Encrypted Attack
Encrypted attacks are detected by analyzing JA3 hashes in TLS transactions. FortiNDR uses both JA3 client and server SSL fingerprints in detection, resulting in fewer false positive detections.
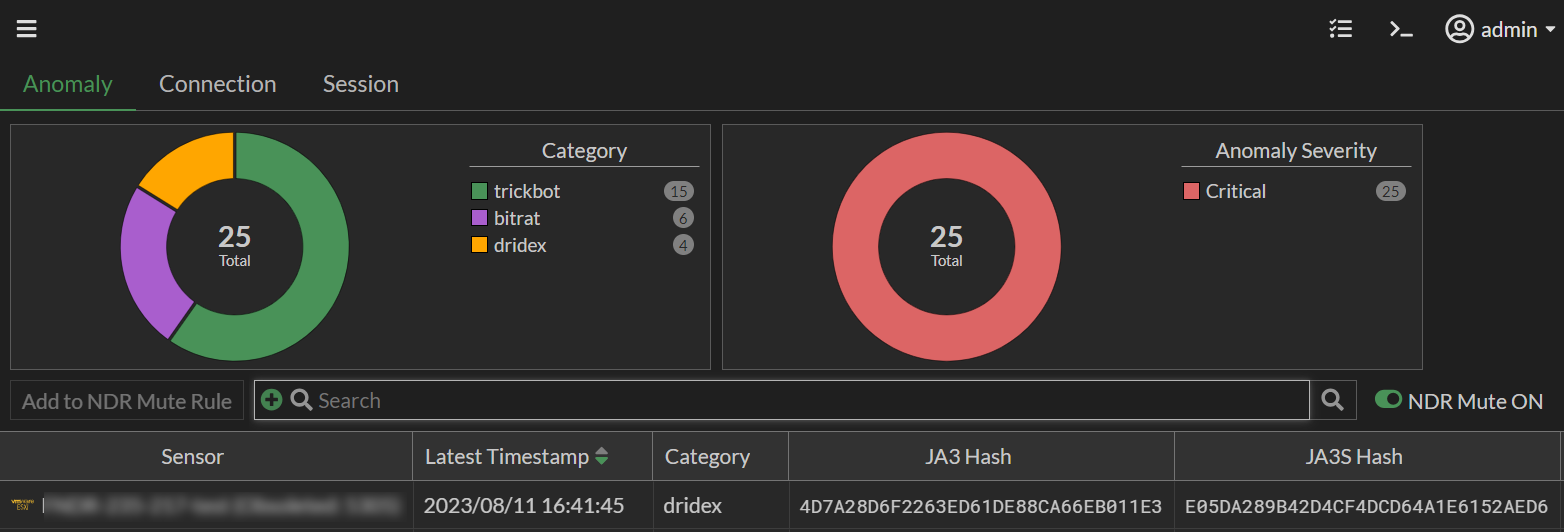
The Encrypted Attack monitor displays the following information:
| Column | Description |
|---|---|
|
Latest Timestamp |
The date the record was updated. |
|
Category |
The device category (Unknown, Home & Office, Mobile and Network). |
|
JA3 Hash |
The JA3 Client. |
|
JA3S Hash |
The JA3 Client. S indicates Severe. |
|
Anomaly Severity |
The anomaly severity (Not Anomaly, Info, Low, Medium, High or Critical). |
|
Count (Historic) |
The total number of times the anomaly was observed. |
|
Count (Past week) |
The total number of times the anomaly was observed during the past week . |
|
First Timestamp |
The timestamp for the first time the anomaly was detected. |
|
|
For information about muting rules, see NDR Muting. |

