Integrating FortiPAM and GitLab- GUI
In the GitLab design, there are 3 methods to connect FortiPAM to JWT.
-
ID Token Mode (GitLab recommended)
-
Legacy
$CI_JOB_JWT -
Terraform Mode
Integrating FortiPAM and GitLab
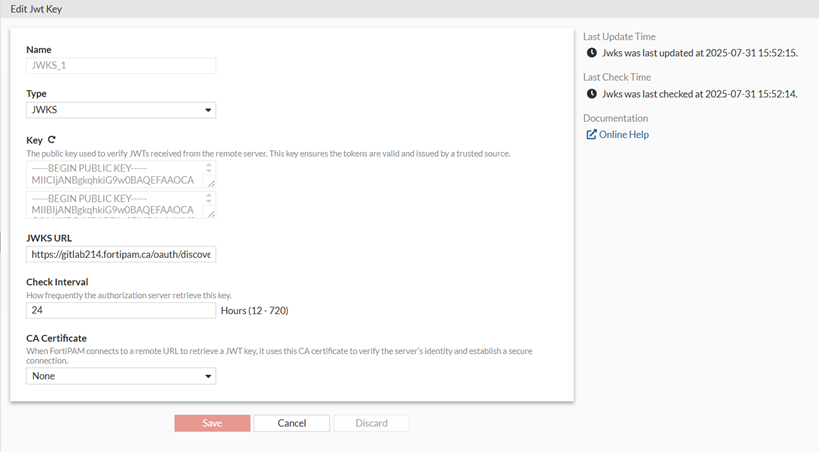
To create a JWT key:
- In the FortiPAM GUI, go to User Management > JWT Key Management, and select Create.
The New JWT Key window opens.
- Enter a name for the JWT key.
- In Type, select JWKS.
- In Key, enter the public key used to verify JWTs received from the remote server.
Select + to add additional keys.
Note: The key ensures the tokens are valid and issued by a trusted source.
- In JWKS URL, enter the JWKS URL.
- In Check Interval, keep the default value
24.The Check Interval is the frequency at which the authorization server retrieves the key, in hours.
-
Click Save.
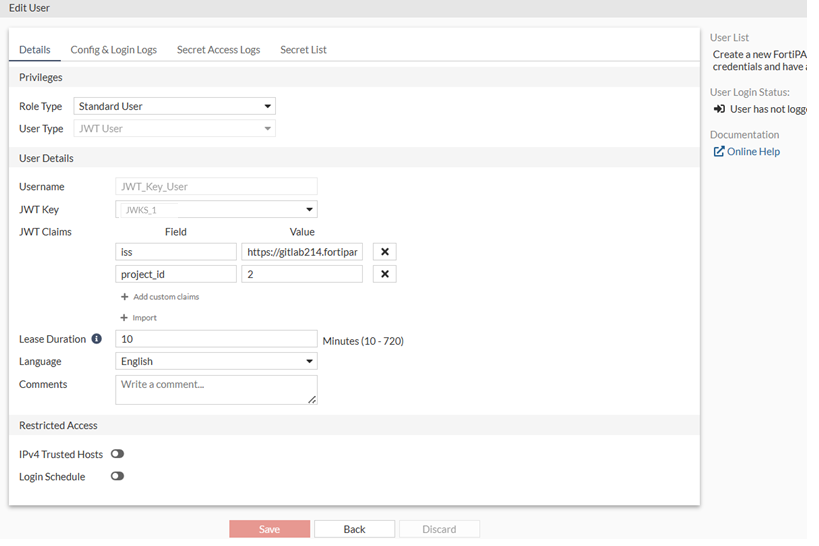
To create a JWT user:
- Go to User Management > User List, and select Create.
The New User List wizard is launched.
- In User Privilege, select Standard User, and click Next.
- In User Type, select JWT User, and click Next.
- In User Details:
- In Username, enter a username.
- In JWT key, select the JWT key earlier created.
- In JWT Claims, select Add custom claims to add JWT claims Field and Value.
- Ensure that the Lease Duration is set to 10 minutes.
The Lease Duration is the validity period of the token obtained through JWT authentication, in minutes.
- Select the language for the user.
- Click Next.
- Review the changes and click Submit.
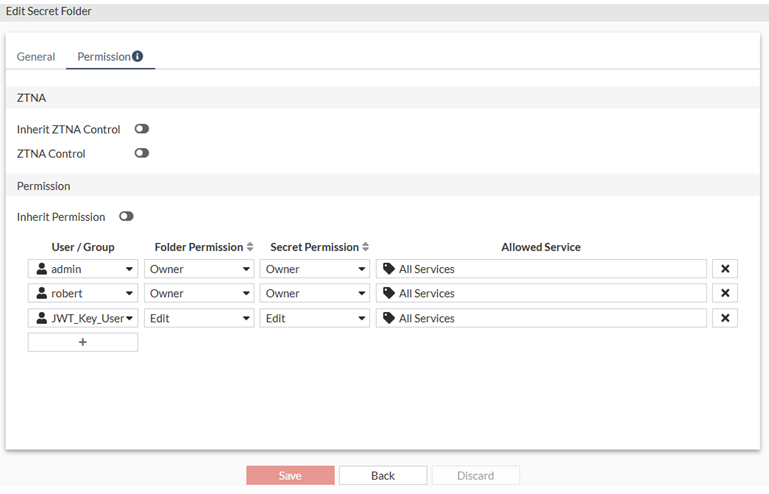
To grant secret permission to the JWT user:
- In Secrets, go to the secret folder.
- Double-click the folder to open it.
- Select Edit Current Folder.
- Go to the Permission tab, add users, and adjust the level of access they get into the folder.
- Click Save.