Azure Kubernetes (AKS) SDN connector using client secret
Azure SDN connectors support dynamic address groups based on Azure Kubernetes (AKS) filters.
To enable an Azure SDN connector to fetch IP addresses from Azure Kubernetes:
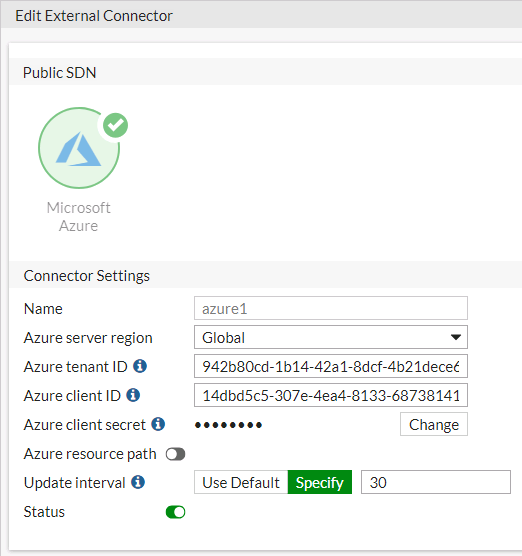
- Configure the Azure SDN connector:
- Go to Security Fabric > External Connectors.
- Click Create New, and select Azure.
- Configure as shown substituting the region, tenant and client IDs, and client secret for your deployment. See Azure SDN connector service principal configuration requirements.
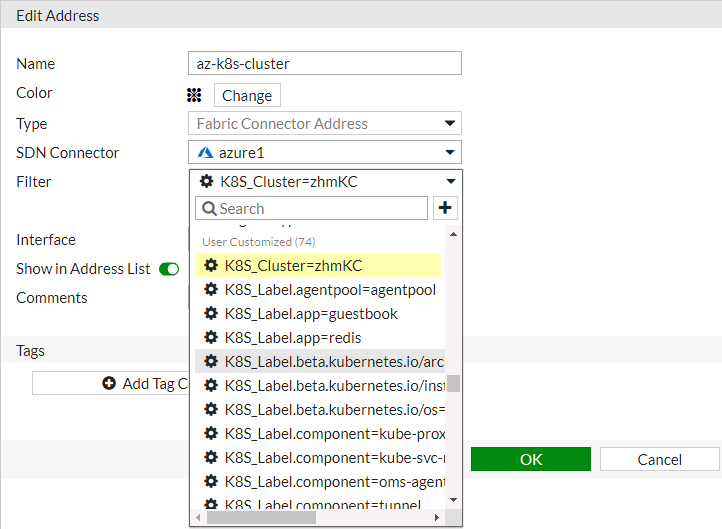
- Create a dynamic firewall address for the configured K8s SDN connector:
- Go to Policy & Objects > Addresses.
- Click Create New, then select Address.
- From the Type dropdown list, select Dynamic.
- From the Sub Type dropdown list, select Fabric Connector Address.
- From the SDN Connector dropdown list, select the desired SDN connector.
- In the Filter field, add the desired filter. The following filters are supported:
Filter
Description
k8s_cluster
Name of Kubernetes cluster.
k8s_namespace
Namespace of a Kubernetes service or pod.
k8s_svcname
Name of a Kubernetes service.
k8s_nodename
Name of a Kubernetes node.
k8s_zone
Zone of a Kubernetes node.
k8s_region
Region of a Kubernetes node.
k8s_podname
Name of a Kubernetes pod.
k8s_label.xxx
Name of label of a Kubernetes resource (cluster/service/node/pod).
In this example, the address is configured to automatically populate and update IP addresses only for instances that belong to the zhmKC cluster:
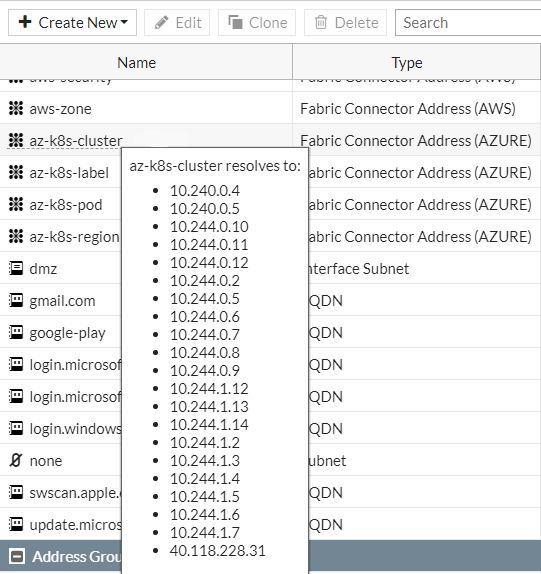
- Ensure that the K8s SDN connector resolves dynamic firewall IP addresses:
- Go to Policy & Objects > Addresses.
- Hover over the address created in step 2 to see a list of IP addresses for instances that belong to the zhmKC cluster as configured in step 2:
To configure an Azure Kubernetes SDN connector through the CLI:
- Configure the SDN connector:
config system sdn-connector
edit "azure1"
set type azure
set tenant-id "942b80cd-1b14-42a1-8dcf-4b21dece61ba"
set client-id "14dbd5c5-307e-4ea4-8133-68738141feb1"
set client-secret xxxxx
set update-interval 30
next
end
- Create a dynamic firewall address for the SDN connector with a supported Kubernetes filter. In this example, the address will automatically populate and update IP addresses only for instances that belong to the zhmKC cluster:
config firewall address
edit "az-k8s-cluster"
set type dynamic
set sdn "azure1"
set filter "K8S_Cluster=zhmKC"
next
end
-
Confirm that the Azure SDN connector resolves dynamic firewall IP addresses using the configured filter:
config firewall address
edit "az-k8s-cluster"
set type dynamic
set sdn "azure1"
set filter "K8S_Cluster=zhmKC"
config list
edit "10.240.0.4"
next
edit "10.240.0.5"
next
edit "10.244.0.10"
next
end
next
end

