What's new
The following sections list new features and changes for each FortiEndpoint release:
- What's new for 26.1.b
- What's new for 26.1.a
- What's new for 25.3
- What's new for 25.1
- What's new for 24.4
What's new for 26.1.b
-
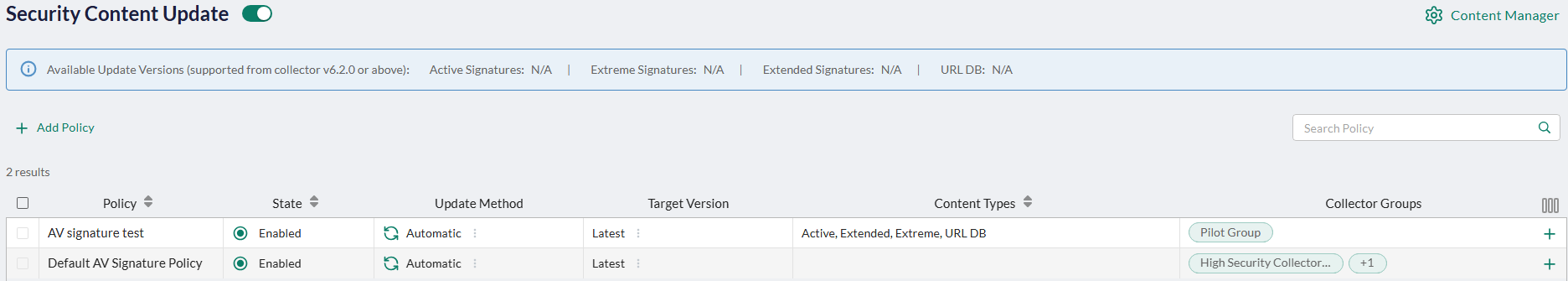
New EDR AV Signature policy to support OT and segmented environments that require controlled update windows (under Profiles > Security > Security Content Update in the EDR page). Use the AV Signature policy to define when and how EDR Collector groups download AV signatures for each type (Active, Extended, Extreme, and URL DB) based on time-based rules and time zones.
-
New green color scheme of the EDR page (see above) for consistency with the EMS page.
What's new for 26.1.a
-
Windows Hello Business support for FortiGate SAML-based IPsec VPN—For FortiGate SAML-based auto-connect IPsec VPN tunnels using Microsoft Entra ID, Windows Hello for Business (key-based or certificate-based) authentication users now automatically connect to the tunnel after Windows login (using MFA with PIN or biometrics, such as fingerprint or facial recognition) without the need to re-authenticate for the VPN connection using the Entra ID username and password.
- Improve ZTNA and VPN troubleshooting process—EMS can now collect time-correlated IPsec VPN and ZTNA-related logs from FortiGate and FortiClient to help troubleshoot ZTNA and VPN integration issues between FortiGate and EMS.
- Support Referrer Host on Windows, macOS, and Linux—You can now define exclusions based on the referrer host (source) URL on FortiClient Windows, macOS, and Linux using the Referrer Host option in FortiEndpoint (see Web Filter) or the
<referrer>XML option. - Added support for uploading a custom FortiClient installer. To do so, go to Deployment & Installers > FortiClient Installer, click Add, and enable the Create a manual installer option under Advanced Options at the bottom of the General tab. See Adding a FortiClient installer in the FortiEndpoint Administration Guide for more information.
- FortiEndpoint EDR features and changes:
- Secure browser—This feature is disabled by default.
- The Forensics Viewer is back with the flow analyzer view, stacks view, and compare view.
- Inconclusive events now appear in the Incidents view only if the FCS verdict is Malicious or Suspicious. The Action of such events will be Post Detection (
) or Post Detection (Simulation) (
), depending on whether the EDR console is in Prevention or Simulation mode. See Incidents pane for more information.
- GUI enhancements:
- "Raw data item" is renamed "variant"
- Loading exceptions on supported Collectors only
- Enhanced validation to exclusion fields
What's new for 25.3
- FortiDeceptor integration—FortiDeceptor can connect to EMS, leveraging EMS capabilities to push deception tokens to FortiClient endpoints more efficiently without requiring mobile device management or group policy objects.
- FortiData integration—FortiClient can integrate with FortiData to retrieve file data labels and use them to control file access.
- Dual IPsec VPN tunnel support—You can create dual IPsec VPN IKEv2 connections for EMS-managed IPsec VPN tunnels, which allows you to route internet traffic through multiple VPN gateways for enhanced security.
- On-demand forensic artifact collection with forensic engine—Fortinet forensic analysts can request additional files from the endpoint for analysis on a case-by-case basis beyond the predefined set that the forensic engine collects. You can define the specific artifacts that the forensic agent collects and sends to EMS on-demand. You and forensic analysts can review these collected artifacts.
- RADIUS server authentication for administrators—You can configure a RADIUS server as an authentication server for EMS administrators so that they can log in to EMS with their RADIUS credentials. To enhance redundancy and scalability in the authentication process, you can configure multiple RADIUS servers for one EMS instance so that users can authenticate through various servers.
- Endpoint health check—In Endpoints > All Endpoints, the endpoint summary includes a new Endpoint Health section (which replaces the previous Features section) with a comprehensive view of feature statuses, such as whether a feature is installed, not installed, enabled, or disabled. It also reports any warnings or error messages associated with a feature.
- Support FortiClient ARM installer creation and deployment—FortiEndpoint supports creating and deploying an ARM installer to a Windows endpoint. You can also upload a repackaged ARM installer file to FortiEndpoint.
- FortiEndpoint EDR features and changes:
- Host firewall—Use the new Communications Control > Host Firewall page to configure host firewall policies to control incoming and outgoing network traffic to protect endpoints against unwanted connections based on remote addresses, protocols, or applications in use to reflect the organization’s network policies.
- Disk encryption management for Windows and macOS endpoints—Use the new Security Settings > Disk Encryption page to configure disk encryption policies to enforce disk encryption on Windows 7 or later (using BitLocker, TPM is required) and macOS (using FileVault) endpoints to ensure consistent security configurations and compliance with regulatory requirements.
- New progress bar when exporting Communication Control applications
- The top-level row of the incidents view now represents an incident entity with its own state independent from the associated child events. As a result, filters are applied to both the top-level incidents and their child events. An incident may appear on its own if it matches the filter criteria even if none of its child events do.
- Localization - Chinese support
What's new for 25.1
- ZTNA automatic login using Microsoft Entra ID—When a user is logged in to an Entra ID domain on an endpoint then attempts to access zero trust network access (ZTNA) TCP-forwarding traffic, FortiClient automatically authenticates with the FortiGate using Entra ID credentials without the need for manual authentication. This feature requires FortiOS 7.6.1 or later.
- FortiPAM agent for macOS—You can now install FortiClient with the FortiPAM feature enabled on a macOS endpoint.
- FortiEndpoint now automatically retrieves FortiAnalyzer Cloud SNI information (account ID) and populates it in endpoint log settings if the administrator's FortiCloud account has a FortiAnalyzer Cloud entitlement. You only need to enable Auto-config FAZ Cloud in Endpoint Profiles > System Settings > Log to automatically populate the FortiAnalyzer Cloud connection information in the IP Address/Hostname field.
- EAP-TTLS support for IPsec VPN—When using IKEv2, user authentication is handled via Extensible Authentication Protocol (EAP). In FortiEndpoint, you can now configure FortiClient to use EAP-TTLS for authentication, which provides a more secure and flexible user authentication method. Only IKEv2 supports EAP-TTLS.
- Zero Trust tag renamed security posture tag
- Security posture tags enhancements for easier management, for example, you can now easily add descriptions for tags and manage tags and rules in a single page for simplicity.
- Upload custom certificate and private key for ZTNA—You can upload a custom intermediate root certificate and private keys to FortiEndpoint to use for signing zero trust network access (ZTNA) endpoint certificates instead of relying on the default certificate,
default_ZTNARootCA.pem. This provides flexibility for organizations that need custom certificate chains for compliance or security reasons. It can also streamline the end user experience by helping to avoid certificate trust issues. - Consolidated endpoint events—You can now view all events from all endpoints and take actions as necessary in the new Endpoints > All Events page.
- Syncing remote categories from imported FortiOS or FortiManager Web Filter profile—Web Filter profiles imported from FortiOS or FortiManager to FortiEndpoint now include FortiGuard Category Based Filter > Remote Categories. Endpoints that are assigned this profile can follow this URL filter list to block outbound connections to known malicious URLs and domains. Prior to this enhancement, you had to manually update the FortiOS static URL filter list, which was time-consuming, error-prone, and inconvenient.
- Vulnerability detection popup—You can now configure FortiClient to display a Vulnerabilities Scan Summary popup to the user after a vulnerability scan on the endpoint.
- FortiEndpoint EDR features and changes:
- The Event Viewer tab is renamed Incidents with usability improvements, such as tabbed view of different types of incidents. Clicking on an incident displays the Handle Incident button and an embedded preview of the investigation view within the console where you can perform operations without opening a separate tab.
- eXtended detection with custom external systems—You can now add custom external systems as eXtended detection source when you create an extended detection connector in the Administration > Integrations page.
- Device security posture indicator for Windows and macOS endpoints—The Inventory > Collectors page includes the new DEVICE SECURITY column which provides insights into the security posture of Windows and macOS endpoints based on OS-level configurations.
- Visibility into external attack surface with FortiRecon integration—Analysts can prioritize security alerts and incidents based on risk factors such as severity of vulnerabilities, relevance of threat intelligence feeds, and severity of affected endpoints, ensuring that efforts are focused on addressing the most significant risks to the organization.
- New look and feel of the EDR console
What's new for 24.4
Initial release.

