Required firmware upgrades for FortiGates with invalid support contracts or that have reached EOES
Since FortiOS 7.4.8 and 7.6.4, FortiGates are required to upgrade to the latest patch within their current minor version when:
-
FortiGate has an invalid Firmware & General Updates (FMWR) license.
-
FortiGate is running a minor FortiOS version that has reached end of engineering support (EOES).
This proactive measure ensures that all devices remain protected with the most up-to-date security features.
FortiGate checks FortiGuard daily for new patch upgrades. When a new patch is available, and the firmware license is invalid or the FortiGate firmware has reached EOES, FortiGate schedules a required upgrade to the new firmware image.
You cannot cancel required upgrades after they are scheduled; however, you can use the following method to adjust the installation schedule:
-
Use the
execute auto-upgrade delay-installationcommand to postpone the installation for a fixed 7-day period.This can be run an unlimited number of times. However, it cannot be run on the same day that the update is scheduled.
For required upgrades on FortiGates with an invalid license, the following information is communicated through the FortiGate FortiGuard communication protocol (FCPC) to FortiGuard:
-
ForcedUpdateflag -
Current <major>.<minor>.<patch>-<build> version, for example
7.4.10-2878
The ForcedUpdate flag instructs FortiGuard server to ignore the license check for the device and parse its firmware version. When the major and minor version on the upgrade-from and upgrade-to firmware are the same, the upgrade is allowed.
The firmware will upgrade to the latest patch in its current minor version. For example, if the current version is FortiOS 7.4.10, the firmware will automatically upgrade to the latest 7.4.x version. It will not upgrade to another minor version, such as 7.6.x. If there are multiple steps on the upgrade path, it will follow the upgrade path to reach the final patch.
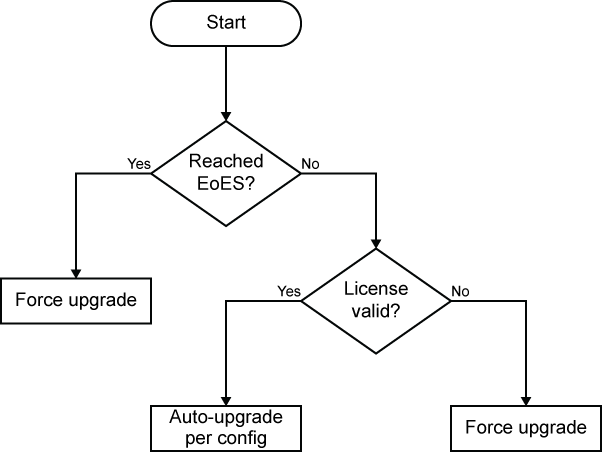
The following decision tree summarizes when a required automatic upgrade occurs on a FortiGate:
Notification methods
Several methods are used to notify administrators about a required upgrade. Before a required upgrade starts, the FortiOS GUI banner shows a new firmware version is available, for example, A new firmware version is available: v7.6.8. After FortiOS confirms a valid upgrade path for the required upgrade:
-
On the System > Firmware & Registration page:
-
The Upgrade Status column displays Upgrade to v7.6.8 shortly.
-
The Cancel Fabric Upgrade button is grayed out because forced upgrades cannot be canceled.
-
-
The Console prints the following information when scheduled to install the new image:
Auto-upgrade new image check triggered. Firmware Update from Management Service Upgrade to image 7.6.8b3800-F (07006000FIMG0025906008) has been scheduled between Sat Apr 4 14:08: 36 2026 and Sat Apr 4 15:00:00 2026. This upgrade is forced and cannot be cancelled, to delay this upgrade, please use "execute auto-upgrade delay-installation".
-
Default automation stitches trigger FortiGate to send email notifications:
-
FortiGate sends an email notification to the email address for the registered FortiCare account before and after upgrade using the
Firmware Upgrade ScheduledandFirmware Upgrade Completeautomation stitches. Following is an example of the email after upgrade:An automated firmware update has completed successfully. The device FortiGate-40F, serial number FGT40FTK<number>, was updated to firmware version 7.6.8 on 2026-4-4 15:00:06. This is an informational notification and was generated by automation stitch configuration on FortiGate-40F.
See Default automation stitches for more information.
-
Example 1: FortiGate required upgrade when firmware license is invalid
In this hypothetical scenario, a FortiGate is running FortiOS 7.6.7, and its firmware license expired on Friday, January 2, 2026:
System contracts:
FMWR,Fri Jan 2 2026
Checking its auto-upgrade status, the Support Contract Status is marked Expired:
# execute auto-upgrade status
Current Image Reached End of Life: no
Is current firmware a special build: No
Support Contract Status: Expired
Scheduled push image upgrade: no
Scheduled Config Restore: no
Scheduled Script Restore: no
Automatic image upgrade: Enabled.
New image information may be fetched.
New image installation may be cancelled by the user.
Next new image info fetch scheduled at (local time) Wed Apr 1 21:07:59 2026
A new firmware is available on the upgrade path on FortiGuard. FortiGate schedules an upgrade.
# execute auto-upgrade status
Current Image Reached End of Life: no
Is current firmware a special build: No
Support Contract Status: Expired
Scheduled push image upgrade: no
Scheduled Config Restore: no
Scheduled Script Restore: no
Automatic image upgrade: Enabled (Forced).
New image information may be fetched.
New image installation will be forced.
Next new image info fetch scheduled at (local time) Thu Apr 2 21:19:00 2026
New image 7.6.8b3800(07006000FIMG0025906008) installation is scheduled to:
start at Sat Apr 4 14:08:36 2026
end by Sat Apr 4 15:00:00 2026
Last new image info fetch executed at (local time) Wed Apr 1 21:07:59 2026
When the scheduled time is reached, FortiGate will request the download from the FortiGuard server. When FortiGuard server identifies this is a Required-Upgrade, it will bypass license check and allow the firmware image to be downloaded.
FortiGate will install the new image, reboot, and send an email notification to the administrator.
Example 2: FortiGate required upgrade when EOES reached
In this hypothetical scenario, a FortiGate has a valid firmware license but the current firmware has reached the EOES date.
The current firmware version is lower than the patch level image released on FortiGuard server.
Current firmware:
# get system status | grep Version Version: FortiGate-40F v7.6.7,build3679,260330
Available firmware on FortiGuard:
# diagnose fdsm image-list Last update: 895 secs ago. Total: 5 ... ... 07006000FIMG0025906008 v7.6 MR6-GA-F P8 b3800 (upgrade) 07002000FIMG0025902012 v7.2 MR2-GA-F P12 b1800 (downgrade) 07002000FIMG0025902011 v7.2 MR2-NA- b1737 (downgrade)
Upgrade path:
# diagnose fdsm image-upgrade-matrix Last update: 1013 secs ago. Total: 315 v8.0.0.(b150) -> v8.0.1.F(b1234) (id:08000000FIMG0025900001) v7.6.7.(b3679) -> v7.6.8.F(b3800) (id:07006000FIMG0025906008)
Checking its auto-upgrade status, the end of life status is set to yes.
FortiGate-40F (Interim)# execute auto-upgrade status
Current Image Reached End of Life: yes
Is current firmware a special build: No
Support Contract Status: Active
Scheduled push image upgrade: no
Scheduled Config Restore: no
Scheduled Script Restore: no
Automatic image upgrade: Enabled.
New image information may be fetched.
New image installation may be cancelled by the user.
Next new image info fetch scheduled at (local time) Thu Apr 2 14:33:55 2026
To force FortiGate to trigger a manual update-check, run this command:
# execute auto-upgrade check-for-new-image Manually triggering auto-upgrade new image check... Auto-upgrade new image check triggered. Firmware Update from Management Service Upgrade to image 7.6.8b3800-F (07006000FIMG0025906008) has been scheduled between Sat Apr 4 14:21:30 2026 and Sat Apr 4 15:00:00 2026. This upgrade is forced and cannot be cancelled, to delay this upgrade, please use "execute auto-upgrade delay-installation".
The FortiGate is now scheduled to perform the upgrade:
# execute auto-upgrade status
Current Image Reached End of Life: yes
Is current firmware a special build: No
Support Contract Status: Active
Scheduled push image upgrade: no
Scheduled Config Restore: no
Scheduled Script Restore: no
Automatic image upgrade: Enabled (Forced).
New image information may be fetched.
New image installation will be forced.
Next new image info fetch scheduled at (local time) Thu Apr 2 14:51:45 2026
New image 7.6.8b3800(07006000FIMG0025906008) installation is scheduled to:
start at Sat Apr 4 14:21:30 2026
end by Sat Apr 4 15:00:00 2026
Last new image info fetch executed at (local time) Wed Apr 1 17:41:10 2026
Upon the completion of the upgrade, FortiGate will trigger an automation stitch to send the registered FortiCare account owner an email stating:
An automated firmware update has completed successfully. The device FortiGate-40F, serial number FGT40FTK19004135, was updated to firmware version 7.6.8 on 2026-4-4 15:00:06.
This is an informational notification and was generated by automation stitch configuration on FortiGate-40F.
Administrators can delay an upgrade for one (1) week using the command:
# execute auto-upgrade delay-installation
Postponing auto-upgrade image installation to a week later...
Auto-upgrade image installation rescheduled to: start at local time Sat Apr 11 10:12:08 2026
end by local time Sat Apr 11 11:00:00 2026
Special considerations
The status of the FortiGate may affect required upgrades as follows:
-
When FortiGate is running a special FortiOS build, required upgrades do not apply.
-
When FortiGate is a part of the Security Fabric, it will not automatically upgrade the firmware. Alternatively, when a required upgrade is scheduled, FortiGate cannot join a Security Fabric.
-
When FortiGate is connected to FortiManager, it will not automatically upgrade the firmware. Likewise, when a required upgrade is scheduled, FortiGate can still connect to FortiManager, and the required firmware upgrade is canceled.
-
When FortiGate is part of an HA pair, the required firmware upgrade occurs for the primary FortiGate. The secondary FortiGate will not perform the required firmware upgrade on its own because automatic upgrade is disabled on secondary; however, the secondary FortiGate will receive the upgrade through a cluster upgrade initiated by the primary FortiGate.
-
When a required firmware upgrade is scheduled, it will block any new federated upgrades from occurring.

