Signature Detection
|
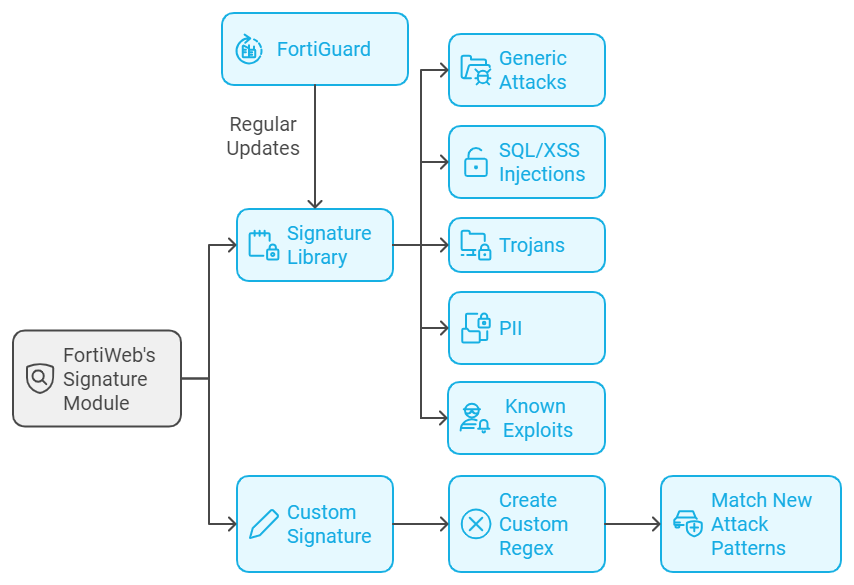
Signature library
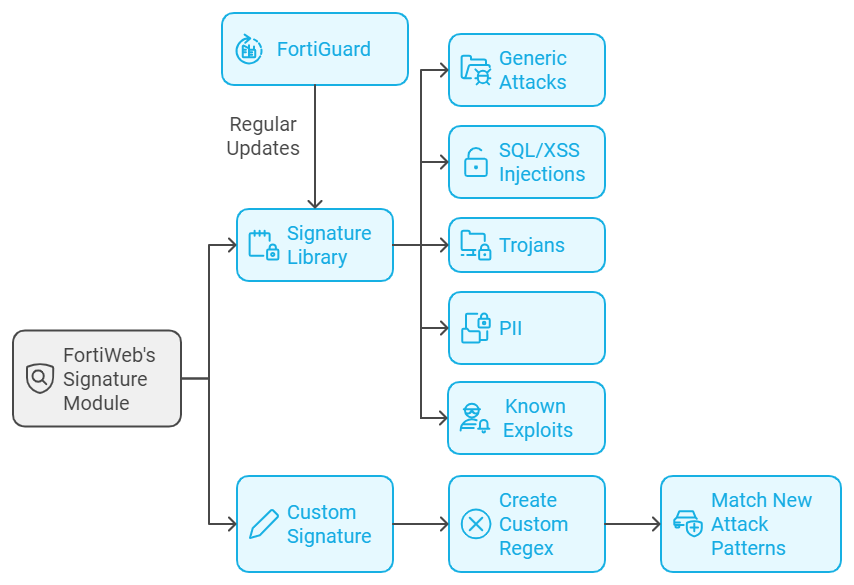
FortiWeb's Signature module uses a signature library to block attacks that match specific characteristics, such as malicious code, SQL injection, cross-site scripting (XSS), path traversal, etc. The signature library is regularly updated to continuously improve known attack signatures.
Custom Signature
FortiWeb also provides Custom Signature module which allows you to create custom regular expressions to match the patterns of these new attacks, enabling you to block any similar attacks moving forward.
|
Machine Learning based Anomaly Detection
|
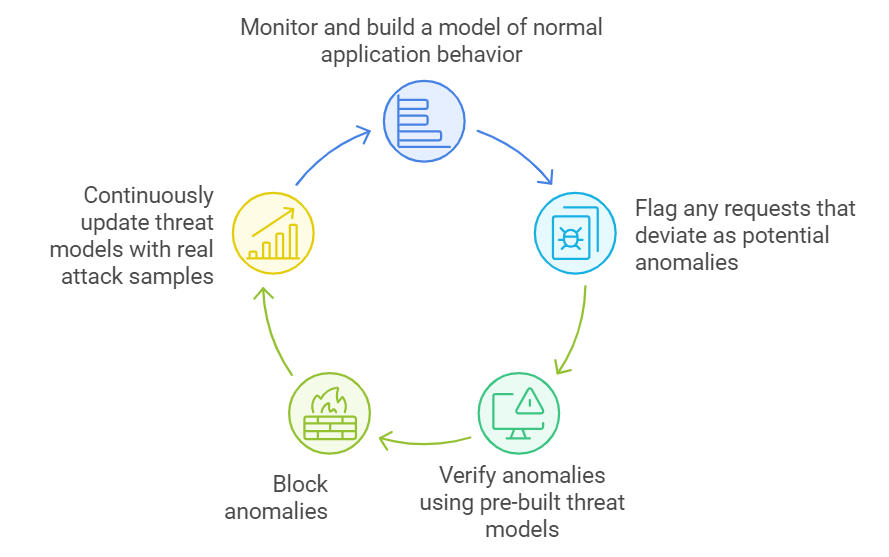
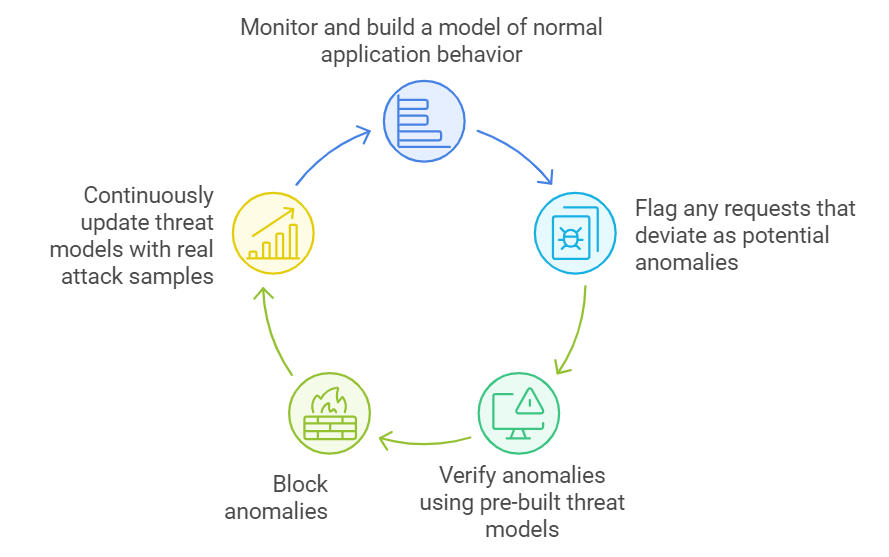
FortiWeb's Machine Learning Anomaly Detection uses a two-layer approach to effectively identify and block web application attacks.
-
The first layer employs a Hidden Markov Model (HMM) to monitor and build a model of normal application behavior, flagging any requests that deviate as potential anomalies.
-
The second layer then verifies these anomalies using pre-built, continuously updated threat models trained on thousands of real attack samples, such as SQL Injection and Cross-site Scripting (XSS).
This dual-layer system ensures accurate detection of malicious activity while minimizing false positives.
|
Data Loss Prevention (DLP)
|
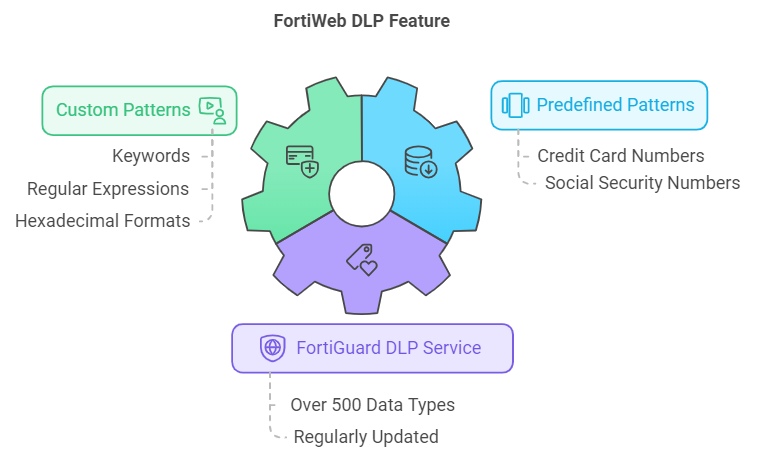
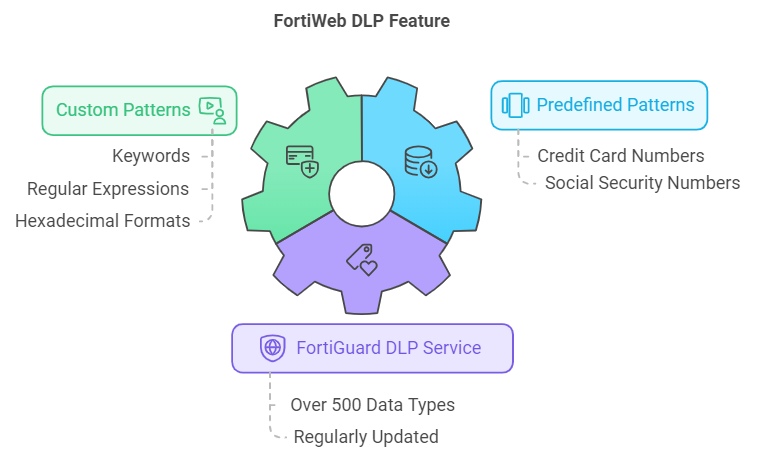
FortiWeb's Data Loss Prevention (DLP) feature is designed to protect against the leakage of sensitive data from web applications.
-
It integrates with the FortiGuard DLP service which includes over 500 predefined, regularly updated data patterns.
-
It has predefined patterns that helps prevent the leakage of sensitive data such as credit card numbers and Social Security Numbers (SSNs).
-
It also supports custom patterns through keywords, regular expressions, or hexadecimal formats.
|
Syntax-based SQL/XSS Injection Detection
|
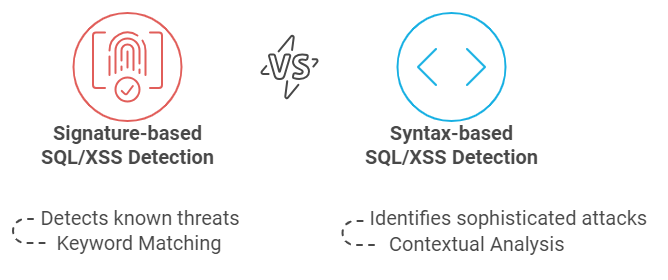
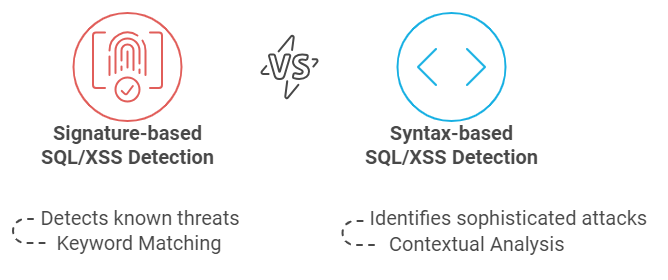
FortiWeb's Syntax-based SQL/XSS Injection Detection analyzes the structure and syntax of input data to detect malicious patterns.
Instead of just looking for specific keywords or characters, FortiWeb evaluates the context and how the input fits into typical SQL/XSS queries. This helps in identifying more sophisticated attacks that might bypass traditional signature-based detection.
|
Input Validation
|
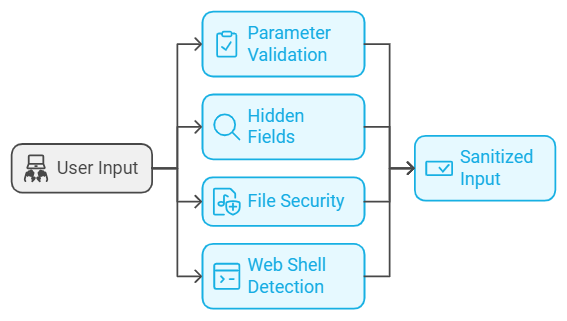
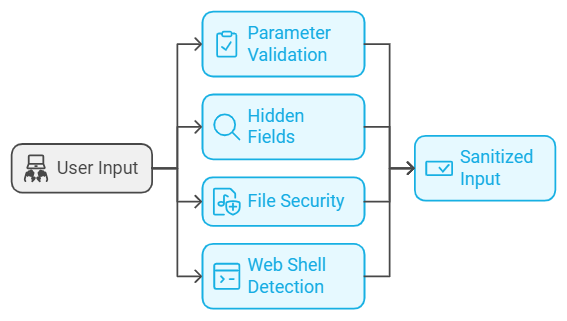
FortiWeb's Input Validation features are designed to protect web applications from various injection attacks and other threats that exploit user inputs. These features ensure that all data submitted by users, such as form fields, URL parameters, and cookies, is properly validated and sanitized before being processed by the application.
The Input Validation modules include Parameter Validation, Hidden Fields, File Security, and Web Shell Detection.
|
|
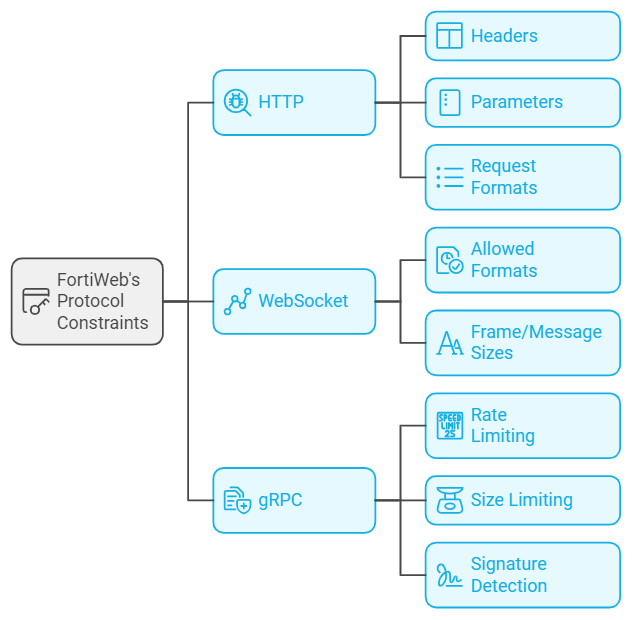
Protocol Constraints
|
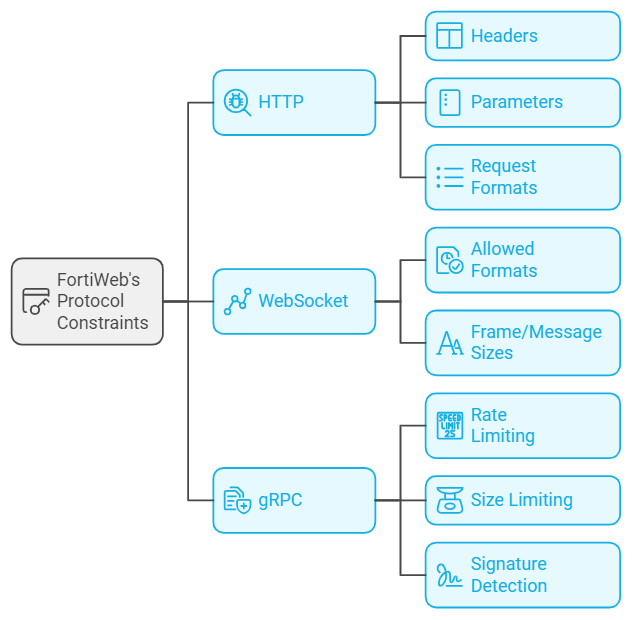
FortiWeb's Protocol Constraints are security features that enforce strict adherence to protocols like HTTP, HTTPS, WebSocket, and gRPC to prevent attacks exploiting protocol weaknesses.
-
For HTTP, FortiWeb checks elements such as headers, parameters, and request formats.
-
For WebSocket, it secures WebSocket traffic by controlling allowed formats and frame/message sizes.
-
For gRPC, it applies controls like rate limiting, size limiting, and signature detection.
|
|
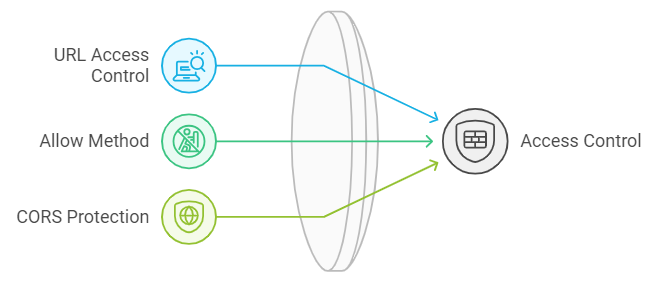
Access Control
|
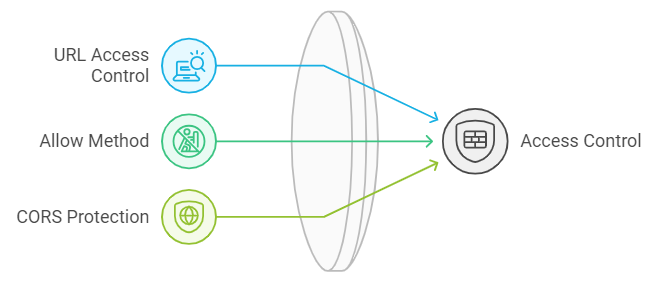
FortiWeb's Access Control features include URL Access Control, Allow Method, and CORS (Cross-Origin Resource Sharing) Protection.
These capabilities provide granular control over how web applications handle requests based on the URL, HTTP methods, and cross-origin requests, ensuring that only authorized and legitimate interactions are permitted.
|
|
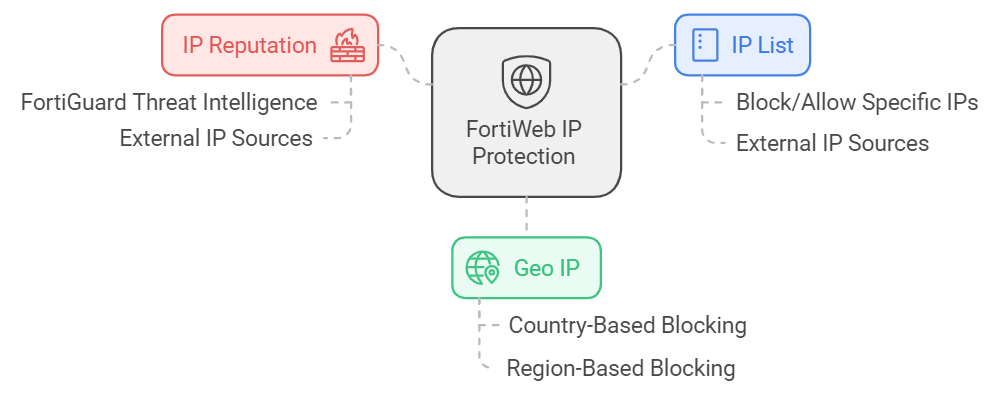
IP Protection
|
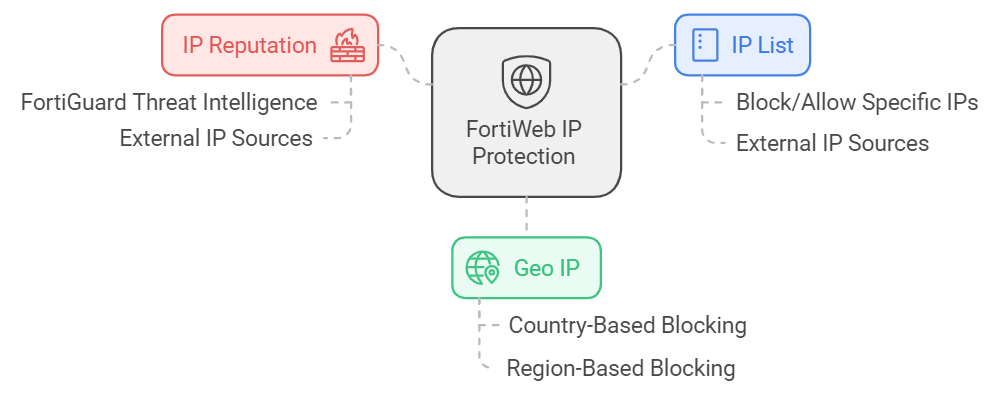
FortiWeb’s IP Protection features include IP List, Geo IP, and IP reputation.
It integrates with FortiGuard’s real-time threat intelligence to automatically block IPs associated with malicious activities and allows for the use of external IP sources to enhance protection. This multi-layered approach ensures that only trusted, legitimate IP addresses can access your web applications, effectively mitigating risks from unauthorized or harmful traffic.
|
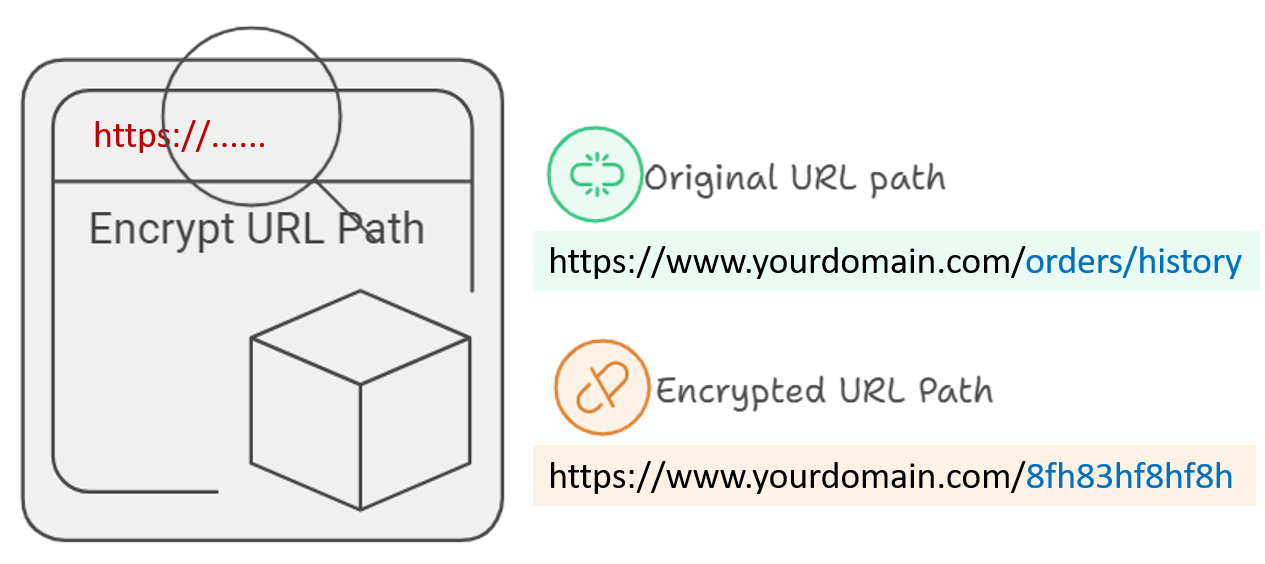
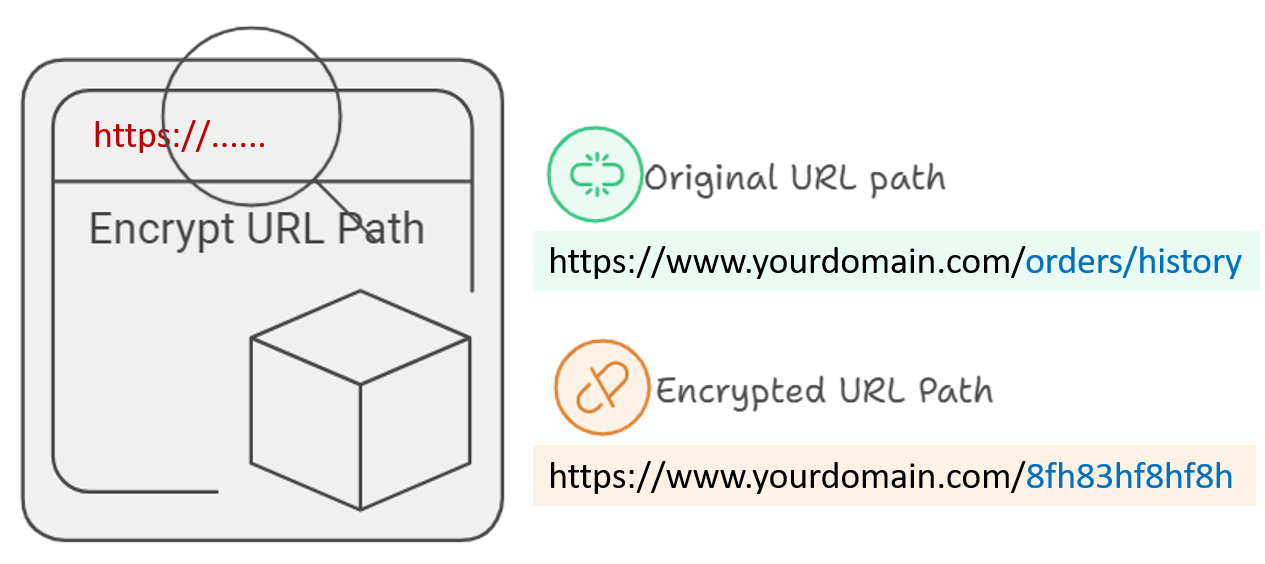
URL Encryption
|
FortiWeb’s URL Encryption feature enhances web application security by encrypting URLs to obscure their actual paths and make them difficult for attackers to guess.
For example, the URL "https://www.secureshop.com/orders/history" might be encrypted to "https://www.secureshop.com/8fh83hf8hf8h", masking the original structure and content of the URL. This prevents attackers from easily identifying and accessing sensitive pages through forceful browsing or URL manipulation.
|
|
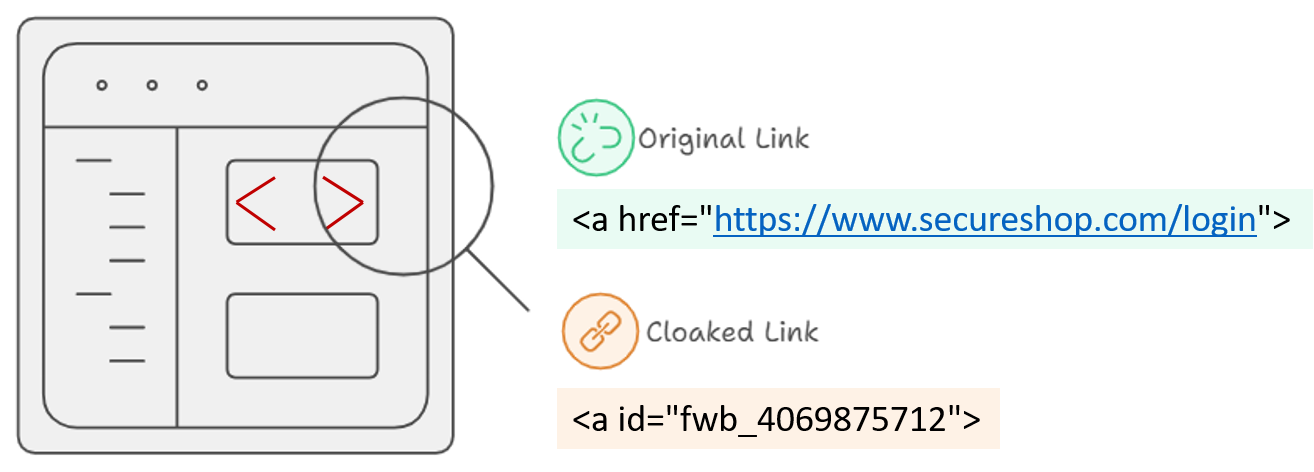
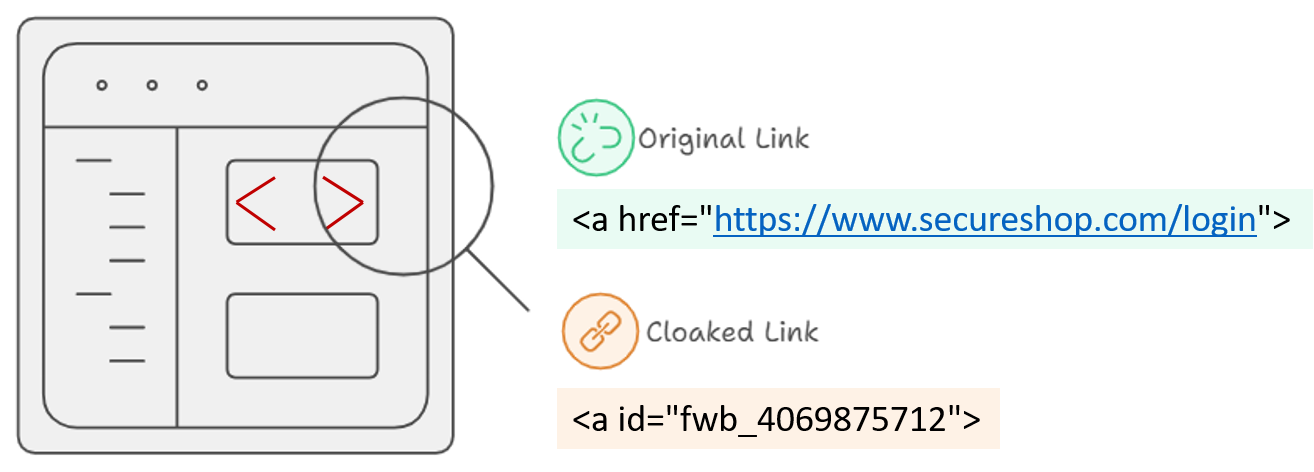
Link Cloaking
|
FortiWeb’s Link Cloaking feature protects sensitive or critical URLs from being indexed by web crawlers while maintaining a seamless experience for users. This is achieved by cloaking the links within the HTML content so that they are not easily readable or accessible to automated systems like search engine bots.
|
|
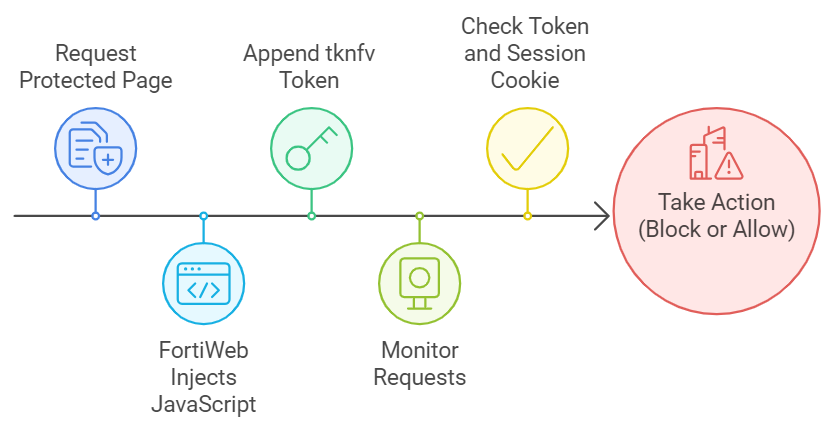
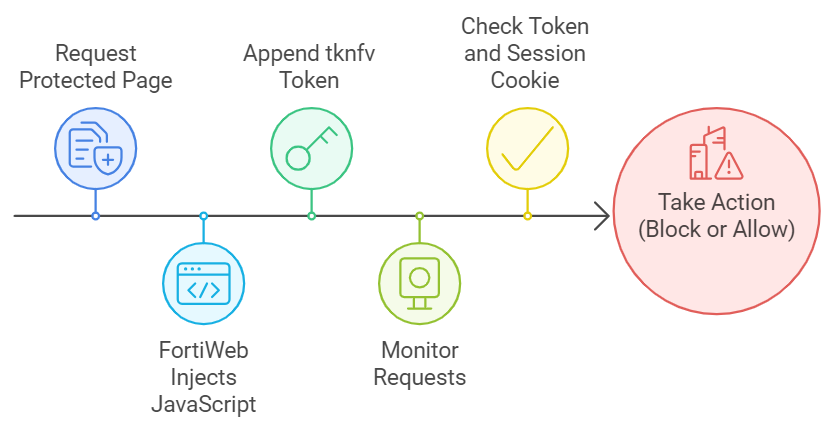
Cross-Site Request Forgery (CSRF) Protection
|
FortiWeb’s Cross-Site Request Forgery (CSRF) Protection is designed to safeguard web applications from CSRF attacks, where an attacker tricks a user into performing actions on a web application without their consent.
When a protected page is requested, FortiWeb injects JavaScript to append the tknfv token to HTML links, forms, and AJAX requests. The token is tied to the session cookie managed by Client Management. FortiWeb monitors requests to the URLs in the list, and if a request lacks the token or the token doesn’t match the session cookie, it takes the specified action, such as blocking the request. Proper configuration ensures effective protection without false positives.
|