About the connector
Fortinet FortiSIEM is a highly scalable multi-tenant Security Information and Event Management (SIEM) solution that provides real-time infrastructure and user awareness for accurate threat detection, analysis, and reporting.
This document provides information about the Fortinet FortiSIEM Connector, which facilitates automated interactions with your Fortinet FortiSIEM server using FortiSOAR™ playbooks. Add the Fortinet FortiSIEM Connector, as a step in FortiSOAR™ playbooks and perform automated operations such as retrieving device information for all devices configured on the Fortinet FortiSIEM server and retrieving a list of monitored organizations from the Fortinet FortiSIEM server.
You can use FortiSOAR™'s Data Ingestion Wizard to easily ingest data into FortiSOAR™ by pulling incidents from Fortinet FortiSIEM.
For more information, see the Data Ingestion Support section.
For a list of recommendations and suggested best practices for working with the FortiSOAR FortiSIEM integration, see the Best Practices - Working with FortiSOAR FortiSIEM Integration section.
FortiSIEM 6.7.6 release contained some API changes that led to updates in connector actions. For details see the Fortinet FortiSIEM v5.1.0 connector document.
Version information
Connector Version: 5.2.0
FortiSOAR™ Version Tested on: 7.4.3-3294
Fortinet FortiSIEM Version Tested on: 7.1.0
Authored By: Fortinet
Certified: Yes
Release Notes for version 5.2.0
Following enhancements have been made to the Fortinet FortiSIEM Connector in version 5.2.0:
- Added the following actions:
- Get IP Context
- Get Host Context
- Get User Context
- Deprecated the following actions:
- Get All Resource Lists
- Get Resource List Entries
- Add Entries To Resource List
- Remove Entries From Resource List
- Updated output schema for following actions:
- List Incidents
- Get Incident Details
Important Notes related to this release of the connector
- Only FortiSIEM v7.1.0 and later are supported by this connector version.
- The FortiSIEM API no longer supports filtering incidents based on sub-categories in the List Incidents action.
- The Time From and Time To parameters in the Get Events For Incident action are supported only in the FortiSIEM v6.7.6.
Installing the connector
Use the Content Hub to install the connector. For the detailed procedure to install a connector, click here.
You can also use the following yum command as a root user to install connectors from an SSH session:
yum install cyops-connector-fortinet-fortisiem
Prerequisites to configuring the connector
- You must have the URL of a Fortinet FortiSIEM server to which you will connect and perform automated operations and the credentials, such as the username and password, to access that server.
- The FortiSOAR™ server should have outbound connectivity to port 443 on the Fortinet FortiSIEM server.
Minimum Permissions Required
- The minimum privileges that require to be assigned to users who are going to use this connector and run actions on FortiSIEM are Read and Update access on Incidents and access to Run Advanced Search Query.
Configuring the connector
For the procedure to configure a connector, click here.
Configuration parameters
In FortiSOAR™, on the Content Hub (or Connector Store) page, click the Manage tab, and then click the Fortinet FortiSIEM connector card. On the connector popup, click the Configurations tab to enter the required configuration details:
| Parameter |
Description |
| Server URL |
Specify the URL of the Fortinet FortiSIEM server to which you will connect and perform the automated operations. |
| Username |
Specify the username used to access the Fortinet FortiSIEM server to which you will connect and perform the automated operations. |
| Password |
Specify the password used to access the Fortinet FortiSIEM server to which you will connect and perform the automated operations. |
| Organization |
Specify the name of the organization that you will access on the Fortinet FortiSIEM server to perform the automated operations. |
| Verify SSL |
Specifies whether the SSL certificate for the server is to be verified or not.
By default, this option is set as True. |
Actions supported by the connector
The following automated operations can be included in playbooks, and you can also use the annotations to access operations from FortiSOAR™:
| Function |
Description |
Annotation and Category |
| Get All Devices |
Retrieves a short description for all devices that are configured on the Fortinet FortiSIEM server. |
get_devices
Investigation |
| Get All Devices For Specified IP Address Range |
Retrieves a short description for devices that are configured on the Fortinet FortiSIEM server, based on the IP address range that you have specified. |
get_devices
Investigation |
| Get Device Information |
Retrieves details of a specific device that is configured on the Fortinet FortiSIEM server, based on the Device IP that you have specified. |
get_devices
Investigation |
| List Monitored Devices and Attributes |
Retrieves a list and attributes of all monitored devices that are configured on the Fortinet FortiSIEM server. |
get_devices
Investigation |
| List Monitored Organizations |
Retrieves a list and details of all monitored organizations that are configured on the Fortinet FortiSIEM server. |
get_domains
Investigation |
| Get Organization Details |
Retrieves the details of a specific organization from the Fortinet FortiSIEM server based on the organization ID that you have specified. |
get_organization
Investigation |
| List Incidents |
Retrieves a list and details of incidents from the Fortinet FortiSIEM server based on the time range, and other filter criteria you have specified.
NOTE: The FortiSIEM API does not support filtering incidents in the "List Incident" action based on sub-categories. |
get_incidents
Investigation |
| Get Incident Details |
Retrieves details of an incident from the Fortinet FortiSIEM server based on the incident IDs you have specified. |
get_incident_details
Investigation |
| Comment Incident |
Adds a comment to a specific incident on the Fortinet FortiSIEM server based on the incident ID you have specified. |
incident_comment
Investigation |
| Clear Incident With Reason |
Clears an incident with the reason you have specified on the Fortinet FortiSIEM server based on the incident ID you have specified. |
clear_incident
Investigation |
| Get Events For Incident |
Retrieves all associated events for a specified incident from the Fortinet FortiSIEM server, based on the incident ID and other input parameters you have specified. |
get_associated_events
Investigation |
| Run Advanced Search Query |
Runs an advanced search query on the Fortinet FortiSIEM server, based on the search conditions and other input parameters you have specified. |
run_report
Investigation |
| Update Incident |
Updates the attributes of a specific incident on the Fortinet FortiSIEM server based on the incident ID and other input parameters you have specified. |
update_incident
Investigation |
| Get Event Details |
Retrieves details of a specific event from the Fortinet FortiSIEM server based on the event ID you have specified and optionally the date range you have specified. |
get_event_details
Investigation |
| Search Events |
Searches for events in the Fortinet FortiSIEM server based on search attributes and other input parameters you have specified. |
search_events
Investigation |
| Get Event Attributes |
Retrieves all event attributes from the Fortinet FortiSIEM server. |
get_incident_attributes
Investigation |
| Get Events Data By Query ID |
Retrieves data for events or incidents from the Fortinet FortiSIEM server based on the executed query ID you have specified. |
get_events_by_query_id
Investigation |
| Get Watch Lists |
Retrieves details for all watch lists or for specific watch lists based on input parameters you have specified. |
get_watch_lists
Investigation |
| Get Watch List Entries Count |
Returns the count of all watch list entries from all watch lists in Fortinet FortiSIEM. |
get_watch_list_entries_count
Investigation |
| Get Watch List Entry |
Retrieves the specific watch list entry from Fortinet FortiSIEM based on the watch list entry ID you have specified. |
get_watch_list_entry
Investigation |
| Add Watch List Entries To Watch List |
Adds watch list entries to one or more watch lists based on watch list ID and other input parameters you have specified. |
update_watch_list_group
Investigation |
| Create Watch List |
Creates a watch list in the FortiSIEM database. A watch list can contain one or more watch list entries. |
create_watch_list_group
Investigation |
| Update Watch List Entry |
Updates a watch list entry in the FortiSIEM database based on the watch list entry ID and other input parameters you have provided. |
update_watch_list_entry
Investigation |
| Delete Watch List Entry |
Deletes watch list entries from the FortiSIEM database based on the ID of the watch list entries you have specified. |
delete_watch_list_entry
Investigation |
| Delete Watch List |
Deletes watch lists from the FortiSIEM database based on the ID of the watch lists you have specified. |
delete_watch_list
Investigation |
| Create Lookup Table |
Creates the definition of a lookup table in the FortiSIEM server based on the name, column list, and other input parameters you have specified. |
create_lookup_table
Investigation |
| Get All Lookup Table |
Retrieves the list of all lookupTable definitions from the FortiSIEM server based on the input parameters you have specified. |
get_all_lookup_tables
Investigation |
| Delete Lookup Table |
Deletes the lookupTable definition from the FortiSIEM server based on the lookup table ID you have specified. |
delete_lookup_table
Investigation |
| Import Lookup Table Data |
Imports the data of a specific CSV file in FortiSOAR to a specific lookup table in FortiSIEM based on the File/Attachment IRI, lookup table ID, and other input parameters you have specified. |
import_lookup_table_data
Investigation |
| Check Import Task Status |
Checks the status of the import lookup table data task in FortiSIEM based on the lookup table ID and task ID you have specified. |
check_import_task_status
Investigation |
| Get Lookup Table Data |
Retrieves items of the specified lookup table from FortiSIEM based on the lookup table ID and other input parameters you have specified. |
get_lookup_table_data
Investigation |
| Update Lookup Table Data |
Updates items of a specified lookup table based on the lookup table ID, key, column data, and other input parameters you have specified. |
update_lookup_table_data
Investigation |
| Delete Lookup Table Data |
Delete items of the specified lookup table in FortiSIEM based on the lookup table ID and primary keys you have specified. |
delete_lookup_table_data
Investigation |
| Get IP Context |
Retrieves the contextual data of the specified IP such as hostname, device type, location, device properties and known device information. |
get_ip_context
Investigation |
| Get Host Context |
Retrieves the contextual data of the specified hostname such as device type, and domain lookup information if an FQDN is supplied. |
get_host_context
Investigation |
| Get User Context |
Retrieves the contextual data of the specified user such as known groups, location data, and top event types associated with this user account. |
get_user_context
Investigation |
operation: Get All Devices
Input parameters
| Parameter |
Description |
| Organization |
(Optional) Specify the name of the organization using which you want to filter the devices retrieved from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"devices": {
"device": [
{
"name": "",
"accessIp": "",
"approved": "",
"creationMethod": "",
"discoverMethod": "",
"discoverTime": "",
"naturalId": "",
"unmanaged": "",
"updateMethod": "",
"version": "",
"deviceType": {
"accessProtocols": "",
"jobWeight": "",
"model": "",
"vendor": "",
"version": ""
},
"organization": {
"@id": "",
"@name": ""
}
}
]
}
}
operation: Get All Devices For Specified IP Address Range
Input parameters
| Parameter |
Description |
| Include IP SET |
Specify the value of IP addresses based on which you want to retrieve device information from the Fortinet FortiSIEM server. You must provide the value of this field as a range or in the .csv format.
For example, enter, 192.168.20.1-192.168.20.100 |
| Exclude IP SET |
(Optional) Specify the value of the range of IP addresses that you want to exclude from this search operation. You must provide the value of this field as a range or in the .csv format. |
| Organization |
(Optional) Specify the name of the organization using which you want to filter the devices retrieved from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"devices": {
"device": [
{
"name": "",
"accessIp": "",
"approved": "",
"creationMethod": "",
"discoverMethod": "",
"discoverTime": "",
"naturalId": "",
"unmanaged": "",
"updateMethod": "",
"version": "",
"deviceType": {
"accessProtocols": "",
"jobWeight": "",
"model": "",
"vendor": "",
"version": ""
},
"organization": {
"@id": "",
"@name": ""
}
}
]
}
}
operation: Get Device Information
Input parameters
| Parameter |
Description |
| Device IP |
Specify the IP address of the device for which you want to retrieve details from the Fortinet FortiSIEM server. |
| Organization |
(Optional) Specify the name of the organization for which you want to retrieve details of the device from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"device": {
"luns": "",
"name": "",
"status": "",
"version": "",
"accessIp": "",
"approved": "",
"storages": "",
"naturalId": "",
"unmanaged": "",
"components": "",
"deviceType": {
"model": "",
"vendor": "",
"version": "",
"category": "",
"jobWeight": ""
},
"interfaces": {
"networkinterface": {
"adminStatus": "",
"description": "",
"inSpeed": "",
"ipv4Addr": "",
"ipv4IsVirtual": "",
"ipv4Mask": "",
"isCritical": "",
"isMonitor": "",
"isTrunk": "",
"isWAN": "",
"macAddr": "",
"macIsVirtual": "",
"name": "",
"operStatus": "",
"outSpeed": "",
"snmpIndex": "",
"speed": "",
"type": ""
}
},
"processors": "",
"raidGroups": "",
"applications": "",
"discoverTime": "",
"organization": {
"@id": "",
"@name": ""
},
"updateMethod": "",
"ipToHostNames": "",
"storageGroups": "",
"creationMethod": "",
"description": "",
"discoverMethod": "",
"winMachineGuid": "",
"eventParserList": "",
"systemUpTime": "",
"softwarePatches": "",
"softwareServices": "",
"sanControllerPorts": ""
}
}
operation: List Monitored Devices and Attributes
Input parameters
None.
Output
The output contains the following populated JSON schema:
{
"monitoredDevices": {
"perfMonDevices": {
"device": {
"accessIp": "",
"deviceName": "",
"deviceType": "",
"monitors": {
"monitor": [
{
"category": "",
"method": ""
}
]
},
"organization": ""
}
},
"eventPullingDevices": ""
}
}
operation: List Monitored Organizations
Input parameters
None.
Output
The output contains the following populated JSON schema:
[
{
"@id": "",
"name": "",
"@xmlId": "",
"@custId": "",
"@ownerId": "",
"disabled": "",
"domainId": "",
"initialized": "",
"@creationTime": "",
"collectors": {
"collector": []
},
"@lastModified": "",
"@entityVersion": "",
"custProperties": ""
}
]
operation: Get Organization Details
Input parameters
| Parameter |
Description |
| Organization ID |
Specify the ID of the organization whose details you want to retrieve from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"@entityVersion": "",
"@creationTime": "",
"@custId": "",
"@id": "",
"@lastModified": "",
"custProperties": "",
"collectors": {
"collector": []
},
"@ownerId": "",
"@xmlId": "",
"disabled": "",
"domainId": "",
"initialized": "",
"name": ""
}
operation: List Incidents
Input parameters
Important: The FortiSIEM API does not support filtering incidents in the "List Incident" action based on sub-categories.
| Parameter |
Description |
| From |
(Optional) Specify the start DateTime to retrieve incidents from the Fortinet FortiSIEM server. |
| To |
(Optional) Specify the end DateTime to retrieve the incidents from the Fortinet FortiSIEM server. |
| Incident Status |
(Optional) Select one or more incident statuses from the following options to filter incidents:
- Active
- Auto Cleared,
- Manually Cleared
- System Cleared
|
| Incident Category |
(Optional) Select one or more incident categories from the following options to filter incidents:
- Availability
- Performance,
- Changed
- Security
- Other
|
| Incident Sub Category |
(Optional) Specify the sub-category of the incident based on which you want to retrieve incidents from the Fortinet FortiSIEM server. |
| Incident Severity |
(Optional) Select one or more incident severities from the following options to filter incidents:
|
| Event Type |
(Optional) Specify the event type of the incident based on which you want to retrieve incidents from the Fortinet FortiSIEM server. |
| Other Filters |
(Optional) Specify the parameters in the JSON format using which you want to filter the incidents retrieved from the Fortinet FortiSIEM server. For example:
{
"status": [
0
],
"eventType": [
"PH_RULE_SERVER_CPU_WARN"
],
"incidentRptIp": [
"10.7.12.156"
]
}
|
| Number Of Items To Return In Response or Size Per Page |
(Optional) For FortiSIEM 6.7.6: This parameter defines the maximum number of items that this operation will return, per page, in the response.
For versions other than FortiSIEM 6.7.6: This parameter defines the maximum number of items that this operation will return in the response.
By default, this parameter is set to 500 items. |
| Offset |
(Optional) Specify the index of the first item to be returned by this operation. This parameter is useful if you want to get a subset of records, say incidents starting from the 10th incident. By default, this is set as 0. |
| Order By |
(Optional) Specify the field using which to sort the incidents retrieved from the Fortinet FortiSIEM server. You can also specify the sort direction of the specified field. For example, incidentLastSeen DESC |
| Event Fields To Show In Response |
(Optional) Specify the comma-separated list of event fields that you want to include in the list of incidents that you want to retrieve from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"data": [
{
"count": "",
"tactic": "",
"customer": "",
"eventName": "",
"eventType": "",
"technique": "",
"incidentId": "",
"incidentSrc": {
"srcIpAddr": "",
"computer": ""
},
"attackTactic": "",
"incidentReso": "",
"eventSeverity": "",
"incidentRptIp": "",
"incidentTitle": "",
"incidentDetail": "",
"incidentStatus": "",
"incidentTarget": {
"user": "",
"domain": "",
"hostName": "",
"hostIpAddr": "",
"targetUser": "",
"targetDomain": "",
"destIpAddr": "",
"destIpPort": ""
},
"attackTechnique": [
{
"name": "",
"techniqueid": ""
}
],
"eventSeverityCat": "",
"incidentLastSeen": "",
"incidentFirstSeen": "",
"incidentStatusStr": "",
"incidentRptDevName": "",
"phIncidentCategory": "",
"incidentClearedTime": "",
"incidentClearedReason": "",
"phSubIncidentCategory": "",
"destName": ""
}
]
}
operation: Get Incident Details
Input parameters
| Parameter |
Description |
| Incident IDs |
Specify the IDs of incidents, in the CSV or list format, whose details you want to retrieve from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"pages": "",
"total": "",
"queryId": "",
"sizePerPage": "",
"data": [
{
"incidentTitle": "",
"eventSeverity": "",
"incidentFirstSeen": "",
"incidentReso": "",
"incidentRptIp": "",
"incidentLastSeen": "",
"incidentSrc": "",
"count": "",
"attackTechnique": "",
"eventType": "",
"phIncidentCategory": "",
"incidentClearedTime": "",
"incidentTarget": "",
"attackTactic": "",
"phSubIncidentCategory": "",
"eventSeverityCat": "",
"incidentDetail": "",
"incidentRptDevName": "",
"eventName": "",
"incidentId": "",
"incidentStatus": "",
"customer": ""
}
],
"start": ""
}
operation: Comment Incident
Input parameters
| Parameter |
Description |
| Incident ID |
Specify the ID of the incident in which you want to add the comment on the Fortinet FortiSIEM server. |
| Comment Text |
Specify the text of the comment that you want to add to the specified incident on the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"message": "",
"incident_id": ""
}
operation: Clear Incident With Reason
Input parameters
| Parameter |
Description |
| Incident ID |
Specify the ID of the incident that you want to clear from the Fortinet FortiSIEM server. |
| Reason |
Specify the text of the reason that you want to specify while clearing the specified incident from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"message": "",
"incident_id": []
}
operation: Get Events For Incident
Input parameters
| Parameter |
Description |
| Incident ID |
Specify the ID of the incident for which you want to retrieve all associated events from the Fortinet FortiSIEM server. |
| Time From |
Select the start time range from when you want to search raw events for the given incident ID.
NOTE: This parameter is supported only in the FortiSIEM 6.7.6 version. Also, note that the max interval between the Time To and Time From cannot exceed 24 hours. |
| Time To |
Select the end time range till when you want to search raw events for the given incident ID.
NOTE: This parameter is supported only in the FortiSIEM 6.7.6 version. Also, note that the max interval between the Time To and Time From cannot exceed 24 hours. |
| Number Of Items To Return In Response |
(Optional) The maximum number of events that you want this operation to return in the response.
By default, this parameter is set to 10 items.
|
Output
The output contains the following populated JSON schema:
[
{
"id": "",
"nid": "",
"index": 0,
"custId": 2000,
"dataStr": {},
"eventType": "",
"attributes": {
"Count": "",
"Event ID": "",
"Source IP": "",
"Time skew": "",
"Event Type": "",
"Attack Name": "",
"Device Time": "",
"Relaying IP": "",
"Collector ID": "",
"Malware Name": "",
"Reporting IP": "",
"Raw Event Log": "",
"Destination IP": "",
"Event Severity": "",
"Organization ID": "",
"Reporting Model": "",
"Reporting Device": "",
"Reporting Vendor": "",
"Source Host Name": "",
"Virus/Malware ID": "",
"Event Parser Name": "",
"Organization Name": "",
"Event Parse Status": "",
"Event Receive Time": "",
"Event Rule Trigger": "",
"Source TCP/UDP Port": "",
"Destination Host Name": "",
"System Event Category": "",
"Event Severity Category": "",
"Destination TCP/UDP Port": "",
"External Event Receive Protocol": ""
},
"rawMessage": "",
"receiveTime": "",
"eventAttributes": []
}
]
operation: Run Advanced Search Query
Input parameters
| Parameter |
Description |
| Advanced Search Query |
Specify the conditions using which you want to process the search results for the report that you want to run on the Fortinet FortiSIEM server. For example, (incidentDetail CONTAIN "jobName" AND phEventCategory = 1) AND (phCustId IN (1)). |
| Event Fields To Show In Response |
Specify the comma-separated list of event fields that you want to include in the response retrieved from the FortiSIEM server. |
| Order By |
(Optional) Specify the field using which you want to sort the search results for the report that you want to run on the Fortinet FortiSIEM server. You can also specify the sort direction of the specified field. For example, phRecvTime DESC |
| Time Range |
(Optional) Specify the time duration to search for reports to run on the Fortinet FortiSIEM server. By default, this is set as Relative Time. You can select from the following options:
- Relative Time: Specify values in the following fields:
- Relative Time: Select the unit of the duration from the following options:
- Last: Select the quantity of the units for the duration selected. For example, if the unit selected was hours, select
2 to set the relative time duration as 2 hours.
- Absolute Time: Specify values in the following fields:
- From: (Optional) Specify the start DateTime for which to get events from the Fortinet FortiSIEM server.
- To: (Optional) Specify the end DateTime for which to get events from the Fortinet FortiSIEM server.
|
| Number Of Items To Return In Response |
(Optional) Specify the maximum number of events that you want this operation to return in the response.
By default, this parameter is set to 50 items.
|
| Offset |
(Optional) Specify the index of the first item to be returned by this operation. This parameter is useful if you want to get a subset of events, say events starting from the 10th event. By default, this is set as 0. |
Output
No output schema is available currently.
operation: Update Incident
Input parameters
| Parameter |
Description |
| Incident ID |
Specify the ID of the incident you want to update on the Fortinet FortiSIEM server. |
| Comment Text |
Specify the text of the comment that you want to add to the specified incident you want to update on the Fortinet FortiSIEM server. |
| Incident Status |
(Optional) Select the incident status that you want to assign to the specified incident you want to update on the Fortinet FortiSIEM server. You can select one of the following options:
- Active
- Auto Cleared,
- Manually Cleared
- System Cleared
|
| Incident Severity |
(Optional) Select the incident severity that you want to assign to the specified incident you want to update on the Fortinet FortiSIEM server. You can select one of the following options:
|
| Incident Resolution |
(Optional) Select the resolution that you want to assign to the specified incident you want to update on the Fortinet FortiSIEM server. You can choose between True Positive or False Positive. |
| External Ticket Type |
(Optional) Select the external ticket type of the specified incident you want to update on the Fortinet FortiSIEM server. You can select one of the following options:
|
| External Ticket ID |
(Optional) Specify the ID of the external ticket ID to update in the specified incident you want to update on the Fortinet FortiSIEM server. |
| External Ticket State |
(Optional) Select the external ticket state of the specified incident you want to update on the Fortinet FortiSIEM server. You can select one of the following options:
- New
- Assigned
- In Progress
- Closed
|
| External Assigned User |
(Optional) Specify the assigned user of the external ticket to update in the specified incident you want to update on the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"message": "",
"incident_id": ""
}
operation: Get Event Details
Input parameters
| Parameter |
Description |
| Event ID |
The ID of the event whose details you want to retrieve from the Fortinet FortiSIEM server. |
| Event Fields To Show In Response |
Specify the comma-separated list of event fields that you want to include in the response retrieved from the FortiSIEM server. |
| From |
(Optional) Specify the start DateTime from when you want to retrieve event details from the Fortinet FortiSIEM server. |
| To |
(Optional) Specify the end DateTime till when you want to retrieve event details from the Fortinet FortiSIEM server.
Important: If you do not specify the From and To parameters for this operation, then by default events for the last 2 weeks will be retrieved from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"id": "",
"nid": "",
"index": "",
"custId": "",
"dataStr": "",
"eventType": "",
"attributes": {
"uuid": "",
"vdom": "",
"count": "",
"fwRule": "",
"eventId": "",
"ipProto": "",
"srcName": "",
"subtype": "",
"customer": "",
"destName": "",
"fwAction": "",
"logLevel": "",
"memberID": "",
"totFlows": "",
"trandisp": "",
"eventName": "",
"eventType": "",
"reptModel": "",
"sessionId": "",
"srcIpAddr": "",
"srcIpPort": "",
"totPkts64": "",
"destGeoOrg": "",
"destIpAddr": "",
"destIpPort": "",
"deviceTime": "",
"parserName": "",
"phRecvTime": "",
"recvPkts64": "",
"reptVendor": "",
"sentPkts64": "",
"totBytes64": "",
"collectorId": "",
"destGeoCity": "",
"eventAction": "",
"rawEventMsg": "",
"hostIpAddr": "",
"hostName": "",
"recvBytes64": "",
"reptDevName": "",
"sentBytes64": "",
"serviceName": "",
"srcIntfName": "",
"timeSkewSec": "",
"appGroupName": "",
"destGeoState": "",
"destIntfName": "",
"durationMSec": "",
"eventParsedOk": "",
"eventSeverity": "",
"reptDevIpAddr": "",
"destGeoCountry": "",
"profileDetails": "",
"relayDevIpAddr": "",
"destGeoLatitude": "",
"phEventCategory": "",
"destGeoLongitude": "",
"eventRuleTrigger": "",
"eventSeverityCat": "",
"postNATSrcIpAddr": "",
"postNATSrcIpPort": "",
"extEventRecvProto": "",
"destGeoCountryCodeStr": ""
},
"receiveTime": ""
}
operation: Search Events
Input parameters
| Parameter |
Description |
| Search Attributes |
Select attribute types using which you want to search for events in the Fortinet FortiSIEM server. You can choose one or more search attributes from the following options: Destination Port, Destination IP, Event ID, Event Action, Incident ID, File Name, Host Name, Organization Name, Process Name, Post-NAT Source IP, Raw Event Log, Relay IP, Reporting Ip, Source IP, Source Port, Source MAC, or User
- If you choose Destination Port, then in the Destination Port IN field, enter the value of the destination port for which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Destination IP, then in the Destination IP IN field, enter a comma-separated list of destination IPs based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Event ID, then in the Event ID IN field, enter the value of the event ID for which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Event Action, then from the Event Action IN drop-down list, choose the event action for which you want to search for events in the Fortinet FortiSIEM server. You can choose 1-Deny or 0-Permit.
- If you choose Incident ID, then in the Incident ID IN field, enter the value of the Incident ID for which you want to search for events in the Fortinet FortiSIEM server.
- If you choose File Name, then in the File Name CONTAINS field, enter the name of the file based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Host Name, then in the Host Name CONTAINS field, enter the name of the host using which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Organization Name, then in the Organization Name CONTAINS field, enter the name of the organization based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Process Name, then in the Process Name CONTAINS field, enter the name of the process based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Post-NAT Source IP, then in the Post-NAT Source IP IN field, enter the Post-NAT source IP based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Raw Event Log, then in the Raw Event Log CONTAINS field, enter the search attribute for the raw event based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Relay IP, then in the Relay IP IN field, enter the relay IP based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Reporting IP, then in the Reporting IP IN field, enter the reporting IP based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Source IP, then in the Source IP IN field, enter the source IP based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Source Port, then in the Source Port IN field, enter the source port based on which you want to search for events in the Fortinet FortiSIEM server.
- If you choose Source MAC, then in the Source MAC CONTAINS field, enter the search attribute for the source MAC using which you want to search for events in the Fortinet FortiSIEM server.
- If you choose User, then in the User CONTAINS field, enter the search attribute for the user based on which you want to search for events in the Fortinet FortiSIEM server.
|
| Event Fields To Show In Response |
Specify the comma-separated list of event fields that you want to include in the response retrieved from the FortiSIEM server. |
| Time Range |
(Optional) Specify the time duration to search for reports to run on the Fortinet FortiSIEM server. By default, this is set as Relative Time. You can select from the following options:
- Relative Time: Specify values in the following fields:
- Relative Time: Select the unit of the duration from the following options:
- Last: Select the quantity of the units for the duration selected. For example, if the unit selected was hours, select
2 to set the relative time duration as 2 hours.
- Absolute Time: Specify values in the following fields:
- From: (Optional) Specify the start DateTime for which to get events from the Fortinet FortiSIEM server.
- To: (Optional) Specify the end DateTime for which to get events from the Fortinet FortiSIEM server.
|
| Number Of Items To Return In Response |
(Optional) Specify the maximum number of events that you want this operation to return in the response.
By default, this parameter is set to 50 items.
|
| Offset |
(Optional) Specify the index of the first item to be returned by this operation. This parameter is useful if you want to get a subset of events, say events starting from the 10th event. By default, this is set as 0. |
Output
The output contains the following populated JSON schema:
{
"@start": "",
"events": [
{
"id": "",
"nid": "",
"index": "",
"custId": "",
"dataStr": "",
"eventType": "",
"attributes": {
"type": "",
"uuid": "",
"vdom": "",
"count": "",
"fwRule": "",
"osType": "",
"eventId": "",
"ipProto": "",
"srcName": "",
"subtype": "",
"customer": "",
"destName": "",
"fwAction": "",
"logLevel": "",
"memberID": "",
"totFlows": "",
"trandisp": "",
"eventName": "",
"eventType": "",
"reptModel": "",
"sessionId": "",
"srcIpAddr": "",
"srcIpPort": "",
"totPkts64": "",
"destIpAddr": "",
"destIpPort": "",
"deviceTime": "",
"parserName": "",
"phRecvTime": "",
"recvPkts64": "",
"reptVendor": "",
"sentPkts64": "",
"srcMACAddr": "",
"totBytes64": "",
"collectorId": "",
"eventAction": "",
"rawEventMsg": "",
"recvBytes64": "",
"reptDevName": "",
"sentBytes64": "",
"serviceName": "",
"srcIntfName": "",
"timeSkewSec": "",
"appGroupName": "",
"destIntfName": "",
"durationMSec": "",
"eventParsedOk": "",
"eventSeverity": "",
"reptDevIpAddr": "",
"profileDetails": "",
"relayDevIpAddr": "",
"phEventCategory": "",
"eventRuleTrigger": "",
"eventSeverityCat": "",
"masterSrcMACAddr": "",
"postNATSrcIpAddr": "",
"postNATSrcIpPort": "",
"extEventRecvProto": ""
},
"receiveTime": ""
}
],
"@queryId": "",
"@errorCode": "",
"@totalCount": ""
}
operation: Get Event Attributes
Input parameters
None.
Output
{
"FQDN": "",
"Type": "",
"UUID": "",
"User": "",
"VM IP": "",
"Domain": "",
"Host IP": "",
"ICMP Id": "",
"IP Port": "",
"Message": "",
"User Id": "",
"Agent ID": "",
"Checksum": "",
"Computer": "",
"Duration": "",
"Event ID": "",
"Host MAC": "",
"URI Stem": "",
"Disk Name": "",
"File Name": "",
"File Path": "",
"Host City": "",
"Host Name": "",
"Host VLAN": "",
"ICMP Code": "",
"ICMP Type": "",
"Rule Name": "",
"Server IP": "",
"TCP flags": "",
"URI Query": "",
"WLAN SSID": "",
"Event Name": "",
"Event Type": "",
"File Owner": "",
"Host Model": "",
"Host State": "",
"IP Version": "",
"Image File": "",
"Sent Bytes": "",
"Source IP ": "",
"Source MAC": "",
"Source TOS": "",
"User Group": "",
"VPN Status": "",
"Attack Name": "",
"Device Port": "",
"Device Time": "",
"Employee ID": "",
"Host Vendor": "",
"IP Protocol": "",
"Incident ID": "",
"Mail Sender": "",
"New Host IP": "",
"Object Name": "",
"Relaying IP": "",
"Server Name": "",
"Source City": "",
"Source VLAN": "",
"Target User": "",
"Total Bytes": "",
"Collector ID": "",
"Collector IP": "",
"DHCP Gateway": "",
"Event Action": ": ",
"Event Source": "",
"Host Country": "",
"Mail Subject": "",
"Malware Name": "",
"Malware Type": "",
"Process Name": "",
"Reporting IP": ": ",
"Sent Packets": "",
"Source State": "",
"VM Host Name": "",
"Win Logon Id": "",
"ARP Source IP": "",
"Connection Id": "",
"DNS Server IP": "",
"IPS Sensor Id": "",
"Mail Receiver": "",
"Object Handle": "",
"Raw Event Log": "",
"Software Name": "",
"Target Domain": "",
"Total Packets": "",
"VPN Conn Type": "",
"WLAN Radio Id": "",
"ARP Source MAC": "",
"Account Number": "",
"Auth Server IP": "",
"Collector Name": "",
"DNS Query Type": "",
"Destination IP": "",
"Event Severity": "",
"Hash Algorithm": "",
"Incident Title": "",
"Malware Action": "",
"OS Object Type": "",
"Received Bytes": "",
"Recv Auth Fail": "",
"Reporting City": "",
"Sent TCP flags": "",
"Snort Event ID": "",
"Source Country": "",
"TCP Connection": "",
"UDP Connection": "",
"Win Logon Type": "",
"DHCP Server MAC": "",
"Destination MAC": "",
"Destination TOS": "",
"Firewall Action": "",
"HTTP User Agent": "",
"Host Virtual IP": "",
"ICMP Connection": "",
"Incident Source": "",
"Incident Target": "",
"Organization ID": "",
"Relaying Device": "",
"Reporting Model": "",
"Reporting State": "",
"Target Computer": "",
"Target Host MAC": "",
"VPN Tunnel Name": "",
"WLAN Channel Id": "",
"WLAN User count": "",
"Application Name": "",
"Application Port": "",
"Auth Server Name": "",
"Destination City": "",
"Destination VLAN": "",
"Event Occur Time": "",
"Firewall Session": "",
"Operating System": "",
"Received Packets": "",
"Reporting Device": "",
"Reporting Vendor": "",
"Source Host Name": "",
"DHCP Request Type": "",
"Destination State": "",
"Event Description": "",
"Host Organization": "",
"Incident Category": "",
"Informational URL": "",
"Organization Name": "",
"Reporting Country": "",
"Target User Group": "",
"ARP Destination IP": "",
"Event Parse Status": "",
"Event Receive Time": "",
"IP Type of Service": "",
"Object Access Type": "",
"Post-NAT Source IP": "",
"Previous Source IP": "",
"Recv Packet Errors": "",
"Sent Packet Errors": "",
"Source Device Port": "",
"Vulnerability Name": "",
"Vulnerability Type": "",
"ARP Destination MAC": "",
"Destination Country": "",
"Host Interface Name": "",
"Recv Interface Util": "",
"Sent Interface Util": "",
"Source Organization": "",
"Source TCP/UDP Port": "",
"Vulnerability Score": "",
"Win Logon Fail Code": "",
"False Positive Check": "",
"IDS Database Version": "",
"Post-NAT Source Port": "",
"Source Firewall Zone": "",
"Vulnerability CVE Id": "",
"Business Service Name": "",
"Destination Host Name": "",
"IPS Event Risk Rating": "",
"Incident Reporting IP": "",
"Network Access Device": "",
"Recv Packet Error Pct": "",
"Sent Packet Error Pct": "",
"Source Interface Name": "",
"System Event Category": "",
"Pre-NAT Destination IP": "",
"Reporting Organization": "",
"Virus Database Version": "",
"Destination Device Port": "",
"Event Severity Category": "",
"IPS Event Threat Rating": ": ",
"Post-NAT Destination IP": "",
"Destination Organization": "",
"Destination Service Name": "",
"Destination TCP/UDP Port": "",
"Network Access Device IP": "",
"Operating System Version": "",
"Pre-NAT Destination Port": "",
"Destination Firewall Zone": "",
"Palo Alto Firewall Action": "",
"Destination Interface Name": "",
"Extension Database Version": "",
"Network Access Device Port": "",
"Source Interface SNMP Index": "",
"Firewall Session Utilization": "",
"Post-NAT Destination Ip Port": "",
"Previous Source TCP/UDP Port": "",
"Command and Control Host Name": "",
"Wireless Attack Signature Name": "",
"Incident Trigger Attribute List": "",
"Source Autonomous System Number": "",
"Command and Control TCP/UDP Port": "",
"Destination Interface SNMP Index": "",
"Destination Autonomous System Number": "",
"Anti-Virus Extension Database Version": ""
}
operation: Get Events Data By Query ID
Input parameters
| Parameter |
Description |
| Query ID |
Specify the ID of the executed query based on which you want to retrieve data of events from the Fortinet FortiSIEM server. You can retrieve the Query ID from the output of actions such as List Incidents, Search Query, etc. |
| Number Of Items To Return In Response |
(Optional) Specify the maximum number of items that you want this operation to return in the response. By default, the page size is set to 50 items. |
| Offset |
(Optional) Specify the index of the first item to be returned by this operation. This parameter is useful if you want to get a subset of records, say incidents starting from the 10th incident. By default, this is set as 0. |
Output
The output contains a non-dictionary value.
operation: Get Watch Lists
Input parameters
| Parameter |
Description |
| Get Watch List Data By |
Select the parameters using which you want to retrieve watch list data from Fortinet FortiSIEM.
- If you choose Get All Watch Lists, then data for all watch lists are retrieved from Fortinet FortiSIEM.
- If you choose By Watch List ID, then in the Watch List IDfield you must specify the ID of the watch list whose details you want to retrieve from Fortinet FortiSIEM.
- If you choose By Watch List Entry Value, then in the Entry Valuefield you must specify the value of the watch list entry whose watch list details you want to retrieve from Fortinet FortiSIEM.
- If you choose By Watch List Entry ID, then in the Watch List Entry IDfield you must specify the ID of the watch list entry whose watch list details you want to retrieve from Fortinet FortiSIEM.
|
Output
The output contains the following populated JSON schema:
If you choose Get All Watch Lists or By Watch List ID as the Get Watch List Data By:
{
"response": [
{
"isCaseSensitive": "",
"naturalId": "",
"displayName": "",
"description": "",
"valuePattern": "",
"ageOut": "",
"topGroup": "",
"entries": [
{
"naturalId": "",
"firstSeen": "",
"count": "",
"triggeringRules": "",
"description": "",
"entryValue": "",
"expiredTime": "",
"ageOut": "",
"lastSeen": "",
"dataCreationType": "",
"custId": "",
"id": "",
"state": ""
}
],
"dataCreationType": "",
"valueType": "",
"custId": "",
"name": "",
"id": ""
}
],
"status": ""
}
Output schema when you choose By Watch List Entry ID as Get Watch List Data By:
{
"response": {
"isCaseSensitive": "",
"naturalId": "",
"displayName": "",
"description": "",
"valuePattern": "",
"ageOut": "",
"topGroup": "",
"entries": [
{
"naturalId": "",
"firstSeen": "",
"count": "",
"triggeringRules": "",
"description": "",
"entryValue": "",
"expiredTime": "",
"ageOut": "",
"lastSeen": "",
"dataCreationType": "",
"custId": "",
"id": "",
"state": ""
}
],
"dataCreationType": "",
"valueType": "",
"custId": "",
"name": "",
"id": ""
},
"status": ""
}
This is the default output schema:
{
"response": [
{
"isCaseSensitive": "",
"naturalId": "",
"displayName": "",
"description": "",
"valuePattern": "",
"ageOut": "",
"topGroup": "",
"entries": [
{
"naturalId": "",
"firstSeen": "",
"count": "",
"triggeringRules": "",
"description": "",
"entryValue": "",
"expiredTime": "",
"ageOut": "",
"lastSeen": "",
"dataCreationType": "",
"custId": "",
"id": "",
"state": ""
}
],
"dataCreationType": "",
"valueType": "",
"custId": "",
"name": "",
"id": ""
}
],
"status": ""
}
operation: Get Watch List Entries Count
Input parameters
None.
Output
The output contains the following populated JSON schema:
{
"status": "",
"response": {
"entry_count": ""
}
}
operation: Get Watch List Entry
Input parameters
| Parameter |
Description |
| Watch List Entry ID |
Specify the ID of the watch list entry that you want to retrieve from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"status": "",
"response": {
"id": "",
"count": "",
"state": "",
"ageOut": "",
"custId": "",
"lastSeen": "",
"firstSeen": "",
"naturalId": "",
"entryValue": "",
"description": "",
"expiredTime": "",
"triggeringRules": "",
"dataCreationType": ""
}
}
operation: Add Watch List Entries To Watch List
Input parameters
| Parameter |
Description |
| Watch List ID |
Specify the ID of the watch list to which you want to add watch list entries. |
| Other parameters |
Specify a JSON Array of watch list entry objects that you want to add to specific watch lists.
For example,
{
"inclusive": false,
"count": 10,
"custId": 1,
"triggeringRules": "Datastore Space Warning",
"entryValue": "PVVol_A001_A000356_POWER2",
"ageOut": "1d",
"lastSeen": 1613601369215,
"firstSeen": 1613601369215,
"disableAgeout": false,
"dataCreationType": "USER"
}
|
Output
The output contains the following populated JSON schema:
{
"response": "",
"status": ""
}
operation: Create Watch List
Input parameters
| Parameter |
Description |
| Watch List JSON Object |
Specify the JSON Object of a watch list with a watch list entry to create in the FortiSIEM database. For example:
{
"description":"Servers,networkorstoragedevices",
"displayName":"ResourceIssuesTest4",
"type":"DyWatchList",
"isCaseSensitive":false,
"dataCreationType":"USER",
"topGroup":false,
"valuePattern":null,
"valueType":"STRING",
"ageOut":"1d",
"custId":1,
"entries":[
{
"inclusive":true,
"entryValue":"PVVol_A001_A000356_5new",
"ageOut":"1d",
"count":1,
"custId":1,
"firstSeen":1612901760000,
"lastSeen":1612901760000,
"triggeringRules":"DatastoreSpaceWarning",
"dataCreationType":"USER"
}
]
}
NOTE: displayName and type are required fields. |
Output
The output contains the following populated JSON schema:
{
"response": [
{
"isCaseSensitive": "",
"naturalId": "",
"displayName": "",
"description": "",
"valuePattern": "",
"ageOut": "",
"topGroup": "",
"entries": [
{
"naturalId": "",
"firstSeen": "",
"count": "",
"triggeringRules": "",
"description": "",
"entryValue": "",
"expiredTime": "",
"ageOut": "",
"lastSeen": "",
"dataCreationType": "",
"custId": "",
"id": "",
"state": ""
}
],
"dataCreationType": "",
"valueType": "",
"custId": "",
"name": "",
"id": ""
}
],
"status": ""
}
operation: Update Watch List Entry
Input parameters
| Parameter |
Description |
| Watch List Entry ID |
Specify the ID of the watch list entry that you want to update in the FortiSIEM database. |
| Count |
(Optional) Specify the occurrence count of the watch list entry that you want to update in the FortiSIEM database. |
| Last Seen Time |
(Optional) Specify the value of the last seen time, i.e., the Unix timestamp, of the specific watch list that you want to update in the FortiSIEM database. |
| State |
From the State drop-down list select Active to set the specific watch list to the Active state; select Inactive to set the specific watch list to the Inactive state. |
| Other Parameters |
JSON Object of a watch list with a watch list entry that you want to update in the FortiSIEM database. For example
{
"lastSeen": 1612901760002,
"dataCreationType": "USER",
"firstSeen": 1612901760001,
"count": 100,
"custId": 1,
"triggeringRules": "Datastore Space Warning",
"description": "Testing again",
"id": 889400,
"inclusive": true,
"entryValue": "PVVol_A001_A000356_POWER23",
"expiredTime": 1612988160001,
"ageOut": "2d"
}
|
Output
The output contains the following populated JSON schema:
{
"response": {
"naturalId": "",
"firstSeen": "",
"count": "",
"triggeringRules": "",
"description": "",
"entryValue": "",
"expiredTime": "",
"ageOut": "",
"lastSeen": "",
"dataCreationType": "",
"custId": "",
"id": "",
"state": ""
},
"status": ""
}
operation: Delete Watch List Entry
Input parameters
| Parameter |
Description |
| Watch List Entry IDs |
Specify the IDs of the watch list entries, in the CSV or list format, that you want to delete from the FortiSIEM database. For example, [5.0.10, 5.0.11] |
Output
The output contains the following populated JSON schema:
{
"response": "",
"status": ""
}
operation: Delete Watch List
Input parameters
| Parameter |
Description |
| Watch List IDs |
IDs of the watch lists, in the CSV or list format, that you want to delete from the FortiSIEM database. For example, [5.0.10, 5.0.11] |
Output
The output contains the following populated JSON schema:
{
"response": "",
"status": ""
}
operation: Create Lookup Table
Input parameters
| Parameter |
Description |
| Name |
Specify the name of the lookup table that you want to create in FortiSIEM.
NOTE: The table name must contain only alphabets and numbers. |
| Column List |
Specify the list of column definitions for the lookup table to create in FortiSIEM. For each column, you must specify the following three values:
key: Specify a key indicating whether the column is a primary columnname: Specify the name of the columntype: Specify the type of the column, for example, STRING, LONG, or DOUBLE.
For example,
[
{
"key": true,
"name": "url",
"type": "STRING"
},
{
"key": false,
"name": "wfCategoryID",
"type": "LONG"
}
]
|
| Description |
(Optional) Specify the description of the lookup table that you want to create in FortiSIEM. |
| Organization Name |
(Optional) Specify the organization name to be assigned to the lookup table that you want to create in FortiSIEM. By default, this is set to the organization of the current user. |
Output
The output contains the following populated JSON schema:
{
"id": "",
"name": "",
"columnList": [
{
"key": "",
"name": "",
"type": ""
}
],
"description": "",
"lastUpdated": "",
"organizationName": ""
}
operation: Get All Lookup Table
Input parameters
| Parameter |
Description |
| Offset |
(Optional) Specify the index of the first item to be returned by this operation. This parameter is useful if you want to get a subset of records, say lookup table definitions starting from the 10th position. By default, this is set as 0. |
| Number Of Items To Return |
(Optional) Specify the maximum number of items that you want this operation to return in the response. By default, the page size is set to 25 items, and the maximum is set at 1000. |
Output
The output contains the following populated JSON schema:
{
"data": [
{
"id": "",
"name": "",
"columnList": [
{
"key": "",
"name": "",
"type": ""
}
],
"description": "",
"lastUpdated": "",
"organizationName": ""
}
],
"size": "",
"start": "",
"total": ""
}
operation: Delete Lookup Table
Input parameters
| Parameter |
Description |
| Lookup Table ID |
Specify the unique identifier representing the lookup Table whose definitions you want to delete from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"status": "",
"message": ""
}
operation: Import Lookup Table Data
Input parameters
| Parameter |
Description |
| File IRI/Attachment ID |
Select the method using which you want to import the CSV file present in FortiSOAR to the Fortinet FortiSIEM server lookup table. You can choose between Attachment ID and File IRI.
- If you choose Attachment ID, then in the Attachment ID field specify the Attachment ID of the CSV file that you want to import into the specified lookup table in FortiSIEM.
- If you choose File IRI, then in the File IRI field specify the CSV file that you want to import into the specified lookup table in FortiSIEM.
|
| Lookup Table ID |
Specify the unique identifier representing the lookup table in FortiSIEM into which you want to import the CSV file in the Fortinet FortiSIEM server. |
| Mapping |
Specify the configuration that matches the position of columns in the CSV file to columns in the specified lookup table. The format of the mapping is as follows: {"":,"":}. For example,
{
"url": 1,
"wfCategoryID": 2
}
|
| File Separator |
Specify the file separator for the specified CSV file. By default, this is set as the comma character(,) |
| File Quote Char |
Specify the file quote character for the specified CSV file. By default, this is set as the double quotation character(") |
| Skip Header |
Select this option to ignore the header of the specified CSV file. |
| Update Type |
Select the method of updating the data in the Fortinet FortiSIEM server. You can choose between Overwrite (default) or Append. |
Output
The output contains the following populated JSON schema:
{
"taskId": ""
}
operation: Check Import Task Status
Input parameters
| Parameter |
Description |
| Lookup Table ID |
Specify the unique identifier representing the lookup table in the Fortinet FortiSIEM server for which you want to check the import task status. |
| Task ID |
Specify the task id of the importing data to the specified lookup table. You can retrieve the task ID from the response of the "Import Lookup Table Data" action. |
Output
The output contains the following populated JSON schema:
{
"actionResult": "",
"id": "",
"progress": "",
"status": ""
}
operation: Get Lookup Table Data
Input parameters
| Parameter |
Description |
| Lookup Table ID |
Specify the unique identifier representing the lookup table for which you want to retrieve items from the Fortinet FortiSIEM server. |
| Start |
(Optional) Specify the index of the first item to be returned by this operation. This parameter is useful if you want to get a subset of records, say lookup table items starting from the 10th position. By default, this is set as 0. |
| Number Of Items To Return |
(Optional) Specify the maximum number of items that you want this operation to return in the response. By default, the page size is set to 25 items, and the maximum is set at 1000. |
| Search Text |
(Optional) Specify the Search text using which you want to filter items of the specified lookup table in the Fortinet FortiSIEM server. |
| Sort By |
(Optional) Specify the lookup table columns using which you want to sort the search results retrieved from the Fortinet FortiSIEM server. You can also specify the sort direction of the specified lookup table columns, i.e., descending (DESC) or ascending (ASC). |
Output
The output contains the following populated JSON schema:
{
"data": [],
"size": "",
"start": "",
"total": ""
}
operation: Update Lookup Table Data
Input parameters
| Parameter |
Description |
| Lookup Table ID |
Specify the unique identifier representing the lookup table whose items you want to update in the Fortinet FortiSIEM server. |
| Key |
Specify the primary key of the item column and its value that you want to update in the specified lookup table. The format is <keyColumn_1>:<value>
For example, key={"url":"http://example.com"} |
| Column Data |
Specify the dictionary of column values to update in the specified lookup table. For example,
{
"url": "www.test.com",
"wfCategoryID": 30,
"score": 0.50119
}
|
Output
The output contains the following populated JSON schema:
{
"response": "",
"message": ""
}
operation: Delete Lookup Table Data
Input parameters
| Parameter |
Description |
| Lookup Table ID |
Specify the unique identifier representing the lookup table whose items you want to delete from the Fortinet FortiSIEM server. |
| Primary Keys |
Specify the list of primary keys of the item columns and their values that you want to delete from the specified lookup table. The format is:
[
{
"keyColumn_1": "value",
"keyColumn_2": "value"
}
]
|
Output
The output contains the following populated JSON schema:
{
"status": "",
"message": ""
}
operation: Get IP Context
Input parameters
| Parameter |
Description |
| IP Address |
Specify the IP address for which to retrieve context from FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"contexts": [
{
"value": "",
"location": {
"city": "",
"region": "",
"latitude": "",
"longitude": "",
"countryCode": "",
"countryName": ""
},
"parameter": "",
"whoisInfo": "",
"topEventTypes": [],
"externalLookups": {
"ip": "",
"FortiGuardIOCResult": {
"av_cate": "",
"verdict": "",
"wf_cate": "",
"ioc_cate": "",
"ioc_tags": "",
"confidence": "",
"spam_cates": ""
}
},
"topVulnerabilities": []
}
]
}
operation: Get Host Context
Input parameters
| Parameter |
Description |
| Host Name |
Specify the host name for which to retrieve context from FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"contexts": [
{
"value": "",
"hostName": "",
"parameter": "",
"deviceType": "",
"importance": "",
"externalLookups": {
"domain": "",
"FortiGuardIOCResult": {
"av_cate": "",
"verdict": "",
"wf_cate": "",
"ioc_cate": "",
"ioc_tags": "",
"confidence": "",
"spam_cates": ""
}
}
}
]
}
operation: Get User Context
Input parameters
| Parameter |
Description |
| User Name |
Specify the user name for which to retrieve context from FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"contexts": [
{
"value": "",
"location": {
"latitude": "",
"longitude": ""
},
"userInfo": {
"groups": [],
"company": "",
"fullName": "",
"jobTitle": ""
},
"parameter": "",
"topEventTypes": []
}
]
}
Included playbooks
The Sample - Fortinet FortiSIEM - 5.2.0 playbook collection comes bundled with the Fortinet FortiSIEM connector. This playbook contains steps using which you can perform all supported actions. You can see the bundled playbooks in the Automation > Playbooks section in FortiSOAR™ after importing the Fortinet FortiSIEM connector.
- > FortiSIEM > Fetch
- >> FortiSIEM > Fetch Associated events for Incident
- Add Watch List Entries to Watch List
- Check Import Task Status
- Clear Incident With Reason
- Comment Incident
- Create Lookup Table
- Create Watch List
- Delete Lookup Table
- Delete Lookup Table Data
- Delete Watch List
- Delete Watch List Entry
- FortiSIEM > Ingest
- Get All Devices
- Get All Devices For Specified IP Address Range
- Get All Lookup Table
- Get Device Information
- Get Event Attributes
- Get Event Details
- Get Events Data By Query ID
- Get Events For Incident
- Get Host Context
- Get IP Context
- Get Incident Details
- Get Lookup Table Data
- Get Organization Details
- Get User Context
- Get Watch List Entries Count
- Get Watch List Entry
- Get Watch Lists
- Import Lookup Table Data
- List Incidents
- List Monitored Devices and Attributes
- List Monitored Organizations
- Run Advanced Search Query
- Search Events
- Update Incident
- Update Lookup Table Data
- Update Watch List Entry
NOTE: If you are planning to use any of the sample playbooks in your environment, ensure that you clone those playbooks and move them to a different collection since the sample playbook collection gets deleted during the connector upgrade and delete.
Data Ingestion Support
Use the Data Ingestion Wizard to easily ingest data into FortiSOAR™ by pulling incidents from Fortinet FortiSIEM. Currently, Incidents in Fortinet FortiSIEM are mapped to Alerts in FortiSOAR™. For more information on the Data Ingestion Wizard, see the Connectors Guide in the FortiSOAR™ product documentation.
NOTE: To link MITRE techniques records to alerts that are being created using the Data Ingestion Wizard, use the MITRE ATT&CK Enrichment Framework and MITRE ATT&CK Threat Hunting Solution Packs.
Configure Data Ingestion
You can configure data ingestion using the Data Ingestion Wizard to seamlessly map the incoming FortiSIEM Incidents to FortiSOAR™Alerts.
The Data Ingestion Wizard helps you configure the scheduled pulling of data from FortiSIEM into FortiSOAR™. It also helps you pull some sample data from FortiSIEM using which you can define the mapping of data between FortiSIEM and FortiSOAR™. The mapping of common fields is generally already done by the Data Ingestion Wizard; users are mostly required to only map any custom fields that are added to the FortiSIEM incident.
-
To begin configuring data ingestion, click Configure Data Ingestion on the Fortinet FortiSIEM connector's Configurations page.
Click Let's Start by fetching some data, to open the Fetch Sample Data screen.
Sample data is required to create a field mapping between FortiSIEM data and FortiSOAR™. The sample data is pulled from connector actions or ingestion playbooks.
-
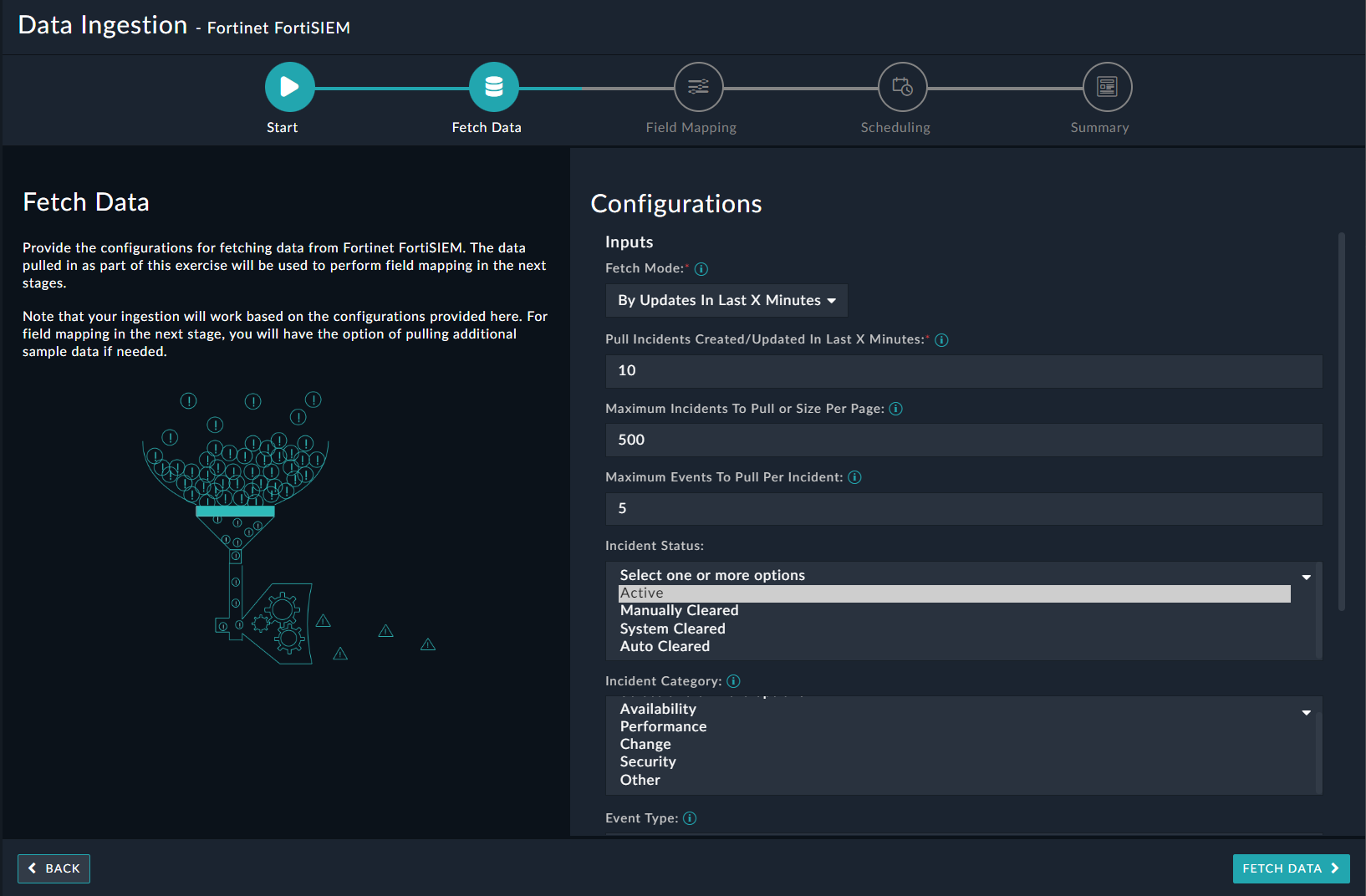
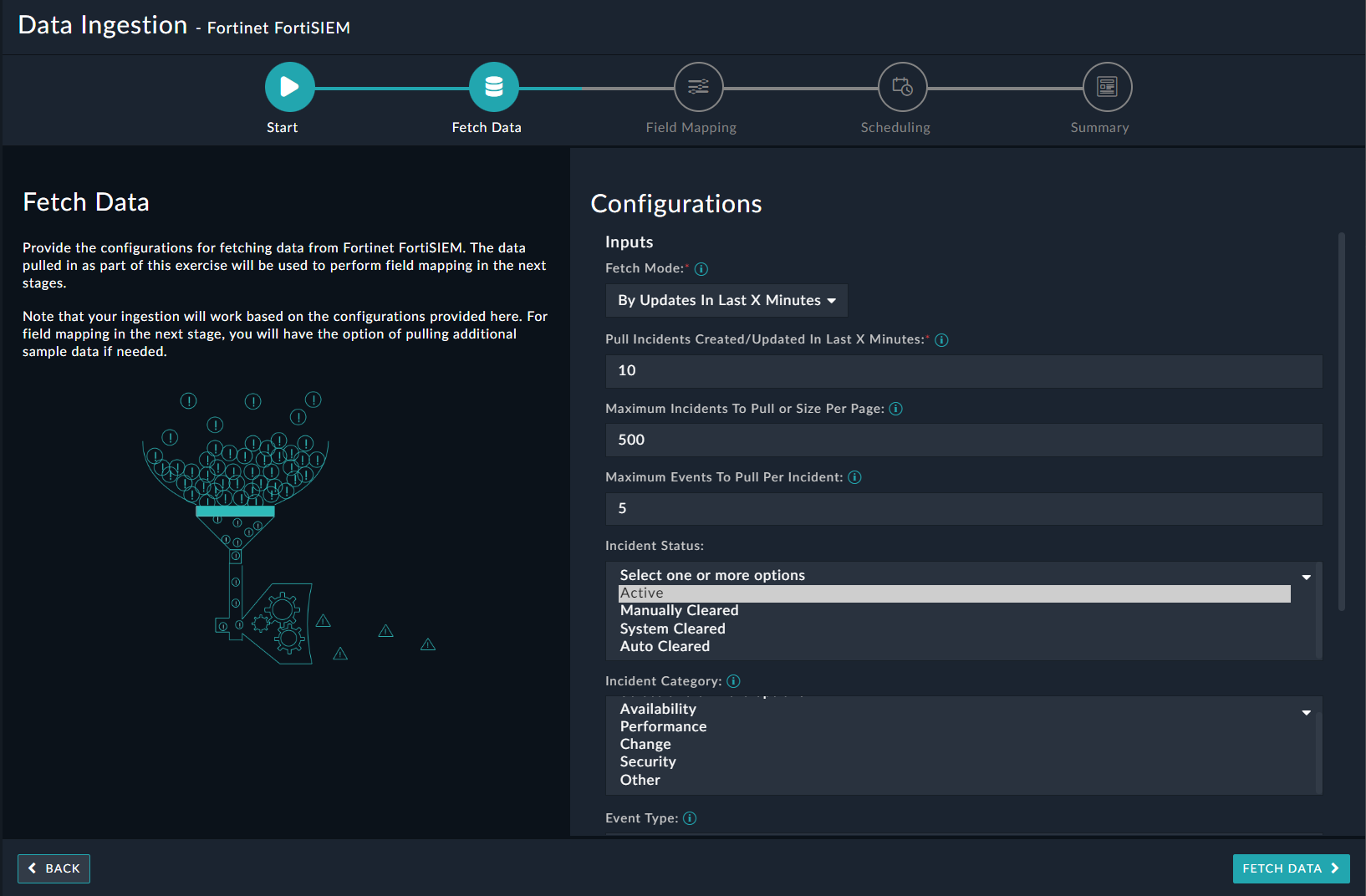
On the Fetch Data screen, provide the configurations required to fetch Fortinet FortiSIEM data.
Users can choose to pull data from Fortinet FortiSIEM by selecting either the last X minutes in which the incidents have been created or updated in FortiSIEM (By Updates in Last X Minutes) or by specifying an Incident ID (By Sample Incident ID) from the Fetch Mode drop-down list. When fetching data based on By Updates in Last X Minutes, specify the number of minutes from when to retrieve incidents that were created or updated in Fortinet FortiSIEM, in the Pull Incidents Creates/Updates In Last X Minutes field. When fetching data based on By Sample Incident ID, specify the ID of the incident to retrieve from Fortinet FortiSIEM, in the Incident ID field. When fetching data based on By Updates in Last X Minutes, you can apply additional parameters such as:
- Maximum Incidents To Pull Or Size Per Page:
NOTE: For FortiSIEM 6.7.6 and 7.1.0: This parameter defines the maximum number of items that this operation will return, per page, in the response.
By default, this parameter is set to 500 items.
- Maximum Events To Pull Per Incident
- Incident Status - Select one or more incident statuses from the Active, Manually Cleared, System Cleared, and Auto Cleared options to filter incidents.
- Incident Category - Select one or more incident categories from the Availability, Performance, Change, Security, and Other options to filter incidents.
- Event Type: Filters incidents based on event type
- Other Filters: Specify parameters using which to filter the incidents retrieved from the Fortinet FortiSIEM server. For example,
{
"status": [0],
"eventType": ["PH_RULE_SERVER_CPU_WARN"],
"incidentRptIp": [10.7.12.156"]
}
The fetched data is used to create a mapping between the FortiSIEM data and FortiSOAR™ alerts. Once you have completed specifying the configurations, click the Fetch Data button.
When configuring data ingestion for MSSP systems, if the Configure Multi-Tenant Mappings checkbox is checked, ensure that you map the organization name defined in FortiSIEM as a tenant in FortiSOAR™, in the Organization Mapping field:
NOTE: If you have not mapped or wrongly mapped an organization, then the incident record will be created as a Self entry.
-
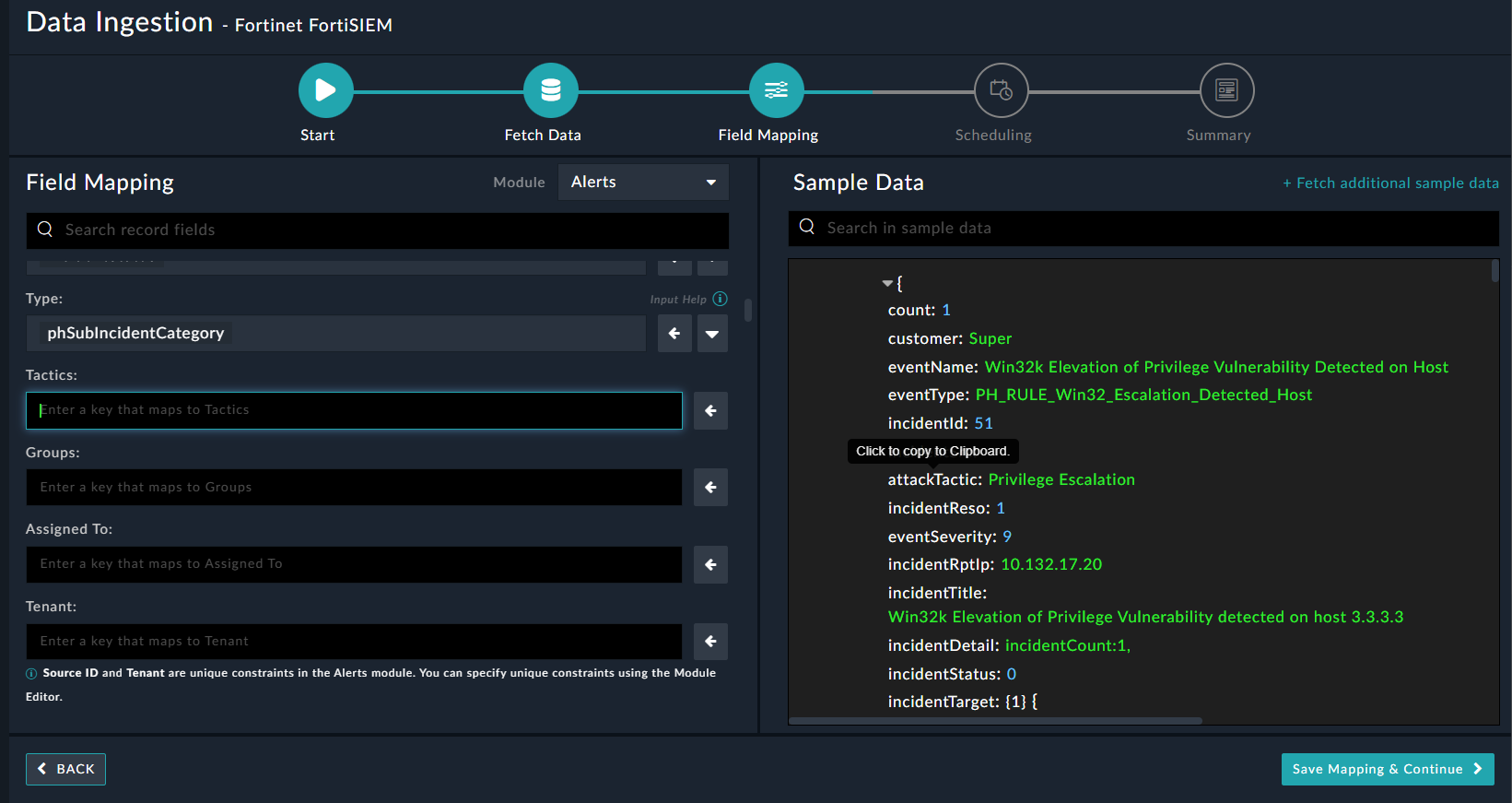
On the Field Mapping screen, map the fields of a FortiSIEM incident to the fields of an alert present in FortiSOAR™
To map a field, click the key in the sample data to add the Jinja value of the field. For example, to map the attackTactic parameter of a FortiSIEM incident to the Tactics parameter of a FortiSOAR™ alert, click the Tactics field and then click the attackTactic field to populate its keys:
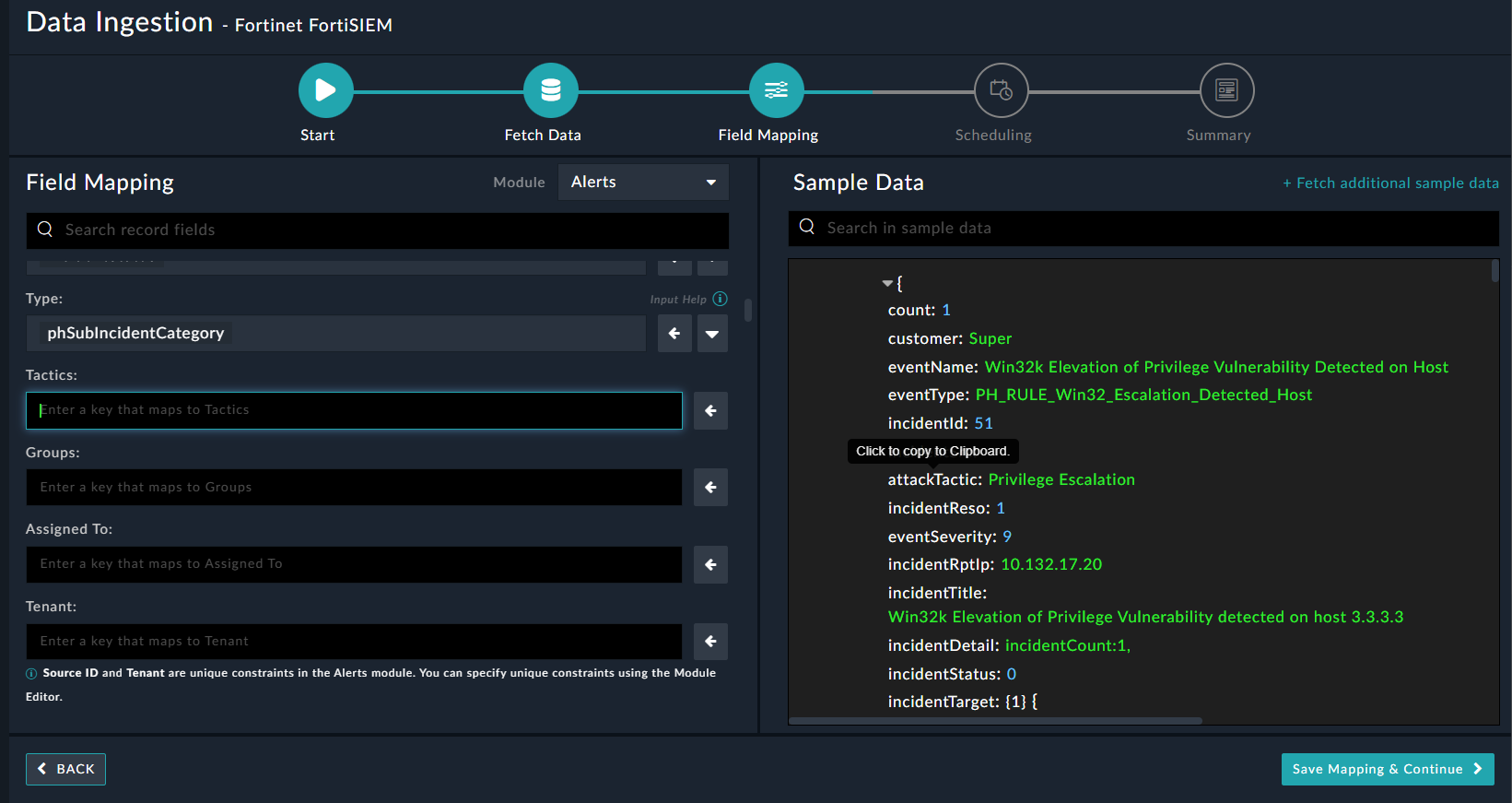
For more information on field mapping, see the Data Ingestion chapter in the FortiSOAR™ product documentation's Connectors Guide. Once you have completed the mapping of fields, click Save Mapping & Continue.
NOTE: The Field Mapping was updated in the release 5.1.0 of the FortiSIEM connector as follows:
- Updated the Description field of the mapped alert record to contain additional information such as Incident Category/Sub-Category, First/Last Occurred, etc. for the incident fetched from FortiSIEM.
- Mapped the Name field of the alert record to the "incidentTitle" key of the incident fetched from FortiSIEM.
- Mapped the Rule field of the alert record to the "eventType" key of the incident fetched from FortiSIEM.
- Updated the Status of the alert to be set to OPEN if the "incidentStatus" of the incident fetched from FortiSIEM is 0 (zero)
-
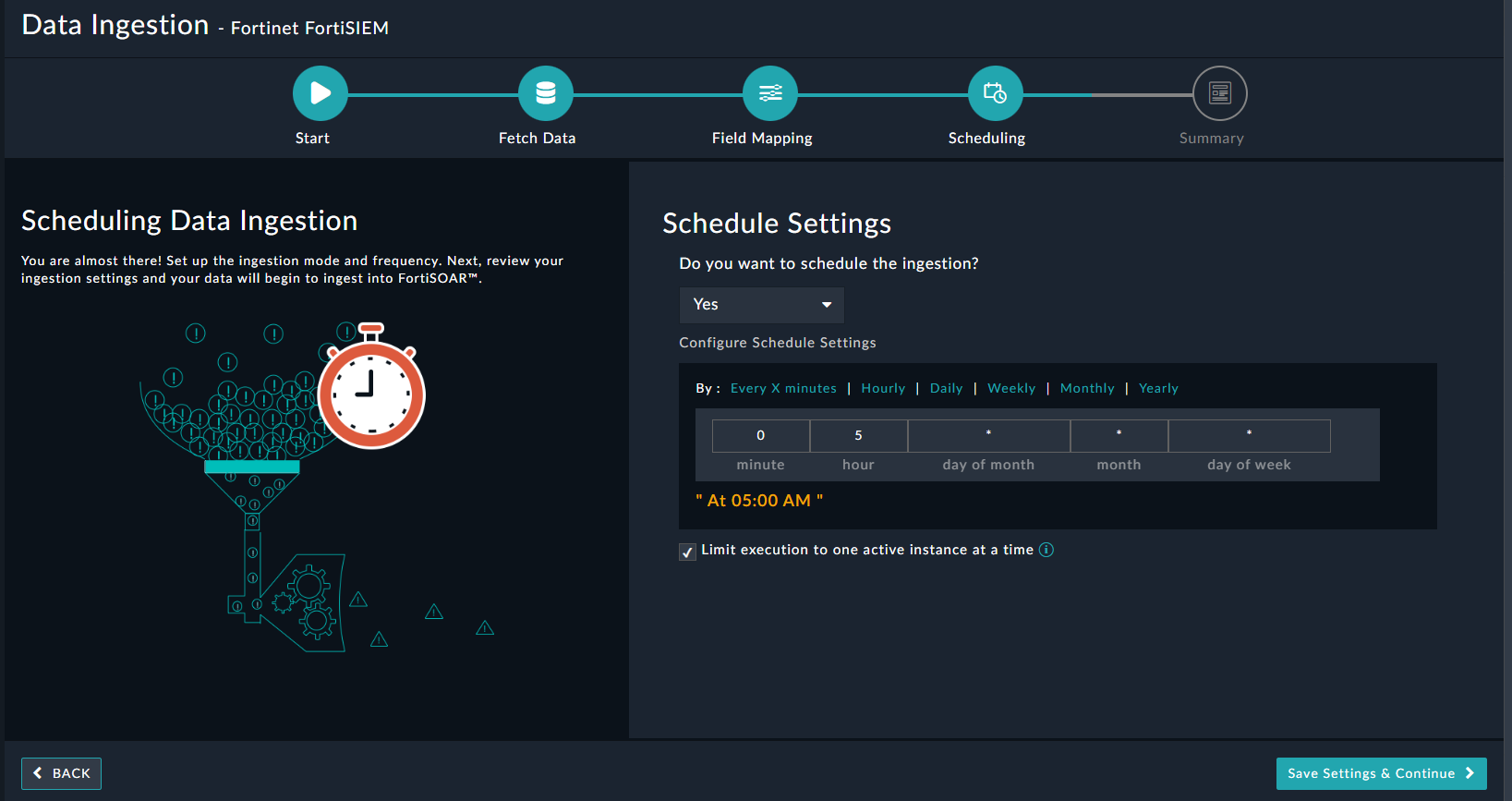
(Optional) Use the Scheduling screen to configure schedule-based ingestion, i.e., specify the polling frequency to FortiSIEM, so that the content gets pulled from the FortiSIEM integration into FortiSOAR™
On the Scheduling screen, from the Do to schedule the ingestion? drop-down list, select Yes.
In the Configure Schedule Settings section, specify the Cron expression, for example, if you want to pull data from FortiSIEM every morning at 5 a.m., click Daily, in the hour box enter 5, and in the minute box, enter 0:
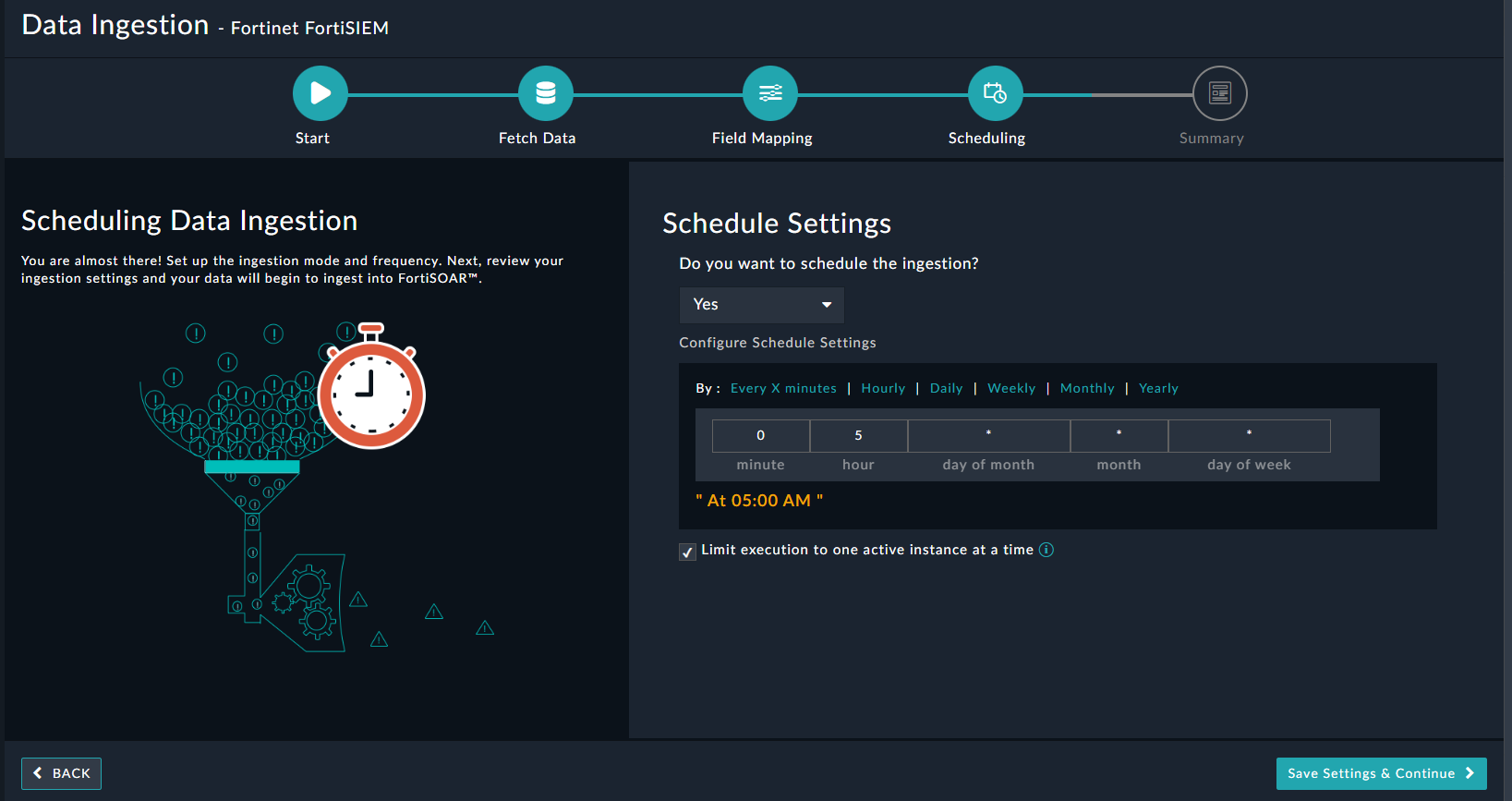
Once you have completed scheduling, click Save Settings & Continue.
- The Summary screen displays a summary of the mapping done, and it also contains links to the Ingestion playbooks. Click Done to complete the data ingestion and exit the Data Ingestion Wizard.
Best Practices - Working with FortiSOAR FortiSIEM Integration
Following is a list of recommendations and suggested best practices for working with the FortiSOAR FortiSIEM integration:
- As the number of incidents in FortiSIEM might be very high, it is suggested to only pull the incidents that are of importance and need to be worked upon. For example, incidents of certain types and certain severity. The ingestion experience allows the configuration of these filters to meet the right requirements.
- It is strongly suggested to use the Maximum Events To Pull Per Incident parameter to limit and only fetch required/latest events per incident.
- It is recommended to tune the ‘Maximum Incidents To Pull Or Size Per Page’ parameter to limit the incidents fetched per iteration. Tune this parameter based on your scheduler time and the average number of incidents being pulled (with some buffer for peaks).
- Various performance improvements are done with each important release of the connector, and hence it is suggested to upgrade to the latest version of the integration. Before upgrading, we strongly recommend reading the Release notes and the connector documentation to understand the upgrade requirements/precursors/compatibility.