Zone
Zones are a group of one or more physical or virtual FortiGate interfaces that you can apply firewall policies to for controlling inbound and outbound traffic. Grouping interfaces and VLAN subinterfaces into zones simplifies creating firewall policies where a number of network segments can use the same policy settings and protection profiles.
When you add a zone, you select the names of the interfaces and VLAN subinterfaces to add to the zone. Each interface still has its own address. Routing is still done between interfaces, that is, routing is not affected by zones. You can use firewall policies to control the flow of intra-zone traffic.
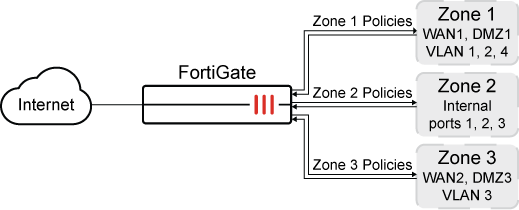
For example, in the sample configuration below, the network includes three separate groups of users representing different entities on the company network. While each group has its own set of ports and VLANs in each area, they can all use the same firewall policy and protection profiles to access the Internet. Rather than the administrator making nine separate firewall policies, he can make administration simpler by adding the required interfaces to a zone and creating three policies.
Example configuration
You can configure policies for connections to and from a zone but not between interfaces in a zone. For this example, you can create a firewall policy to go between zone 1 and zone 3, but not between WAN2 and WAN1, or WAN1 and DMZ1.
To create a zone in the GUI:
-
Go to Network > Interfaces.

If VDOMs are enabled, go to the VDOM to create a zone.
-
Click Create New > Zone.
-
Configure the Name and add the Interface Members.
-
Enable or disable Block intra-zone traffic as required.
-
Click OK.
To configure a zone to include the interfaces WAN1, DMZ1, VLAN1, VLAN2 and VLAN4 using the CLI:
config system zone
edit zone_1
set interface WAN1 DMZ1 VLAN1 VLAN2 VLAN4
set intrazone {deny | allow}
next
end
Using zone in a firewall policy
To configure a firewall policy to allow any interface to access the Internet using the CLI:
config firewall policy
edit 2
set name "2"
set srcintf "zone_1"
set dstintf "port15"
set srcaddr "all"
set dstaddr "all"
set action accept
set schedule "always"
set service "ALL"
set nat enable
next
end
Intra-zone traffic
In the zone configuration you can set intrazone deny to prohibit the different interfaces in the same zone to talk to each other.
For example, if you have ten interfaces in your zone and the intrazone setting is deny. You now want to allow traffic between a very small number of networks on different interfaces that are part of the zone but you do not want to disable the intra-zone blocking.
In this example, the zone VLANs are defined as: 192.168.1.0/24, 192.168.2.0/24, ... 192.168.10.0/24.
This policy allows traffic from 192.168.1.x to 192.168.2.x even though they are in the same zone and intra-zone blocking is enabled. The intra-zone blocking acts as a default deny rule and you have to specifically override it by creating a policy within the zone.
To enable intra-zone traffic, create the following policy:
|
Source Interface |
Zone-name, e.g., |
|
Source Address |
192.168.1.0/24 |
|
Destination |
Zone-name (same as Source Interface, i.e., |
|
Destination Address |
192.168.2.0/24 |

