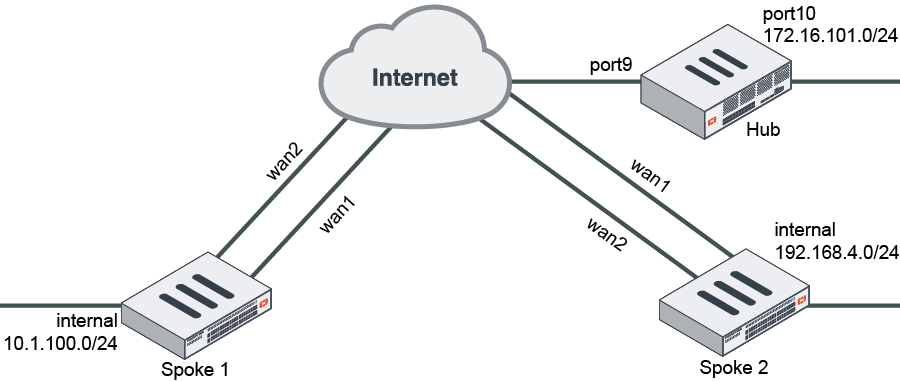
This is a sample configuration of ADVPN with BGP as the routing protocol. The following options must be enabled for this configuration:
-
On the hub FortiGate, IPsec phase1-interface
net-device disablemust be run. -
IBGP must be used between the hub and spoke FortiGates.
-
bgp neighbor-group/neighbor-rangemust be reused.
To configure ADVPN with BGP as the routing protocol using the CLI:
-
Configure hub FortiGate WAN interface, internal interface, and a static route:
config system interface edit "port9" set alias "WAN" set ip 22.1.1.1 255.255.255.0 next edit "port10" set alias "Internal" set ip 172.16.101.1 255.255.255.0 next end config router static edit 1 set gateway 22.1.1.2 set device "port9" next end -
Configure the hub FortiGate:
-
Configure the hub FortiGate IPsec phase1-interface and phase2-interface:
config vpn ipsec phase1-interface edit "advpn-hub" set type dynamic set interface "port9" set peertype any set net-device disable set proposal aes128-sha256 aes256-sha256 3des-sha256 aes128-sha1 aes256-sha1 3des-sha1 set add-route disable set dpd on-idle set auto-discovery-sender enable set psksecret sample set dpd-retryinterval 5 next end config vpn ipsec phase2-interface edit "advpn-hub" set phase1name "advpn-hub" set proposal aes128-sha1 aes256-sha1 3des-sha1 aes128-sha256 aes256-sha256 3des-sha256 next end
When
net-deviceis disabled, a tunnel ID is generated for each dynamic tunnel. This ID, in the form of an IP address, is used as the gateway in the route entry to that tunnel. Thetunnel-searchoption is removed in FortiOS 7.0.0 and later. -
Configure the hub FortiGate firewall policy:
config firewall policy edit 1 set name "spoke2hub" set srcintf "advpn-hub" set dstintf "port10" set srcaddr "all" set dstaddr "172.16.101.0" set action accept set schedule "always" set service "ALL" next edit 2 set name "spoke2spoke" set srcintf "advpn-hub" set dstintf "advpn-hub" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next end -
Configure the hub FortiGate's IPsec tunnel interface IP address:
config system interface edit "advpn-hub1" set ip 10.10.10.254 255.255.255.255 set remote-ip 10.10.10.253 255.255.255.0 next end -
Configure the hub FortiGate's BGP:
config router bgp set as 65412 config neighbor-group edit "advpn" set link-down-failover enable set remote-as 65412 set route-reflector-client enable next end config neighbor-range edit 1 set prefix 10.10.10.0 255.255.255.0 set neighbor-group "advpn" next end config network edit 1 set prefix 172.16.101.0 255.255.255.0 next end end
-
-
Configure the spoke FortiGates:
-
Configure the spoke FortiGates' WAN, internal interfaces, and static routes:
-
Configure Spoke1:
config system interface edit "wan1" set alias "primary_WAN" set ip 15.1.1.2 255.255.255.0 next edit "wan2" set alias "secondary_WAN" set ip 12.1.1.2 255.255.255.0 next edit "internal" set ip 10.1.100.1 255.255.255.0 next end config router static edit 1 set gateway 12.1.1.1 set device "wan2" set distance 15 next edit 2 set gateway 15.1.1.1 set device "wan1" next end -
Configure the Spoke2:
config system interface edit "wan1" set alias "primary_WAN" set ip 13.1.1.2 255.255.255.0 next edit "wan2" set alias "secondary_WAN" set ip 17.1.1.2 255.255.255.0 next edit "internal" set ip 192.168.4.1 255.255.255.0 next end config router static edit 1 set gateway 17.1.1.1 set device "wan2" set distance 15 next edit 2 set gateway 13.1.1.1 set device "wan1" next end
-
-
Configure the spoke FortiGates' IPsec phase1-interface and phase2-interface:
-
Configure Spoke1:
config vpn ipsec phase1-interface edit "spoke1" set interface "wan1" set peertype any set net-device enable set proposal aes128-sha256 aes256-sha256 aes128-sha1 aes256-sha1 set add-route disable set dpd on-idle set auto-discovery-receiver enable set remote-gw 22.1.1.1 set psksecret sample set dpd-retryinterval 5 next edit "spoke1_backup" set interface "wan2" set peertype any set net-device enable set proposal aes128-sha256 aes256-sha256 aes128-sha1 aes256-sha1 set add-route disable set dpd on-idle set auto-discovery-receiver enable set remote-gw 22.1.1.1 set monitor "spoke1" set psksecret sample set dpd-retryinterval 5 next end config vpn ipsec phase2-interface edit "spoke1" set phase1name "spoke1" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set auto-negotiate enable next edit "spoke1_backup" set phase1name "spoke1_backup" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set auto-negotiate enable next end -
Configure Spoke2:
config vpn ipsec phase1-interface edit "spoke2" set interface "wan1" set peertype any set net-device enable set proposal aes128-sha256 aes256-sha256 aes128-sha1 aes256-sha1 set add-route disable set dpd on-idle set auto-discovery-receiver enable set remote-gw 22.1.1.1 set psksecret sample set dpd-retryinterval 5 next edit "spoke2_backup" set interface "wan2" set peertype any set net-device enable set proposal aes128-sha256 aes256-sha256 aes128-sha1 aes256-sha1 set add-route disable set dpd on-idle set auto-discovery-receiver enable set remote-gw 22.1.1.1 set monitor "spoke2" set psksecret sample set dpd-retryinterval 5 next end config vpn ipsec phase2-interface edit "spoke2" set phase1name "spoke2" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set auto-negotiate enable next edit "spoke2_backup" set phase1name "spoke2_backup" set proposal aes128-sha1 aes256-sha1 aes128-sha256 aes256-sha256 aes128gcm aes256gcm chacha20poly1305 set auto-negotiate enable next end
-
-
Configure the spoke FortiGates' firewall policies:
-
Configure Spoke1:
config firewall policy edit 1 set name "outbound_advpn" set srcintf "internal" set dstintf "spoke1" "spoke1_backup" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next edit 2 set name "inbound_advpn" set srcintf "spoke1" "spoke1_backup" set dstintf "internal" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next end -
Configure Spoke2:
config firewall policy edit 1 set name "outbound_advpn" set srcintf "internal" set dstintf "spoke2" "spoke2_backup" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next edit 2 set name "inbound_advpn" set srcintf "spoke2" "spoke2_backup" set dstintf "internal" set srcaddr "all" set dstaddr "all" set action accept set schedule "always" set service "ALL" next end
-
-
Configure the spoke FortiGates' tunnel interface IP addresses:
-
Configure Spoke1:
config system interface edit "spoke1" set ip 10.10.10.1 255.255.255.255 set remote-ip 10.10.10.254 255.255.255.0 next edit "spoke1_backup" set ip 10.10.10.2 255.255.255.255 set remote-ip 10.10.10.254 255.255.255.0 next end -
Configure Spoke2:
config system interface edit "spoke2" set ip 10.10.10.3 255.255.255.255 set remote-ip 10.10.10.254 255.255.255.0 next edit "spoke2_backup" set ip 10.10.10.4 255.255.255.255 set remote-ip 10.10.10.254 255.255.255.0 next end
-
-
Configure the spoke FortiGates' BGP:
-
Configure Spoke1:
config router bgp set as 65412 config neighbor edit "10.10.10.254" set advertisement-interval 1 set link-down-failover enable set remote-as 65412 next end config network edit 1 set prefix 10.1.100.0 255.255.255.0 next end end -
Configure Spoke2:
config router bgp set as 65412 config neighbor edit "10.10.10.254" set advertisement-interval 1 set link-down-failover enable set remote-as 65412 next end config network edit 1 set prefix 192.168.4.0 255.255.255.0 next end end
-
-
-
Run
diagnoseandgetcommands on Spoke1 to check VPN and BGP states:-
Run the
diagnose vpn tunnel listcommand on Spoke1. The system should return the following:list all ipsec tunnel in vd 0 ---- name=spoke1 ver=1 serial=2 15.1.1.2:0->22.1.1.1:0 tun_id=22.1.1.1 bound_if=7 lgwy=static/1 tun=intf/0 mode=auto/1 encap=none/536 options[0218]=npu create_dev frag-rfc accept_traffic=1 proxyid_num=1 child_num=1 refcnt=19 ilast=1 olast=1 ad=r/2 stat: rxp=1 txp=160 rxb=16428 txb=8969 dpd: mode=on-idle on=1 idle=5000ms retry=3 count=0 seqno=628 natt: mode=none draft=0 interval=0 remote_port=0 proxyid=spoke1 proto=0 sa=1 ref=6 serial=1 auto-negotiate adr src: 0:0.0.0.0/0.0.0.0:0 dst: 0:0.0.0.0/0.0.0.0:0 SA: ref=6 options=1a227 type=00 soft=0 mtu=1438 expire=1225/0B replaywin=1024 seqno=a1 esn=0 replaywin_lastseq=00000002 itn=0 life: type=01 bytes=0/0 timeout=2369/2400 dec: spi=c53a8f5b esp=aes key=16 cbe88682ad896a69290027b6dd8f7162 ah=sha1 key=20 7bb704b388f83783ac76c2ab0b6c9f7dcf78e93b enc: spi=6e3633fc esp=aes key=16 1a0da3f4deed3d16becc9dda57537355 ah=sha1 key=20 368544044bd9b82592d72476ff93d5055056da8d dec:pkts/bytes=1/16364, enc:pkts/bytes=160/19168 npu_flag=03 npu_rgwy=22.1.1.1 npu_lgwy=15.1.1.2 npu_selid=1 dec_npuid=1 enc_npuid=1 ---- name=spoke1_backup ver=1 serial=1 12.1.1.2:0->22.1.1.1:0 tun_id=22.1.1.1 bound_if=6 lgwy=static/1 tun=intf/0 mode=auto/1 encap=none/536 options[0218]=npu create_dev frag-rfc accept_traffic=0 proxyid_num=1 child_num=0 refcnt=11 ilast=0 olast=0 ad=/0 stat: rxp=0 txp=0 rxb=0 txb=0 dpd: mode=on-idle on=0 idle=5000ms retry=3 count=0 seqno=0 natt: mode=none draft=0 interval=0 remote_port=0 proxyid=spoke1_backup proto=0 sa=0 ref=2 serial=1 auto-negotiate adr src: 0:0.0.0.0/0.0.0.0:0 dst: 0:0.0.0.0/0.0.0.0:0 -
Run the
get router info bgp summarycommand on Spoke1. The system should return the following:BGP router identifier 7.7.7.7, local AS number 65412 BGP table version is 2 1 BGP AS-PATH entries 0 BGP community entries Neighbor V AS [[QualityAssurance62/MsgRcvd]] [[QualityAssurance62/MsgSent]] [[QualityAssurance62/TblVer]] InQ OutQ Up/Down State/PfxRcd 10.10.10.254 1. 65412 143 142 1. 1. 1. 00:24:45 2 Total number of neighbors 1
-
Run the
get router info routing-table bgpcommand on Spoke1. The system should return the following:Routing table for VRF=0 B 172.16.101.0/24 [200/0] via 10.10.10.254, spoke1, 00:23:57 B 192.168.4.0/24 [200/0] via 10.10.10.254, spoke1, 00:22:03
-
Generate traffic between the spokes and check the shortcut tunnel and routing table. Run the
diagnose vpn tunnel listcommand on Spoke1. The system should return the following:list all ipsec tunnel in vd 0 ---- name=spoke1 ver=1 serial=2 15.1.1.2:0->22.1.1.1:0 tun_id=22.1.1.1 bound_if=7 lgwy=static/1 tun=intf/0 mode=auto/1 encap=none/536 options[0218]=npu create_dev frag-rfc accept_traffic=1 proxyid_num=1 child_num=1 refcnt=19 ilast=2 olast=2 ad=r/2 stat: rxp=1 txp=268 rxb=16428 txb=31243 dpd: mode=on-idle on=1 idle=5000ms retry=3 count=0 seqno=714 natt: mode=none draft=0 interval=0 remote_port=0 proxyid=spoke1 proto=0 sa=1 ref=6 serial=1 auto-negotiate adr src: 0:0.0.0.0/0.0.0.0:0 dst: 0:0.0.0.0/0.0.0.0:0 SA: ref=6 options=1a227 type=00 soft=0 mtu=1438 expire=345/0B replaywin=1024 seqno=10d esn=0 replaywin_lastseq=00000002 itn=0 life: type=01 bytes=0/0 timeout=2369/2400 dec: spi=c53a8f5b esp=aes key=16 cbe88682ad896a69290027b6dd8f7162 ah=sha1 key=20 7bb704b388f83783ac76c2ab0b6c9f7dcf78e93b enc: spi=6e3633fc esp=aes key=16 1a0da3f4deed3d16becc9dda57537355 ah=sha1 key=20 368544044bd9b82592d72476ff93d5055056da8d dec:pkts/bytes=1/16364, enc:pkts/bytes=268/48320 npu_flag=03 npu_rgwy=22.1.1.1 npu_lgwy=15.1.1.2 npu_selid=1 dec_npuid=1 enc_npuid=1 ---- name=spoke1_backup ver=1 serial=1 12.1.1.2:0->22.1.1.1:0 tun_id=22.1.1.1 bound_if=6 lgwy=static/1 tun=intf/0 mode=auto/1 encap=none/536 options[0218]=npu create_dev frag-rfc accept_traffic=0 proxyid_num=1 child_num=0 refcnt=11 ilast=8 olast=8 ad=/0 stat: rxp=0 txp=0 rxb=0 txb=0 dpd: mode=on-idle on=0 idle=5000ms retry=3 count=0 seqno=0 natt: mode=none draft=0 interval=0 remote_port=0 proxyid=spoke1_backup proto=0 sa=0 ref=2 serial=1 auto-negotiate adr src: 0:0.0.0.0/0.0.0.0:0 dst: 0:0.0.0.0/0.0.0.0:0 ---- name=spoke1_0 ver=1 serial=9 15.1.1.2:4500->13.1.1.2:4500 tun_id=13.1.1.2 bound_if=7 lgwy=static/1 tun=intf/0 mode=dial_inst/3 encap=none/728 options[02d8]=npu create_dev no-sysctl rgwy-chg frag-rfc accept_traffic=1 parent=spoke1 index=0 proxyid_num=1 child_num=0 refcnt=17 ilast=4 olast=4 ad=r/2 stat: rxp=1 txp=100 rxb=112 txb=4686 dpd: mode=on-idle on=1 idle=5000ms retry=3 count=0 seqno=231 natt: mode=keepalive draft=32 interval=10 remote_port=4500 proxyid=spoke1 proto=0 sa=1 ref=5 serial=1 auto-negotiate adr src: 0:0.0.0.0/0.0.0.0:0 dst: 0:0.0.0.0/0.0.0.0:0 SA: ref=6 options=1a227 type=00 soft=0 mtu=1422 expire=447/0B replaywin=1024 seqno=65 esn=0 replaywin_lastseq=00000002 itn=0 life: type=01 bytes=0/0 timeout=2368/2400 dec: spi=c53a8f5c esp=aes key=16 73fd9869547475db78851e6c057ad9b7 ah=sha1 key=20 6ad3a5b1028f6b33c82ba494a370f13c7f462635 enc: spi=79cb0f2b esp=aes key=16 52ab0acdc830d58c00e5956a6484654a ah=sha1 key=20 baa82aba4106dc60618f6fe95570728656799239 dec:pkts/bytes=1/46, enc:pkts/bytes=100/11568 npu_flag=03 npu_rgwy=13.1.1.2 npu_lgwy=15.1.1.2 npu_selid=5 dec_npuid=1 enc_npuid=1 -
Run the
get router info routing-tale bgpcommand. The system should return the following:Routing table for VRF=0 B 172.16.101.0/24 [200/0] via 10.10.10.254, spoke1, 00:23:57 B 192.168.4.0/24 [200/0] via 10.10.10.3, spoke1_0 , 00:22:03
-

