IP address threat feed
An IP address threat feed is a dynamic list that contains IPv4 and IPv6 addresses, address ranges, and subnets. The list is periodically updated from an external server and stored in text file format on an external server. After the FortiGate imports this list, it can be used as a source or destination in firewall policies, proxy policies, and ZTNA rules. It can also be used as an external IP block list in DNS filter profiles.
Text file example:
192.168.2.100 172.200.1.4/16 172.16.1.2/24 172.16.8.1-172.16.8.100 2001:0db8::eade:27ff:fe04:9a01/120 2001:0db8::eade:27ff:fe04:aa01-2001:0db8::eade:27ff:fe04:ab01
The file contains one IPv4 or IPv6 address, address range, or subnet per line. See External resources file format for more information about the IP list formatting style.
Example configuration
In this example, a list of destination IP addresses is imported using the IP address threat feed. The newly created threat feed is then used as a destination in a firewall policy with the action set to deny. Any traffic that passes through the FortiGate and matches the defined firewall policy will be dropped.
|
|
Please note that the URI provided in the example is solely for demonstration purposes and does not represent a reliable list of well-maintained IP addresses. It is recommended that you utilize a URI of a reputable external IP list that is regularly updated. |
To configure an IP address threat feed in the GUI:
- Go to Security Fabric > External Connectors and click Create New.
- In the Threat Feeds section, click IP Address.
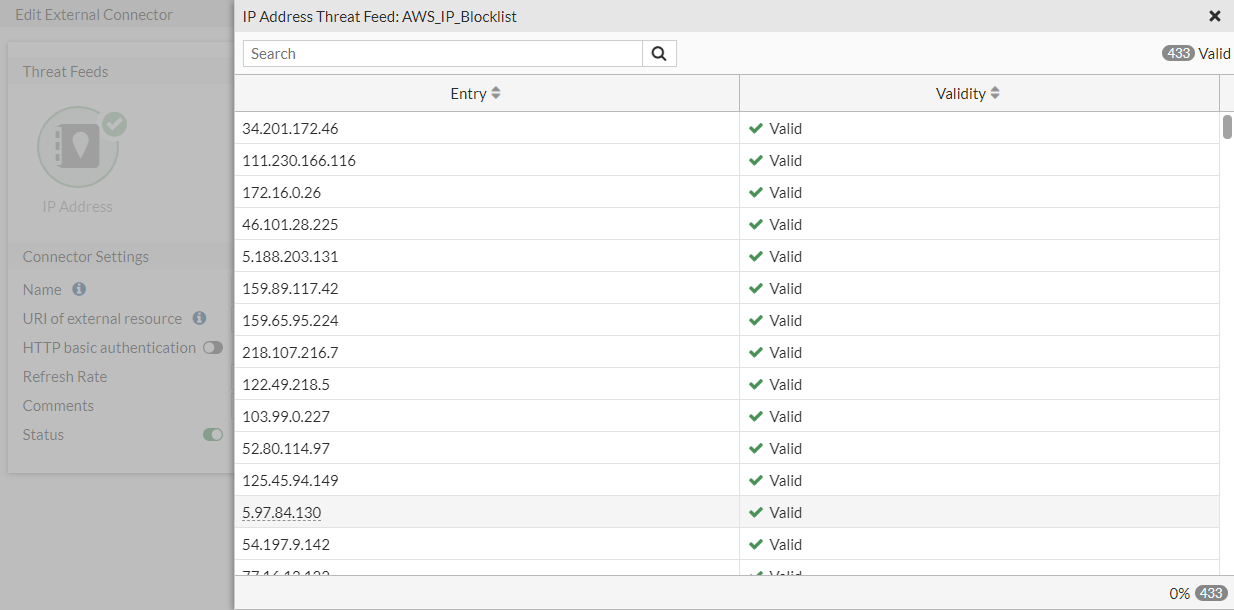
- Set the Name to AWS_IP_Blocklist.
- Set the URI of external resource to https://blocklist-example.com/ip-blocklist/ip.txt.
- Configure the remaining settings as required, then click OK.
- Edit the connector, then click View Entries to view the IP addresses in the feed.
To configure an IP address threat feed in the CLI:
config system external-resource
edit "AWS_IP_Blocklist"
set type address
set resource "https://blocklist-example.com/ip-blocklist/ip.txt"
set server-identity-check {none | basic | full}
next
end
|
|
To improve the security of the connection, it is recommended to enable server certificate validation ( |
To apply an IP address threat feed in a firewall policy:
-
Go to Policy & Objects > Firewall Policy and create a new policy, or edit an existing one.
-
Configure the policy fields as required.
-
In the Destination field, click the + and select AWS_IP_Blocklist from the list (in the IP ADDRESS FEED section).
-
Set Action to DENY.
-
Enable Log Allowed Traffic.
-
Click OK.
Applying an IP address threat feed as an external IP block list in a DNS filter profile
An IP address threat feed can be applied by enabling External IP Block Lists in a DNS filter profile. Any DNS query that passes through the FortiGate and resolves to any of the IP addresses in the threat feed list will be dropped.
To configure the DNS filter profile:
-
Go to Security Profiles > DNS Filter and create a new profile, or edit an existing one.
- Enable External IP Block Lists.
- Click the + and select AWS_IP_Blocklist from the list.
-
Click OK.
To apply the DNS filter profile in a firewall policy:
-
Go to Policy & Objects > Firewall Policy and create a new policy, or edit an existing one.
-
Configure the policy fields as required.
-
Under Security Profiles, enable DNS Filter and select the profile used in the previous procedure.
-
Enable Log Allowed Traffic.
-
Click OK.
IP addresses that match the IP address threat feed list will be blocked.
To view the DNS query logs:
-
Go to Log & Report > DNS Query.
-
View the log details in the GUI, or download the log file:
1: date=2023-02-06 time=15:06:50 eventtime=1675724810452621179 tz="-0800" logid="1501054400" type="utm" subtype="dns" eventtype="dns-response" level="warning" vd="root" policyid=0 sessionid=555999 srcip=172.20.120.13 srcport=59602 srccountry="Reserved" srcintf="port2" srcintfrole="undefined" dstip=172.20.120.12 dstport=53 dstcountry="Reserved" dstintf="root" dstintfrole="undefined" proto=17 profile="default" xid=24532 qname="dns.google" qtype="A" qtypeval=1 qclass="IN" ipaddr="208.91.112.55" msg="Domain was blocked because it is in the domain-filter list" action="redirect" domainfilteridx=0 domainfilterlist="AWS_IP_Block_list"

