About the connector
The FortiGate next-generation firewall platform (hardware and virtualized) is the heart of the Fortinet Security Fabric, which delivers true end-to-end network security. FortiGate firewalls are purpose-built with security processors to enable threat protection and performance for SSL-encrypted traffic. By providing granular visibility of applications, users, and IOT devices, these appliances are designed to identify issues quickly and intuitively.
This document provides information about the Fortinet FortiGate connector, which facilitates automated interactions, with a Fortinet FortiGate server using FortiSOAR™ playbooks. Add the Fortinet FortiGate connector as a step in FortiSOAR™ playbooks and perform automated operations, such as blocking or unblocking IP addresses, URLs, or applications, or retrieving a list of blocked IP addresses, URLs, or applications from the Fortinet FortiGate server.
Version information
Connector Version: 4.0.1
FortiSOAR™ Version Tested on: 6.4.4-3164
Fortinet FortiGate Version Tested on: FortiGate VM64 v6.0.7 build0302 (GA)
Authored By: Fortinet
Certified: Yes
Release Notes for version 4.0.1
Following enhancements have been made to the Fortinet FortiGate connector in version 4.0.1:
- Added support for blocking or unblocking the source IP address group for policy-based "Block IP Address" or "Unblock IP Address" operations; in the earlier versions, only destination IP address group could be blocked or unblocked.
- Updated the output schema for the "Get Blocked IP Addresses" operation.
Installing the connector
From FortiSOAR™ 5.0.0 onwards, use the Connector Store to install the connector. For the detailed procedure to install a connector, click here.
You can also use the yum command to install connectors. Connectors provided by FortiSOAR™ are delivered using a FortiSOAR™ repository. Therefore, you must set up your FortiSOAR™ repository and run the yum command as a root user to install connectors:
yum install cyops-connector-fortigate-firewall
Prerequisites to configuring the connector
- You must have the IP address or Hostname of the Fortinet FortiGate server to which you will connect and perform the automated operations and the API Key to access that server.
- To access the FortiSOAR™ UI, ensure that port 443 is open through the firewall for the FortiSOAR™ instance.
- To block or unblock IP addresses, URLs, or applications, you need to add the necessary configuration to Fortinet FortiGate. See the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate section".
- Ensure the user has the permissions required for the actions you wish to perform in Fortinet FortiGate.
- To execute Fortinet FortiGate connector actions, the following minimal profile permissions are required:
- User and Device: Read and Write permissions.
- Firewall: Read and Write permissions for Policy and Address.
- Security Profile: Read and Write permissions for Web Filter and Application Control.
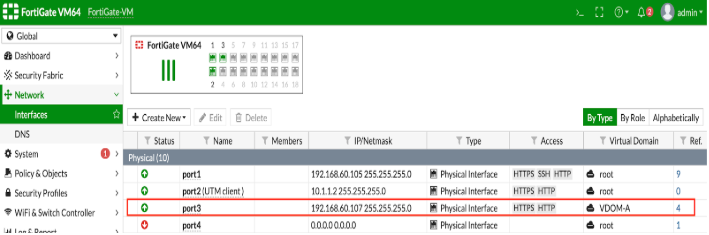
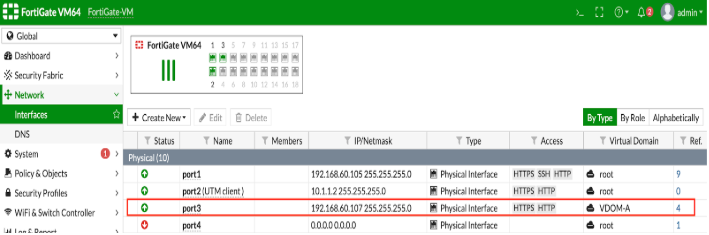
- VDOM is configured using a network interface in FortiGate which have their own IP address with different subnets (separate from "global' or "root" VDOM). When users select "VDOM" in the connector Configuration, users should specify the VDOM interface IP in the Hostname section, otherwise, an "Unauthorized Error" gets thrown. See the following screenshots for VDOM specific connector configuration:

Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate
-
Log on to the Fortinet FortiGate server with the necessary credentials.
-
To block or unblock an IP address, you must create a policy for IP addresses on the Fortinet FortiGate server. Following steps define the process of adding a policy:
- In
Policy & Objects, click IPv4 Policy to create a policy for IPv4 with the following conditions.
Source = Blocked_IPs
Destination = Blocked_IPs
Schedule = always
Service = ALL
Action = DENY
Note: You can create an IPv6 policy in a similar manner.
For more information on address group exclusions, see the FortiOS 6.2.3 Cookbook.
- In
Policy & Objects, click Addresses to create an address group with the following conditions.
Group Name = Blocked_IPs
Member = none
Show in address list = enable
For more information on creating address groups and address group exclusions, see the FortiOS 6.2.3 Cookbook.
- In
Policy & Objects, click IPv4 Policy and enter the IPv4 policy name as the Action parameter. For our example, we have named this as FortiSOAR_Blocked_Policy. When you are configuring your Fortinet FortiGate connector in FortiSOAR™, you must use the policy name that you have specified in this step as your IPv4 Block Policy action parameter.
For more information on IPv4 Policy, see IPv4 Policy in the FortiOS documentation.
- To block or unblock a URL, you must create a profile for blocking or unblocking static URLs on the Fortinet FortiGate server. For information on creating web filters, see Web Filter in the FortiOS 6.2.3 Cookbook.
Following steps define the process of adding a policy:
- In
Security Profiles, click Web Filter to create a new profile for blocking or unblocking static URLs or use the default profile.
Note: Ensure that the "URL Filter " is enabled.
- Enter the Web Filter Profile name on the configuration page. For our example, we have named this as URL Block Policy. When you are configuring your Fortinet FortiGate connector in FortiSOAR™, you must use the Web Filter Profile name that you have specified in this step as your
Web Filter Profile Name configuration parameter.
-
To block or unblock an application, you must create a profile for blocking or unblocking applications on the Fortinet FortiGate server. Following steps define the process of adding a policy:
-
In Security Profiles, click Application Control to create a new profile for blocking or unblocking applications or use the default profile.
-
Enter the policy name in the configuration page. For our example, we have named this as App Block Policy. When you are configuring your Fortinet FortiGate connector in FortiSOAR™, you must use the Application Control Profile name that you have specified in this step as your Application Control Profile Name configuration parameter.
For information on adding application controls, see Application Control in the FortiOS 6.2.3 Cookbook.
Configuring the connector
For the procedure to configure a connector, click here.
Configuration parameters
In FortiSOAR™, on the Connectors page, click the Fortinet FortiGate connector row (if you are in the Grid view on the Connectors page) and in the Configurations tab enter the required configuration details:
| Parameter |
Description |
| Hostname |
IP address or Hostname of the Fortinet FortiGate endpoint server to which you will connect and perform the automated operations. |
| API Key |
API Key of the Fortinet FortiGate endpoint server to which you will connect and perform the automated operations. You can get the API key from the administration settings in FortiGate.
Important: To create a REST API key from Fortinet FortiGate, see the "Create a REST API administrator" section in the Fortinet FortiGate Documentation. |
| Port |
Port number used for connecting to the Fortinet FortiGate server. Defaults to 443. |
| Web Filter Profile Name |
Name of the Web Filter Profile that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter default in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section. |
| Application Control Profile Name |
Name of the Application Control Profile that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter default in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section. |
| VDOM |
VDOMs, in the CSV or List format, to support operations related to IP addresses. |
| Verify SSL |
Specifies whether the SSL certificate for the server is to be verified or not.
By default, this option is set as True. |
Actions supported by the connector
The following automated operations can be included in playbooks, and you can also use the annotations to access operations from version 4.10.0 onwards:
| Function |
Description |
Annotation and Category |
| Get List of Policies |
Retrieves a list and details for all IPv4 policies that are configured on Fortinet FortiGate. |
get_policies
Investigation |
| Get Applications Detail |
Retrieves a list of all application names and associated details from the Fortinet FortiGate server. |
get_app_details
Investigation |
| Block URL |
Blocks URLs on Fortinet FortiGate using the Web Filter Profile Name Policy that you have specified while configuring Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section.
Note: This operation always blocks URLs on the root VDOM and ignores VDOMs provided on the configuration page. |
block_url
Containment |
| Unblock URL |
Unblocks URLs on Fortinet FortiGate using the Web Filter Profile Name that you have specified while configuring Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section.
Note: This operation always unblocks URLs on the root VDOM and ignores VDOMs provided on the configuration page. |
unblock_url
Remediation |
| Block IP Address |
Blocks IP addresses on Fortinet FortiGate using the IPv4 Block Policy that you have specified as the "action" parameter of Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section.
Note: This operation is supported on all VDOMs. |
block_ip
Containment |
| Unblock IP Address |
Unblocks IP addresses on Fortinet FortiGate using the IPv4 Block Policy that you have specified as the "action" parameter of Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section.
Note: This operation is supported on all VDOMs. |
unblock_ip
Remediation |
| Block Application |
Blocks applications on Fortinet FortiGate using the Application Control Profile Name that you have specified while configuring Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section.
Note: This operation always blocks applications on the root VDOM and ignores VDOMs provided on the configuration page. |
block_app
Containment |
| Unblock Application |
Unblocks applications on Fortinet FortiGate using the Application Control Profile Name that you have specified while configuring Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section.
Note: This operation always unblocks applications on the root VDOM and ignores VDOMs provided on the configuration page. |
unblock_app
Remediation |
| Get Blocked URLs |
Retrieves a list of URLs that are blocked on Fortinet FortiGate.
Note: This operation always blocks URLs on the root VDOM and ignores VDOMs provided on the configuration page. |
get_blocked_url
Investigation |
| Get Blocked IP Addresses |
Retrieves a list of IP Addresses that are blocked on Fortinet FortiGate.
Note: This operation is supported on all VDOMs. |
get_blocked_ip
Investigation |
| Get Blocked Applications |
Retrieves a list of application names that are blocked on Fortinet FortiGate.
Note: This operation is only supported on the root VDOM. |
get_blocked_app
Investigation |
operation: Get List of Policies
Input parameters
| Parameter |
Description |
| VDOM |
(Optional) VDOM on which you want to perform automated operations.
Notes:
- You can specify the VDOM, as a configuration parameter, or you can also specify VDOM here, as an input parameter.
- You can specify VDOM in the "CSV" or "list" format
By default, VDOM is set to root.
|
Output
The JSON output retrieves a list and details for all policies that are configured on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"result": [
{
"build": "",
"status": "",
"http_method": "",
"http_status": "",
"vdom": "",
"version": "",
"name": "",
"results": [
{
"name": "",
"profile-group": "",
"block-notification": "",
"profile-protocol-options": "",
"wanopt-detection": "",
"internet-service-custom": [],
"dstintf": [
{
"name": "",
"q_origin_key": ""
}
],
"natinbound": "",
"policyid": "",
"dnsfilter-profile": "",
"service-negate": "",
"action": "",
"webfilter-profile": "",
"ssl-ssh-profile": "",
"internet-service": "",
"ips-sensor": "",
"send-deny-packet": "",
"outbound": "",
"devices": [],
"q_origin_key": "",
"comments": "",
"poolname": [],
"fixedport": "",
"disclaimer": "",
"wanopt-profile": "",
"uuid": "",
"tcp-mss-sender": "",
"rsso": "",
"groups": [],
"srcaddr": [
{
"name": "",
"q_origin_key": ""
}
],
"srcaddr-negate": "",
"traffic-shaper-reverse": "",
"status": "",
"dstaddr-negate": "",
"url-category": [],
"label": "",
"ntlm": "",
"internet-service-id": [],
"global-label": "",
"timeout-send-rst": "",
"auth-cert": "",
"app-category": [],
"av-profile": "",
"ssl-mirror-intf": [],
"users": [],
"auth-redirect-addr": "",
"scan-botnet-connections": "",
"firewall-session-dirty": "",
"ippool": "",
"custom-log-fields": [],
"fsso-agent-for-ntlm": "",
"waf-profile": "",
"tags": [],
"service": [
{
"name": "",
"q_origin_key": ""
}
],
"tcp-session-without-syn": "",
"dlp-sensor": "",
"schedule": "",
"captive-portal-exempt": "",
"dscp-value": "",
"rtp-addr": [],
"learning-mode": "",
"wanopt-passive-opt": "",
"dscp-negate": "",
"natoutbound": "",
"diffservcode-forward": "",
"logtraffic-start": "",
"natip": "",
"wccp": "",
"per-ip-shaper": "",
"ssl-mirror": "",
"icap-profile": "",
"capture-packet": "",
"srcintf": [
{
"name": "",
"q_origin_key": ""
}
],
"spamfilter-profile": "",
"redirect-url": "",
"permit-stun-host": "",
"inbound": "",
"webcache-https": "",
"diffserv-reverse": "",
"profile-type": "",
"traffic-shaper": "",
"rtp-nat": "",
"fsso": "",
"wsso": "",
"nat": "",
"radius-mac-auth-bypass": "",
"auth-path": "",
"wanopt": "",
"diffservcode-rev": "",
"ntlm-enabled-browsers": [],
"utm-status": "",
"schedule-timeout": "",
"vpntunnel": "",
"vlan-cos-fwd": "",
"dsri": "",
"internet-service-negate": "",
"application": [],
"delay-tcp-npu-session": "",
"wanopt-peer": "",
"dstaddr": [
{
"name": "",
"q_origin_key": ""
}
],
"voip-profile": "",
"ntlm-guest": "",
"session-ttl": 0,
"identity-based-route": "",
"diffserv-forward": "",
"tcp-mss-receiver": "",
"application-list": "",
"vlan-cos-rev": "",
"webcache": "",
"match-vip": "",
"replacemsg-override-group": "",
"permit-any-host": "",
"logtraffic": "",
"dscp-match": ""
}
],
"path": "",
"serial": "",
"revision": ""
}
],
"vdom_not_exist": ""
}
operation: Get Applications Detail
Input parameters
None.
Output
The JSON output retrieves a list of all application names and associated details from the Fortinet FortiGate server.
The output contains the following populated JSON schema:
{
"path": "",
"vdom": "",
"name": "",
"http_method": "",
"http_status": "",
"results": [
{
"q_type": "",
"vendor": "",
"q_name": "",
"sub-category": "",
"popularity": "",
"q_class": "",
"protocol": "",
"id": "",
"q_origin_key": "",
"q_path": "",
"weight": "",
"q_mkey_type": "",
"parameter": "",
"q_ref": "",
"name": "",
"q_no_rename": "",
"behavior": "",
"risk": "",
"category": "",
"metadata": [
{
"id": "",
"valueid": "",
"q_origin_key": "",
"metaid": ""
}
],
"technology": "",
"q_static": ""
}
],
"build": "",
"serial": "",
"version": "",
"revision": "",
"status": ""
}
operation: Block URL
Input parameters
| Parameter |
Description |
| URL |
List of URLs that you want to block on Fortinet FortiGate. URLs must be in the list format if you want to block more than one URL. For example, for a list of URLs, enter: [\"URL1\", \"URL2\"] in this field. For a single URL enter: /'example.com/' |
Output
The JSON output contains a status message of whether or not the URL is successfully blocked on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"already_blocked": [],
"newly_blocked": [],
"not_block": []
}
operation: Unblock URL
Input parameters
| Parameter |
Description |
| URL |
List of URLs that you want to unblock on Fortinet FortiGate. URLs must be in the list format if you want to unblock more than one URL. For example, for a list of URLs, enter: [\"URL1\", \"URL2\"] in this field. For a single URL enter: /'example.com/' |
Output
The JSON output contains a status message of whether or not the URL is successfully unblocked on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"already_blocked": [],
"newly_blocked": [],
"not_block": []
}
operation: Block IP Address
Input parameters
| Parameter |
Description |
| Block Method |
Method to be used for blocking IP addresses using Fortinet FortiGate. You can choose from Quarantine Based or Policy Based.
- If you choose Quarantine Based, then you must specify the following parameters:
- IP Addresses: IP addresses that you want to block using Fortinet FortiGate, in the "CSV" or "list" format. For example,
["1.1.1.1", "2.2.2.2"] or "1.1.1.1", "2.2.2.2".
- Time to Live: Time till when the IP addresses will remain in the
Block status. You can choose between the following options: 1 Hour, 6 Hour, 12 Hour, 1 Day, 6 Months, 1 Year, or Custom Time.
Note: If you select Custom Time then the Time to Live (Seconds) field is displayed in which you must specify the Time to Live in seconds.
- VDOM: (Optional) VDOM that is used to block IP addresses. The VDOMs that you specify here will overwrite the VDOM(s) that you have specified as Configuration parameters. You can specify VDOM in the "CSV" or "list" format.
- If you choose Policy Base, then you must specify the following parameters:
- IPv4 Policy Name: Name of the IPv4 Policy that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter FortiSOAR_Blocked_Policy in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate section.
- Address Group Name: Name of the IP address group name that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter Blocked_IPs in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate section.
- IP Addresses: IP addresses that you want to block using Fortinet FortiGate in the "CSV" or "list" format.
For example, ["1.1.1.1", "2.2.2.2"] or "1.1.1.1", "2.2.2.2".
- VDOM: (Optional) VDOM that are used to block IP address. The VDOMs that you specify here will overwrite the VDOM(s) that you have specified as Configuration parameters. You can specify VDOM in the "CSV" or "list" format.
|
Output
The JSON output contains a status message of whether or not the IP Address is successfully blocked on Fortinet FortiGate.
When you choose “Quarantine Based” as the Block Method, then the output contains the following populated JSON schema:
{
"newly_blocked": [],
"already_blocked": [],
"vdom_not_exist": [],
"error_with_block": []
}
When you choose “Policy Based” as the Block Method, then the output contains the following populated JSON schema:
{
"newly_blocked": [],
"already_blocked": [],
"error_with_block": []
}
operation: Unblock IP Address
Input parameters
| Parameter |
Description |
| Block Method |
Method to be used for unblocking IP addresses using Fortinet FortiGate. You can choose from Quarantine Based or Policy Based.
- If you choose Quarantine Based, then you must specify the following parameters:
- IP Addresses: IP addresses that you want to unblock using Fortinet FortiGate, in the "CSV" or "list" format. For example,
["1.1.1.1", "2.2.2.2"] or "1.1.1.1", "2.2.2.2".
- VDOM: (Optional) VDOM that is used to unblock IP addresses. The VDOMs that you specify here will overwrite the VDOM(s) that you have specified as Configuration parameters. You can specify VDOM in the "CSV" or "list" format
- If you choose Policy Based, then you must specify the following parameters:
- IPv4 Policy Name: Name of the IPv4 Policy that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter FortiSOAR_Blocked_Policy in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate section.
- Address Group Name: Name of the IP address group name that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter Blocked_IPs in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate section.
- IP Addresses: IP addresses that you want to unblock using Fortinet FortiGate in the "CSV" or "list" format.
For example, ["1.1.1.1", "2.2.2.2"] or "1.1.1.1", "2.2.2.2".
- VDOM: (Optional) VDOM that is used to unblock IP addresses. The VDOMs that you specify here will overwrite the VDOM(s) that you have specified as Configuration parameters. You can specify VDOM in the "CSV" or "list" format.
|
Output
The JSON output contains a status message of whether or not the IP Address is successfully unblocked on Fortinet FortiGate.
When you choose “Quarantine Based” as the Unblock Method, then the output contains the following populated JSON schema:
{
"newly_unblocked": [],
"ip_not_exist": [],
"vdom_not_exist": [],
"error_with_unblock": []
}
When you choose “Policy Based” as the Unblock Method, then the output contains the following populated JSON schema:
{
"not_exist": [],
"newly_unblocked": [],
"error_with_unblock": []
}
operation: Block Application
Input parameters
| Parameter |
Description |
| Application Names |
List of application names that you want to block on Fortinet FortiGate. Application names must be in the list format if you want to block more than one application.
For example, for a list of applications enter ["Application_Name1", "Application_Name2"] in this field.
For a single application enter Application_Name.
Note: You can retrieve application names using the “Get Application Details” action. |
Output
The JSON output contains a status message of whether or not the application(s) are successfully blocked on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"message": "",
"name": "",
"status": ""
}
operation: Unblock Application
Input parameters
| Parameter |
Description |
| Application Names |
List of application names that you want to block on Fortinet FortiGate. Application names must be in the list format if you want to unblock more than one application.
For example, for a list of applications enter ["Application_Name1", "Application_Name2"] in this field.
For a single application enter Application_Name. |
Output
The JSON output contains a status message of whether or not the application(s) are successfully unblocked on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"message": "",
"name": "",
"status": ""
}
operation: Get Blocked URLs
Input parameters
None.
Output
The JSON output retrieves a list of URLs that are blocked using the Web Filter Profile Name that you have configured.
The output contains the following populated JSON schema:
{
"exempt": "",
"referrer-host": "",
"web-proxy-profile": "",
"url": "",
"q_origin_key": "",
"id": "",
"status": "",
"dns-address-family": "",
"action": "",
"type": ""
}
operation: Get Blocked IP Addresses
Input parameters
| Parameter |
Description |
| Block Method |
Method to be used for retrieving a list of IP Addresses that are blocked on Fortinet FortiGate. You can choose from Quarantine Based or Policy Based.
- If you choose Quarantine Based, then you can specify the following parameter:
- VDOM: (Optional) VDOMs whose associated list of blocked IP addresses you want to retrieve from Fortinet FortiGate. The VDOMs that you specify here will overwrite the VDOM(s) that you have specified as Configuration parameters. You can specify VDOM in the "CSV" or "list" format.
- If you choose Policy Based, then you can specify the following parameters:
- IPv4 Policy Name: Name of the IPv4 Policy that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses and whose associated list of blocked IP addresses you want to retrieve from Fortinet FortiGate. Based on our example, enter FortiSOAR_Blocked_Policy in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate section.
- Address Group Name: Name of the IP address group name that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter Blocked_IPs in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate section.
- VDOM: (Optional) VDOMs whose associated list of blocked IP addresses you want to retrieve from Fortinet FortiGate. The VDOMs that you specify here will overwrite the VDOM(s) that you have specified as Configuration parameters. You can specify VDOM in the "CSV" or "list" format.
|
Output
The JSON output retrieves a list of IP Addresses that are blocked using the IP Block Policy that you have configured.
When you choose “Quarantine Based” as the method to be used for retrieving a list of IP Addresses that are blocked on Fortinet FortiGate, then the output contains the following populated JSON schema:
{
"result": [
{
"name": "",
"path": "",
"serial": "",
"http_method": "",
"status": "",
"results": [
{
"ipv6": "",
"source": "",
"created": "",
"ip_address": "",
"expires": ""
}
],
"build": "",
"version": "",
"vdom": ""
}
],
"vdom_not_exist": []
}
When you choose “Policy Based” as the Block Method, as the method to be used for retrieving a list of IP Addresses that are blocked on Fortinet FortiGate, then the output contains a list of blocked IP addresses.
{
"dstaddr": [],
"srcaddr": [],
"addrgrp": [
{
"name": "",
"member": []
}
],
"addrgrp_not_exist": [],
"policy_name": ""
}
operation: Get Blocked Applications
Input parameters
None.
Output
The JSON output retrieves a list of application names that are blocked using the Application Control Profile Name that you have configured.
Following image displays a sample output:
The output contains the following populated JSON schema:
{
"popularity": "",
"risk": "",
"q_global_entry": "",
"q_no_rename": false,
"protocol": "",
"q_origin_key": "",
"metadata": [
{
"id": "",
"metaid": "",
"q_origin_key": "",
"valueid": ""
}
],
"q_mkey_type": "",
"weight": "",
"q_static": true,
"q_path": "",
"parameter": "",
"vendor": "",
"name": "",
"q_class": "",
"category": "",
"q_type": "",
"q_name": "",
"q_ref": "",
"id": "",
"behavior": "",
"sub-category": "",
"technology": ""
}
Included playbooks
The Sample - Fortinet FortiGate - 4.0.1 playbook collection comes bundled with the Fortinet FortiGate connector. This playbook contains steps using which you can perform all supported actions. You can see the bundled playbooks in the Automation > Playbooks section in FortiSOAR™ after importing the Fortinet FortiGate connector.
- Block Application
- Block IP Address
- Block URL
- Get Applications Detail
- Get Blocked Applications
- Get Blocked IP Addresses
- Get Blocked URLs
- Get List of Policies
- Unblock Application
- Unblock IP Address
- Unblock URL
Note: If you are planning to use any of the sample playbooks in your environment, ensure that you clone those playbooks and move them to a different collection since the sample playbook collection gets deleted during the connector upgrade and delete.