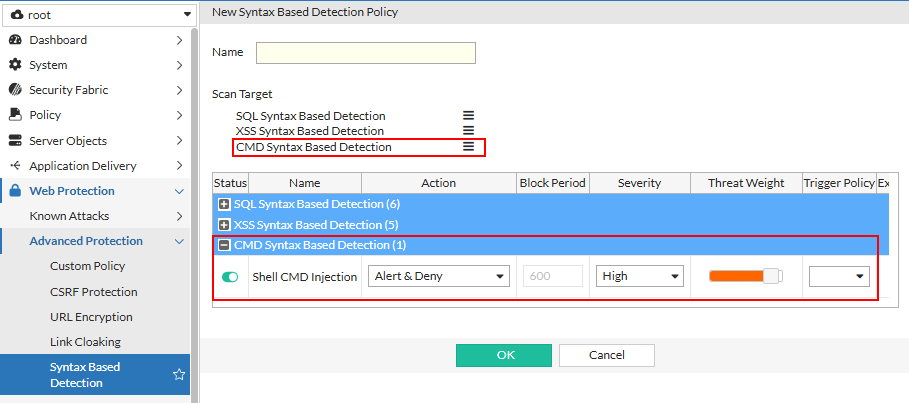
CMD Syntax-Based Detection for Command Injection (8.0.0)
FortiWeb 8.0.0 expands its syntax-based detection capabilities with CMD Syntax Based Detection, a powerful new method for identifying command injection (CMDi) attacks that use shell commands such as ls, cat, or curl.
Unlike traditional signature-based methods—which rely on pattern matching alone—syntax-based detection evaluates the structure and intent of shell commands. This allows FortiWeb to accurately detect obfuscated or multi-stage payloads that would otherwise evade conventional defenses, while also reducing false positives caused by benign keyword usage.
How It Differs from Other Syntax-Based Detection
FortiWeb already supports syntax-based detection for SQL Injection and Cross-Site Scripting (XSS). These engines are optimized for identifying malicious use of structured query language or JavaScript within request payloads.
CMD Syntax Based Detection, in contrast, is tailored for shell command execution attempts. It focuses on detecting the misuse of command-line utilities and shell syntax—such as:
-
Command chaining (
;,&&,||) -
Variable substitution (
$cmd,$(...)) -
Obfuscation through quotes, concatenation, or escape sequences
Why This Matters
Attackers increasingly use sophisticated obfuscation to hide command injection attempts, for example:
-
Splitting commands into character fragments:
'c''a''t' -
Encoding payloads or using dynamic assignment:
cmd=il;k${cmd}l 888 -
Injecting command substitution within other expressions:
`id`or$(whoami)
CMD Syntax Based Detection helps security teams identify these evasive techniques and enforce stronger protections against remote command execution.
Limitations
CMD Syntax Based Detection in this version focuses solely on detecting shell command expressions. The following limitations apply:
-
Command arguments are not analyzed. Only the shell command itself (e.g.,
ls,cat,curl) is detected. Arguments passed to these commands (e.g., file paths or options) are not included in the detection logic.Example:
'c''a''t' /etc/pa''ss''wd— FortiWeb detects the obfuscatedcatcommand, but not the/etc/passwdargument. -
Full shell scripts and complex control flows are not supported. Detection does not extend to constructs such as
if,for, orwhilestatements. -
Non-shell scripting languages are excluded. This includes interpreted languages like Python, PHP, and Node.js.

