Authentication scheme
This section defines the FIC-supported authentication schemes and how Multi-Factor Authentication (MFA) methods apply to each scheme. These schemes determine how users authenticate and what additional verification steps may be required to access the system.
In its 26.1 release, FortiIdentity Cloud introduces an Authentication tab in realm configuration (Settings > Realm).
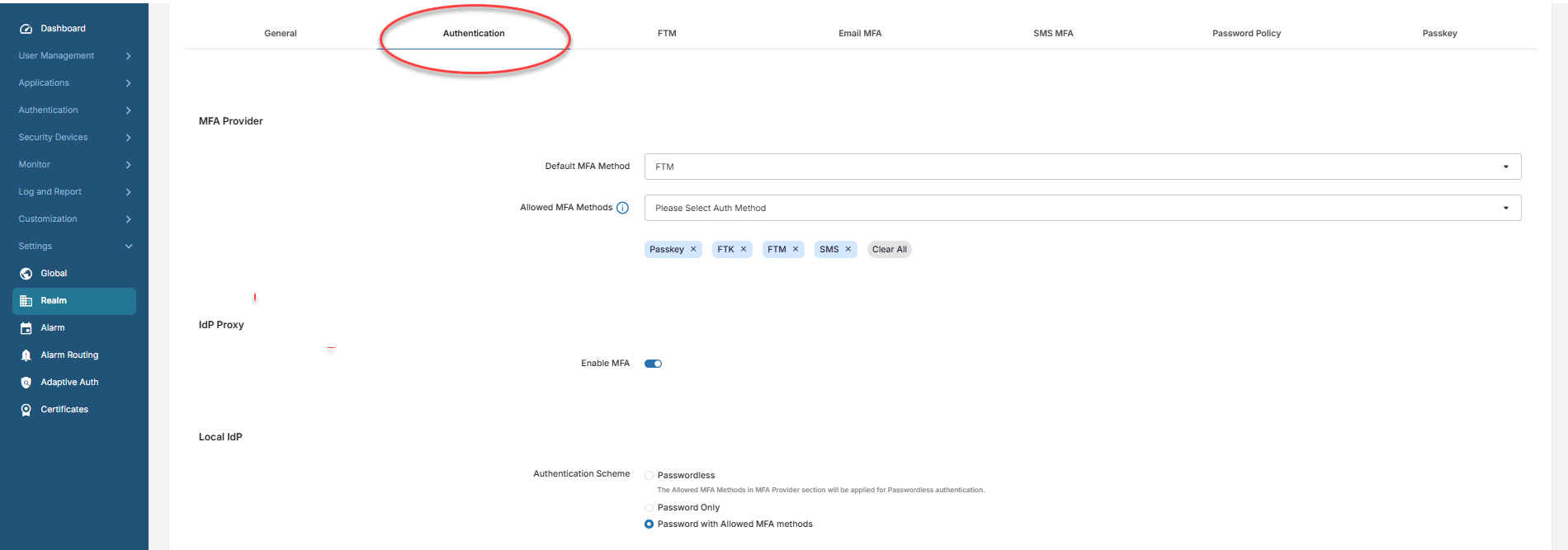
The Settings > Realm > Authentication page has the following three authentication schemes:
| Parameter | Description | |||
|---|---|---|---|---|
|
MFA Provider |
|
|||
|
|
Default MFA Method |
The Default MFA Method that will be assigned by default to all users added in the realm. By default, when a realm is created, FTM is assigned by default as the default MFA method. Select one of the following as the default MFA method that your FIC uses to authenticate end users:
|
||
|
|
Allowed MFA Methods |
In addition to the Default MFA Method, the admin can set other MFA methods that the user can use to complete the authentication process. This option is applicable only for SSO applications.
The drop-down menu shows all the MFA methods that you may allow your end users to use. By default, all the options except Email are preselected. If you are satisfied with the default settings, do nothing; otherwise, you can use the tools here to customize your allowed MFA methods.
|
||
|
IdP Proxy |
|
|||
|
|
Enable MFA |
Turning this toggle switch OFF will by default turn off MFA for all IdP Proxy SSO applications in the realm. The setting can be overridden per SSO application in the realm by using the same Enable MFA option in the Authentication tab of the SSO application. By default, the feature is enabled when a new realm is created. |
||
|
Local IdP |
This section applies only to SSO applications that use FIC’s Local IdP as the user source. It has the following options: |
|||
|
|
Passwordless |
Enables users to sign in without entering a password. The Allowed MFA Methods in MFA Provider section will be applied for Passwordless authentication. This option:
|
||
|
|
Password Only |
Users authenticate solely using a password, with no additional MFA factors required. Authentication success is determined solely by correct password entry. This option is
|
||
|
|
Password with Allowed MFA Methods |
Users authenticate using their password and a MFA method defined in the Allowed MFA Methods configuration. This option:
|
||

