Configuring FortiData integration
You can configure an integration between FortiClient, EMS, and FortiData. FortiData is a document classification and labeling service. It contains a database (DB) of your file hashes, along with file metadata, including a data category (optional) and a label. The file data labels work in the same way as Microsoft's Purview Information Protection labels, although the labels are not included in the file content but are associated with the file hash in the FortiData DB. A label taxonomy is defined to represent the various classification levels required for an organization. FortiClient can integrate with FortiData to retrieve file data labels and use them to control file access.
The following describes how the integration functions once configured:
- The EMS administrator configures a FortiData Fortinet Security Fabric Connector to establish trust. EMS and FortiData communicate in the following ways:
- EMS pulls a data label list from FortiData to use in Data Protection profiles.
- EMS send its certificate to FortiData to verify tokens that managed endpoints send for lookup.
- FortiData must provide a connector API key for Fabric connection with EMS.
- Any other information exchanges between EMS and FortiData are done via this connector.
- FortiData only accepts requests from endpoints that this EMS manages. FortiData verifies this using the EMS serial number.
- EMS sends FortiData a zero trust network access (ZTNA) certificate that FortiData to verify FortiClient requests. FortiData must provide the API key to receive the ZTNA certificate.
- The EMS administrator defines a Data Protection profile to monitor access to a file based on its data label.
- The EMS administrator defines which file types to send to FortiData for classification lookup. FortiClient only sends the selected file types for lookup. FortiData supports file uploads for OCR, such as JPEG and GIF.
- When a user downloads or opens a file that matches the configuration, FortiClient performs a hash lookup and retrieves the data label from FortiData for that file.
- FortiClient sends its token with the request to authenticate with FortiData to authorize the endpoint.
- FortiClient enforces file access based on classification rules that EMS defined. All file monitor activity is logged.
FortiClient and EMS support integration with FortiData 7.6.1 and later versions. This feature requires the Endpoint Protection Platform license.
To configure FortiData for the integration:
- Install FortiData-VM 7.6.1.
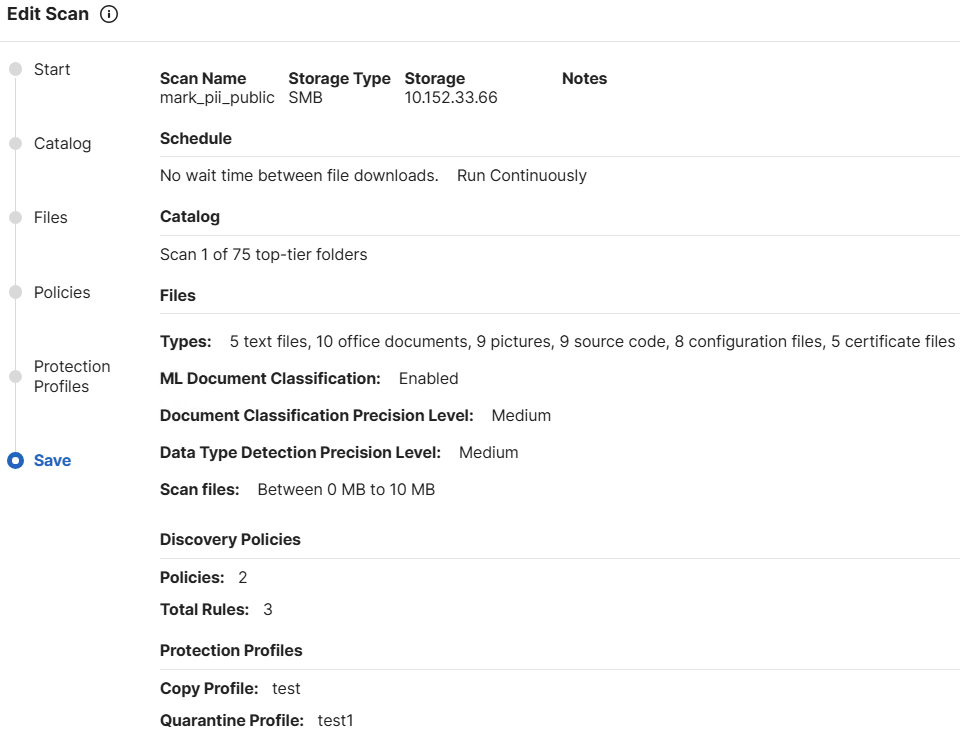
- Configure FortiData discovery policies for file scanning on the endpoint:
- Go to Discovery > Policies.
- Create and configure a policy as desired.
- Configure scan policies to scan for those files. FortiData scans files and assigns labels to files that match the policy after the scan completes:
- Go to Discovery > Scans.
- Configure the scan policy as desired.
- For FortiData and EMS to establish Fabric connection, you must upload a publicly signed certificate to FortiData. Upload the certificate:
- Go to System > Certificates.
- Click Import Certificate > Add a new certificate.
- Upload the certificate and key files.
- Go to Fabric > HTTP2 Service > API Keys. Click New API Key. You will use this API key to establish Fabric connection between EMS and FortiData.
- Create a Fabric connector for EMS in FortiData:
- Go to Fabric > HTTP2 Service.
- Under Settings, configure a new device.
- From the Device Type dropdown list, select FortiClient EMS.
- In the IPv4 Address / Ranges field, enter 0.0.0.0/0.
- Click Enable API Key Authentication.
- From the Associated Scan Policies dropdown list, select the scan policy that you created.
- From the Associated Discovery Policies dropdown list, select the discovery policy that you created.
- Click Save.
- Create a Fabric connector for FortiClient in FortiData:
- Go to Fabric > HTTP2 Service.
- Under Settings, configure a new device.
- From the Device Type dropdown list, select FortiClient.
- Click Enable Client Certificate Validation Using EMS CA.
- Click Save.
To configure the integration in EMS:
- Create a FortiData connector:
- In EMS, go to Fabric & Connectors . Fabric Devices.
- Click Add.
- From the Connector Type dropdown list, select FortiData.
- In the FortiData Hostname / IP address field, enter the FortiData IP address.
- In the FortiData Port field, enter 8443.
- In the FortiData REST API Key field, paste the key that you created in FortiData.
- Click Next and complete creating the FortiData connector. Once EMS establishes the connection with FortiData, it queries tags and file types from FortiData.
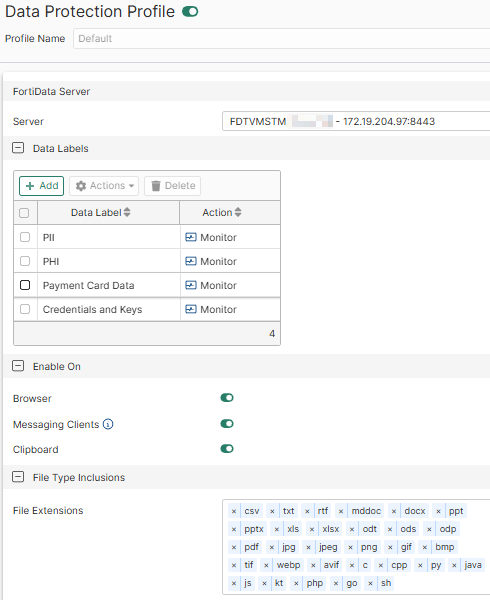
- Create a data protection profile:
- Go to Endpoint Profiles > Data Protection.
- Create a new profile.
- From the Server dropdown list, select the FortiData server.
- Under Enable On, enable Browser, Messaging Clients, or Clipboard to enable the data protection feature on.
- Under File Extensions, select the desired extensions.
- Configure the certificate that you created in FortiData in EMS:
- Go to Endpoint Policy & Components > CA Certificates.
- Click Upload.
- Click Upload File.
- Browse to and select the certificate that you created in FortiData. Click OK.
- Go to Endpoint Profiles > System Settings.
- Create a new profile or edit an existing one.
- Under Other, enable Install CA Certificate on Client.
- Ensure that the desired certificate is selected. FortiClient uses certificate chain validation to verify the FortiData server identity. If you generated your own self-signed certificate for FortiData, you only need to install a root certificate authority (CA) certificate on the endpoint. Using an SSL certificate from a trusted CA is recommended.
- Click Save.
To install FortiClient with FortiData support:
- Run the FortiClient installer on the endpoint. In Additional Security Features, select Data Protection. Configure other installation options as desired.
- After FortiClient connects to EMS, in Registry Editor, confirm that
Computer\HKEY_LOCAL\SOFTWARE\Fortinet\FortiClient\FA_FTDATAexists and includes the configurations from EMS.
To verify the FortiData integration:
- Do one of the following from the endpoint, using a file that matches the conditions configured in FortiData:
- Upload a file to a website.
- Upload a file on a messaging client, such as Microsoft Teams.
- Open a file and take a screenshot. This copies the file to the clipboard.
FortiClient calculates the hash of the file, sends it to FortiData, and checks if the hash matches any labels. If there is a label match, FortiClient monitors access to the file and sends event details to EMS.
- In EMS, go to Endpoints > All Endpoints.
- Select the desired endpoint.
- Go to the Data Protection Events tab. This tab lists the following information about data protection events:
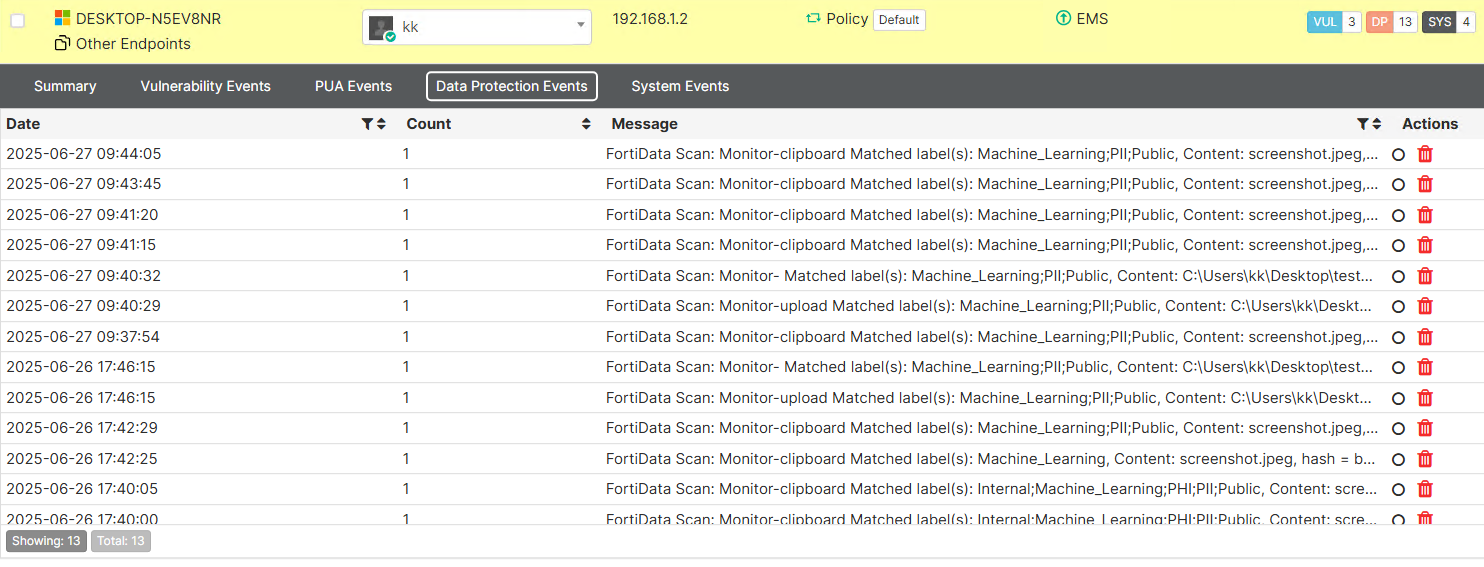
Date/time of event
User name
Hostname
Action type, i.e. monitor or block.
Mode: either simulation or protection mode.
File hash
Data Label
Filename/path
- After uploading the file check fcaptmontrace_1 logs in the trace folder, you can see the matched label and file name and uploaded platform. The following shows example logs for different scenarios:
Scenario
Log example
Browser upload
[2025-06-27 09:59:25.2311041 UTC-07:00] [4244:4656] [fcaptmontrace 431 info] sending ems alert,C:\Users\kk\Desktop\testpkg\testpkg\phi_internal\phi_1_patient_admission_notes--patient_name-dob-diagnosis.png,Monitor- Matched label(s): Internal;Machine_Learning;PHI;PII, Content: C:\Users\kk\Desktop\testpkg\testpkg\phi_internal\phi_1_patient_admission_notes--patient_name-dob-diagnosis.png, hash = 9fc7c807621dadcf29e459db8569884ddce8e718,,Monitor,9fc7c807621dadcf29e459db8569884ddce8e718,Internal;Machine_Learning;PHI;PII,chrome.exe
Screenshotted (clipboard)
[2025-06-26 17:40:04.2583481 UTC-07:00] [5780:10548] [fcaptmontrace 431 info] sending ems alert,screenshot.jpeg,Monitor-clipboard Matched label(s): Internal;Machine_Learning;PHI;PII;Public, Content: screenshot.jpeg, hash = fedbfa3746a420fbd86342077eb04dbd7d821947,clipboard,Monitor,fedbfa3746a420fbd86342077eb04dbd7d821947,Internal;Machine_Learning;PHI;PII;Public,clipboard
Sent via Microsoft Teams
[2025-06-26 17:46:15.0600390 UTC-07:00] [5780:12240] [fcaptmontrace 431 info] sending ems alert,C:\Users\kk\Desktop\testpkg\testpkg\pii_public\pii--50_names.txt,Monitor- Matched label(s): Machine_Learning;PII;Public, Content: C:\Users\kk\Desktop\testpkg\testpkg\pii_public\pii--50_names.txt, hash = 42f2c523834b26ae6934d73de2238a656eafba22,,Monitor,42f2c523834b26ae6934d73de2238a656eafba22,Machine_Learning;PII;Public,msedgewebview2.exe
Sent via Telegram
[2025-06-27 09:40:28.7196748 UTC-07:00] [4244:5768] [fcaptmontrace 431 info] sending ems alert,C:\Users\kk\Desktop\testpkg\testpkg\pii_public\pii--50_names-50_ssns-50_us_drivers_licenses.xlsx,Monitor- Matched label(s): Machine_Learning;PII;Public, Content: C:\Users\kk\Desktop\testpkg\testpkg\pii_public\pii--50_names-50_ssns-50_us_drivers_licenses.xlsx, hash = 3a0b43d3e2e5998e40c45adbaae260bf7900d9be,,Monitor,3a0b43d3e2e5998e40c45adbaae260bf7900d9be,Machine_Learning;PII;Public,Telegram.exe
-
To check the logs in FortiData, run the following commands:
diagnose logs http2 50 diagnose logs analyzer 50
The following shows example output from these commands:
[DEBUG] 2025/06/26 03:10:28.160563 tag_info_service.go:58 Updated tag cache: map[APPI:Compliance APPs:Compliance ASIA:Data Residency AUSTRALIA:Data Residency BRAZIL:Data Residency CCPA:Compliance CSL:Compliance Clinical Records:Data Classification Clinical Studies:Data Classification Compliance and Risk Management:Data Classification Confidential:Sensitivity Configuration Files:Data Classification Contracts and Agreements:Data Classification Credentials and Keys:Data Classification Credit and Risk Management:Data Classification DPA:Compliance Development Documentation:Data Classification EU:Data Residency Education:Data Classification FERPA:Compliance FISMA:Compliance Finance:Data Classification Financial Report:Data Classification Financial Strategy and Research:Data Classification GDPR:Compliance GLBA:Compliance HIPAA:Compliance HR Documentation:Data Classification Healthcare:Data Classification Highly Confidential:Sensitivity Information Technology:Data Classification Insurance and Settlement:Data Classification Internal:Sensitivity JAPAN:Data Residency LGPD:Compliance Legal:Data Classification License Agreement:Data Classification Manufacture:Data Classification Medication Management:Data Classification NDA Form:Data Classification NIST 800-53 and NIST 800-171:Compliance Operational Documentation:Data Classification PCI_DSS:Compliance PHI:Data Classification PII:Data Classification PIPEDA:Compliance Patent:Data Classification Payment Card Data:Data Classification Performance Review:Data Classification Public:Sensitivity Restricted:Sensitivity SOX:Compliance Source Code:Data Classification Test Documentation:Data Classification Timesheet:Data Classification Training Materials:Data Classification Transaction Record:Data Classification UK:Data Residency US:Data Residency User Documentation:Data Classification] [DEBUG] 2025/06/26 03:15:28.160441 tag_info_service.go:58 Updated tag cache: map[APPI:Compliance APPs:Compliance ASIA:Data Residency AUSTRALIA:Data Residency BRAZIL:Data Residency CCPA:Compliance CSL:Compliance Clinical Records:Data Classification Clinical Studies:Data Classification Compliance and Risk Management:Data Classification Confidential:Sensitivity Configuration Files:Data Classification Contracts and Agreements:Data Classification Credentials and Keys:Data Classification Credit and Risk Management:Data Classification DPA:Compliance Development Documentation:Data Classification EU:Data Residency Education:Data Classification FERPA:Compliance FISMA:Compliance Finance:Data Classification Financial Report:Data Classification Financial Strategy and Research:Data Classification GDPR:Compliance GLBA:Compliance HIPAA:Compliance HR Documentation:Data Classification Healthcare:Data Classification Highly Confidential:Sensitivity Information Technology:Data Classification Insurance and Settlement:Data Classification Internal:Sensitivity JAPAN:Data Residency LGPD:Compliance Legal:Data Classification License Agreement:Data Classification Manufacture:Data Classification Medication Management:Data Classification NDA Form:Data Classification NIST 800-53 and NIST 800-171:Compliance Operational Documentation:Data Classification PCI_DSS:Compliance PHI:Data Classification PII:Data Classification PIPEDA:Compliance Patent:Data Classification Payment Card Data:Data Classification Performance Review:Data Classification Public:Sensitivity Restricted:Sensitivity SOX:Compliance Source Code:Data Classification Test Documentation:Data Classification Timesheet:Data Classification Training Materials:Data Classification Transaction Record:Data Classification UK:Data Residency US:Data Residency User Documentation:Data Classification] [DEBUG] 2025/06/26 03:20:28.159709 tag_info_service.go:58 Updated tag cache: map[APPI:Compliance APPs:Compliance ASIA:Data Residency AUSTRALIA:Data Residency BRAZIL:Data Residency CCPA:Compliance CSL:Compliance Clinical Records:Data Classification Clinical Studies:Data Classification Compliance and Risk Management:Data Classification Confidential:Sensitivity Configuration Files:Data Classification Contracts and Agreements:Data Classification Credentials and Keys:Data Classification Credit and Risk Management:Data Classification DPA:Compliance Development Documentation:Data Classification EU:Data Residency Education:Data Classification FERPA:Compliance FISMA:Compliance Finance:Data Classification Financial Report:Data Classification Financial Strategy and Research:Data Classification GDPR:Compliance GLBA:Compliance HIPAA:Compliance HR Documentation:Data Classification Healthcare:Data Classification Highly Confidential:Sensitivity Information Technology:Data Classification Insurance and Settlement:Data Classification Internal:Sensitivity JAPAN:Data Residency LGPD:Compliance Legal:Data Classification License Agreement:Data Classification Manufacture:Data Classification Medication Management:Data Classification NDA Form:Data Classification NIST 800-53 and NIST 800-171:Compliance Operational Documentation:Data Classification PCI_DSS:Compliance PHI:Data Classification PII:Data Classification PIPEDA:Compliance Patent:Data Classification Payment Card Data:Data Classification Performance Review:Data Classification Public:Sensitivity Restricted:Sensitivity SOX:Compliance Source Code:Data Classification Test Documentation:Data Classification Timesheet:Data Classification Training Materials:Data Classification Transaction Record:Data Classification UK:Data Residency US:Data Residency User Documentation:Data Classification] [DEBUG] 2025/06/26 03:25:28.159904 tag_info_service.go:58 Updated tag cache: map[APPI:Compliance APPs:Compliance ASIA:Data Residency AUSTRALIA:Data Residency BRAZIL:Data Residency CCPA:Compliance CSL:Compliance Clinical Records:Data Classification Clinical Studies:Data Classification Compliance and Risk Management:Data Classification Confidential:Sensitivity Configuration Files:Data Classification Contracts and Agreements:Data Classification Credentials and Keys:Data Classification Credit and Risk Management:Data Classification DPA:Compliance Development Documentation:Data Classification EU:Data Residency Education:Data Classification FERPA:Compliance FISMA:Compliance Finance:Data Classification Financial Report:Data Classification Financial Strategy and Research:Data Classification GDPR:Compliance GLBA:Compliance HIPAA:Compliance HR Documentation:Data Classification Healthcare:Data Classification Highly Confidential:Sensitivity Information Technology:Data Classification Insurance and Settlement:Data Classification Internal:Sensitivity JAPAN:Data Residency LGPD:Compliance Legal:Data Classification License Agreement:Data Classification Manufacture:Data Classification Medication Management:Data Classification NDA Form:Data Classification NIST 800-53 and NIST 800-171:Compliance Operational Documentation:Data Classification PCI_DSS:Compliance PHI:Data Classification PII:Data Classification PIPEDA:Compliance Patent:Data Classification Payment Card Data:Data Classification Performance Review:Data Classification Public:Sensitivity Restricted:Sensitivity SOX:Compliance Source Code:Data Classification Test Documentation:Data Classification Timesheet:Data Classification Training Materials:Data Classification Transaction Record:Data Classification UK:Data Residency US:Data Residency User Documentation:Data Classification]

