LDAP authentication with IKEv2 using UDP or TCP as transport
EAP-TTLS for LDAP based user authentication in IKEv2
When configuring IPsec VPNs, the user authentication mechanism used depends on the IKE version in use:
-
IKE version 1 uses XAUTH (Extended Authentication) for user authentication.
-
IKE version 2 uses EAP (Extensible Authentication Protocol) for user authentication.
XAUTH in IKEv1 natively supports LDAP based user authentication. In IKEv2, LDAP based user authentication is not directly supported through all EAP methods. To authenticate users against an LDAP server in IKEv2, you must use EAP-TTLS (Tunneled Transport Layer Security). EAP-TTLS allows credentials to be securely transmitted between FortiClient and FortiGate over a TLS tunnel, ensuring secure user authentication.
EAP-TTLS configuration is supported on FortiClient EMS and FortiClient version 7.4.3 and later, see EAP-TTLS support for IPsec VPN.
Both FortiClient and FortiClient EMS must be running compatible versions to enable this functionality, see EMS Compatibility chart.
Transport options: UDP, TCP or Auto mode
Different options can be selected between transport methods such as UDP, TCP, or Auto mode for IKE negotiation and encapsulation of ESP packets.
Traditionally, dial-up IPsec VPNs have used UDP as the transport protocol for IKE negotiations and encrypted traffic. With recent enhancements, IPsec VPNs can now operate over TCP, providing greater flexibility and compatibility in restrictive network environments. Using TCP as transport is beneficial in scenarios where ISPs, firewalls, or proxy servers only allow inbound and outbound TCP traffic and block UDP traffic. You can also specify a custom TCP port for IPsec communication for both FortiGate and FortiClient. For details on configuring a custom TCP port on FortiClient, see IPsec VPN over TCP. For details on configuring a custom TCP port on FortiGate, see Dialup IPsec VPN using custom TCP port.
Requirements for using TCP as transport:
-
IKE version 2
-
FortiClient version 7.4.1 or later, that supports TCP as transport
In Auto mode, IKE initially uses UDP encapsulation. If the UDP connection fails to establish within the defined time threshold, it uses TCP encapsulation as fallback.
To configure the transport mode:
config vpn ipsec phase1-interface
edit <name>
set ike-version 2
set transport {auto | udp | tcp}
set auto-transport-threshold <integer>
next
end
|
Command |
Description |
|---|---|
|
transport {auto | udp | tcp} |
Set the IKE transport protocol:
This command is available when |
|
auto-transport-threshold <integer> |
How long to wait for the UDP connection to establish before falling back IKE/IPsec traffic to TCP, in seconds (1 - 300, default = 15). |
On FortiClient EMS, you can configure the transport method using the FortiClient EMS GUI (see Example) or the XML tag <transport_mode>.
The available values for this XML tag element include:
|
Value |
Description |
|---|---|
|
0 |
UDP transport mode. This is the default and used for most VPN connections. |
|
1 |
TCP transport mode. This is recommended for use in restrictive networks. |
|
2 |
Auto mode. FortiOS dynamically selects the transport mode. |
Here is an example of the <transport_mode> element. It does not include all elements required for a functioning VPN connection:
<forticlient_configuration>
<vpn>
<ipsecvpn>
<connections>
<connection>
<transport_mode>1</transport_mode>
</connection>
</connections>
</vpn>
</forticlient_configuration>
Ensure that the transport settings selected on FortiGate match the settings specified on FortiClient.
Example
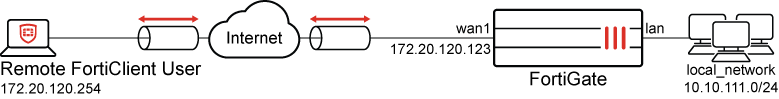
This example demonstrates how to configure an IPsec VPN tunnel using IKEv2 with TCP as the transport protocol and LDAP for user authentication. It also discusses using UDP or Auto mode as transport as an optional step.
On FortiGate, an LDAP server named LDAP-Server is pre-configured to connect to LDAP directory server and is referenced in user group named LDAP-Group. For configuration steps, see Configuring an LDAP server and User groups.
The Group Name option is configured to match users who belong to the Domain Users group on the LDAP server. As a result, only members of the Domain Users group are permitted to connect to the IPsec VPN. For more information on group-based user matching, see Tracking users in each Active Directory LDAP group.
FortiClient is managed by FortiClient EMS. To enable support for both TCP transport and EAP-TTLS (required for secure LDAP authentication with IKEv2), ensure that both FortiClient and FortiClient EMS are running version 7.4.3 or later.
To configure dialup IPsec VPN using IKE version 2 and TCP as transport using GUI:
-
Go to VPN > VPN Wizard.
-
Enter a name for the VPN in the Tunnel name field. In this example, it is dialup_vpn.
-
Set Select a template to Remote Access.
-
Click Begin.
-
Configure the VPN tunnel settings:
Field
Value
VPN client type
FortiClient
Authentication method
Pre-shared key
Pre-shared key
Enter a suitable key.
The same pre-shared key is configured on FortiClient EMS to connect to this IPsec tunnel.
IKE
Version 2
Transport
TCP encapsulation
(Optional) Select UDP for UDP as transport. Ensure that UDP is also configured as desired transport when configuring FortiClient EMS.
(Optional) Select Auto for Auto as transport. Ensure that Auto mode is also configured as desired transport when configuring FortiClient EMS.
Use Fortinet encapsulation
Disable
The Fortinet Inc. encapsulation is RFC 8229 compliant alternative to TCP encapsulation. However, it is not supported by FortiClient.
NAT traversal
Enable
Keepalive frequency
10
EAP peer identification
EAP identity request
User authentication method
Phase 1 interface
Select LDAP-Group from the dropdown list.
Optionally, if you have multiple user groups configured, select Inherit from policy and then specify the groups. See Using single or multiple user groups for user authentication for details.
DNS Server
Use System DNS
-
Click Next.
-
Configure the Remote Endpoint settings:
Field
Value
Addresses to assign to connected endpoints
10.10.2.1-10.10.2.200
Subnet for connected endpoints
255.255.255.255
Security posture gateway matching
Disable
EMS SN verification
Disable
Save password
Enable
Auto Connect
Disable
Always up (keep alive)
Disable
-
Click Next.
-
Configure the Local FortiGate settings:
Field
Value
Incoming interface that binds to tunnel
wan1(port1)
Create and add interface to zone
Disable
Local interface
lan(port2)
Local Address
local_network
Click + to create a new address object with Type set to Subnet and IP/Netmask set to 10.10.111.0/24, if not already configured.
-
Click Next.
-
Review the configuration and click Submit.
To configure dialup IPsec VPN using IKE version 2 and TCP as transport using CLI:
-
Configure a LDAP server on FortiGate:
config user ldap edit "LDAP-Server" set server "203.0.113.1" set cnid "sAMAccountName" set dn "dc=financial,dc=local" set type regular set username "financial\\administrator" set password ***** set port 389 next end -
Configure a user group that uses the LDAP server along with group matching (
group-name):config user group edit "LDAP-Group" set member "LDAP-Server" config match edit 1 set server-name "LDAP-Server" set group-name "CN=Domain Users,CN=Users,DC=financial,DC=local" next end next end -
Configure the internal interface:
config system interface edit "lan" set vdom "root" set ip 10.10.111.1 255.255.255.0 next end config firewall address edit "local_subnet_1" set subnet 10.10.111.0 255.255.255.0 next end config firewall addrgrp edit "local_network" set member "local_subnet_1" next end -
Configure the WAN interface.
The WAN interface is the interface connected to the ISP. It can be configured in static mode (as shown here), DHCP, or PPPoE mode. It is recommended to configure it with a static IP address to ensure that the IPsec VPN configuration on the FortiClient stays unchanged if the WAN IP changes on the FortiGate. The IPsec tunnel is established over the WAN interface.
config system interface edit "wan1" set vdom "root" set ip 172.20.120.123 255.255.255.0 next end -
Configure the client address pool.
You must create a firewall address to assign an IP address to a client from the address pool.
config firewall address edit "client_range" set type iprange set start-ip 10.10.2.1 set end-ip 10.10.2.200 next end -
Configure the IPsec phase 1 interface:
config vpn ipsec phase1-interface edit "dialup_vpn" set type dynamic set interface "wan1" set ike-version 2 set peertype any set net-device disable set mode-cfg enable set proposal aes128-sha256 aes256-sha256 aes128gcm-prfsha256 aes256gcm-prfsha384 chacha20poly1305-prfsha256 set dhgrp 20 21 set eap enable set eap-identity send-request set authusrgrp "LDAP-Group" set transport tcp set assign-ip-from name set ipv4-name "client range" set dns-mode auto set ipv4-split-include "local_network" set save-password enable set psksecret ****** next endTo use UDP as transport method:
config vpn ipsec phase1-interface edit "dialup_vpn" set transport udp next endEnsure that UDP is also configured as desired transport when configuring FortiClient EMS.
To use UDP as transport method and TCP as fallback if UDP is blocked:
config vpn ipsec phase1-interface edit "dialup_vpn" set transport udp-fallback-tcp next endEnsure that Auto mode is also configured as desired transport when configuring FortiClient EMS.
-
Configure the IPsec phase 2 interface:
config vpn ipsec phase2-interface edit "dialup_vpn" set phase1name "dialup_vpn" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 next end -
Configure a firewall policy to allow client traffic flow over the IPsec VPN tunnel to the FortiGate’s LAN interface:
config firewall policy edit 1 set name "inbound" set srcintf "for_client" set dstintf "lan" set srcaddr "client_range" set dstaddr "local_network" set action accept set schedule "always" set service "ALL" next end
|
|
One or more user groups for user authentication can be configured under a single IPsec VPN tunnel. See Using single or multiple user groups for user authentication for details. |
To configure TCP port for dialup IPsec VPN when IKE version 2 is used with TCP as transport:
config system settings
set ike-tcp-port 443
end
|
Command |
Description |
|---|---|
|
|
Set the TCP port for IKE/IPsec traffic (1 - 65535, default = 443). |
|
|
When using TCP port 443 for IKE/IPsec traffic, GUI access can be affected for interfaces that are bound to an IPsec tunnel when the GUI admin port is also using port 443. To ensure continued functionality, change either the IKE/IPsec port or the administrative access port. To change the administrative access port:config system global
set admin-sport <port>
end
For port conflicts with ZTNA and SSL VPN, ZTNA and SSL VPN will take precedence. To avoid any port conflicts with other services, review the FortiOS Ports guide for other incoming ports used on the FortiGate. |
To configure the Remote Access profile to use EAP-TTLS with IKEv2 on FortiClient EMS:
-
On FortiClient EMS, navigate to Endpoint Profiles > Remote Access and click Edit on the Default endpoint profile.
-
Under VPN Tunnels, click Add Tunnel.
-
Set VPN type as Manual.
-
Click Next.
-
Under Basic Settings, enter the following:
Field
Value
Name
IPsec-IKEv2
Remote Gateway
172.20.120.123
Authentication Method
Pre-shared Key
Pre-Shared Key
Enter pre-shared key that was configured on FortiGate’s dialup VPN configuration.
Prompt for Username
Enabled
-
Click VPN Settings, enter the following:
Field
Value
IKE
Version 2
Address Assignment
Mode Config
Encapsulation
IPsec over TCP
(Optional) To use UDP encapsulation, use IKE UDP Port and use the required UDP port. Ensure that FortiGate is also configured to use UDP as transport.
(Optional) To use Auto mode, use Auto and set appropriate IKE TCP Port and IKE UDP Port. Ensure that FortiGate is also configured to use Auto mode as transport.
IKE TCP Port
443
-
Click Phase 1, enter the following details:
Field
Value
IKE Proposal
Encryption, Authentication
AES128, SHA256
Encryption, Authentication
AES256, SHA256
DH Groups
20, 21
Key Life
86400
Dead Peer Detection
Enable
NAT Traversal
Enable
-
Click Phase 2, enter the following details:
Field
Value
IKE Proposal
Encryption, Authentication
AES128, SHA256
Encryption, Authentication
AES256, SHA256
DH Groups
20
Key Life
43200
Enable Replay Detection
Enable
Enable Perfect Forward Secrecy (PFS)
Enable
-
Click Save to save the VPN Tunnel configuration.
-
Click Save to save Remote Access endpoint profile.
-
Select the same endpoint profile in the Endpoint Profiles > Remote Access tab and click Edit.
-
Select the XML tab to view XML configuration for the Remote Access profile.
-
Click Edit.
-
Edit the XML configuration to include the following:
<forticlient_configuration> <vpn> <ipsecvpn> <connections> <connection> <name>IKEV2-PSK - EAP_TTLS</name> <ike_settings> <authentication_method>Preshared Key</authentication_method> <eap_method>2</eap_method> </ike_settings> </connection> </connections> </ipsecvpn> </vpn> </forticlient_configuration> -
Click Save.
-
On FortiClient endpoint that received the configuration, in the Remote Access tab, connect to the applicable IPsec VPN tunnel using LDAP credentials.
To verify VPN tunnel status using FortiGate GUI:
-
On the FortiGate, go to Dashboard > Network and expand the IPsec widget.
-
Find the new tunnel, dialup_vpn_0 in this example, and check the statuses of the Phase 1 and Phase 2 selectors.

Successfully established dialup IPsec VPN tunnels are displayed using a parent name followed by an index, creating a structured and organized association with the parent tunnel. For example, the parent name for_client results in tunnel names such as for_client_0, for_client_1, and so on.
-
Hover the cursor over the tunnel name to see additional details.
To verify VPN tunnel status using FortiGate CLI:
-
Verify the IPsec Phase 1 tunnel status on the FortiGate:
# diagnose vpn ike gateway list name dialup_vpn_0 vd: root/0 name: dialup_vpn_0 version: 2 interface: wan1 3 addr: 172.20.120.123:443 -> 172.20.120.254:64007 tun_id: 10.10.2.1/::10.0.0.5 remote_location: 0.0.0.0 network-id: 0 transport: TCP created: 9s ago eap-user: johnlocus 2FA: no peer-id: 172.20.120.254 peer-id-auth: no assigned IPv4 address: 10.10.2.1/255.255.255.255 nat: me peer pending-queue: 0 PPK: no IKE SA: created 1/1 established 1/1 time 230/230/230 ms IPsec SA: created 1/1 established 1/1 time 0/0/0 ms id/spi: 3 b5472a576bc86fea/7ecec65178be8b3b direction: responder status: established 9-9s ago = 230ms proposal: aes128-sha256 child: no SK_ei: 62a33d927768ab2a-a442c4ed38ce0e40 SK_er: 224fa89374f4acbd-b14a17f3bc4991eb SK_ai: 6d17a5c8e686c9be-b1348327cc844262-86fb3cee982580bb-b554ab3dcd0d84bf SK_ar: b152e2366a159f9f-f371e77f020910d4-f166fd50d0ec2a48-7ea85d1b9f80bfb4 PPK: no message-id sent/recv: 0/13 QKD: no PQC-KEM (IKE): no PQC-KEM (all IPsec): no lifetime/rekey: 86400/86120 DPD sent/recv: 00000000/00000000 peer-id: 172.20.120.254
Note that FortiGate acts as the responder, establishes the IPsec tunnel with remote FortiClient user with IP 172.20.120.254 over TCP port 443 on its wan1 interface, and dynamically assigns a VPN IP of 10.10.2.1 to FortiClient endpoint. The authenticated username is also displayed in
eap-userfield. -
Verify the IPsec Phase 2 tunnel status on the FortiGate:
# diagnose vpn tunnel list name dialup_vpn_0 list ipsec tunnel by names in vd 0 ------------------------------------------------------ name=dialup_vpn_0 ver=2 serial=5 172.20.120.123:443->172.20.120.254:64007 nexthop=::f07b:1205:c9:ffff:0:0 tun_id=172.20.120.254 tun_id6=::10.0.0.5 status=up dst_mtu=0 weight=1 bound_if=3 real_if=0 lgwy=static/1 tun=intf mode=dial_inst/3 encap=none/74664 options[123a8]=npu rgwy-chg rport-chg frag-rfc run_state=0 role=primary accept_traffic=1 overlay_id=0 parent=dialup_vpn index=0 proxyid_num=1 child_num=0 refcnt=7 ilast=297 olast=42968325 ad=/0 stat: rxp=40 txp=0 rxb=2397 txb=0 dpd: mode=on-demand on=1 status=ok idle=20000ms retry=3 count=0 seqno=0 natt: mode=none draft=0 interval=0 remote_port=0 proxyid=dialup_vpn proto=0 sa=1 ref=2 serial=1 add-route src: 0:0.0.0.0-255.255.255.255:0 dst: 0:10.10.2.1-10.10.2.1:0 SA: ref=3 options=20682 type=00 soft=0 mtu=1280 expire=42891/0B replaywin=2048 seqno=1 esn=0 replaywin_lastseq=00000028 qat=0 rekey=0 hash_search_len=1 life: type=01 bytes=0/0 timeout=43190/43200 dec: spi=cec9531d esp=aes key=16 2d5aad4d9e1485cb6581a22dbb0adc83 ah=sha256 key=32 0ae8d0f3756defc0388d0637481f17da996aa21c146a0cfdf98ff791eae19fd8 enc: spi=594455d1 esp=aes key=16 dc407cae5fb744f6cb6bf12fd4354aa3 ah=sha256 key=32 61dcb6744b2bd68a9b27b2249eebac9e9739c07081bff8e906d595399a51189a dec:pkts/bytes=40/2397, enc:pkts/bytes=0/0 npu_flag=00 npu_rgwy=0.0.0.0 npu_lgwy=0.0.0.0 npu_selid=0 dec_npuid=0 enc_npuid=0 dec_engid=-1 enc_engid=-1 dec_saidx=-1 enc_saidx=-1Note the decryption, encryption, and authentication keys negotiated in Phase 2 to protect subnets under the
srcanddstfields. FortiOS also automatically adds the dynamically assigned VPN IP of 10.10.2.1 to its traffic selectors for dialup tunnel dialup_vpn_0.
To verify traffic through the IPsec tunnel:
-
On the remote FortiClient user with IP address 172.20.120.254, initiate ICMP traffic to a machine in the 10.10.111.0/24 network and verify that traffic goes through:
# ping 10.10.111.3 PING 10.10.111.3 (10.10.111.3) 56(84) bytes of data. 64 bytes from 10.10.111.3: icmp_seq=1 ttl=62 time=9.84 ms 64 bytes from 10.10.111.3: icmp_seq=2 ttl=62 time=0.808 ms
-
On FortiGate, run a sniffer trace for ICMP packets destined to 10.10.111.3:
# diagnose sniffer packet any 'host 10.10.111.3’ 4 0 l Using Original Sniffing Mode interfaces=[any] filters=[host 10.10.111.3] 2024-11-05 12:06:05.509711 dialup_vpn_0 in 10.10.2.1 -> 10.10.111.3: icmp: echo request 2024-11-05 12:06:05.509791 lan out 10.10.2.1 -> 10.10.111.3: icmp: echo request 2024-11-05 12:06:05.518809 lan in 10.10.111.3 -> 10.10.2.1: icmp: echo reply 2024-11-05 12:06:05.518899 dialup_vpn_0 out 10.10.111.3 -> 10.10.2.1: icmp: echo reply
The ICMP request packets are received on dialup_vpn_0 tunnel interface and routed to the LAN interface. ICMP reply packets are received on the LAN interface and routed back out on dialup_vpn_0 tunnel interface.
For more information, see Performing a sniffer trace or packet capture.
-
Optionally, run real time IKE debug using appropriate filters for troubleshooting if the IPsec tunnel does not come up:
# diagnose vpn ike log filter rem-addr4 172.20.120.254 # diagnose debug application ike -1 # diagnose debug enable
For more information, see VPN IPsec troubleshooting.
To verify LDAP authentication using EAP-TTLS on FortiClient:
-
Ensure that the logging level is set to Debug on FortiClient.
-
After the VPN tunnel establishes on FortiClient, go to the folder located under C:\%ProgramFiles%\Fortinet\FortiClient\logs\trace\ and open the file FortiIKE_1.log. The following shows expected log output for this feature:
[7868:11132] [FortiIKE 524 info] IPsec daemon start ipsec.exe -s FC_{73EFB30F-1CAD-4a7a-AE2E-150282B6CE25}_000002 -i 2 -g 172.20.120.254 IPsec-IKEv2 [7868:11132] [FortiIKE 419 debug] EAP-TTLS method loaded [7868:11132] [FortiIKE 427 debug] EAP-GTC method loaded [7868:11132] [FortiIKE 4939 debug] 0:IPsec-IKEv2:0: initiator received EAP msg [7868:11132] [FortiIKE 400 debug] EAP: Initialize selected EAP method: vendor 0 method 21 (TTLS) [7868:11132] [FortiIKE 145 debug] EAP-TTLS: Phase2 type: PAP [7868:11132] [FortiIKE 4779 debug] 0:IPsec-IKEv2:0: authentication succeeded

