Vulnerability Scan
The Vulnerability Scan module integrates FortiDAST's web vulnerability scanner (WVS) to help identify OWASP Top 10 vulnerabilities in web applications and provides a detailed report with remediation recommendations to enhance security.
By default, the Vulnerability Scan report reflects your current WAF configuration, highlighting vulnerabilities that remain exposed to attackers. This helps you fine-tune WAF settings to improve security.
Bypass WAF
To view vulnerabilities as if WAF protection were disabled, enable the Bypass WAF option at the top-right corner of the Vulnerability Scan page.
To scan the asset without enabling Bypass WAF, make sure the action for the following modules is not set to Period Block.
-
Known Bot
-
Threshold-Based Detection
-
ML Bot Detection
-
Bot Deception
-
DDoS Prevention
Additionally, ensure that the following limits in DDoS Prevention are not set below 100:
-
HTTP Request Limit
-
TCP Connection Number Limit
-
HTTP Request Rate Limit
To add applications for vulnerability Scan:
- Navigate to Vulnerability Scan.
- Click Create New.
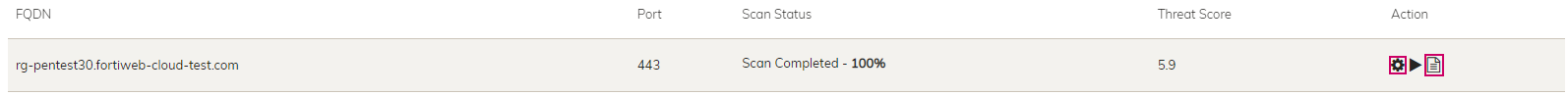
- In Add Asset window, select the FQDN and Port. These are the domain names and port numbers you have defined in Network > Endpoints.
- Click OK.
The maximum number of applications allowed are defined in your contracts. Check your contract information in General > Contracts .
To configure and view the vulnerability report:
Click the Settings button to configure scanning settings and the Reports button to view the reports. For more information, check FortiDAST User Guide: https://docs.fortinet.com/product/FortiDAST
To configure your Vulnerability Scan subscription from a public cloud marketplace:
Go to WAF > System settings > Contracts.
Billing
The billing cycle for Vulnerability Scan occurs monthly, and you will be charged on the date you initially add an application and subsequently on the same date each month. For instance, if you add an application on May 1st, your next billing date will be June 1st. If you happen to remove the application on May 15th and then re-add it on May 20th, you will be charged once at the time of re-adding the application. Following this, your next billing date will be on June 20th.
Please note that Vulnerability Scan seats are nontransferable. Removing applications does not open a seat in your contract that can be replaced with a different application.

