Debug
By default, the FortiADC Kubernetes Controller records the process of the Ingress and Fortinet-defined custom resources implementation in verbose mode. The debug log shows the check of annotation parameters and the process of calling the REST API to FortiADC when deploying, updating, or deleting the Ingress resources.
The verbose log can be enabled or disabled for any particular Ingress or Fortinet-defined custom resources. This is determined by the status of the fortiadc-ctrl-log configuration parameter.
For more information, see Configuration Parameters.
To see the log, you can use the kubectl logs command:
kubectl logs -n [namespace] -f [FortiADC Kubernetes Controller pod name]
The log shows which problem you encounter. For example, the below log shows that you do not have the correct FortiADC Authentication Secret in the Kubernetes cluster.
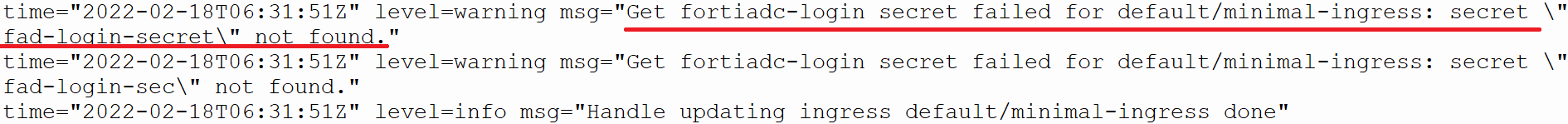
Based on the error message, you can correct it and use the kubectl apply or edit command to reconfigure the resource.
Some troubleshooting steps may require restarting the FortiADC Kubernetes Controller. For example, the FortiADC Kubernetes Controller may not connect to FortiADC after changing the network firewall rule. To fix this type of environment issue, you can restart the FortiADC Kubernetes Controller by using the following command:
kubectl -n [namespace] rollout restart deployment/[ FortiADC Kubernetes Controller deployment name]

