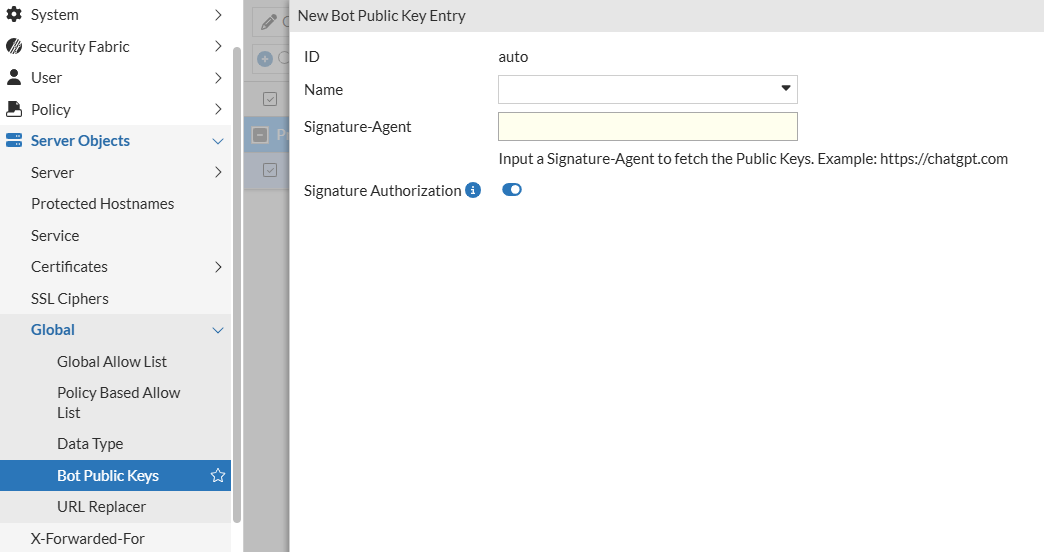
server-policy bot-public-keys
You can now use cryptographic signature verification to identify legitimate search engines and AI crawlers. These updates shift bot identification from easily forged attributes to a robust security model based on industry standards and strict behavioral enforcement.
Syntax
config server-policy bot-public-keys
edit 1
set name "<entry_name>"
set signature-agent "<url>"
set signature-authorization {enable|disable}
next
end
| Variable | Description | Default |
|---|---|---|
| name "<entry_name>" | Enter a name for the signature. | No default |
| signature-agent "<url>" | Enter the signature agent URL to fetch the public keys. | No default |
| signature-authorization {enable|disable} | Enable signature authorization so that cryptographic signature verification can be used to identify legitimate search engines and AI crawlers. | enable
|
Cryptographic Signature Verification
FortiWeb now supports the RFC 9421 HTTP Message Signatures standard to accurately identify bots from providers such as OpenAI. By using public keys fetched directly from the bot service, FortiWeb verifies the authenticity of incoming requests. This method ensures that even if a bot's IP or User-Agent is spoofed, the request is only recognized as a Known Good Bot if it carries a valid cryptographic signature. Requests that fail this verification are treated as unverified and subjected to standard security processing.
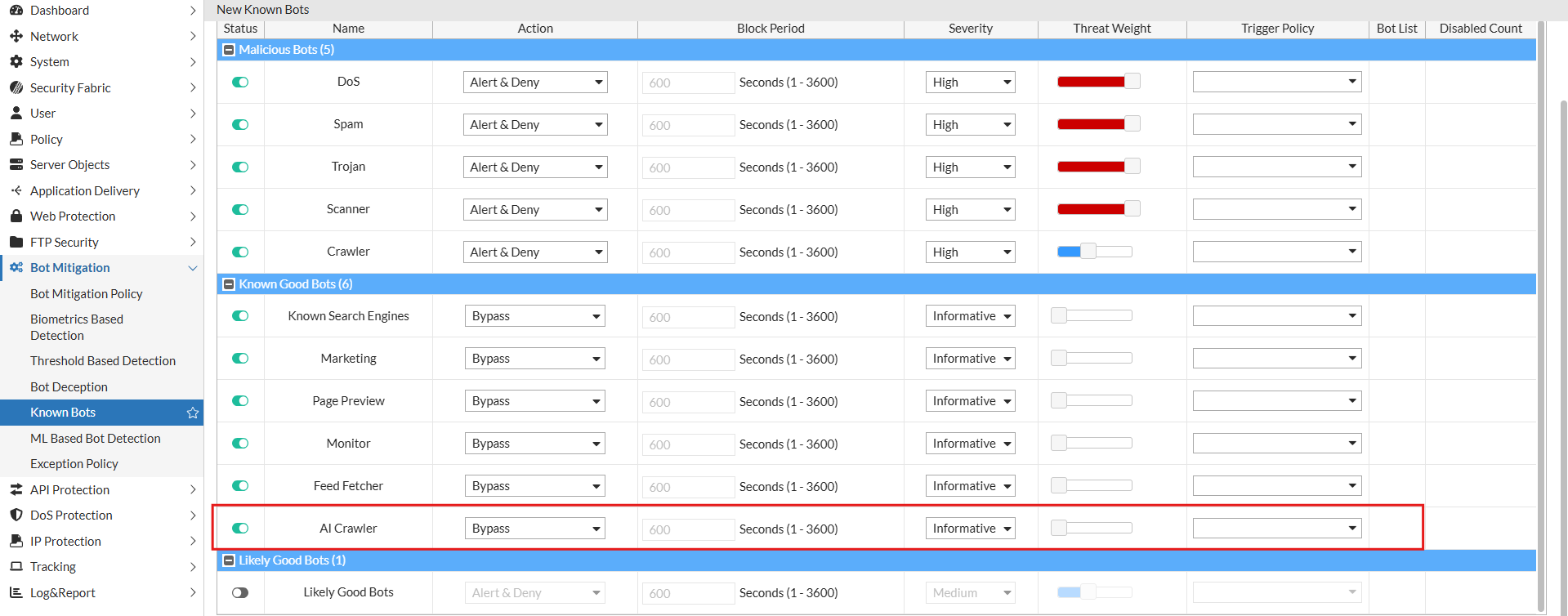
AI Crawler Classification
A dedicated AI Crawler category has been introduced to the Known Bots module. This allows you to define specific security actions for AI-driven agents, such as GPTBot or ClaudeBot, separate from traditional search engines or marketing tools.