Port block allocation with NAT64
Port block allocation (PBA) support for NAT64 is supported on FortiGates with a hyperscale firewall license. This feature has been added to mainstream FortiOS to make it available to non-hyperscale customers, including customers running a VM version of FortiOS. Hyperscale firewall logging is designed for optimal performance and does not have the same detailed logging features as are available for non-hyperscale traffic.
config firewall ippool
edit <name>
set type port-block-allocation
set nat64 enable
next
end
Example
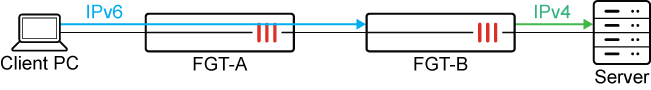
In this example, a NAT64 virtual IPv6 address and PBA IP pool are configured on FGT-B. IPv6 traffic from the client PC is able to access the IPv4 server.
|
|
The IPv6 addresses used in this example are for demonstrative purposes only and should not be used in your environment. The 2001:db8::/32 prefix is a special IPv6 prefix designated for use in documentation examples. See RFC 3849 for more information. |
To configure PBA for NAT64 on FGT-B:
-
Configure the IP pools and enable NAT 64:
(vdom1) config firewall ippool edit "ippool4-1072390-1" set type port-block-allocation set startip 172.16.164.164 set endip 172.16.164.164 set block-size 64 set num-blocks-per-user 1 set pba-timeout 60 set nat64 enable next edit "ippool4-1072390-2" set type port-block-allocation set startip 172.16.164.165 set endip 172.16.164.165 set block-size 64 set num-blocks-per-user 1 set pba-timeout 60 set nat64 enable next end -
Configure the virtual IP for IPv6:
(vdom1) config firewall vip6 edit "vip64-1072390" set extip 64:ff9b::-64:ff9b::ffff:ffff set nat66 disable set nat64 enable set embedded-ipv4-address enable next end -
Configure the firewall policy:
(vdom1) config firewall policy edit 1072390 set srcintf "port7" set dstintf "port1" set action accept set nat64 enable set srcaddr "all" set dstaddr "all" set srcaddr6 "all" set dstaddr6 "vip64-1072390" set schedule "always" set service "ALL" set auto-asic-offload disable set ippool enable set poolname "ippool4-1072390-1" "ippool4-1072390-2" next end -
Send IPv6 packets from the client to access the IPv4 server.
-
Verify the NAT64 sessions:
(vdom1) # diagnose sys session6 stat misc info: session_count=128 setup_rate=0 exp_count=0 reflect_count=0 clash=0 memory_tension_drop=0 ephemeral=0/0 removeable=0 extreme_low_mem=0 npu_session_count=0 nturbo_session_count=0 delete=0, flush=3, dev_down=0/0 ses_walkers=0There are 128 sessions allocated to the two PBA IP pools.
-
Verify the PBA IP pools status:
(vdom1) # diagnose firewall ippool list list ippool info:(vf=vdom1) ippool ippool4-1072390-1: id=1, block-sz=64, num-block=1, fixed-port=no, use=5 nat ip-range=172.16.164.164-172.16.164.164 start-port=5117, num-pba-per-ip=944 clients=2, inuse-NAT-IPs=1 total-PBAs=944, inuse-PBAs=1, expiring-PBAs=1, free-PBAs=99.89% allocate-PBA-times=2, reuse-PBA-times=0 ippool ippool4-1072390-2: id=2, block-sz=64, num-block=1, fixed-port=no, use=4 nat ip-range=172.16.164.165-172.16.164.165 start-port=5117, num-pba-per-ip=944 clients=1, inuse-NAT-IPs=1 total-PBAs=944, inuse-PBAs=1, expiring-PBAs=0, free-PBAs=99.89% allocate-PBA-times=1, reuse-PBA-times=0Each IP pool uses one IPv4 address and one block (64 ports) for SNAT.
-
Verify the PBAs in the IP pools in the current VDOM:
(vdom1) # diagnose firewall ippool list pba user 2001:db8:d0c:1::1, 172.16.164.164, 5181-5244, idx=1, use=66 user 2001:db8:d0c:1::1, 172.16.164.165, 5117-5180, idx=0, use=66
This output includes the client IP, NAT IP, NAT port range, port block index, and a kernel reference counter.
-
Verify the NAT IPs in use in the current VDOM:
(vdom1) # diagnose firewall ippool list nat-ip NAT-IP 172.16.164.164, pba=1, use=3 NAT-IP 172.16.164.165, pba=1, use=3
This output includes the number of PBAs allocated for the NAT IP and the number of PBAs in use.
-
Verify the number of PBAs assigned to the user IP and the number of PBAs being used:
(vdom1) # diagnose firewall ippool list user User-IP 2001:db8:d0c:1::1, pba=1, use=3 User-IP 2001:db8:d0c:1::1, pba=1, use=3

