Configuring a Fingerprint Based Detection policy
Fingerprint Based Detection detects the client's fingerprint using multiple characteristics to ascertain whether an access request originates from a human or a bot. Using the Fingerprint Based Detection policy, FortiADC collects and monitors the behavioral fingerprint information, such as WebDriver, WindowsProperties and MimeTypesConsistent, with JavaScript enabled on the client browser. The collected information forms the client fingerprint that is then checked against known automation tools and frameworks to determine whether the requests are generated by automation tools such as Headless Chrome, Selenium or Electron.
After you have configured Fingerprint Based Detection policies, you can select them in WAF profiles.
Before you begin:
- You must have Read-Write permission for Security settings.
To configure a Fingerprint Based Detection policy:
- Go to Web Application Firewall > Fingerprint Based Detection.
- In the Fingerprint Based Detection tab, click Create New to display the configuration editor.
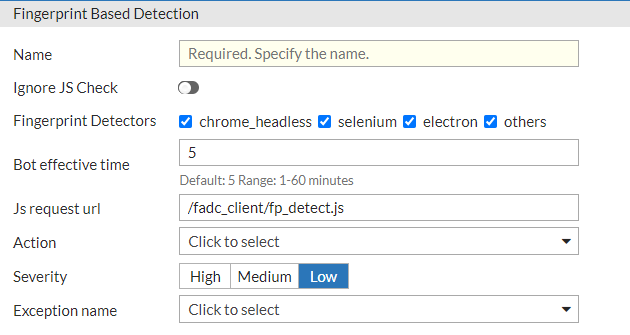
- Configure the following Fingerprint Based Detection settings:
Setting
Description
Name Specify a name for the Fingerprint Based Detection rule. Valid characters are
A-Z,a-z,0-9,_, and-. No spaces.The configuration name cannot be edited once it has been saved.
Ignore JS Check Enable/disable redirect to a warning page to enable JavaScript. This is disabled by default.
- Disable — FortiADC will check if JavaScript is enabled on the client browser. If JavaScript is not enabled, then FortiADC will redirect to a warning page to let the user enable JavaScript. If the client does not enable JavaScript, Fingerprint Based Detection cannot be activated.
- Enable — FortiADC will not check if JavaScript is enabled on the client browser. If JavaScript is enabled on the client browser, behavioral fingerprint information can be collected normally and FortiADC can determine if it is a bot or not. But if JavaScript is disabled on the client browser, Fingerprint Based Detection cannot be activated.
Fingerprint Detectors Select one or more fingerprint detectors:
- chrome_headless — Headless Chrome
- selenium — Selenium
- electron — Electron
- others — includes SlimerJS and CefSharp
All fingerprint detectors are preselected by default. If the configuration is saved with no Fingerprint Detectors selected, it will default to the preselected.
Bot Effective Time Specify the time interval before FortiADC tests and verifies a bot again, once a bot has been detected. Default: 5 Range: 1-60 minute(s). JS Request URL Specify the URL to use to insert JavaScript code to the client browser. Default: /fadc_client/fp_detect.js.Action Specify a WAF action object to apply when a bot is detected. See Configuring WAF Action objects.
The default action is alert.
Severity
Select the event severity to log when a bot is detected:
- High — Log as high severity events.
- Medium — Log as a medium severity events.
- Low — Log as low severity events.
The default is Low.
Exception Name
Select an exception configuration object. Exceptions identify specific hosts or URL patterns that are not subject to processing by this rule.
- Click Save.
Once the configuration is saved, the URL List becomes configurable. The Fingerprint Based Detection policy will be applied to the request URLs in the URL List. - Under the URL List section, click Create New to display the configuration editor.
- Configure the following URL List settings:
Setting
Description
Host Status If enabled, require authorization only for the specified host. If disabled, ignore hostname in the HTTP request header and require authorization for requests with any Host header. Disabled by default. Host The Host option is available if Host Status is enabled.
Specify the HTTP Host header. If Host Status is enabled, the policy matches only if the Host header matches this value. Complete, exact matching is required. For example,
www.example.commatcheswww.example.combut notwww.example.com.hk.Request URL The literal URL, such as
/index.php, or a regular expression, such as^/*.phpthat the HTTP request must contain in order to match the rule. Multiple URLs are supported. - Click Save.
Once the URL List configuration is saved, you are returned to the Fingerprint Based Detection configuration editor. - Click Save again to apply the newly created URL List configuration to the Fingerprint Based Detection configuration.
Once the Fingerprint Based Detection policy is saved, you can apply it to the WAF profile.

