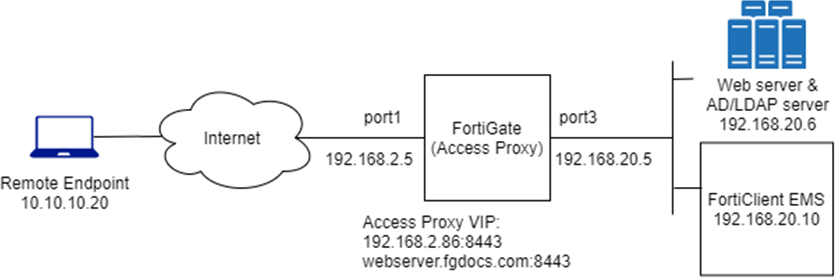
This example assumes that the FortiGate EMS fabric connector is already successfully connected.
LDAP/Active Directory Users and Groups:
-
Domain: KLHOME.local
-
Users (Groups):
-
radCurtis (Domain Users, ALLOWED-VPN)
-
radKeith (Domain Users)
-
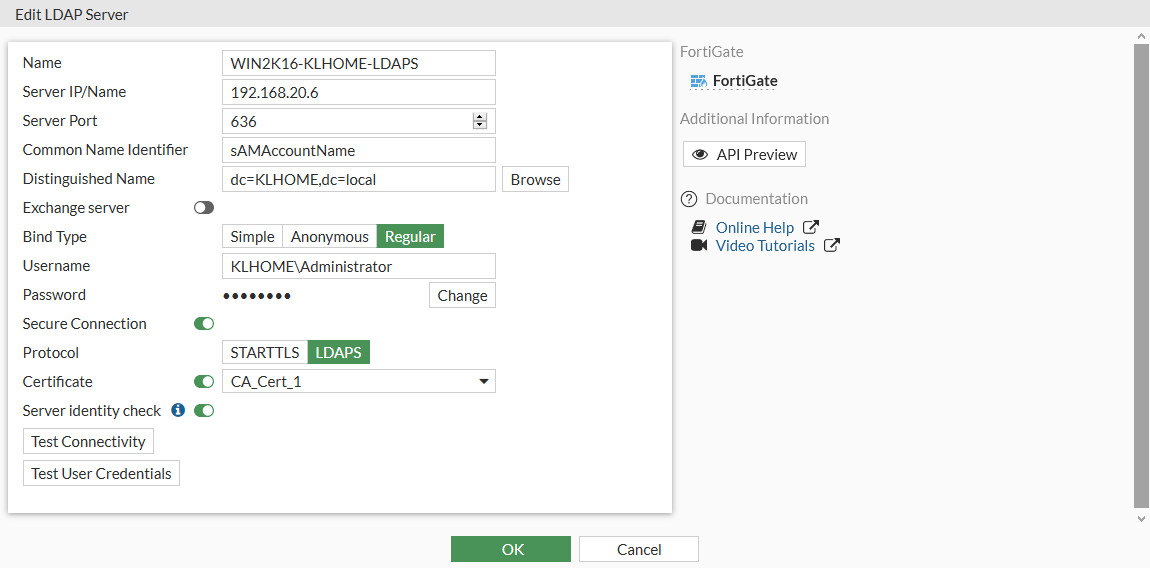
To configure a secure connection to the LDAP server in the GUI:
-
Go to User & Authentication > LDAP Servers and click Create New.
-
Configure the following settings:
Name
WIN2K16-KLHOME-LDAPS
Server IP/Name
192.168.20.6
Server Port
636
Common Name Identifier
sAMAccountName
Distinguished Name
dc=KLHOME,dc=local
Exchange server
Disabled
Bind Type
Regular
Enter the Username and Password for LDAP binding and lookup.
Secure Connection
Enabled
-
Set Protocol to LDAPS
-
Enable Certificate and select the CA certificate to validate the server certificate.
Server identity check
Optionally, enable to verify the domain name or IP address against the server certificate.
-
-
Click Test Connectivity to verify the connection to the server.
-
Click OK.
To configure a secure connection to the LDAP server in the CLI:
config user ldap
edit "WIN2K16-KLHOME-LDAPS"
set server "192.168.20.6"
set cnid "sAMAccountName"
set dn "dc=KLHOME,dc=local"
set type regular
set username "KLHOME\\Administrator"
set password <password>
set secure ldaps
set ca-cert "CA_Cert_1"
set port 636
next
end
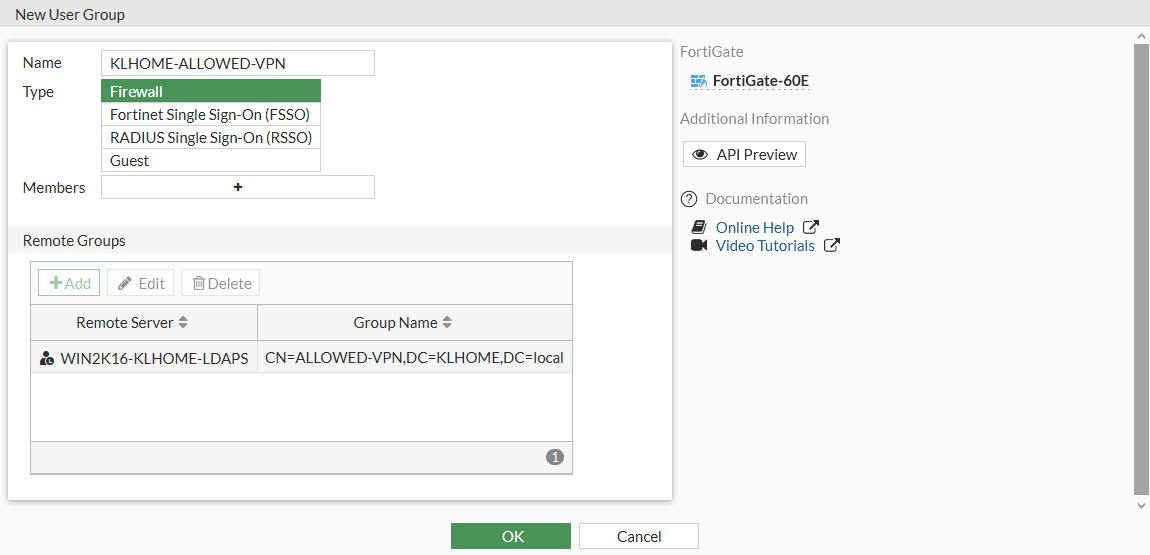
To configure a remote user group from the LDAP server in the GUI:
-
Go to User & Authentication > User Groups and click Create New.
-
Set the name to KLHOME-ALLOWED-VPN.
-
Set Type to Firewall.
-
In the Remote Groups table click Add:
-
Set Remote Server to WIN2K16-KLHOME-LDAPS.
-
Locate the ALLOWED-VPN group, right-click on it, and click Add Selected.
-
Click OK.
-
-
Click OK.
To configure a remote user group from the LDAP server in the CLI:
config user group
edit "KLHOME-ALLOWED-VPN"
set member "WIN2K16-KLHOME-LDAPS"
config match
edit 1
set server-name "WIN2K16-KLHOME-LDAPS"
set group-name "CN=ALLOWED-VPN,DC=KLHOME,DC=local"
next
end
next
end
Authentication scheme and rules
After the LDAP server and user group have been configured, an authentication scheme and rule must be configured.
|
|
To configure authentication schemes and rules in the GUI, go to System > Feature Visibility and enable Explicit Proxy. |
Authentication scheme
The authentication scheme defines the method of authentication that is applied. In this example, basic HTTP authentication is used so that users are prompted for a username and password the first time that they connect to a website through the HTTPS access proxy.
To configure an authentication scheme in the GUI:
-
Go to Policy & Objects > Authentication Rules and click Create New > Authentication Scheme.
-
Set the name to ZTNA-Auth-scheme.
-
Set Method to Basic.
-
Set User database to Other and select WIN2K16-KLHOME-LDAPS as the LDAP server.
-
Click OK.
To configure an authentication scheme in the CLI:
config authentication scheme
edit "ZTNA-Auth-scheme"
set method basic
set user-database "WIN2K16-KLHOME-LDAPS"
next
end
Authentication rule
The authentication rule defines the proxy sources and destination that require authentication, and what authentication scheme is applied. In this example, active authentication through the basic HTTP prompt is used and applied to all sources.
To configure an authentication rule in the GUI:
-
Go to Policy & Objects > Authentication Rules and click Create New > Authentication Rule.
-
Set the name to ZTNA-Auth-rule.
-
Set Source Address to all.
-
Set Protocol to HTTP.
-
Enable Authentication Scheme and select ZTNA-Auth-scheme.
-
Click OK.
To configure an authentication rule in the CLI:
config authentication rule
edit "ZTNA-Auth-rule"
set srcaddr "all"
set active-auth-method "ZTNA-Auth-scheme"
next
end
Applying the user group to a ZTNA rule
A user or user group must be applied to the ZTNA rule that you need to control user access to. The authenticated user from the authentication scheme and rule must match the user or user group in the ZTNA rule.
In this example, the user group is applied to the two ZTNA rules that were configured in ZTNA HTTPS access proxy example.
To apply a user group to the ZTNA rules in the GUI:
-
Go to Policy & Objects > ZTNA and select the ZTNA Rules tab.
-
Edit the ZTNA-Deny-malicious rule.
-
Click in the Source field, select the User tab, select the KLHOME-ALLOWED-VPN group, then click Close.
-
Click OK.
-
Edit the proxy-WIN2K16-P1 rule.
-
Click in the Source field, select the User tab, select the KLHOME-ALLOWED-VPN group, then click Close.
-
Click OK.
To apply a user group to the ZTNA rules in the CLI:
config firewall proxy-policy
edit 3
set name "ZTNA-Deny-malicious"
set proxy access-proxy
set access-proxy "WIN2K16-P1"
set srcintf "port1"
set srcaddr "all"
set dstaddr "all"
set ztna-ems-tag "FCTEMS0000109188_Malicious-File-Detected"
set schedule "always"
set logtraffic all
set groups "KLHOME-ALLOWED-VPN"
next
edit 2
set name "proxy-WIN2K16-P1"
set proxy access-proxy
set access-proxy "WIN2K16-P1"
set srcintf "port1"
set srcaddr "all"
set dstaddr "all"
set ztna-ems-tag "FCTEMS0000109188_Low"
set action accept
set schedule "always"
set logtraffic all
set groups "KLHOME-ALLOWED-VPN"
next
end
Testing remote access to the HTTPS access proxy with user authentication
Scenario 1: access allowed - user radCurtis
-
On a remote Windows PC, open the FortiClient app, select the Zero Trust Telemetry tab, and confirm that you are connected to the EMS server.

It is not necessary to configure a ZTNA Destination on the FortiClient for the HTTPS access proxy use case. In fact, configuring a ZTNA Destination rule for the website may interfere with its operation.
-
In a browser, enter the address of the server and the access port.
If entering an FQDN, make sure that DNS can resolve the address to the IP address of the FortiGate. In this example, winserver.fgdocs.com resolves to 192.168.2.86.
-
When the browser asks for the client certificate to use, select the EMS signed certificate, then click OK.
The client certificate is verified by the FortiGate to authenticate your identity.
-
When prompted, enter the username radCurtis and the password, and click Sign in.
As radCurtis is a member of the ALLOWED-VPN group in Active Directory, it will match the KLHOME-ALLOWED-VPN user group. After the user authentication passes, the FortiGate performs a posture check on the ZTNA group. When that passes, you are allowed access to the website.
Verifying the results
# diagnose firewall auth list
10.10.10.20, radCurtis
type: fw, id: 0, duration: 13, idled: 13
expire: 587, allow-idle: 600
packets: in 0 out 0, bytes: in 0 out 0
group_id: 8 16777220
group_name: KLHOME-ALLOWED-VPN grp_16777220# diagnose test application fcnacd 7
ZTNA Cache:
-uid F4F3263AEBE54777A6509A8FCCDF9284: { "tags": [ "all_registered_clients", "Low" ], "user_name": "keith", "client_cert_sn": "6C7433E8E2CEDEB49B6C3C3C03677A3521EA4486", "ems_sn": "FCTEMS0000109188" }
|
|
The |
# execute log display 1: date=2021-04-13 time=00:11:56 eventtime=1618297916023667886 tz="-0700" logid="0000000010" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.10.10.20 srcport=51513 srcintf="port1" srcintfrole="wan" dstcountry="Reserved" srccountry="Reserved" dstip=192.168.20.6 dstport=443 dstintf="root" dstintfrole="undefined" sessionid=2319197 srcuuid="2d8e1736-8ec6-51eb-885c-009bdf9c31d7" dstuuid="5445be2e-5d7b-51ea-e2c3-ae6b7855c52f" service="HTTPS" wanoptapptype="web-proxy" proto=6 action="accept" policyid=2 policytype="proxy-policy" poluuid="5aba29de-8ec6-51eb-698f-25b59d5bf852" duration=10 user="radCurtis" group="KLHOME-ALLOWED-VPN" authserver="WIN2K16-KLHOME-LDAPS" wanin=104573 rcvdbyte=104573 wanout=2364 lanin=3538 sentbyte=3538 lanout=104445 appcat="unscanned"
Scenario 2: access denied – user radKeith
-
If scenario 1 has just been tested, log in to the FortiGate and deauthenticate the user:
-
Go to Dashboard > Users & Devices and expand the Firewall Users widget.
-
Right-click on the user radCurtis and select deauthenticate.
-
-
On a remote Windows PC, open the FortiClient app, select the Zero Trust Telemetry tab, and confirm that you are connected to the EMS server.
-
In a browser, enter the address winserver.fgdocs.com.
-
When the browser asks for the client certificate to use, select the EMS signed certificate, then click OK. This option might not appear if you have already selected the certificate when testing scenario 1.
The client certificate is verified by the FortiGate to authenticate your identity.
-
When prompted, enter the username radKeith and the password, and click Sign in.
As radKeith is not a member of the ALLOWED-VPN group in Active Directory, it will not match the KLHOME-ALLOWED-VPN user group. Because no other policies are matched, this user is implicitly denied
Verifying the results
Go to Dashboard > Users & Devices, expand the Firewall Users widget, and confirm that user radKeith is listed, but no applicable user group is returned.
# execute log display 1: date=2021-04-13 time=12:29:21 eventtime=1618342161821542277 tz="-0700" logid="0000000013" type="traffic" subtype="forward" level="notice" vd="root" srcip=10.10.10.20 srcport=52571 srcintf="port1" srcintfrole="wan" dstip=192.168.20.6 dstport=443 dstintf="root" dstintfrole="undefined" srcuuid="5445be2e-5d7b-51ea-e2c3-ae6b7855c52f" srccountry="Reserved" dstcountry="Reserved" sessionid=2394329 proto=6 action="deny" policyid=0 policytype="proxy-policy" user="radKeith" authserver="WIN2K16-KLHOME-LDAPS" service="HTTPS" trandisp="noop" url="https://winserver.fgdocs.com/" agent="Chrome/89.0.4389.114" duration=0 sentbyte=0 rcvdbyte=0 sentpkt=0 rcvdpkt=0 appcat="unscanned" crscore=30 craction=131072 crlevel="high" msg="Traffic denied because of explicit proxy policy"

