Overview
FortiNDR Cloud is a cloud-native network detection and response solution built for the rapid detection of threat activity, investigation of suspicious behavior, proactive hunting for potential risks, and directing a fast and effective response to active threats.
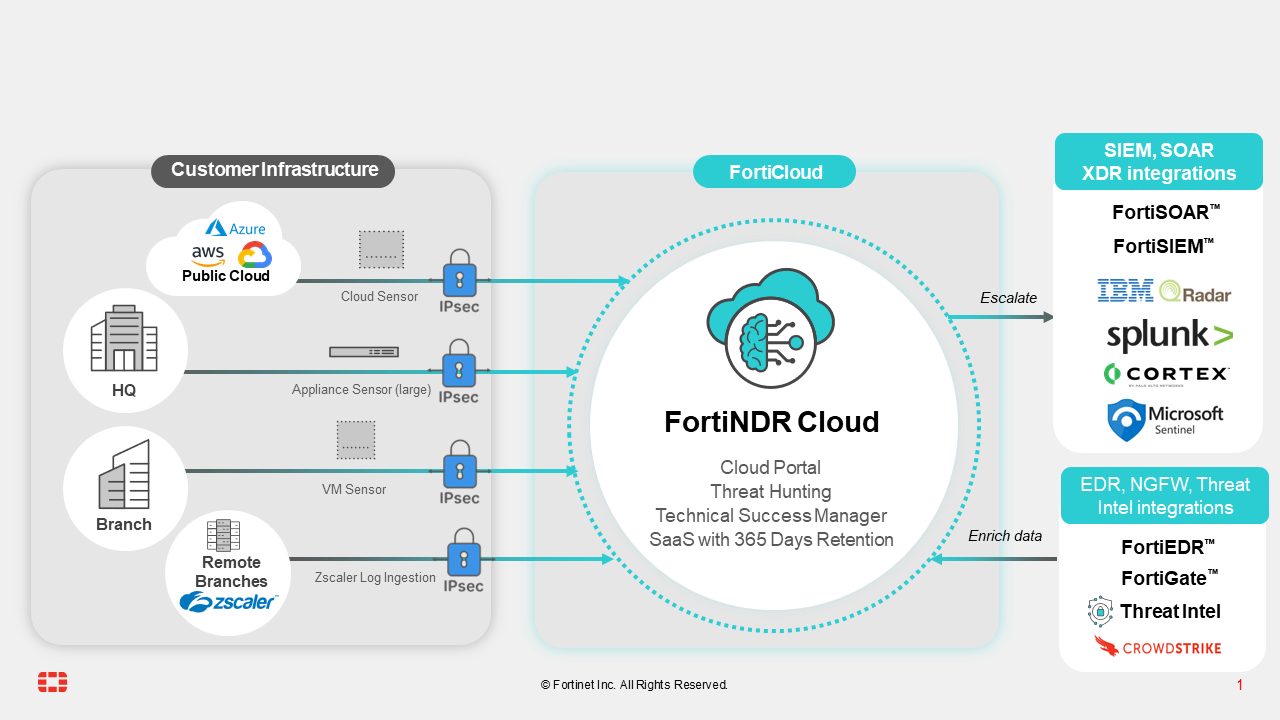
The following diagram illustrates the components and benefits of the solution at a high level:
Key notes relating to architecture and securing customer data:
- Data from customer and/or public cloud sensors encrypts network meta data collected to SaaS solution with strong IPSEC encryption. This encryption is end-to-end to ensure customer network metadata is not compromised (data in transit).
-
Network data from customers is encrypted at rest in FortiNDR Cloud.
- Customers will have a portal which enable access to illustrate detection, conduct investigations, and threat hunting.
- Third-party integrations such as EDR, NGFW, SIEM and SOAR products are enabled via APIs available from FortiNDR Cloud.
- FortiNDR Cloud data are enriched with different threat and network feeds to make data useful to comprehend.
- Network metadata collected do not contain PCAPS (despite it being possible to collect PCAPS on sensors for forensic analysis), please see further chapters on enabling PCAPs
- Fortinet data security and privacy practices are documented here: Data Privacy Practices

