Use secondary tunnel for FEC redundant parity packets NEW
In the original implementation of adaptive FEC, FEC parity packets are sent inside the same overlay tunnel. However, the parity packets are susceptible to being dropped at the same rate as other VPN packets.
This enhancement to adaptive FEC introduces the capability to send FEC parity packets in a secondary overlay tunnel that is associated with the same destination. The following setting can be configured on the primary tunnel that requires parity packets to be sent on a redundant tunnel:
config vpn ipsec phase1-interface
edit <tunnel>
set fec-separate-redundant-tunnel enable
next
end
The redundant tunnel must have the same destination location-id as the original tunnel.
Example
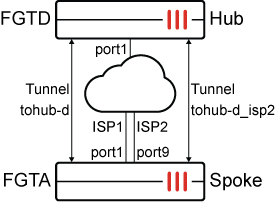
In the following example, a VPN Hub (FGTD) is configured as a dialup VPN gateway. A spoke has two underlays going to different ISPs, where the primary (port1) has 10G bandwidth and the secondary (port9) has 1G bandwidth. Two tunnels are established from the Spoke to the Hub over the two underlays. The intention is to send data over the primary tunnel while using the secondary tunnel for redundancy and parity packets for the primary tunnel.
The FEC mappings are configured to send two parity packets per 8 base packets upon packet-loss threshold above 2%. Additionally, it will send three parity packets per nine base packets when bandwidth exceeds 950Mbps.
This example utilizes one Hub/destination, so the default location-id will be shared between the tunnels without any conflicts. When multiple Hubs are in use, and you need to apply the parity packet duplication on the same Hub and destination, use a different location-id for each hub.
config system settings
set location-id <unique id for each hub>
end
To configure the hub, FGTD:
config vpn ipsec phase1-interface
edit "tospokes"
set type dynamic
set interface "port1"
set ike-version 2
set peertype any
set net-device disable
set mode-cfg enable
set proposal aes128-sha256 aes256-sha256 aes128gcm-prfsha256 aes256gcm-prfsha384 chacha20poly1305-prfsha256
set add-route disable
set dpd on-idle
set dhgrp 20 21
set auto-discovery-sender enable
set fec-ingress enable
set transport auto
set ipv4-start-ip 100.100.100.10
set ipv4-end-ip 100.100.100.20
set ipv4-netmask 255.255.255.0
set psksecret ****************
set dpd-retryinterval 60
next
endconfig vpn ipsec phase2-interface
edit "tospokes"
set phase1name "tospokes"
set proposal aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305
set dhgrp 20 21
next
end
To configure the spoke, FGTA:
-
Configure FEC mapping to bind network SLA metrics and FEC base and redundant packets:
config vpn ipsec fec edit "m1" config mappings edit 1 set base 8 set redundant 2 set packet-loss-threshold 2 next edit 2 set base 9 set redundant 3 set bandwidth-up-threshold 950000 next end next end -
Configure the IPsec tunnels:
On the primary tunnel, enable FEC enabled and apply FEC mapping. The redundant tunnel does not need FEC enabled, or the fec-separate-redundant-tunnel setting.
config vpn ipsec phase1-interface edit "tohub-d" set interface "port1" set ike-version 2 set peertype any set net-device disable set mode-cfg enable set proposal aes128-sha256 aes256-sha256 aes128gcm-prfsha256 aes256gcm-prfsha384 chacha20poly1305-prfsha256 set add-route disable set dhgrp 20 21 set auto-discovery-receiver enable set auto-discovery-shortcuts dependent set fec-egress enable set fec-separate-redundant-tunnel enable set fec-codec rs set fec-health-check "1" set fec-mapping-profile "m1" set transport auto set remote-gw 172.16.200.4 set psksecret **************** next edit "tohub-d_isp2" set interface "port9" set ike-version 2 set peertype any set net-device disable set mode-cfg enable set proposal aes128-sha256 aes256-sha256 aes128gcm-prfsha256 aes256gcm-prfsha384 chacha20poly1305-prfsha256 set add-route disable set dhgrp 20 21 set auto-discovery-receiver enable set auto-discovery-shortcuts dependent set transport auto set remote-gw 172.16.200.4 set psksecret **************** next endconfig vpn ipsec phase2-interface edit "tohub-d" set phase1name "tohub-d" set proposal aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set dhgrp 20 21 set auto-negotiate enable next edit "tohub-d_isp2" set phase1name "tohub-d_isp2" set proposal aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set dhgrp 20 21 set auto-negotiate enable next end -
Configure SD-WAN:
Assign the overlay interface as an SD-WAN member and attach it to a zone. Configure health-check on the overlay member in order to detect packet-loss and bandwidth utilization.
config system sdwan set status enable config zone edit "virtual-wan-link" next end config members edit 1 set interface "port1" set gateway 172.16.200.3 next edit 4 set interface "tohub-d" next edit 5 set interface "port9" set gateway 11.101.1.2 next end config health-check edit "1" set server "192.168.5.44" set members 4 config sla edit 1 next end next end config service edit 2 set name "1_clone" set dst "all" set src "10.1.100.0" set priority-members 4 1 next end end
To verify the results:
-
Confirm that both tunnels are established on their respective interfaces on FGTA:
# diagnose vpn ike gateway list vd: root/0 name: tohub-d_isp2 version: 2 interface: port9 15 addr: 11.101.1.1:5929 -> 172.16.200.4:4500 ext addr: 11.101.1.1 5929 tun_id: 10.0.0.2/::10.0.0.2 remote_location: 0.0.0.0 network-id: 0 transport: TCP virtual-interface-addr: remote: 100.100.100.4 created: 407s ago peer-id: 172.16.200.4 peer-id-auth: no assigned IPv4 address: 100.100.100.11/255.255.255.0 nat: me auto-discovery: 2 receiver pending-queue: 0 PPK: no IKE SA: created 1/1 established 1/1 time 36000/36000/36000 ms IPsec SA: created 1/1 established 1/1 time 36000/36000/36000 ms id/spi: 10217 77f9b317d1c985cd/cd40650eb175ec62 direction: initiator status: established 407-371s ago = 36000ms proposal: aes128-sha256 child: no SK_ei: 3fc9a5151af50e58-fec5cfed3c436fb1 SK_er: de07bdc42f053f82-cdc945fc5a7ad5f4 SK_ai: 0262f60ee41bafa2-2f7b9fc40f38e2b6-415b31885b81b778-b28c62a9915d2e5d SK_ar: 693d5e98d6695490-bc9c26b8a15e5322-0285e96df10e48cc-3535038e2c9a442d PPK: no message-id sent/recv: 2/0 QKD: no PQC-KEM (IKE): no PQC-KEM (all IPsec): no lifetime/rekey: 86400/85728 DPD sent/recv: 00000000/00000000 peer-id: 172.16.200.4 vd: root/0 name: tohub-d version: 2 interface: port1 7 addr: 172.16.200.1:500 -> 172.16.200.4:500 ext addr: 172.16.200.1 500 tun_id: 172.16.200.4/::172.16.200.4 remote_location: 0.0.0.0 network-id: 0 transport: UDP virtual-interface-addr: remote: 100.100.100.4 created: 377s ago peer-id: 172.16.200.4 peer-id-auth: no assigned IPv4 address: 100.100.100.10/255.255.255.0 auto-discovery: 2 receiver pending-queue: 0 PPK: no IKE SA: created 1/1 established 1/1 time 0/0/0 ms IPsec SA: created 1/1 established 1/1 time 0/0/0 ms id/spi: 10218 43bc6decd5bc56af/d5a405f1ff957a2f direction: initiator status: established 377-377s ago = 0ms proposal: aes128-sha256 child: no SK_ei: 677aadd417ae719f-6cc99b2215be8711 SK_er: f2b69ab1aecc08d6-04236a6849b56cae SK_ai: e9294b9b9087f973-9aebb458b27f5b13-39aab03bfee864bf-e616994e29cae238 SK_ar: 7ef28f030c54ef5a-84c9765946e408da-d026e7294a209973-3d607b182eb86ec4 PPK: no message-id sent/recv: 2/0 QKD: no PQC-KEM (IKE): no PQC-KEM (all IPsec): no lifetime/rekey: 86400/85722 DPD sent/recv: 00000000/00000000 peer-id: 172.16.200.4
-
Confirm that FEC is enabled in the egress direction for the tohub-d tunnel:
# diagnose vpn tunnel list list all ipsec tunnel in vd 0 ------------------------------------------------------ name=tohub-d_isp2 ver=2 serial=5 11.101.1.1:5929->172.16.200.4:4500 nexthop=11.101.1.2 tun_id=10.0.0.2 tun_id6=::10.0.0.2 status=up dst_mtu=1500 weight=1 country=ZZ bound_if=15 real_if=15 lgwy=static/1 tun=intf mode=auto/1 encap=none options[0x228]=npu frag-rfc run_state=0 role=primary accept_traffic=1 overlay_id=0 proxyid_num=1 child_num=0 refcnt=5 ilast=31 olast=31 ad=r/2 stat: rxp=347 txp=22 rxb=458878 txb=1410 dpd: mode=on-demand on=1 status=ok idle=20000ms retry=3 count=0 seqno=1802 natt: mode=none draft=0 interval=0 remote_port=0 proxyid=tohub-d_isp2 proto=0 sa=1 ref=3 serial=1 auto-negotiate adr src: 0:0.0.0.0-255.255.255.255:0 dst: 0:0.0.0.0-255.255.255.255:0 SA: ref=3 options=1a227 type=00 soft=0 mtu=1438 expire=42519/0B replaywin=2048 seqno=17 esn=0 replaywin_lastseq=0000015c qat=0 rekey=0 hash_search_len=1 life: type=01 bytes=0/0 timeout=42902/43200 dec: spi=18e0b19e esp=aes key=16 c005a5c587fcd4ad85686868323f7a21 ah=sha256 key=32 3da0b40b525f363355acb3dd445f0131c924b14bb3f704dfd8d7b205412e01d9 enc: spi=c0e46a65 esp=aes key=16 a161fb71279cd02bed75614c16ce48d0 ah=sha256 key=32 34977a64e77716c20d4fdfb4619f0745f8d850e448e0330a64baed64dbc24f91 dec:pkts/bytes=347/458878, enc:pkts/bytes=22/2952 npu_flag=00 npu_rgwy=0.0.0.0:0 npu_lgwy=0.0.0.0:0npu_selid=6 dec_npuid=0 enc_npuid=0 dec_engid=-1 enc_engid=-1 dec_saidx=-1 enc_saidx=-1 ------------------------------------------------------ name=tohub-d ver=2 serial=4 172.16.200.1:0->172.16.200.4:0 nexthop=172.16.200.4 tun_id=172.16.200.4 tun_id6=::172.16.200.4 status=up dst_mtu=1500 weight=1 country=ZZ bound_if=7 real_if=7 lgwy=static/1 tun=intf mode=auto/1 encap=none options[0x228]=npu frag-rfc run_state=0 role=primary accept_traffic=1 overlay_id=0 proxyid_num=1 child_num=0 refcnt=4 ilast=1 olast=1 ad=r/2 stat: rxp=375 txp=937 rxb=40092 txb=61856 dpd: mode=on-demand on=1 status=ok idle=20000ms retry=3 count=0 seqno=16 natt: mode=none draft=0 interval=0 remote_port=0 fec: egress=1 ingress=0 proxyid=tohub-d proto=0 sa=1 ref=31 serial=1 auto-negotiate adr src: 0:0.0.0.0-255.255.255.255:0 dst: 0:0.0.0.0-255.255.255.255:0 SA: ref=6 options=1a227 type=00 soft=0 mtu=1342 expire=42509/0B replaywin=2048 seqno=17aa esn=0 replaywin_lastseq=0000004d qat=0 rekey=0 hash_search_len=1 life: type=01 bytes=0/0 timeout=42898/43200 dec: spi=18e0b19f esp=aes key=16 3e578ce917adbf940e9ad602baa71a92 ah=sha256 key=32 4a23b8861918b8ad336cae572dd17f808e64ee22367a219d00249d06405736cf enc: spi=c0e46a64 esp=aes key=16 b5e7464c94b4847c30c804f7effa8a0d ah=sha256 key=32 bbde5831078147c8b3fd88d0d5112b6110cce75bdb5b23392cc3c2f90c9e4336 dec:pkts/bytes=6/240, enc:pkts/bytes=937/125532 npu_flag=03 npu_rgwy=172.16.200.4:0 npu_lgwy=172.16.200.1:0npu_selid=5 dec_npuid=1 enc_npuid=1 dec_engid=-1 enc_engid=-1 dec_saidx=7399 enc_saidx=4 -
Confirm that the profile selected is sending three parity packets per nine base packets:
# diagnose vpn tunnel fec tohub-d egress: enabled=1 base=9 redundant=3 codec=0 timeout=10(ms) encode=132 encode_timeout=129 encode_fail=0 tx_data=166 tx_parity=396 total_tx_data=166 total_tx_parity=396 ingress: enabled=0 timeout=0(ms) fasm_cnt=0 fasm_full=0 ipsec_fec_chk_fail=0 complete=0 recover=0 recover_timeout=0 recover_fail=0 rx_data=0 rx_parity=0 rx=0 rx_fail=0

