Native VPN as dialup client - Windows New
Native VPN remote access configurations have been improved on the VPN wizard. For supported OS's, configurations from the VPN wizard will work out of the box. Native VPN client defaults to using L2TP over IPsec for Windows, Android, and macOS/iOS clients. Administrators can also configure IKEv2 for Windows and Android clients. DH groups and proposals have been updated to work with native clients.
In L2TP over IPsec mode, only pre-shared key is supported; signature cannot be chosen as Authentication method. Addressing mode must be set to Manual. These limitations do not apply to IKEv2 mode.
Organizations that manage a mixed environment (Windows, macOS, iOS, Android) can use the wizard to deploy a VPN tunnel that automatically aligns with each OS’s native VPN client defaults.
Example 1: Configure IPsec tunnel for native VPN clients

In this example, the FortiGate acts as a VPN gateway to provide secure internet access (SIA) through the shared WAN on port2, and for remote access to the Internal network through port9. The settings are compatible for Windows, Android, and macOS/iOS clients connecting through L2TP over IPsec. However, connecting from a Windows client is demonstrated here. User authentication is based on pre-defined usergroup local-group that contains a user called userc.
To configure L2TP IPsec tunnel from a template for Windows, Android, and macOS:
-
Go to VPN > VPN Wizard.
-
Name the VPN tunnel, select Remote Access template, and click Begin.
-
Configure the VPN tunnel settings, then click Next:
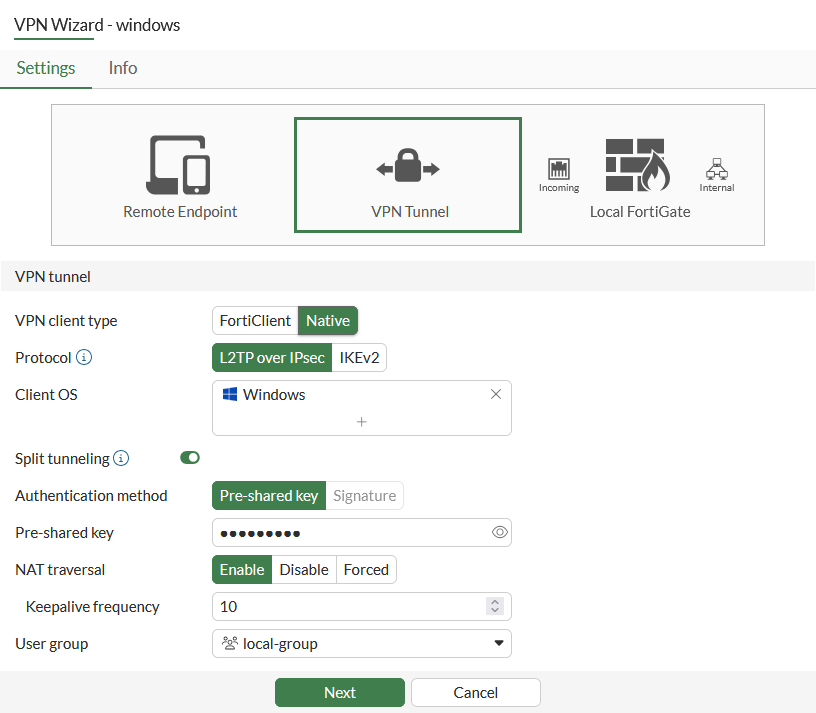
Parameter
Value
VPN client type
Native
Protocol
L2TP over IPsec
Client OS
Windows
Shared WAN
port2
Authentication method
Pre-Shared key
Pre-Shared key
Enter the pre-shared key
User group
local-group
-
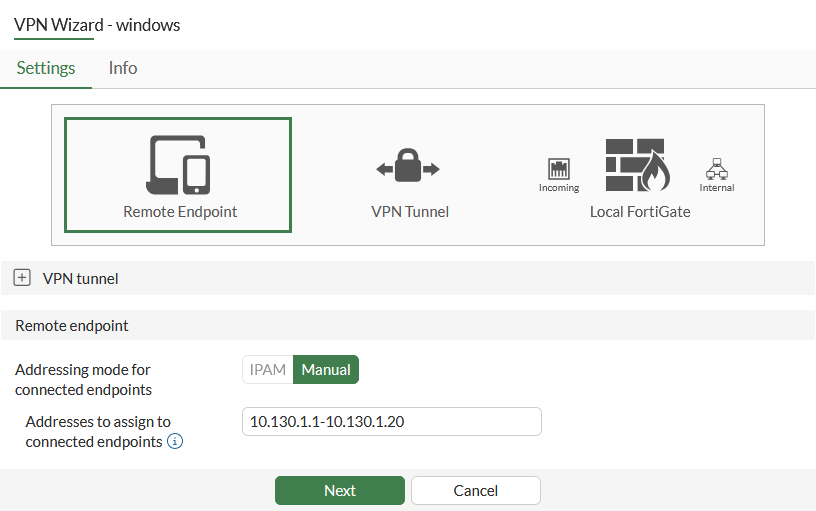
Set Addresses to assign to connected endpoints to 10.130.1.1-10.130.1.20, then click Next.
-
Configure the local FortiGate options, then click Next:
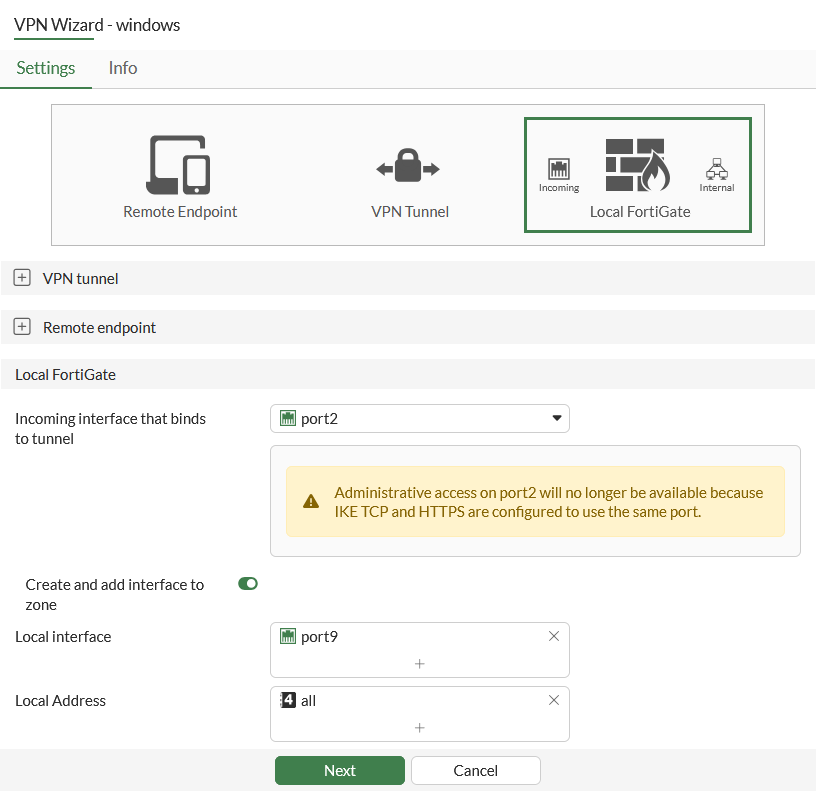
Parameter
Value
Incoming interface that binds to tunnel
port2
Local interface
port9
Local Address
all
-
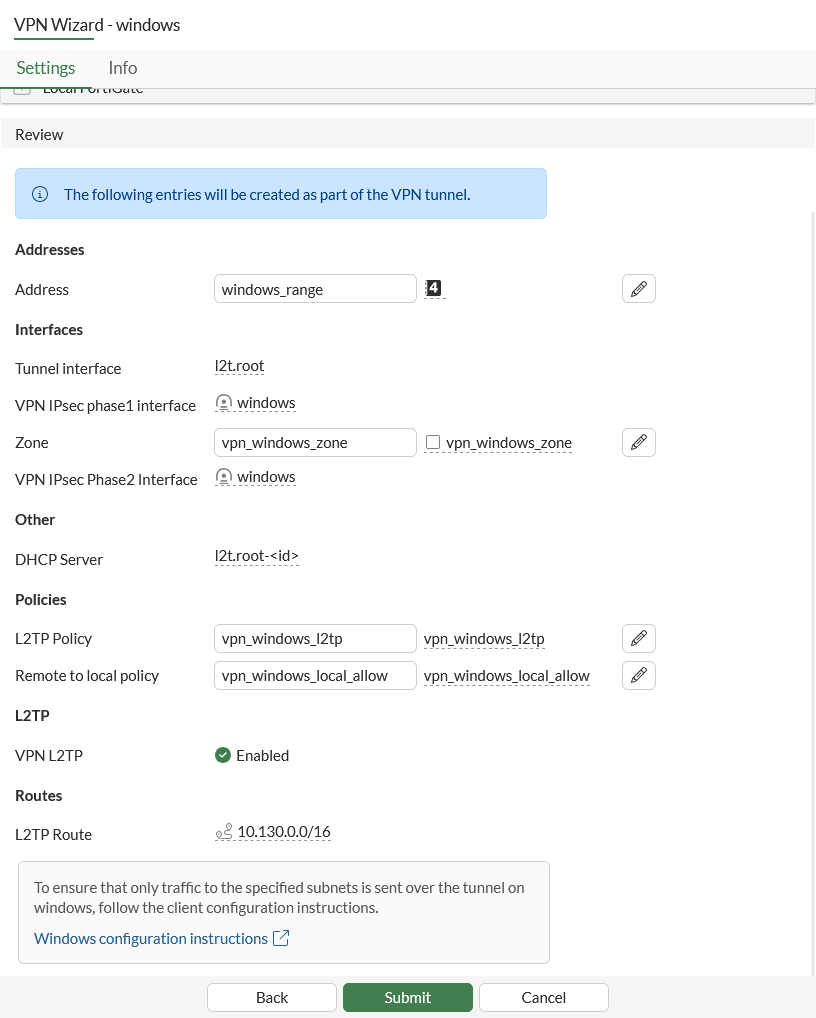
Review the configuration, then click Submit.
Only Android 12 and below are supported for L2TP VPN.
To configure L2TP connection for Windows:
-
Open VPN or go to Settings > Network & internet.
-
Add and configure a VPN:
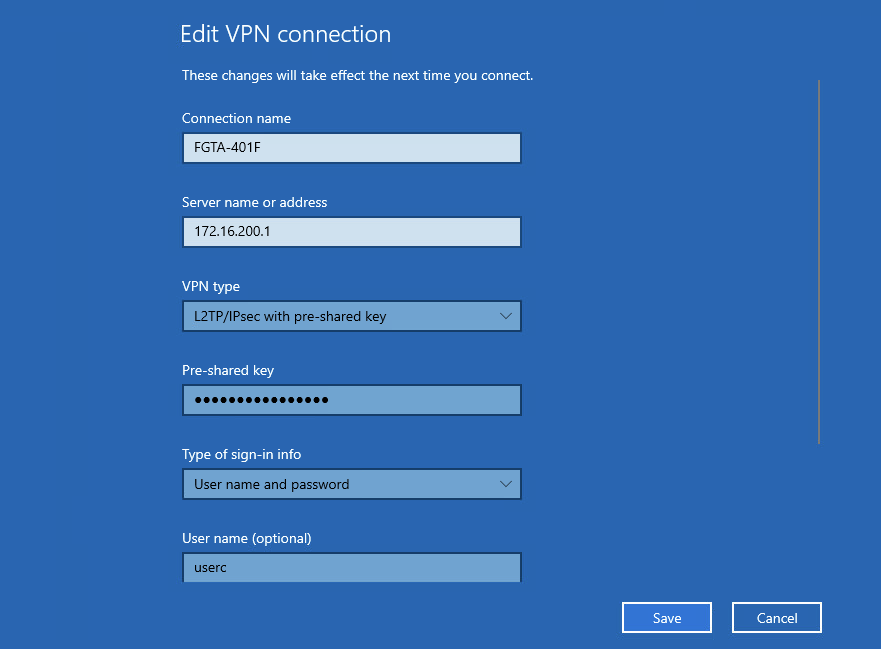
Parameter
Value
VPN provider
Windows (built-in)
Connection name
Enter a connection name.
Server name or address
Enter your FortiGate Firewall's hostname or IP address.
VPN type
L2TP/IPsec with pre-shared key
Pre-shared key
Enter the pre-shared key.
Type of sign-in info
Username and password
Username (optional)
Enter the username.
Password (optional)
Enter the password.
-
Click Save.
To configure L2TP IPsec tunnel in the CLI:
config user group
edit "local-group"
set member "usera" "userc"
next
end
config vpn ipsec phase1-interface
edit "windows"
set type dynamic
set interface "port1"
set ike-version 1
set peertype any
set net-device disable
set proposal aes256-sha512 aes256-sha256 aes256-sha1
set dhgrp 19 14 2
set wizard-type dialup-l2tp
set psksecret <password>
next
end
config vpn ipsec phase2-interface
edit "windows"
set phase1name "windows"
set proposal aes256-sha512 aes256-sha256 aes256-sha1
set pfs disable
set keepalive enable
set encapsulation transport-mode
set l2tp enable
next
end
config vpn l2tp
set status enable
set eip 10.130.1.20
set sip 10.130.1.1
set enforce-ipsec enable
set usrgrp "local-group"
end
config firewall address
edit "windows_range"
set type iprange
set start-ip 10.130.1.1
set end-ip 10.130.1.20
next
end
Three policies are created:
-
One to allow L2TP traffic into the WAN interface
-
One to allow VPN traffic to the local subnet
-
One to allow VPN traffic to the Internet
config firewall policy
edit 3
set name "vpn_windows_l2tp"
set srcintf "windows"
set dstintf "port2"
set action accept
set srcaddr "all"
set dstaddr "all"
set schedule "always"
set service "L2TP"
next
edit 4
set name "vpn_windows_local_allow"
set srcintf "l2t.root"
set dstintf "port9"
set action accept
set srcaddr "windows_range"
set dstaddr "all"
set schedule "always"
set service "ALL"
set nat enable
next
edit 5
set name "vpn_windows_utm_allow"
set srcintf "l2t.root"
set dstintf "port2"
set action accept
set srcaddr "windows_range"
set dstaddr "all"
set schedule "always"
set service "ALL"
set nat enable
next
endconfig router static
edit 2
set dst 10.130.0.0 255.255.0.0
set device "l2t.root"
next
end
To check the IPsec phase1/phase2 interface status:
# diagnose vpn ike gateway list vd: root/0 name: windows_0 version: 1 interface: port1 7 addr: 172.16.200.1:4500 -> 172.16.200.254:64916 tun_id: 172.16.200.254/::10.0.0.15 remote_location: 0.0.0.0 network-id: 0 transport: UDP created: 19s ago peer-id: 31.1.1.198 peer-id-auth: no nat: me peer pending-queue: 0 IKE SA: created 1/1 established 1/1 time 20/20/20 ms IPsec SA: created 1/1 established 1/1 time 0/0/0 ms id/spi: 16 ccfbf5c901e3899f/547217d62b9bc1ef direction: responder status: established 19-19s ago = 20ms proposal: aes256-sha1 key: cd7c7a2385ef9085-30a95bab3c1a6178-4dea8ede135046e0-fbb2c44074b6fd74 QKD: no PQC-KEM (IKE): no PQC-KEM (all IPsec): no lifetime/rekey: 28800/28510 DPD sent/recv: 00000000/00000000 peer-id: 31.1.1.198
# diagnose vpn tunnel list
list all ipsec tunnel in vd 0
------------------------------------------------------
name=windows_0 ver=1 serial=10 172.16.200.1:4500->172.16.200.254:64916 nexthop=0.0.0.0 tun_id=172.16.200.254 tun_id6=::10.0.0.15 status=up dst_mtu=1500 weight=1 country=ZZ
bound_if=7 real_if=7 lgwy=static/1 tun=intf mode=dial_inst/3 encap=none options[0x23a8]=npu rgwy-chg rport-chg frag-rfc run_state=0 role=primary accept_traffic=1 overlay_id=0
parent=windows index=0
proxyid_num=1 child_num=0 refcnt=6 ilast=0 olast=42955707 ad=/0
stat: rxp=6 txp=0 rxb=696 txb=0
dpd: mode=on-demand on=1 status=ok idle=60000ms retry=3 count=0 seqno=0
natt: mode=keepalive draft=32 interval=10 remote_port=64916
fec: egress=0 ingress=0
proxyid=windows proto=17 sa=1 ref=2 serial=1 transport-mode add-route
src: 17:172.16.200.1-172.16.200.1:1701
dst: 17:172.16.200.254-172.16.200.254:0
SA: ref=3 options=1a7 type=00 soft=0 mtu=1454 expire=3563/0B replaywin=2048
seqno=401 esn=0 replaywin_lastseq=00000006 qat=0 rekey=0 hash_search_len=1
life: type=01 bytes=0/0 timeout=3589/3600
dec: spi=a91127c2 esp=aes key=32 e54c49f9205f06ff55e9e974eefa00079bd57466041cf0a0512a11193a533a36
ah=sha1 key=20 3eca7a57dda0ae2dbdf589f2798a2539b3ca774b
enc: spi=c8be2f10 esp=aes key=32 008379628c4d67a232fb43dd2b7606bb43c8e02a731df7b90833485e2bb9f522
ah=sha1 key=20 0291e163d22963ebe01bc8cc075cfabef935c10d
dec:pkts/bytes=6/696, enc:pkts/bytes=0/0
npu_flag=00 npu_rgwy=0.0.0.0:0 npu_lgwy=0.0.0.0:0npu_selid=e
dec_npuid=0 enc_npuid=0 dec_engid=-1 enc_engid=-1 dec_saidx=-1 enc_saidx=-1
------------------------------------------------------
name=windows ver=1 serial=2 172.16.200.1:0->0.0.0.0:0 nexthop=0.0.0.0 tun_id=10.0.0.1 tun_id6=::10.0.0.1 status=up dst_mtu=0 weight=1
bound_if=7 real_if=0 lgwy=static/1 tun=intf mode=dialup/2 encap=none options[0x228]=npu frag-rfc role=primary accept_traffic=1 overlay_id=0
proxyid_num=0 child_num=1 refcnt=3 ilast=42955707 olast=42955707 ad=/0
stat: rxp=30 txp=0 rxb=3480 txb=0
dpd: mode=on-demand on=0 status=ok idle=20000ms retry=3 count=0 seqno=0
natt: mode=none draft=0 interval=0 remote_port=0
fec: egress=0 ingress=0# diagnose debug enable # diagnose debug app ike -1 # diagnose debug app fnbam -1 ike V=root:0:ccfbf5c901e3899f/0000000000000000:16: responder: main mode get 1st message... ... ike V=root:0:windows: adding new dynamic tunnel for 172.16.200.254:64916 ike V=root:0:windows_0: tunnel created tun_id 172.16.200.254/::10.0.0.15 remote_location 0.0.0.0 ike V=root:0:windows_0: added new dynamic tunnel for 172.16.200.254:64916 ike V=root:0:windows_0:16: established IKE SA ccfbf5c901e3899f/547217d62b9bc1ef ike V=root:0:windows_0: DPD disabled, not negotiated ike V=root:0:windows_0:16: check peer route: if_addr4_rcvd=0, if_addr6_rcvd=0, mode_cfg=0 ike V=root:0:windows_0:16: no pending Quick-Mode negotiations ike V=root:0: udp comes 172.16.200.254:64916->172.16.200.1:4500,ifindex=7,vrf=0,len=448.... ike V=root:0: IKEv1 exchange=Quick id=ccfbf5c901e3899f/547217d62b9bc1ef:00000001 len=444 vrf=0 ... ike V=root:0:windows_0:16:61: received NATOA-i 31.1.1.198 ike V=root:0:windows_0:16:61: received NATOA-r 172.18.68.206 ike V=root:0:windows_0:16:61: peer proposal is: peer:17:31.1.1.198-31.1.1.198:1701, me:17:172.18.68.206-172.18.68.206:1701 ike V=root:0:windows_0:16:windows:61: trying ike V=root:0:windows_0:16:61: L2TP selectors 17:172.18.68.206-172.18.68.206:1701 -> 17:31.1.1.198-31.1.1.198:1701 ike V=root:0:windows_0:16:61: transport mode, override with 17:172.16.200.1-172.16.200.1:1701 -> 17:172.16.200.254-172.16.200.254:0 ike V=root:0:windows_0:16:windows:61: matched phase2 ike V=root:0:windows_0:16:windows:61: dynamic client ike V=root:0:windows_0:16:windows:61: my proposal: ike V=root:0:windows_0:16:windows:61: proposal id = 1: ike V=root:0:windows_0:16:windows:61: protocol id = IPSEC_ESP: ike V=root:0:windows_0:16:windows:61: trans_id = ESP_AES_CBC (key_len = 256) ike V=root:0:windows_0:16:windows:61: encapsulation = ENCAPSULATION_MODE_TRANSPORT ike V=root:0:windows_0:16:windows:61: type = AUTH_ALG, val=SHA2_512 ike V=root:0:windows_0:16:windows:61: trans_id = ESP_AES_CBC (key_len = 256) ike V=root:0:windows_0:16:windows:61: encapsulation = ENCAPSULATION_MODE_TRANSPORT ike V=root:0:windows_0:16:windows:61: type = AUTH_ALG, val=SHA2_256 ike V=root:0:windows_0:16:windows:61: trans_id = ESP_AES_CBC (key_len = 256) ike V=root:0:windows_0:16:windows:61: encapsulation = ENCAPSULATION_MODE_TRANSPORT ike V=root:0:windows_0:16:windows:61: type = AUTH_ALG, val=SHA1 ike V=root:0:windows_0:16:windows:61: incoming proposal: ike V=root:0:windows_0:16:windows:61: proposal id = 1: ike V=root:0:windows_0:16:windows:61: protocol id = IPSEC_ESP: ike V=root:0:windows_0:16:windows:61: trans_id = ESP_AES_CBC (key_len = 256) ike V=root:0:windows_0:16:windows:61: encapsulation = UDP_ENCAPSULATION_MODE_TRANSPORT_RFC3947 ike V=root:0:windows_0:16:windows:61: type = AUTH_ALG, val=SHA1 ike V=root:0:windows_0:16:windows:61: negotiation result ike V=root:0:windows_0:16:windows:61: proposal id = 1: ike V=root:0:windows_0:16:windows:61: protocol id = IPSEC_ESP: ike V=root:0:windows_0:16:windows:61: trans_id = ESP_AES_CBC (key_len = 256) ike V=root:0:windows_0:16:windows:61: encapsulation = ENCAPSULATION_MODE_TRANSPORT ike V=root:0:windows_0:16:windows:61: type = AUTH_ALG, val=SHA1 ike V=root:0:windows_0:16:windows:61: using udp transport mode. ike V=root:0:windows_0:16:61: sending NATOA-i 172.16.200.254 ike V=root:0:windows_0:16:61: sending NATOA-r 172.16.200.1 ike V=root:0:windows_0:16:windows:61: replay protection enabled ike V=root:0:windows_0:16:windows:61: SA life soft seconds=3589. ike V=root:0:windows_0:16:windows:61: SA life hard seconds=3600. ike V=root:0:windows_0:16:windows:61: IPsec SA selectors #src=1 #dst=1 ike V=root:0:windows_0:16:windows:61: src 0 7 17:172.16.200.1-172.16.200.1:1701 ike V=root:0:windows_0:16:windows:61: dst 0 7 17:172.16.200.254-172.16.200.254:0 ike V=root:0:windows_0:16:windows:61: add dynamic IPsec SA selectors 183 ike V=root:0:windows_0:16:windows:61: added dynamic IPsec SA proxyids new 1 183 ike V=root:0:windows:61: add route 172.16.200.254/255.255.255.255 gw 172.16.200.254 oif windows(51) metric 15 priority 1 ike V=root:0:windows_0:16:windows:61: tunnel 1 of VDOM limit 0/0 ike V=root:0:windows_0:16:windows:61: add IPsec SA: SPIs=a91127c2/c8be2f10 ike 0:windows_0:16:windows:61: IPsec SA dec spi a91127c2 key 32:E54C49F9205F06FF55E9E974EEFA00079BD57466041CF0A0512A11193A533A36 auth 20:3ECA7A57DDA0AE2DBDF589F2798A2539B3CA774B ike 0:windows_0:16:windows:61: IPsec SA enc spi c8be2f10 key 32:008379628C4D67A232FB43DD2B7606BB43C8E02A731DF7B90833485E2BB9F522 auth 20:0291E163D22963EBE01BC8CC075CFABEF935C10D ike V=root:0:windows_0:16:windows:61: transport mode encapsulation is enabled ike V=root:0:windows_0:16:windows:61: added IPsec SA: SPIs=a91127c2/c8be2f10 ike V=root:0:windows_0:16:windows:61: sending SNMP tunnel UP trap ike V=root:0:windows_0: tunnel up event ...
Example 2: Configure IKE v2 IPsec tunnel from template for Windows
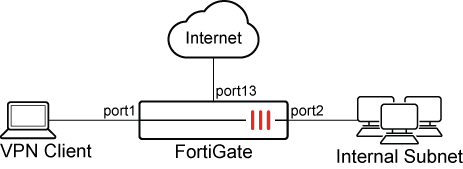
In this example, the FortiGate acts as a VPN gateway to provide secure internet access (SIA) through the shared WAN on port13, and for remote access to the Internal network through port2. The settings are compatible for Windows and Android clients only connecting through IKEv2. However, connecting from a Windows client is demonstrated here. Signature authentication is used, and user authentication is based on RADIUS authentication.
To configure IKE v2 IPsec tunnel from a template for Windows:
-
Go to VPN > VPN Wizard.
-
Name the VPN tunnel, select Remote Access template, and click Begin.
-
Configure the VPN tunnel settings, then click Next:
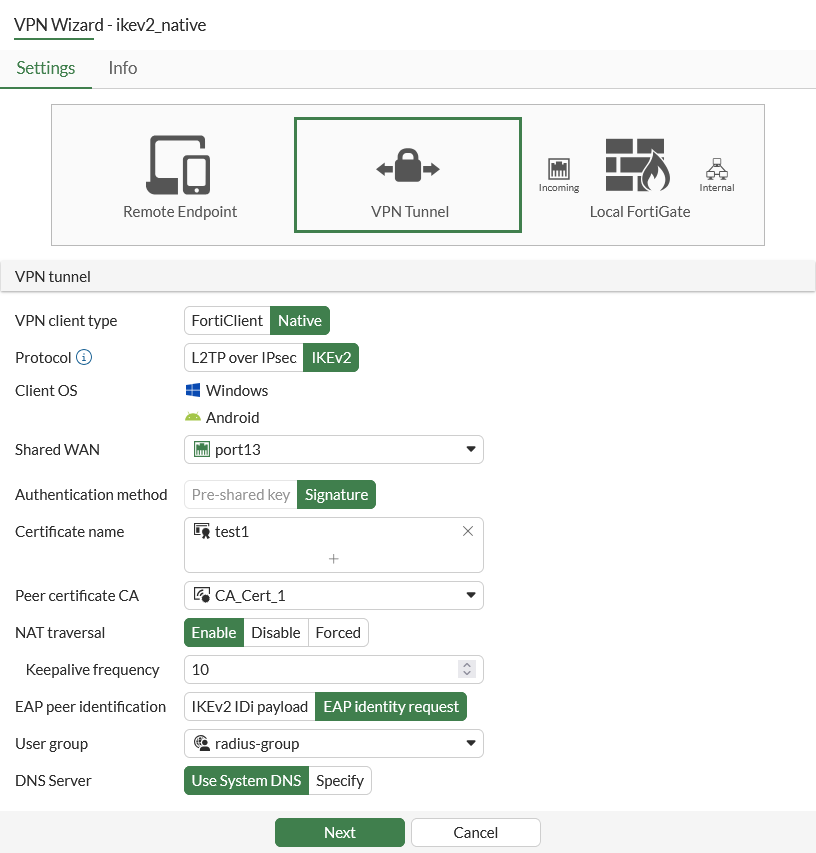
Parameter
Value
VPN client type
Native
Protocol
IKEv2
Shared WAN
port13
Authentication method
Signature
Certificate names
test1
Peer Certificate CA
CA_Cert_1
User group
radius-group
-
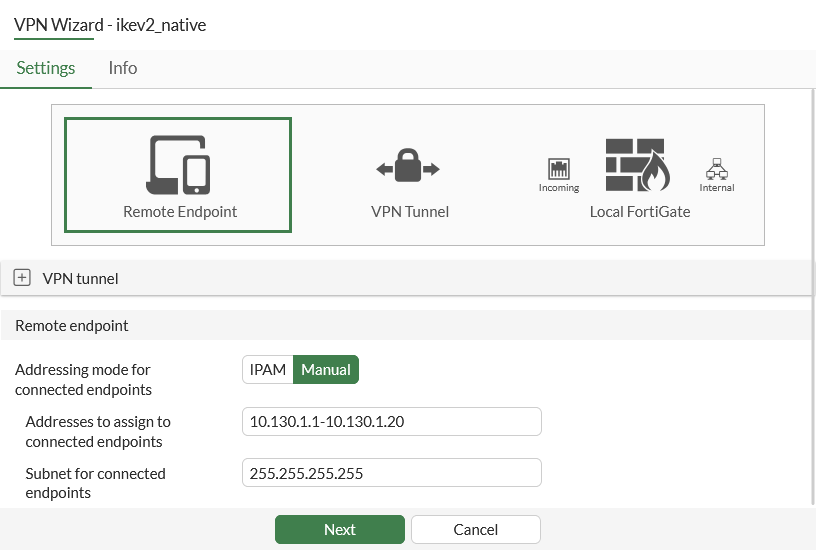
Set Addressing mode for connected endpoints to Manual and set Addresses to assign to connected endpoints to 10.130.1.1-10.130.1.20, then click Next.
-
Configure the local FortiGate options, then click Next:
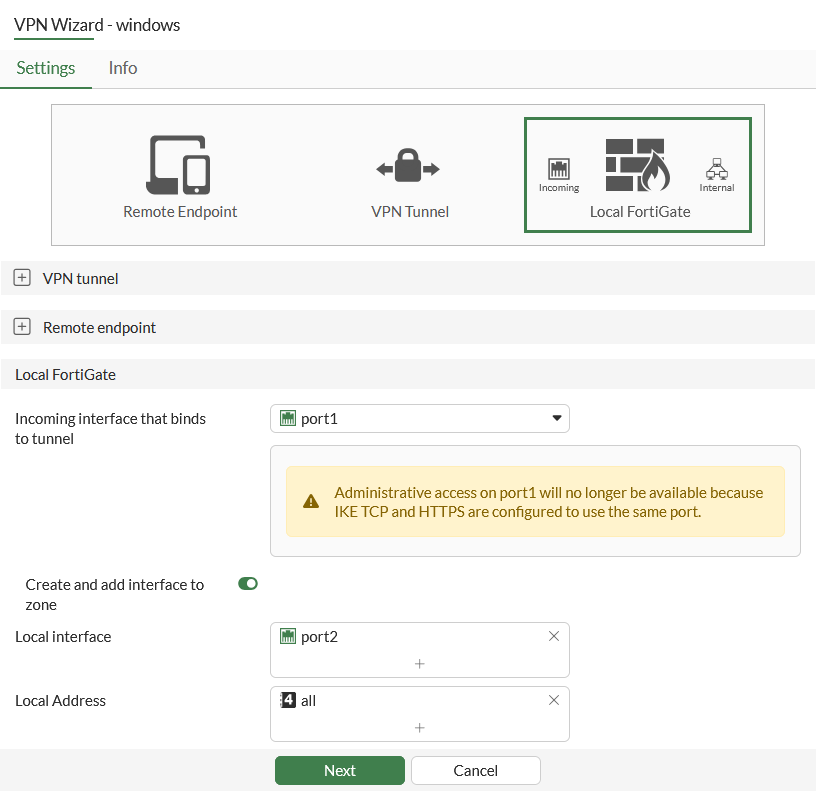
Parameter
Value
Incoming interface that binds to tunnel
port1
Local interface
port2
Local Address
all
-
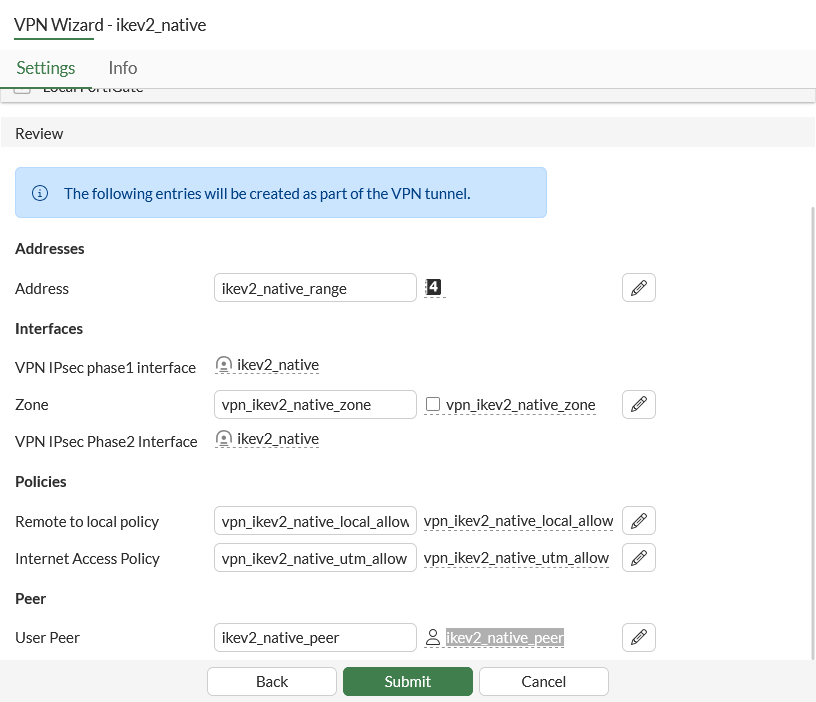
Review the configuration, then click Submit.
To configure IKEv2 VPN connection for Windows:
-
Open VPN or go to Settings > Network & internet.
-
Add and configure a VPN:
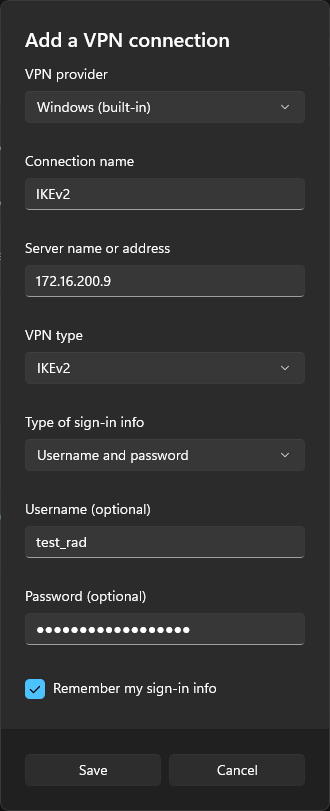
Parameter
Value
VPN provider
Windows (built-in)
Connection name
Enter a connection name.
Server name or address
Enter your FortiGate Firewall's hostname or IP address.
VPN type
IKEv2
Type of sign-in info
Username and password
Username (optional)
Enter the username.
Password (optional)
Enter the password.
-
Click Save.
To configure IKE v2 IPsec tunnel for Windows in the CLI:
config vpn ipsec phase1-interface
edit "ikev2_native"
set type dynamic
set interface "port1"
set ike-version 2
set authmethod signature
set net-device disable
set mode-cfg enable
set proposal aes256-sha256 aes256gcm-prfsha256 aes256gcm-prfsha384
set dhgrp 20 14 2
set eap enable
set eap-identity send-request
set wizard-type dialup-ikev2
set authusrgrp "radius-group"
set certificate "test1"
set peer "ikev2_native_peer"
set assign-ip-from name
set dns-mode auto
set ipv4-name "ikev2_native_range"
next
end
config vpn ipsec phase2-interface
edit "ikev2_native"
set phase1name "ikev2_native"
set proposal aes256gcm aes256-sha1 aes128-sha1
set pfs disable
set keepalive enable
next
endconfig firewall policy
edit 1
set name "vpn_ikev2_native_local_allow"
set uuid 402dbbe2-0de4-51f1-202f-ea123f6da629
set srcintf "ikev2_native"
set dstintf "port2"
set action accept
set srcaddr "ikev2_native_range"
set dstaddr "all"
set schedule "always"
set service "ALL"
set nat enable
next
edit 2
set name "vpn_ikev2_native_utm_allow"
set uuid 402fbab4-0de4-51f1-97c2-2e4456a64492
set srcintf "ikev2_native"
set dstintf "port13"
set action accept
set srcaddr "ikev2_native_range"
set dstaddr "all"
set schedule "always"
set service "ALL"
set nat enable
next
end
config firewall address
edit "ikev2_native_range"
set uuid 402b4d9e-0de4-51f1-c355-1375e255836b
set type iprange
set start-ip 10.130.1.1
set end-ip 10.130.1.20
next
endconfig router static
edit 1
set gateway 172.16.200.254
set device "port1"
next
end
To check the IPsec phase1/phase2 interface status:
# diagnose vpn ike gateway list vd: root/0 name: ikev2_native_0 version: 2 interface: port1 7 addr: 172.16.200.4:4500 -> 172.16.200.254:64917 tun_id: 10.130.1.1/::10.0.0.5 remote_location: 0.0.0.0 network-id: 0 transport: UDP created: 9s ago eap-user: test_rad 2FA: no assigned IPv4 address: 10.130.1.1/0.0.0.0 nat: me peer pending-queue: 0 PPK: no IKE SA: created 1/1 established 1/1 time 230/230/230 ms IPsec SA: created 1/1 established 1/1 time 0/0/0 ms id/spi: 89 bc5aa3bb99c0963c/290cf660b0977bf5 direction: responder status: established 9-8s ago = 230ms proposal: aes256-sha256 child: no SK_ei: 1f769b39b6e45680-bc358b9bbd82e462-5f0843ec67ac6a5a-56ef87e3cd629067 SK_er: 094a6134c1e9e472-8730eb86ceb92a04-292ea04fa3514643-1ad51077fc429420 SK_ai: 1cb620c46998be6e-aaa2136a04ccae9a-d478963782112a87-c35806662125531b SK_ar: 9d3c9205a68e9efb-3d95fce5b3bbb81a-b2642e584c509f6c-08be1b3cd27a2a02 PPK: no message-id sent/recv: 0/7 QKD: no PQC-KEM (IKE): no PQC-KEM (all IPsec): no lifetime/rekey: 86400/86121 DPD sent/recv: 00000000/00000000
# diagnose vpn tunnel list
list all ipsec tunnel in vd 0
------------------------------------------------------
name=ikev2_native ver=2 serial=4 172.16.200.4:0->0.0.0.0:0 nexthop= tun_id=10.0.0.2 tun_id6=::10.0.0.2 status=up dst_mtu=0 weight=1
bound_if=7 real_if=0 lgwy=static/1 tun=intf mode=dialup/2 encap=none options[0x228]=npu frag-rfc role=primary accept_traffic=1 overlay_id=0
proxyid_num=0 child_num=1 refcnt=3 ilast=42973580 olast=42973580 ad=/0
stat: rxp=203 txp=0 rxb=31104 txb=0
dpd: mode=on-demand on=0 status=ok idle=20000ms retry=3 count=0 seqno=0
natt: mode=none draft=0 interval=0 remote_port=0
fec: egress=0 ingress=0
------------------------------------------------------
name=ikev2_native_0 ver=2 serial=6 172.16.200.4:4500->172.16.200.254:64917 nexthop= tun_id=10.130.1.1 tun_id6=::10.0.0.5 status=up dst_mtu=0 weight=1 country=ZZ
bound_if=7 real_if=0 lgwy=static/1 tun=intf mode=dial_inst/3 encap=none options[0x23a8]=npu rgwy-chg rport-chg frag-rfc run_state=0 role=primary accept_traffic=1 overlay_id=0
parent=ikev2_native index=0
proxyid_num=1 child_num=0 refcnt=6 ilast=0 olast=42973580 ad=/0
stat: rxp=72 txp=0 rxb=11248 txb=0
dpd: mode=on-demand on=1 status=ok idle=20000ms retry=3 count=0 seqno=0
natt: mode=keepalive draft=0 interval=10 remote_port=64917
fec: egress=0 ingress=0
proxyid=ikev2_native proto=0 sa=1 ref=2 serial=1 add-route
src: 0:0.0.0.0-255.255.255.255:0
dst: 0:10.130.1.1-10.130.1.1:0
SA: ref=4 options=4a7 type=00 soft=0 mtu=1280 expire=43173/0B replaywin=2048
seqno=1 esn=0 replaywin_lastseq=00000002 qat=0 rekey=0 hash_search_len=1
life: type=01 bytes=0/0 timeout=43189/43200
dec: spi=5c8e4a53 esp=aes key=32 34420e33f9e18eea020278fdeadfc111aa099f84e1dd2a0f25ec20fd242bff9f
ah=sha1 key=20 4a4f61a0a89017d5ac711be76adb3631b1f24be5
enc: spi=ec7bfcfc esp=aes key=32 80a0b64bdf7e1caca170a0641dca00dd657629af8913c5baeacc209edc4ccac3
ah=sha1 key=20 ebd8bc8a2f88cd2dc8a2232fdadb7fc627694a77
dec:pkts/bytes=72/11248, enc:pkts/bytes=0/0
npu_flag=02 npu_rgwy=172.16.200.254:64917 npu_lgwy=172.16.200.4:4500npu_selid=3
dec_npuid=1 enc_npuid=0 dec_engid=-1 enc_engid=-1 dec_saidx=3 enc_saidx=-1# diagnose debug enable # diagnose debug app ike -1 # diagnose debug app fnbam -1 ike V=root:0: udp comes 172.16.200.254:1012->172.16.200.4:500,ifindex=7,vrf=0,len=624.... ike V=root:0: IKEv2 exchange=SA_INIT id=bc5aa3bb99c0963c/0000000000000000 len=624 ... ike V=root:0:ikev2_native:89: reassembled fragmented message ike V=root:0:ikev2_native:89: responder received AUTH msg ike V=root:0:ikev2_native:89: processing notify type MOBIKE_SUPPORTED ike V=root:0:ikev2_native:89: peer identifier IPV4_ADDR 172.17.249.189 ike V=root:0:ikev2_native:89: eap-peer=yes ike V=root:0:ikev2_native:89: re-validate gw ID ike V=root:0:ikev2_native:89: gw validation OK ... ike V=root:0:ikev2_native:89: responder preparing EAP identity request ike V=root:0:ikev2_native:89: local cert, subject='172.18.68.209', issuer='eku-ca' ike V=root:0:ikev2_native:89: local CA cert, subject='eku-ca', issuer='eku-ca' ... ike V=root:0:ikev2_native:89: sent IKE msg (AUTH_RESPONSE): 172.16.200.4:4500->172.16.200.254:64917, len=148, vrf=0, id=bc5aa3bb99c0963c/290cf660b0977bf5:00000001, oif=7 ike V=root:0: udp comes 172.16.200.254:64917->172.16.200.4:4500,ifindex=7,vrf=0,len=100.... ike V=root:0: IKEv2 exchange=AUTH id=bc5aa3bb99c0963c/290cf660b0977bf5:00000002 len=96 ike 0: in BC5AA3BB99C0963C290CF660B0977BF52E2023080000000200000060300000442BFE21A653DCF88A4F0CA11AD6C68644ECCF0388EE7FB9AB1E00C94DD75AE4A1D24007C230347591E0B69DADA0D9878F315EDC6D47851E78EF816D43CBA95A67 ike 0:ikev2_native:89: dec BC5AA3BB99C0963C290CF660B0977BF52E20230800000002000000313000000400000011025A000D01746573745F726164 ike V=root:0:ikev2_native:89: responder received EAP msg ike V=root:0:ikev2_native:89: send EAP message to FNBAM ike V=root:0:ikev2_native:89: initiating EAP authentication ike V=root:0:ikev2_native: EAP user "test_rad" ike V=root:0:ikev2_native: auth group radius-group ike V=root:0:ikev2_native: EAP 24730597347332 pending ... ike V=root:0:ikev2_native:89 EAP 24730597347332 result FNBAM_CHALLENGED [1098] __rad_del_job_timer- [1386] freeze_auth_session- ike V=root:0:ikev2_native: EAP challenged for user "test_rad" ike V=root:0:ikev2_native:89: responder preparing EAP pass through message ike 0:ikev2_native:89: enc 0000001A015B00160410812E67D63D7945B8A54A6049EEA98733050403020105 ike 0:ikev2_native:89: out BC5AA3BB99C0963C290CF660B0977BF52E202320000000020000006030000044669A4D0DFD7FC82E33253FD3AEB8ED5D550976ED0D67F21B71DB16A0ABEB36BC652DCC055A81D59E5A36C27E1BE94EF9135A01ED5E27E4009BBB1DEF26EC8925 ike V=root:0:ikev2_native:89: sent IKE msg (AUTH_RESPONSE): 172.16.200.4:4500->172.16.200.254:64917, len=96, vrf=0, id=bc5aa3bb99c0963c/290cf660b0977bf5:00000002, oif=7 ike V=root:0: udp comes 172.16.200.254:64917->172.16.200.4:4500,ifindex=7,vrf=0,len=84.... ike V=root:0: IKEv2 exchange=AUTH id=bc5aa3bb99c0963c/290cf660b0977bf5:00000003 len=80 ike 0: in BC5AA3BB99C0963C290CF660B0977BF52E20230800000003000000503000003439E6158679F4F96936D70706661FE643073C60362D82775DCB70395B4B3FC89F31EF9D45E142EB6BB224B76BE92F1EE3 ike 0:ikev2_native:89: dec BC5AA3BB99C0963C290CF660B0977BF52E202308000000030000002A300000040000000A025B0006031A ike V=root:0:ikev2_native:89: responder received EAP msg ike V=root:0:ikev2_native:89: send EAP message to FNBAM ike V=root:0:ikev2_native: EAP 24730597347332 pending ... [672] __group_match-Use 'test_rad' for user group matching. [710] __group_match-Check if radius-server is a group member [716] __group_match-Group 'radius-group' passed group matching [719] __group_match-Add matched group 'radius-group'(7) [276] find_matched_usr_grps-Passed group matching [1024] update_auth_token_session-config does not require 2fa [336] fnbamd_comm_send_result-Sending result 0 (nid 0) for req 24730597347332, len=2784 [668] destroy_auth_silent-delete session 24730597347332 [1938] handle_child_rsp-Auth rsp 24730597347332, session created, line 126 [1650] fnbamd_rad_stop- [1271] __rad_stop- [545] __rad_udp_close-closed. [1266] __rad_conn_stop-Stop rad conn timer. [1098] __rad_del_job_timer- ike V=root:0:ikev2_native:89 EAP 24730597347332 result FNBAM_SUCCESS ike V=root:0:ikev2_native: EAP succeeded for user "test_rad" group "radius-group" 2FA=no ike V=root:0:ikev2_native:89: responder preparing EAP pass through message ... ike V=root:0:ikev2_native:89: responder received AUTH msg ike V=root:0:ikev2_native:89: peer identifier IPV4_ADDR 172.17.249.189 ike V=root:0:ikev2_native:89: eap-peer=yes ike V=root:0:ikev2_native:89: auth verify done ike V=root:0:ikev2_native:89: responder AUTH continuation ike V=root:0:ikev2_native:89: authentication succeeded ike V=root:0:ikev2_native:89: responder creating new child ike V=root:0:ikev2_native:89: mode-cfg type 1 request 0:'' ike V=root:0:ikev2_native: mode-cfg allocate 10.130.1.1/0.0.0.0 ike V=root:0:ikev2_native:89: mode-cfg using allocated IPv4 10.130.1.1 ... ike V=root:0:ikev2_native_0: tunnel created tun_id 10.130.1.1/::10.0.0.5 remote_location 0.0.0.0 ike V=root:0:ikev2_native_0: added new dynamic tunnel for 172.16.200.254:64917 ike V=root:0:ikev2_native_0:89: established IKE SA bc5aa3bb99c0963c/290cf660b0977bf5 ike V=root:0:ikev2_native_0:89: check peer route: if_addr4_rcvd=0, if_addr6_rcvd=0, mode_cfg=1 ike V=root:0:ikev2_native_0:89: mode-cfg assigned (1) IPv4 address 10.130.1.1 ike V=root:0:ikev2_native_0:89: mode-cfg send (3) IPv4 DNS(1) 172.17.254.148 ike V=root:0:ikev2_native_0:89: mode-cfg send (3) IPv4 DNS(2) 8.8.8.8 ike V=root:0:ikev2_native_0:89: mode-cfg IPv6 DNS ignored, no IPv6 DNS servers found ike V=root:0:ikev2_native_0:89:ikev2_native:1: replay protection enabled ike V=root:0:ikev2_native_0:89:ikev2_native:1: set sa life soft seconds=43189. ike V=root:0:ikev2_native_0:89:ikev2_native:1: set sa life hard seconds=43200. ike V=root:0:ikev2_native_0:89:ikev2_native:1: IPsec SA selectors #src=1 #dst=1 ike V=root:0:ikev2_native_0:89:ikev2_native:1: src 0 7 0:0.0.0.0-255.255.255.255:0 ike V=root:0:ikev2_native_0:89:ikev2_native:1: dst 0 7 0:10.130.1.1-10.130.1.1:0 ike V=root:0:ikev2_native_0:89:ikev2_native:1: add dynamic IPsec SA selectors 483 ike V=root:0:ikev2_native_0:89:ikev2_native:1: added dynamic IPsec SA proxyids new 1 483 ike V=root:0:ikev2_native:1: add route 10.130.1.1/255.255.255.255 gw 10.130.1.1 oif ikev2_native(49) metric 15 priority 1 ike V=root:0:ikev2_native_0:89:ikev2_native:1: tunnel 1 of VDOM limit 0/0 ike V=root:0:ikev2_native_0:89:ikev2_native:1: add IPsec SA: SPIs=5c8e4a53/ec7bfcfc ike 0:ikev2_native_0:89:ikev2_native:1: IPsec SA dec spi 5c8e4a53 key 32:34420E33F9E18EEA020278FDEADFC111AA099F84E1DD2A0F25EC20FD242BFF9F auth 20:4A4F61A0A89017D5AC711BE76ADB3631B1F24BE5 ike 0:ikev2_native_0:89:ikev2_native:1: IPsec SA enc spi ec7bfcfc key 32:80A0B64BDF7E1CACA170A0641DCA00DD657629AF8913C5BAEACC209EDC4CCAC3 auth 20:EBD8BC8A2F88CD2DC8A2232FDADB7FC627694A77 ike V=root:0:ikev2_native_0:89:ikev2_native:1: added IPsec SA: SPIs=5c8e4a53/ec7bfcfc ike V=root:0:ikev2_native_0:89:ikev2_native:1: sending SNMP tunnel UP trap ike V=root:0:ikev2_native_0: tunnel up event assigned address 10.130.1.1 ...

