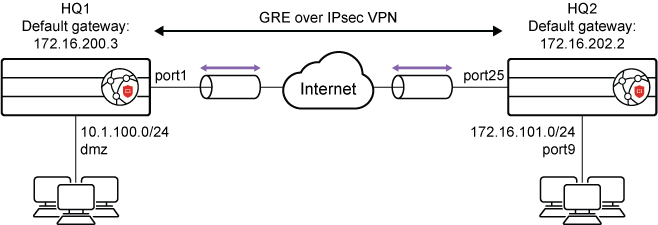
GRE over IPsec
This is an example of GRE over an IPsec tunnel using a static route over GRE tunnel and tunnel-mode in the phase2-interface settings.
To configure GRE over an IPsec tunnel:
- Enable subnet overlapping at both HQ1 and HQ2.
config system settings set allow-subnet-overlap enable end - Configure the WAN interface and static route.
- HQ1.
config system interface edit "port1" set ip 172.16.200.1 255.255.255.0 next edit "dmz" set ip 10.1.100.1 255.255.255.0 next end config router static edit 1 set gateway 172.16.200.3 set device "port1" next end - HQ2.
config system interface edit "port25" set ip 172.16.202.1 255.255.255.0 next edit "port9" set ip 172.16.101.1 255.255.255.0 next end config router static edit 1 set gateway 172.16.202.2 set device "port25" next end
- HQ1.
- Configure IPsec phase1-interface and phase2-interface.
- HQ1.
config vpn ipsec phase1-interface edit "greipsec" set interface "port1" set peertype any set proposal aes128-sha256 aes256-sha256 aes128-sha1 aes256-sha1 set remote-gw 172.16.202.1 set psksecret sample next end config vpn ipsec phase2-interface edit "greipsec" set phase1name "greipsec" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set protocol 47 next end - HQ2.
config vpn ipsec phase1-interface edit "greipsec" set interface "port25" set peertype any set proposal aes128-sha256 aes256-sha256 aes128-sha1 aes256-sha1 set remote-gw 172.16.200.1 set psksecret sample next end config vpn ipsec phase2-interface edit "greipsec" set phase1name "greipsec" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set protocol 47 next end
- HQ1.
- Configure IPsec tunnel interface IP address.
- HQ1.
config system interface edit "greipsec" set ip 10.10.10.1 255.255.255.255 set remote-ip 10.10.10.2 255.255.255.255 next end - HQ2.
config system interface edit "greipsec" set ip 10.10.10.2 255.255.255.255 set remote-ip 10.10.10.1 255.255.255.255 next end
- HQ1.
- Configure the GRE tunnel.
- HQ1.
config system gre-tunnel edit "gre_to_HQ2" set interface "greipsec" set remote-gw 10.10.10.2 set local-gw 10.10.10.1 next end - HQ2.
config system gre-tunnel edit "gre_to_HQ1" set interface "greipsec" set remote-gw 10.10.10.1 set local-gw 10.10.10.2 next end
- HQ1.
- Configure the firewall policy.
- HQ1.
config firewall policy edit 1 set srcintf "dmz" set dstintf "gre_to_HQ2" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next edit 2 set srcintf "gre_to_HQ2" set dstintf "dmz" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next edit 3 set srcintf "greipsec" set dstintf "greipsec" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next end - HQ2.
config firewall policy edit 1 set srcintf "port9" set dstintf "gre_to_HQ1" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next edit 2 set srcintf "gre_to_HQ1" set dstintf "port9" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next edit 3 set srcintf "greipsec" set dstintf "greipsec" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next end
- HQ1.
- Configure the static route.
- HQ1.
config router static edit 2 set dst 172.16.101.0 255.255.255.0 set device "gre_to_HQ2" next end - HQ2.
config router static edit 2 set dst 10.1.100.0 255.255.255.0 set device "gre_to_HQ1" next end
- HQ1.
-
Configure central SNAT in HQ1 and HQ2:
- HQ1.
config firewall central-snat-map edit 7 set srcintf "gre_to_HQ2" set dstintf "dmz" set src-addr "all" set dst-addr "all" next end - HQ2.
config firewall central-snat-map edit 7 set srcintf "gre_to_HQ1" set dstintf "port9" set src-addr "all" set dst-addr "all" next end
- HQ1.

