WAF solutions against OWASP Top 10 Client-Side Security risks
Since modern web apps rely heavily on JavaScript, APIs, and third-party integrations, the browser becomes a critical attack surface. Attacks that target the browser specifically focus on exploiting the environment in which web pages are rendered, rather than attacking the server. These attacks aim to steal sensitive data, manipulate content, or compromise user behavior — often silently.
OWASP identifies ten key categories of client-side security risks, outlined as follows.
Risks Related to Inline or DOME-Based Scripts
These involve scripts that are either embedded directly in the page or dynamically manipulated via the DOME. They are often exploited through injection or a lack of proper input control.
-
#1: Broken Client-side Access Control
Insufficient control of JavaScript access to client-side assets (data and code), exfiltration of sensitive data, or manipulation of the DOM for malicious purposes (to access those assets).
*DOM elements are the building blocks of a web page as seen by your browser. They represent HTML elements (like <div>, <button>, <input>) in a structure called the Document Object Model (DOM).Example: A malicious script reads apiToken and sends it to an attacker. The data is exposed:
<script>
// Sensitive config exposed on the client
const userRole = 'admin';
const apiToken = 'ABC123'; // Visible in JS
</script>
-
#2: DOM-based XSS
Vulnerabilities that permit XSS attacks through DOM manipulation or abuse.
Example: Visiting
example.com#<script>alert(1)</script>triggers JavaScript execution — untrusted input was injected into the DOM.<div id="output"></div>
<script>
const payload = location.hash.substring(1);
document.getElementById('output').innerHTML = payload;
</script>
-
#3: Sensitive Data Leakage
Inability to detect/prevent digital trackers and pixels across a web property to ensure national and international privacy laws are complied with.
Risks Related to External or Third-Party Resources
These risks stem from loading external JavaScript libraries or third-party services. If those resources are compromised or behave unexpectedly, they can jeopardize security.
-
#4: Vulnerable and Outdated Components
Lack of detection and updates to JavaScript libraries that are outdated or contain known vulnerabilities. Just like OWASP Top 10: A06-2021 - Vulnerable and Outdated Components, but focused on client-side libraries.
-
#5: Lack of Third-party Origin Control
Origin control allows the restriction of certain web assets or resources by comparing the origin of the resource to the origin of the third-party library. Without leveraging such controls, supply chain risk increases due to inclusion of unknown or uncontrolled third-party code that has access to data in the site’s origin.
-
#6: JavaScript Drift
Inability to detect changes at the asset and code level of JavaScript used client-side. This includes the inability to detect behavioral changes of this code to determine if the changes are potentially malicious in nature. This is particularly important for third-party libraries.
This risk is not about loading unauthorized scripts, but about trusted scripts that change over time in ways that become malicious — and those changes going undetected.
Risks Related to Data Handling and Monitoring
These focus on how data is stored in the browser, how frontend activity is monitored, and whether proper security controls are enforced.
-
#7: Sensitive Data Stored Client-Side
Storage of sensitive data like passwords, crypto secrets, API tokens, or PII data in persistent client-side storage like LocalStorage, browser cache, or transient storage like JavaScript variables in a data layer.
-
#8: Client-side Security Logging and Monitoring Failures
Insufficient monitoring and detection of client-side changes and data accesses, particularly failures and errors, in real-time as each page is assembled and executed using both first-party and third-party code. Just like OWASP Top 10: A09-2021 - Security Logging and Monitoring Failures, but focused on client-side behavior.
-
#9: Not Using Standard Browser Security Controls
Not using common standards-based security controls built into browsers such as iframe sandboxes, and security headers like Content Security Policy (CSP), subresource integrity, and many other standard security features.
FortiWeb helps bridge this gap by automatically inserting key browser-enforced security headers into HTTP responses — even if the application itself doesn’t set them — ensuring these controls are consistently applied.
-
#10: Including Proprietary Information on the Client-Side
Presence of sensitive business logic, developer comments, proprietary algorithms, or system information contained in client-side code or stored data.
FortiWeb’s Layered Defense Against Client-Side Security Threats
FortiWeb actively prevents and mitigates these attacks by controlling how browsers behave, validating resource integrity, and securing sensitive data. Its layered protection strategy provides defense before, during, and even after the browser is comprised.
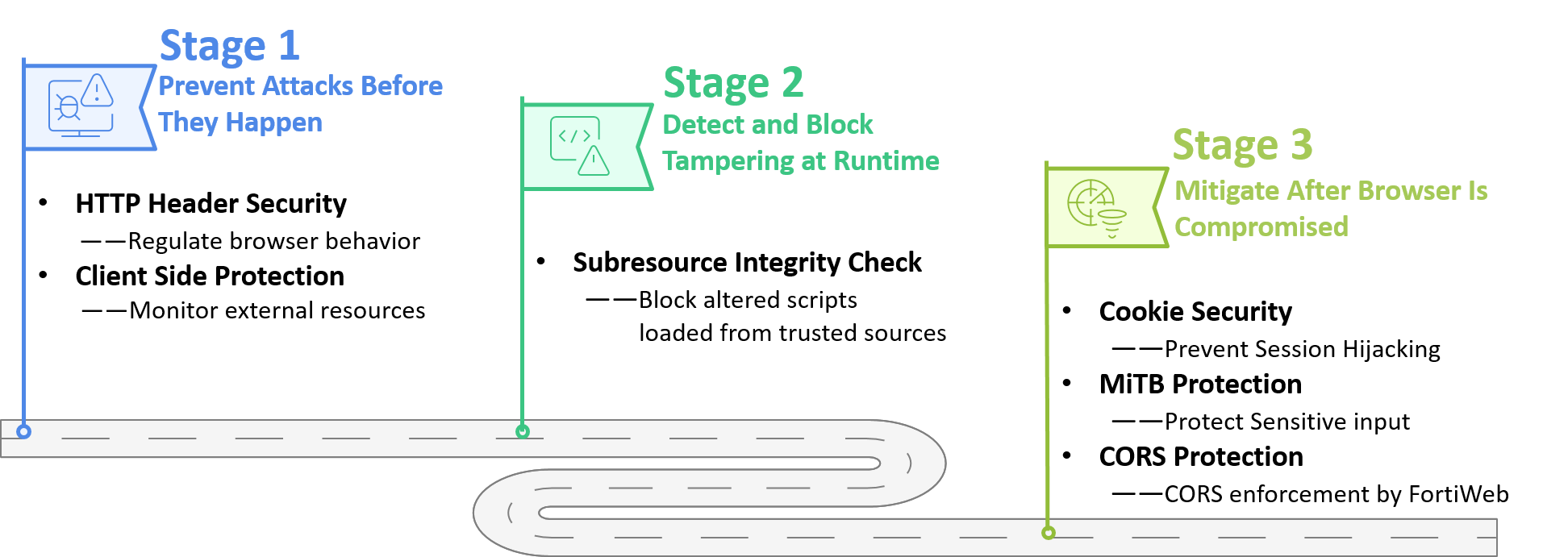
Stage 1: Prevent Attacks Before They Happen
The goal of this stage is to prevent malicious scripts from executing by enforcing strict browser behavior policies.
-
HTTP Header Security
FortiWeb’s HTTP Header Security feature inserts security headers into the response to regulate browser-side behavior. It instructs the browser on how to handle inline scripts and which external resources are considered trustworthy.
FortiWeb inserts security headers to:
-
Block inline scripts
-
Restrict script sources to trusted origins
-
Control how external resources (scripts, images, styles) are loaded.
-
OWASP Client-Side Risks Addressed:
-
#2: DOM-based XSS
-
#3: Sensitive Data Leakage
-
#4: Vulnerable and Outdated Components
-
#5: Lack of Third-party Origin Control
-
#6: JavaScript Drift
-
#9: Not Using Standard Browser Security Controls
-
#10: Including Proprietary Information on the Client Side
Stage 2: Detect Tampering at Runtime
This stage detects tampering of scripts and assets as they are loaded into the browser—even from trusted sources.
-
Subresource Integrity (SRI)
Verifies that JavaScript or CSS files match their expected cryptographic hashes. If a file has been altered (e.g., due to a compromised CDN or injection), it is blocked from execution.
OWASP Client-Side Risks Addressed:
-
#4: Vulnerable and Outdated Components
-
#5: Lack of Third-party Origin Control
-
#6: JavaScript Drift
Stage 3: Mitigate After Browser Is Compromised
If an attack succeeds, FortiWeb still works to contain the damage and protect critical data.
-
Cookie Security
Automatically applies cookie attributes such as HttpOnly, Secure, and SameSite to prevent theft or tampering of session data.
-
MitB Protection
Encrypts sensitive user inputs (e.g., login credentials, payment fields) and includes anti-keylogging mechanisms to secure data in transit.
-
CORS Protection
Enforces origin and method validation for cross-origin requests. Any request from an untrusted origin or using disallowed methods is blocked before it reaches your backend servers.
OWASP Client-Side Risks Addressed:
-
#1: Broken Client-side Access Control
-
#2: DOM-based XSS
-
#3: Sensitive Data Leakage
-
#7: Sensitive Data Stored Client-Side
-
#8: Client-side Logging and Monitoring Failures
-
#10: Including Proprietary Information on the Client Side
Monitoring Client Side Risks
FortiWeb’s Client-Side Protection is specifically designed to help you monitor and control third-party scripts and services loaded in your web application. It analyzes your front-end code and automatically identifies all external services and domains involved.
With Client-Side Protection, you can monitor the types of content retrieved from external services, assess the risk level of each script, check whether the connections are encrypted, and see how frequently they are loaded by clients. Based on this information, you can choose to allow, block, or annotate each service—enabling you to build a precise and secure Content-Security-Policy (CSP) that minimizes exposure to untrusted sources.
OWASP Client-Side Risks Addressed:
-
#8: Client-side Logging and Monitoring Failures
For best practices of configuring FortiWeb to effectively defend against the Client-Side Security risks, see WAF Solutions against OWASP Top 10 Client-Side Security Risks.

