Wildcard Matching Support for Global Cookie Allow Lists (7.6.4)
FortiWeb now supports wildcard pattern matching in cookie names for entries in the Global Allow List and the Policy Based Allow List. This enhancement increases flexibility when defining global exceptions for known benign cookies, especially those with dynamic names generated on the client side—such as cookies set by Google Analytics (_ga, _gid, _gac_*, _ga_*).
Previously, cookie names in the Global Allow List/Policy Based Allow List required exact matches, which made it difficult to accommodate variations in automatically generated cookie names. With wildcard support, administrators can now define global exceptions using the asterisk (*) symbol to represent variable segments of a cookie name.
Wildcard matching rules:
-
Up to two asterisks (
*) are supported per pattern. -
Wildcards can appear at the beginning, middle, or end of the string.
-
Matching is case-sensitive.
Example patterns:
-
_ga*matches_ga,_ga123 -
*_gidmatches_gid,abc_gid -
aaa*bbbmatchesaaabbb,aaa123bbb -
*aaa*bbbmatchesxyzaaa123bbb
This enhancement allows the Cookie Security module to safely bypass specified patterns at a global level, reducing false positives and ensuring compatibility with widely-used tracking and analytics services.
Server Objects > Global > Global Allow List
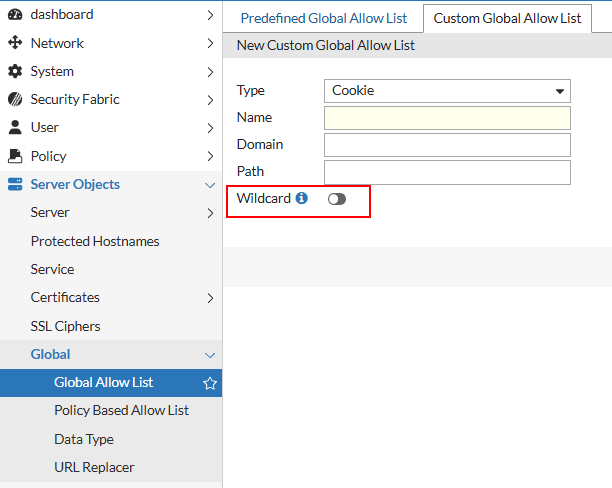
CLI Syntax:
config server-policy pattern custom-global-white-list-group
edit <name>
set type Cookie
set wildcard {enable|disable}
next
end
Server Objects > Global > Policy Based Allow List
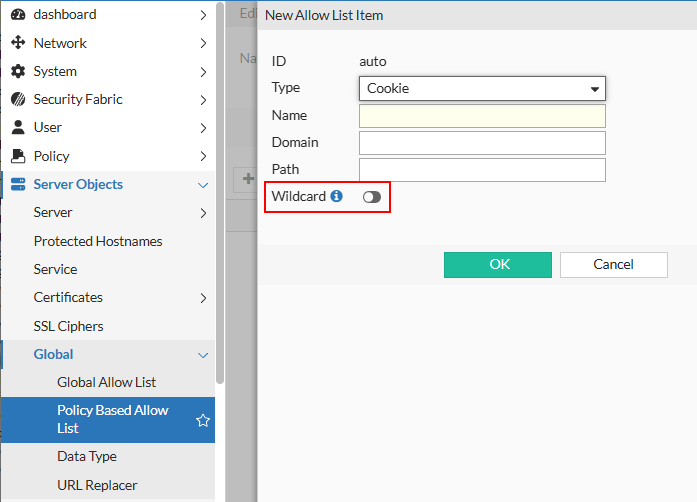
CLI Syntax:
config server-policy allow-list
edit <name>
config allow-list-items
edit <entry_index>
set type Cookie
set wildcard {enable|disable}
next
end
next
end

