SAML
SAML authentication allows a user to complete authentication and authorization between a Service Provider (SP) and an Identity Provider (IdP). It enables Single Sign-On (SSO) by allowing users who have been authenticated against an IdP to be allowed access to different applications (the SPs providing a service such as a web application).
A FortiGate (SP) can provide a web service, such as an SSL VPN connection, that requires users to be authenticated through SAML. The user identities for the company can be stored remotely in an IdP, such as Microsoft Entra ID. Other applications might also require authentication from the same IdP, so after a user is authenticated once, the same SAML assertion carrying user and group information can be used to authorize the user access to the FortiGate SSL VPN, as well as other applications.
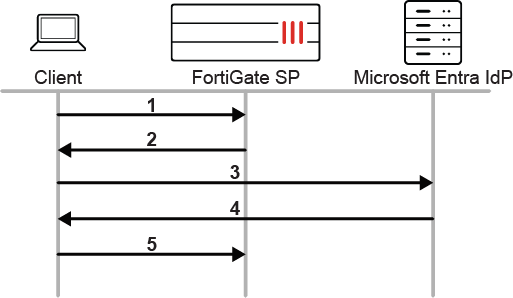
To illustrate the communication between the user or browser, SP, and IdP:
-
The user initiates an SSL VPN connection to the FortiGate.
-
The FortiGate SP redirects the user to the SAML IdP.
-
The user connects to the Microsoft log in page for the SAML authentication request.
-
The SAML IdP authenticates the user and sends the SAML assertion containing the user and group within the SAML response.
-
The browser forwards the SAML response to the FortiGate SP. If the user and group are allowed by the FortiGate, the user is allowed to access the application, in this case, connecting to SSL VPN.
Usage
There are many practical uses and applications for SAML authentication on the FortiGate. For example:
-
Authentication for SSL VPN
-
Firewall authentication for firewall policy access
-
Authentication for ZTNA
-
Authentication for Explicit Proxy
-
Authentication for Administrative Access
Identity providers
FortiGate’s SAML SSO configurations can be integrated with any common Identity providers, such as Microsoft Entra ID, Okta, Google Workspace, Onelogin, and others. You can also use FortiAuthenticator as an identity provider with local or remote user integration, or as an IdP Proxy to other IdP providers.
For more information on using FortiAuthenticator, see the FortiAuthenticator Administration Guide and FortiAuthenticator Examples Guide.
Response and assertion signing
For security purposes, FortiGate can perform signature verification for both the SAML response message and the SAML assertion carried inside the SAML response. This means that the SAML response must have a valid signature, and the SAML assertion must also have a valid signature. If the Identity Provider (IdP) provides an invalid signature, or fails to sign one of these, the FortiGate will reject the SAML response.
This check is disabled by default but can be enabled using the following configuration:
config user saml
edit <name>
set require-signed-resp-and-asrt {enable | disable}
next
end
|
Option |
Description |
|---|---|
|
enable |
Both response and assertion must be signed and valid. |
|
disable |
At least one of response or assertion must be signed and valid (default). |
When disabled, the FortiGate performs a signature check using the following logic:
-
If the SAML response is missing signature, each SAML assertion must have a valid signature.
-
If the SAML response signature is invalid, check fails.
-
If the SAML response signature is valid, check the following:
-
If the SAML assertion signature is missing, check passes.
-
If the SAML assertion signature is invalid, check fails.
-
If the SAML assertion signature is valid, check passes.
-
Example
Some SAML IdPs defaults to signing the SAML assertions only. To increase security, you can enable signing both the SAML response and assertion to work natively with the FortiGate.
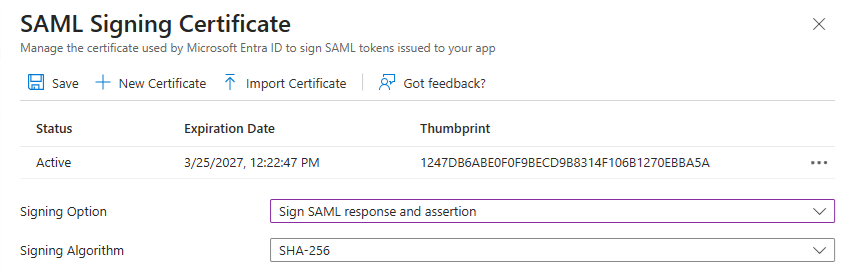
To enable Sign SAML response and assertion in Microsoft Entra ID:
-
Go to the Microsoft Entra admin center.
-
Navigate to Enterprise Applications.
-
Select your application.
-
Go to Single sign-on > SAML.
-
Scroll to SAML Signing Certificate and click Edit (the pencil icon).
-
For Signing Option, choose Sign SAML response and assertion.
-
Click Save.
For details, see Certificate signing options in a SAML token - Microsoft Entra ID | Microsoft Learn.
For other SAML IdP vendors, check the setting to enable signing both the SAML response and assertion.
If the SAML IdP vendor does not have a setting to sign both the SAML response and assertion, or fails to sign both even when configured, you can considering loosening up the requirement on the FortiGate per Response and assertion signing.

