Using SSO applications
An SSO application serves as a bridge or gateway between a federation of SAML IdPs and a federation of SAML SPs, as illustrated in the following diagram:
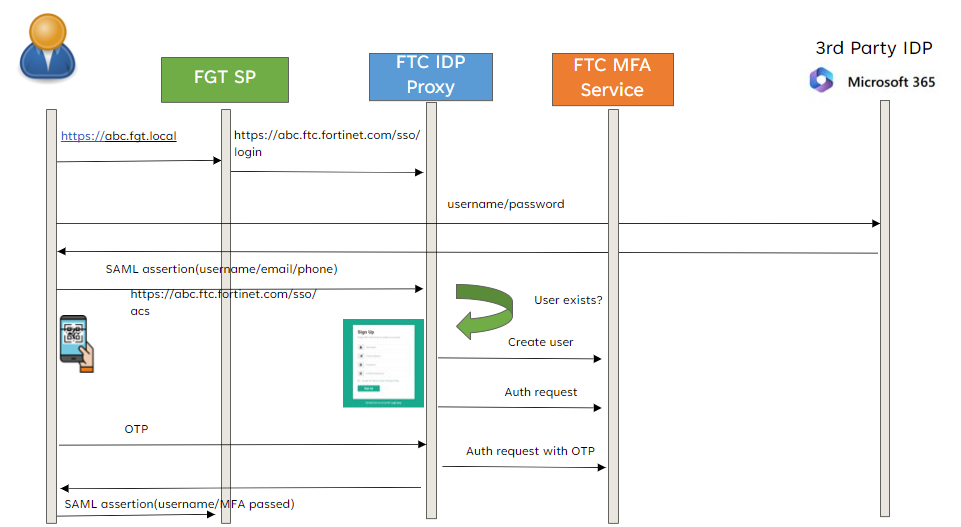
To an SP, an IdP Proxy looks like an ordinary IdP. Likewise, to an IdP, an IdP Proxy looks like an SP. Thus an IdP Proxy has the combined capability of both an IdP and an SP.
With FIC providing the SAML and OIDC IdP interface, we can move the application into the scope of FIC SaaS service and make use of existing SSO protocol to integrate with the Fortinet ecosystem, which already supports SAML log-in. This relieves Fortinet devices from private integration with FIC, as long as they use SAML SP for authentication. FIC can introduce new features such as FIDO and adaptive authentication without downstream support.
Furthermore, customers no longer need to worry about device serial numbers and FIC license ownership.
For more information, see Use Cases.

