About the connector
The FortiGate next-generation firewall platform (hardware and virtualized) is the heart of the Fortinet Security Fabric, which delivers true end-to-end network security. FortiGate firewalls are purpose-built with security processors to enable threat protection and performance for SSL-encrypted traffic. By providing granular visibility of applications, users, and IoT devices, these appliances are designed to identify issues quickly and intuitively.
This document provides information about the Fortinet FortiGate connector, which facilitates automated interactions, with a Fortinet FortiGate server using FortiSOAR™ playbooks. Add the Fortinet FortiGate connector as a step in FortiSOAR™ playbooks and perform automated operations, such as blocking or unblocking IP addresses, URLs, or applications, or retrieving a list of blocked IP addresses, URLs, or applications from the Fortinet FortiGate server.
Version information
Connector Version: 5.2.0
FortiSOAR™ Version Tested on: 7.2.0-914
Fortinet FortiGate Version Tested on: FortiGate VM64 v6.4.6 build1879
Authored By: Fortinet
Certified: Yes
Release Notes for version 5.2.0
Following enhancements have been made to the Fortinet FortiGate connector in version 5.2.0:
- Added the following new actions and playbooks
- Create User
- Get Users
- Update User
- Delete User
- Get System Events
- Get User Last Login Details
- Added support for IPv6 addresses in all the actions related to IP addresses.
- Fixed a bug that caused the 'Create Address Group' and 'Update Address Group' actions to ignore the VDOM input.
- Removed the unused input parameter 'VDOM' from the 'Execute Command' action.
Installing the connector
Use the Content Hub to install the connector. For the detailed procedure to install a connector, click here.
You can also use the following yum command as a root user to install connectors from an SSH session:
yum install cyops-connector-fortigate-firewall
Prerequisites to configuring the connector
- You must have the IP address or Hostname of the Fortinet FortiGate server to which you will connect and perform the automated operations and the API Key to access that server.
- The FortiSOAR™ server should have outbound connectivity to port 443 on Fortinet FortiGate.
- To block or unblock IP addresses, URLs, or applications, you need to add the necessary configuration to Fortinet FortiGate. See the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate section".
- Ensure the user has the permissions required for the actions you wish to perform in Fortinet FortiGate.
- To execute Fortinet FortiGate connector actions, the following minimal profile permissions are required:
- User and Device: Read and Write permissions.
- Firewall: Read and Write permissions for Policy, Address, and Service.
- Security Profile: Read and Write permissions for Web Filter and Application Control.
- Security Fabric - Read and Write permissions.
- WiFi & Switch - Read and Write permissions.
- Log & Report - Read and Write permissions.
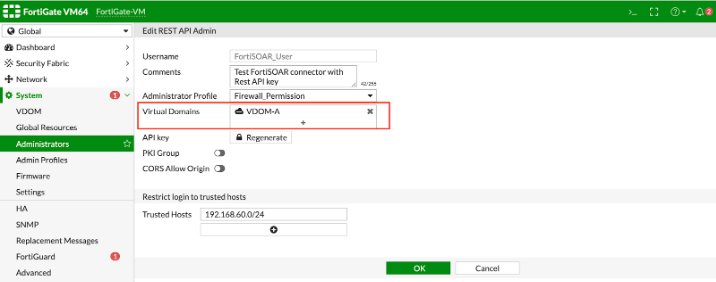
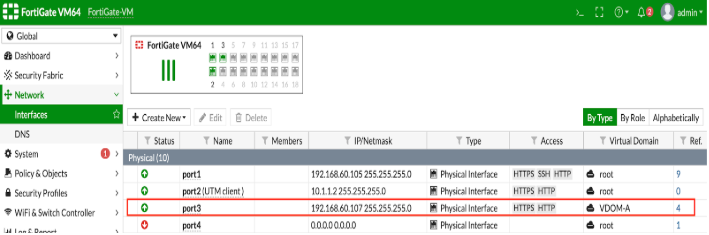
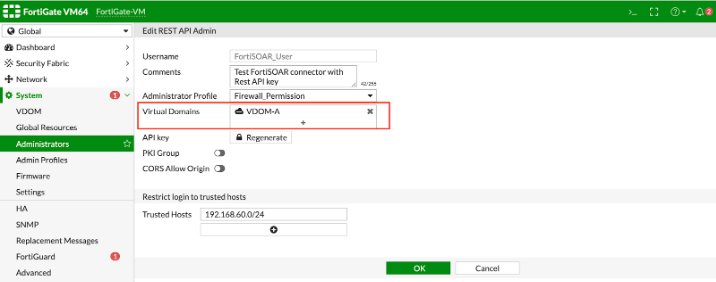
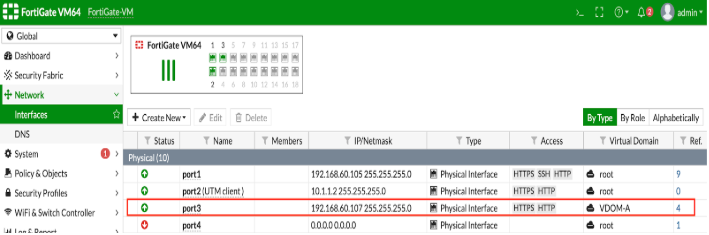
- VDOM is configured using a network interface in FortiGate which has its own IP address with different subnets (separate from "global' or "root" VDOM). When users select "VDOM" in the connector Configuration, users should specify the VDOM interface IP in the Hostname section, otherwise, an "Unauthorized Error" gets thrown. See the following screenshots for VDOM-specific connector configuration:
Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate
-
Log on to the Fortinet FortiGate server with the necessary credentials.
-
To block or unblock an IP address, you must create a policy for IP addresses on the Fortinet FortiGate server. The following steps define the process of adding a policy:
- In
Policy & Objects, click IPv4 Policy to create a policy for IPv4 with the following conditions.
Source = Blocked_IPs
Destination = Blocked_IPs
Schedule = always
Service = ALL
Action = DENY
Note: You can similarly create an IPv6 policy.
For more information on address group exclusions, see the FortiOS 6.2.3 Cookbook.
- In
Policy & Objects, click Addresses to create an address group with the following conditions.
Group Name = Blocked_IPs
Member = none
Show in address list = enable
For more information on creating address groups and address group exclusions, see the FortiOS 6.2.3 Cookbook.
- In
Policy & Objects, click IPv4 Policy and enter the IPv4 policy name as the Action parameter. For our example, we have named this as FortiSOAR_Blocked_Policy. When you are configuring your Fortinet FortiGate connector in FortiSOAR™, you must use the policy name that you have specified in this step as your IPv4 Block Policy action parameter.
For more information on IPv4 Policy, see IPv4 Policy in the FortiOS documentation.
- To block or unblock a URL, you must create a profile for blocking or unblocking static URLs on the Fortinet FortiGate server. For information on creating web filters, see Web Filter in the FortiOS 6.2.3 Cookbook.
The following steps define the process of adding a policy:
- In
Security Profiles, click Web Filter to create a new profile for blocking or unblocking static URLs or use the default profile.
Note: Ensure that the "URL Filter " is enabled.
- Enter the Web Filter Profile name on the configuration page. For our example, we have named this URL Block Policy. When you are configuring your Fortinet FortiGate connector in FortiSOAR™, you must use the Web Filter Profile name that you have specified in this step as your
Web Filter Profile Name configuration parameter.
-
To block or unblock an application, you must create a profile for blocking or unblocking applications on the Fortinet FortiGate server. The following steps define the process of adding a policy:
-
In Security Profiles, click Application Control to create a new profile for blocking or unblocking applications or use the default profile.
-
Enter the policy name on the configuration page. For our example, we have named this App Block Policy. When you are configuring your Fortinet FortiGate connector in FortiSOAR™, you must use the Application Control Profile name that you have specified in this step as your Application Control Profile Name configuration parameter.
For information on adding application controls, see Application Control in the FortiOS 6.2.3 Cookbook.
Configuring the connector
For the procedure to configure a connector, click here.
Configuration parameters
In FortiSOAR™, on the Content Hub (or Connector Store) page, click the Manage tab, and then click the Fortinet FortiGate connector card. On the connector popup, click the Configurations tab to enter the required configuration details:
| Parameter |
Description |
| Hostname |
IP address or Hostname of the Fortinet FortiGate endpoint server to which you will connect and perform the automated operations. |
| API Key |
API Key of the Fortinet FortiGate endpoint server to which you will connect and perform the automated operations. You can get the API key from the administration settings in FortiGate.
Important: To create a REST API key from Fortinet FortiGate, see the "Create a REST API administrator" section in the Fortinet FortiGate Documentation. |
| Port |
Port number used for connecting to the Fortinet FortiGate server. Defaults to 443. |
| Web Filter Profile Name |
Name of the Web Filter Profile that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter default in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section. |
| Application Control Profile Name |
Name of the Application Control Profile that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter default in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section. |
| VDOM |
VDOMs, in the CSV or List format, if the VDOM mode is enabled, to support operations related to IP addresses. |
| Verify SSL |
Specifies whether the SSL certificate for the server is to be verified or not. |
Actions supported by the connector
The following automated operations can be included in playbooks, and you can also use the annotations to access operations from release 4.10.0 onwards:
| Function |
Description |
Annotation and Category |
| Get Applications Detail |
Retrieves a list of all application names and associated details from the Fortinet FortiGate server. |
get_app_details
Investigation |
| Block URL |
Blocks URLs on Fortinet FortiGate using the Web Filter Profile Name Policy that you have specified while configuring Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section. |
block_url
Containment |
| Unblock URL |
Unblocks URLs on Fortinet FortiGate using the Web Filter Profile Name that you have specified while configuring Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section. |
unblock_url
Remediation |
| Block IP Address |
Blocks IP addresses on Fortinet FortiGate using the IPv4 Block Policy that you have specified as the "action" parameter of Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section. |
block_ip
Containment |
| Unblock IP Address |
Unblocks IP addresses on Fortinet FortiGate using the IPv4 Block Policy that you have specified as the "action" parameter of Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section. |
unblock_ip
Remediation |
| Block Application |
Blocks applications on Fortinet FortiGate using the Application Control Profile Name that you have specified while configuring Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section. |
block_app
Containment |
| Unblock Application |
Unblocks applications on Fortinet FortiGate using the Application Control Profile Name that you have specified while configuring Fortinet FortiGate. For more information see the "Blocking or Unblocking IP addresses, URLs, or applications in Fortinet FortiGate" section. |
unblock_app
Remediation |
| Get Blocked URLs |
Retrieves a list of URLs that are blocked on Fortinet FortiGate. |
get_blocked_url
Investigation |
| Get Blocked IP Addresses |
Retrieves a list of IP Addresses that are blocked on Fortinet FortiGate. |
get_blocked_ip
Investigation |
| Get Blocked Applications |
Retrieves a list of application names that are blocked on Fortinet FortiGate. |
get_blocked_app
Investigation |
| Quarantine Host |
Quarantines hosts on the Fortinet Fortigate server based on MAC addresses and other input parameters you have specified. |
quarantine_host
Containment |
| Unquarantine Host |
Unquaratines host entries from the Fortinet Fortigate server based on MAC addresses and other input parameters you have specified. |
unquarantine_host
Containment |
| Get Quarantine Hosts |
Retrieves a list of all quarantine hosts from Fortinet FortiGate. |
get_quarantine_hosts
Investigation |
| Create Address |
Create a new address in Fortinet FortiGate based on the name of the address, type, and other input parameters you have specified. |
create_address
Investigation |
| Get Addresses |
Retrieves a list of all addresses or specific addresses that are configured on Fortinet FortiGate based on the input parameters you have specified. |
get_addresses
Investigation |
| Update Address |
Update an existing address in Fortinet FortiGate based on the address name, type, and other input parameters you have specified. |
update_address
Investigation |
| Delete Address |
Deletes an address that is configured on Fortinet FortiGate based on the name of the address and other input parameters you have specified. |
delete_address
Investigation |
| Create Address Group |
Creates a new address group in Fortinet FortiGate based on the name of the address group, members of the group, and other input parameters you have specified. |
create_address_group
Investigation |
| Get Address Groups |
Retrieves a list of all address groups or specific address groups that are configured on Fortinet FortiGate based on the input parameters you have specified. |
get_address_groups
Investigation |
| Update Address Group |
Updates an existing address group in Fortinet FortiGate based on the name of the address group, members of the group, and other input parameters you have specified. |
update_address_group
Investigation |
| Delete Address Group |
Deletes an address group that is configured on Fortinet FortiGate based on the name of the address group and other input parameters you have specified. |
delete_address_group
Investigation |
| Create Service |
Create a new service in Fortinet FortiGate based on the name of the service and other input parameters you have specified. |
create_firewall_service
Investigation |
| Get Services |
Retrieves a list of all firewalls' services or specific services that are configured on Fortinet FortiGate based on the input parameters you have specified. |
get_firewall_services
Investigation |
| Update Service |
Creates an existing service in Fortinet FortiGate based on the name of the service and other input parameters you have specified. |
update_firewall_service
Investigation |
| Delete Service |
Deletes a firewall service that is configured on Fortinet FortiGate based on the name of the address group and other input parameters you have specified. |
delete_firewall_service
Investigation |
| Create Service Group |
Creates a new service group in Fortinet FortiGate based on the name of the service group, members of the group, and other input parameters you have specified. |
create_service_group
Investigation |
| Get Service Groups |
Retrieves a list of all service groups or specific service groups that are configured on Fortinet FortiGate based on the input parameters you have specified. |
get_service_groups
Investigation |
| Update Service Group |
Updates an existing service group in Fortinet FortiGate based on the name of the service group, members of the group, and other input parameters you have specified. |
update_service_group
Investigation |
| Delete Service Group |
Deletes a service group that is configured on Fortinet FortiGate based on the name of the service group and other input parameters you have specified. |
delete_service_group
Investigation |
| Create Policy |
Creates a new firewall policy in Fortinet FortiGate based on the name of the policy, names of the incoming and outgoing interfaces, and other input parameters you have specified. |
create_policy
Investigation |
| Get List of Policies |
Retrieves a list and details for all IPv4 policies or specific IPv4 policies that are configured on Fortinet FortiGate based on the input parameters you have specified. |
get_policies
Investigation |
| Update Policy |
Updates an existing firewall policy in Fortinet FortiGate based on the ID of the policy, names of the incoming and outgoing interfaces, and other input parameters you have specified. |
update_policy
Investigation |
| Delete Policy |
Deletes a policy that is configured on Fortinet FortiGate based on the ID of the policy and other input parameters you have specified. |
delete_policy
Investigation |
| Execute Command |
Executes a CLI command on the FortiOS console based on the commands and other input parameters you have specified. |
execute_command
Investigation |
| Create User |
Creates a new user in the Fortinet FortiGate server based on the username, authentication type, and other input parameters you have specified. |
create_user
Investigation |
| Get Users |
Retrieves a list of all users that are configured on Fortinet FortiGate based on the input parameters you have specified. |
get_users
Investigation |
| Update User |
Updates an existing user in the Fortinet FortiGate server based on the username, authentication type, and other input parameters you have specified. |
update_user
Investigation |
| Delete User |
Deletes a user who is configured on Fortinet FortiGate based on the name of the user you have specified. |
delete_user
Investigation |
| Get System Events |
Retrieves system log data from the Fortinet FortiGate server, based on the input parameters you have specified. |
get_system_events
Investigation |
| Get User Last Login Details |
Retrieves the last login details for a specified user from the Fortinet FortiGate server, based on the username you have specified. |
get_user_list_login_details
Investigation |
operation: Get Applications Detail
Input parameters
None.
Output
The JSON output retrieves a list of all application names and associated details from the Fortinet FortiGate server.
The output contains the following populated JSON schema:
{
"path": "",
"vdom": "",
"name": "",
"http_method": "",
"http_status": "",
"results": [
{
"q_type": "",
"vendor": "",
"q_name": "",
"sub-category": "",
"popularity": "",
"q_class": "",
"protocol": "",
"id": "",
"q_origin_key": "",
"q_path": "",
"weight": "",
"q_mkey_type": "",
"parameter": "",
"q_ref": "",
"name": "",
"q_no_rename": "",
"behavior": "",
"risk": "",
"category": "",
"metadata": [
{
"id": "",
"valueid": "",
"q_origin_key": "",
"metaid": ""
}
],
"technology": "",
"q_static": ""
}
],
"build": "",
"serial": "",
"version": "",
"revision": "",
"status": ""
}
operation: Block URL
Input parameters
| Parameter |
Description |
| URL |
List of URLs that you want to block on Fortinet FortiGate. URLs must be in the list format if you want to block more than one URL. For example, for a list of URLs, enter: [\"URL1\", \"URL2\"] in this field. For a single URL enter: /'example.com/' |
| VDOM |
(Optional) VDOM on which you want to perform automated operations i.e, the VDOM whose associated URLs you want to block in FortiGate. The VDOM mode should be enabled and you can specify only a single VDOM value in this field.
Note: You can specify the VDOM here as a configuration parameter or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. |
Output
The JSON output contains a status message of whether or not the URL is successfully blocked on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"already_blocked": [],
"newly_blocked": [],
"not_block": []
}
operation: Unblock URL
Input parameters
| Parameter |
Description |
| URL |
List of URLs that you want to unblock on Fortinet FortiGate. URLs must be in the list format if you want to unblock more than one URL. For example, for a list of URLs, enter: [\"URL1\", \"URL2\"] in this field. For a single URL enter: /'example.com/' |
| VDOM |
(Optional) VDOM on which you want to perform automated operations i.e, the VDOM whose associated URLs you want to unblock in FortiGate. The VDOM mode should be enabled and you can specify only a single VDOM value in this field.
Note: You can specify the VDOM here as a configuration parameter or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. |
Output
The JSON output contains a status message of whether or not the URL is successfully unblocked on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"already_blocked": [],
"newly_blocked": [],
"not_block": []
}
operation: Block IP Address
Input parameters
| Parameter |
Description |
| Block Method |
Method to be used for blocking IP addresses using Fortinet FortiGate. You can choose from Quarantine Based or Policy Based.
- If you choose Quarantine Based, then you must specify the following parameters:
- IP Addresses: IP addresses that you want to block using Fortinet FortiGate, in the "CSV" or "list" format. For example,
["1.1.1.1", "2.2.2.2"] or "1.1.1.1", "2.2.2.2".
- Time to Live: Time till when the IP addresses will remain in the
Block status. You can choose between the following options: 1 Hour, 6 Hour, 12 Hour, 1 Day, 6 Months, 1 Year, or Custom Time.
Note: If you select Custom Time then the Time to Live (Seconds) field is displayed in which you must specify the Time to Live in seconds.
- If you choose Policy Base, then you must specify the following parameters:
- Policy Name: Name of the Policy that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter FortiSOAR_Blocked_Policy in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section.
- IP Type: Type of IP that you want to block on the FortiOS server. You can choose between IPv4 and IPv6.
For both IPv4 and IPv6, you must specify the following parameters:
- Address Group Name: Name of the IP address group name that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter Blocked_IPs in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section.
- IP Address (for IPv4) or IPv6 Addresses (for IPv6): IP addresses that you want to block using Fortinet FortiGate in the "CSV" or "list" format.
For IPv4 the format of IP addresses is: ["1.1.1.1", "2.2.2.2"] or "1.1.1.1", "2.2.2.2"
For IPv6 the format of IP addresses is: ff06::/120
|
| VDOM |
(Optional) VDOM that are used to block IP addresses.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The JSON output contains a status message of whether or not the IP Address is successfully blocked on Fortinet FortiGate.
When you choose “Quarantine Based” as the Block Method, then the output contains the following populated JSON schema:
{
"newly_blocked": [],
"already_blocked": [],
"vdom_not_exist": [],
"error_with_block": []
}
When you choose “Policy Based” as the Block Method, then the output contains the following populated JSON schema:
{
"newly_blocked": [],
"already_blocked": [],
"error_with_block": []
}
operation: Unblock IP Address
Input parameters
| Parameter |
Description |
| Block Method |
Method to be used for unblocking IP addresses using Fortinet FortiGate. You can choose from Quarantine Based or Policy Based.
- If you choose Quarantine Based, then you must specify the following parameters:
- IP Addresses: IP addresses that you want to unblock using Fortinet FortiGate, in the "CSV" or "list" format. For example,
["1.1.1.1", "2.2.2.2"] or "1.1.1.1", "2.2.2.2".
- If you choose Policy Based, then you must specify the following parameters:
- Policy Name: Name of the Policy that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter FortiSOAR_Blocked_Policy in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section.
- IP Type: Type of IP that you want to block on the FortiOS server. You can choose between IPv4 and IPv6.
For both IPv4 and IPv6, you must specify the following parameters:
- Address Group Name: Name of the IP address group name that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter Blocked_IPs in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section.
- IP Address (for IPv4) or IPv6 Addresses (for IPv6): : IP addresses that you want to unblock using Fortinet FortiGate in the "CSV" or "list" format.For IPv4 the format of IP addresses is:
["1.1.1.1", "2.2.2.2"] or "1.1.1.1", "2.2.2.2"
For IPv6 the format of IP addresses is: ff06::/120
|
| VDOM |
(Optional) VDOM that is used to unblock IP addresses.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The JSON output contains a status message of whether or not the IP Address is successfully unblocked on Fortinet FortiGate.
When you choose “Quarantine Based” as the Unblock Method, then the output contains the following populated JSON schema:
{
"newly_unblocked": [],
"ip_not_exist": [],
"vdom_not_exist": [],
"error_with_unblock": []
}
When you choose “Policy Based” as the Unblock Method, then the output contains the following populated JSON schema:
{
"not_exist": [],
"newly_unblocked": [],
"error_with_unblock": []
}
operation: Block Application
Input parameters
| Parameter |
Description |
| Application Names |
List of application names that you want to block on Fortinet FortiGate. Application names must be in the list format if you want to block more than one application.
For example, for a list of applications enter ["Application_Name1", "Application_Name2"] in this field.
For a single application enter Application_Name.
Note: You can retrieve application names using the “Get Application Details” action. |
| VDOM |
(Optional) VDOM on which you want to perform automated operations i.e, the VDOM whose associated applications you want to block in FortiGate. The VDOM mode should be enabled and you can specify only a single VDOM value in this field.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. |
Output
The JSON output contains a status message of whether or not the application(s) are successfully blocked on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"message": "",
"name": "",
"status": ""
}
operation: Unblock Application
Input parameters
| Parameter |
Description |
| Application Names |
List of application names that you want to block on Fortinet FortiGate. Application names must be in the list format if you want to unblock more than one application.
For example, for a list of applications enter ["Application_Name1", "Application_Name2"] in this field.
For a single application enter Application_Name. |
| VDOM |
(Optional) VDOM on which you want to perform automated operations i.e, the VDOM whose associated applications you want to unblock in FortiGate. The VDOM mode should be enabled and you can specify only a single VDOM value in this field.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. |
Output
The JSON output contains a status message of whether or not the application(s) are successfully unblocked on Fortinet FortiGate.
The output contains the following populated JSON schema:
{
"message": "",
"name": "",
"status": ""
}
operation: Get Blocked URLs
Input parameters
| Parameter |
Description |
| VDOM |
(Optional) VDOM on which you want to perform automated operations, i.e., the VDOM whose associated list of blocked URLs you want to retrieve from Fortinet FortiGate.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The JSON output retrieves a list of URLs that are blocked using the Web Filter Profile Name that you have configured.
The output contains the following populated JSON schema:
{
"exempt": "",
"referrer-host": "",
"web-proxy-profile": "",
"url": "",
"q_origin_key": "",
"id": "",
"status": "",
"dns-address-family": "",
"action": "",
"type": ""
}
operation: Get Blocked IP Addresses
Input parameters
| Parameter |
Description |
| Block Method |
Method to be used for retrieving a list of IP Addresses that are blocked on Fortinet FortiGate. You can choose from Quarantine Based or Policy Based.
- If you choose Policy Based, then you can specify the following parameters:
- Policy Name: Name of the Policy that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses and whose associated list of blocked IP addresses you want to retrieve from Fortinet FortiGate. Based on our example, enter FortiSOAR_Blocked_Policy in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section.
- Address Group Name: Name of the IP address group name that you have specified in Fortinet FortiGate for blocking or unblocking IP addresses. Based on our example, enter Blocked_IPs in this field. See the Blocking or Unblocking IP addresses, URLs, or applications in the Fortinet FortiGate section.
|
| VDOM |
(Optional) VDOMs whose associated list of blocked IP addresses you want to retrieve from Fortinet FortiGate.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The JSON output retrieves a list of IP Addresses that are blocked using the IP Block Policy that you have configured.
When you choose “Quarantine Based” as the method to be used for retrieving a list of IP Addresses that are blocked on Fortinet FortiGate, then the output contains the following populated JSON schema:
{
"result": [
{
"name": "",
"path": "",
"serial": "",
"http_method": "",
"status": "",
"results": [
{
"ipv6": "",
"source": "",
"created": "",
"ip_address": "",
"expires": ""
}
],
"build": "",
"version": "",
"vdom": ""
}
],
"vdom_not_exist": []
}
When you choose “Policy Based” as the Block Method, as the method to be used for retrieving a list of IP Addresses that are blocked on Fortinet FortiGate, then the output contains a list of blocked IP addresses.
{
"dstaddr": [],
"srcaddr": [],
"addrgrp": [
{
"name": "",
"member": []
}
],
"addrgrp_not_exist": [],
"policy_name": ""
}
operation: Get Blocked Applications
Input parameters
| Parameter |
Description |
| VDOM |
(Optional) VDOM on which you want to perform automated operations, i.e., the VDOM whose associated list of blocked applications you want to retrieve from Fortinet FortiGate. The VDOM mode should be enabled and you can specify only a single VDOM value in this field. Ensure that the specified VDOM contains the required \"Application Control Profile Name\" to execute the action.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. |
Output
The JSON output retrieves a list of application names that are blocked using the Application Control Profile Name that you have configured.
The output contains the following populated JSON schema:
{
"popularity": "",
"risk": "",
"q_global_entry": "",
"q_no_rename": false,
"protocol": "",
"q_origin_key": "",
"metadata": [
{
"id": "",
"metaid": "",
"q_origin_key": "",
"valueid": ""
}
],
"q_mkey_type": "",
"weight": "",
"q_static": true,
"q_path": "",
"parameter": "",
"vendor": "",
"name": "",
"q_class": "",
"category": "",
"q_type": "",
"q_name": "",
"q_ref": "",
"id": "",
"behavior": "",
"sub-category": "",
"technology": ""
}
operation: Quarantine Host
Input parameters
| Parameter |
Description |
| MAC Address |
List of MAC addresses of the hosts you want to quarantine on Fortinet FortiGate. For example, 00:15:00:e8:27:25 or ['00:15:00:e8:27:25', '00:15:00:e8:27:26'] |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"already_quarantine": [],
"newly_quarantine": [],
"not_quarantine": []
}
operation: Unquarantine Host
Input parameters
| Parameter |
Description |
| MAC Address |
List of MAC addresses of the hosts whose entries you want to remove from the quarantine on Fortinet FortiGate. For example, 00:15:00:e8:27:25 or ['00:15:00:e8:27:25', '00:15:00:e8:27:26'] |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"not_exist": [],
"newly_unquarantine": [],
"not_unquarantine": []
}
operation: Get Quarantine Hosts
Input parameters
| Parameter |
Description |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"results": {
"targets": [
{
"macs": [
{
"mac": "",
"drop": "",
"parent": "",
"entry-id": "",
"description": "",
"q_origin_key": ""
}
],
"entry": "",
"description": "",
"q_origin_key": ""
}
],
"quarantine": "",
"traffic-policy": "",
"firewall-groups": ""
},
"version": "",
"revision": "",
"http_method": "",
"http_status": ""
}
operation: Create Address
Input parameters
| Parameter |
Description |
| Address Category |
Select the category of address you want to create in Fortinet FortiGate. You can choose between IPv4 and IPv6. |
| Address Name |
The name of the address that you want to create in Fortinet FortiGate. |
| Type |
The type of address that you want to create in Fortinet FortiGate. You can choose from the following options based on the address category you have selected: Subnet (for IPv4) or IPv6 Subnet (for IPv6), IP Range (for IPv4) or IPv6 Range (for IPv6), FQDN (for IPv4) or IPv6 FQDN (for IPv6), Geography (for IPv4) or IPv6 Geography (for IPv6), or Device (MAC Address) applicable to both IPv4 and IPv6. In the case of IPv6, we have two additional types, i.e., IPv6 Fabric Connector Address and IPv6 Template.
If you choose 'Subnet' or 'IPv6 Subnet', then you must specify the following parameters:
- IP/Netmask: IP address or Netmask name of the address that you want to create in Fortinet FortiGate.
- Static Route Configuration: Select the Enable option to enable usage of this address in the static route configuration, else select Disable.
If you choose 'IP Range' or 'IPv6 IP Range', then you must specify the following parameters:
- Start IP: Starting (First) IP address (inclusive) in the range for the address to be added to the address that you want to create in Fortinet FortiGate.
- End IP: Ending (Final) IP address (inclusive) in the range for the address to be added to the address that you want to create in Fortinet FortiGate.
- Static Route Configuration: Select the Enable option to enable usage of this address in the static route configuration, else select Disable.
If you choose 'FQDN' or 'IPv6 FQDN', then you must specify the following parameters:
- FQDN: Fully Qualified Domain Name address of the address that you want to create in Fortinet FortiGate.
- Static Route Configuration: Select the Enable option to enable usage of this address in the static route configuration, else select Disable.
If you choose 'Geography' or 'IPv6 Geography', then you must specify the following parameters:
- Country/Region: Select the country whose IP addresses you want to associate with the address that you want to create in Fortinet FortiGate.
If you choose 'Device (MAC Address)', then you must specify the following parameters:
- MAC Address Scope: Select the MAC Address Scope to be associated with the address that you want to create in Fortinet FortiGate. You can choose between Single Address or Address Range.
- If you choose 'Single Address', then you must specify the following parameters:
-
- MAC Address: MAC Address that you want to add to the address that you want to create in Fortinet FortiGate. For example,
00:15:00:e8:27:25
- If you choose 'Address Range', then you must specify the following parameters:
- Starting MAC: Starting (First) MAC address in the range for the address to be added to the address that you want to create in Fortinet FortiGate. For example,
00:15:00:e8:27:25
- Ending MAC: Ending (Final) MAC address in the range for the address to be added to the address that you want to create in Fortinet FortiGate. For example,
00:15:00:e8:27:27
If you choose 'IPv6 Fabric Connector Address' (only applicable to IPv6)
- SDN Connector: Name of the SDN connector you want to associate with the address that you want to create in Fortinet FortiGate.
If you choose 'IPv6 Template' (only applicable to IPv6)
- IPv6 Address Template: IPv6 Address Template using which you want to create the address in Fortinet FortiGate.
|
| Comments |
(Optional) Comment to be added to the address that you want to create in Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"mkey": "",
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"version": "",
"revision": "",
"http_method": "",
"http_status": "",
"old_revision": "",
"revision_changed": ""
}
operation: Get Addresses
Input parameters
Note: All the input parameters are optional. However, if you do not specify any parameter, then no filter criterion is applied and an unfiltered list (of addresses) is returned.
| Parameter |
Description |
| Address Category |
Select the category of address you want to retrieve from Fortinet FortiGate. You can choose between IPv4 and IPv6. |
| Address Name |
The name of the address whose details you want to retrieve from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"results": [
{
"name": "",
"q_origin_key": "",
"uuid": "",
"subnet": "",
"type": "",
"sub-type": "",
"clearpass-spt": "",
"start-mac": "",
"end-mac": "",
"country": "",
"cache-ttl": "",
"sdn": "",
"fsso-group": [],
"interface": "",
"obj-type": "",
"comment": "",
"associated-interface": "",
"color": "",
"filter": "",
"sdn-addr-type": "",
"obj-id": "",
"list": [],
"tagging": [],
"allow-routing": "",
"fabric-object": ""
}
],
"vdom": "",
"path": "",
"name": "",
"mkey": "",
"status": "",
"http_status": "",
"serial": "",
"version": "",
"build": ""
}
operation: Update Address
Input parameters
| Parameter |
Description |
| Address Category |
Select the category of address you want to update in Fortinet FortiGate. You can choose between IPv4 and IPv6. |
| Address Name |
The name of the address that you want to update in Fortinet FortiGate. |
| Type |
The type of address that you want to update in Fortinet FortiGate. You can choose from the following options based on the address category you have selected: Subnet (for IPv4) or IPv6 Subnet (for IPv6), IP Range (for IPv4) or IPv6 Range (for IPv6), FQDN (for IPv4) or IPv6 FQDN (for IPv6), Geography (for IPv4) or IPv6 Geography (for IPv6), or Device (MAC Address) applicable to both IPv4 and IPv6. In the case of IPv6, we have two additional types, i.e., IPv6 Fabric Connector Address and IPv6 Template.
If you choose 'Subnet' or 'IPv6 Subnet', then you must specify the following parameters:
- IP/Netmask: IP address or Netmask name of the address that you want to update in Fortinet FortiGate.
- Static Route Configuration: Select the Enable option to enable usage of this address in the static route configuration, else select Disable.
If you choose 'IP Range' or 'IPv6 IP Range', then you must specify the following parameters:
- Start IP: Starting (First) IP address (inclusive) in the range for the address to be added to the address that you want to update in Fortinet FortiGate.
- End IP: Ending (Final) IP address (inclusive) in the range for the address to be added to the address that you want to update in Fortinet FortiGate.
- Static Route Configuration: Select the Enable option to enable usage of this address in the static route configuration, else select Disable.
If you choose 'FQDN' or 'IPv6 FQDN', then you must specify the following parameters:
- FQDN: Fully Qualified Domain Name address of the address that you want to update in Fortinet FortiGate.
- Static Route Configuration: Select the Enable option to enable usage of this address in the static route configuration, else select Disable.
If you choose 'Geography' or 'IPv6 Geography', then you must specify the following parameters:
- Country/Region: Select the country whose IP addresses you want to associate with the address that you want to update in Fortinet FortiGate.
If you choose 'Device (MAC Address)', then you must specify the following parameters:
- MAC Address Scope: Select the MAC Address Scope to be associated with the address that you want to update in Fortinet FortiGate. You can choose between Single Address or Address Range.
- If you choose 'Single Address', then you must specify the following parameters:
-
- MAC Address: MAC Address that you want to add to the address that you want to update in Fortinet FortiGate. For example,
00:15:00:e8:27:25
- If you choose 'Address Range', then you must specify the following parameters:
- Starting MAC: Starting (First) MAC address in the range for the address to be added to the address that you want to update in Fortinet FortiGate. For example,
00:15:00:e8:27:25
- Ending MAC: Ending (Final) MAC address in the range for the address to be added to the address that you want to update in Fortinet FortiGate. For example,
00:15:00:e8:27:27
If you choose 'IPv6 Fabric Connector Address' (only applicable to IPv6)
- SDN Connector: Name of the SDN connector you want to associate with the address that you want to update in Fortinet FortiGate.
If you choose 'IPv6 Template' (only applicable to IPv6)
- IPv6 Address Template: IPv6 Address Template using which you want to update the address in Fortinet FortiGate.
|
| New Address Name |
(Optional) Specify a new name for the address if you want to update its name in Fortinet FortiGate. |
| Comments |
(Optional) Comment to be added to the address that you want to update in Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"mkey": "",
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"version": "",
"revision": "",
"http_method": "",
"http_status": "",
"old_revision": "",
"revision_changed": ""
}
operation: Delete Address
Input parameters
| Parameter |
Description |
| Address Category |
Select the category of address you want to update in Fortinet FortiGate. You can choose between IPv4 and IPv6. |
| Address Name |
The name of the address that you want to delete from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"mkey": "",
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"version": "",
"revision": "",
"http_method": "",
"http_status": "",
"old_revision": "",
"revision_changed": ""
}
operation: Create Address Group
Input parameters
| Parameter |
Description |
| Address Group Category |
Select the category of address group you want to create in Fortinet FortiGate. You can choose between IPv4 and IPv6.
If you choose IPv4, then you must specify the following parameters:
- Group Name: Name of address group that you want to create in Fortinet FortiGate.
- Members: List of IP addresses or URLs to add to the address group you want to create in Fortinet FortiGate.
- Type: Type of address group that you want to create in Fortinet FortiGate. You can choose between Group or Folder.
- Group: This is the default address group type (address might belong to multiple groups).
- Folder: The address folder group (members cannot belong to any other group).
- Select this checkbox, i.e., set it to True, to enable address exclusion. If you select this checkbox, then in the Exclude Members field, specify the list of IP addresses or URLs that you want to add to the exclusion list in Fortinet FortiGate.
If you choose IPv6, then you must specify the following parameters:
- Group Name: Name of address group that you want to create in Fortinet FortiGate.
- Members: List of IP addresses or URLs to add to the address group you want to create in Fortinet FortiGate.
|
| Comments |
(Optional) Comment to be added to the address group that you want to create in Fortinet FortiGate. |
| Static Route Configuration |
Select the Enable option to enable usage of this address group in the static route configuration, else select Disable. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Get Address Groups
Input parameters
Note: All the input parameters are optional. However, if you do not specify any parameter, then no filter criterion is applied and an unfiltered list (of address groups) is returned.
| Parameter |
Description |
| Address Group Category |
Select the category of address group whose details you want to retrieve from Fortinet FortiGate. You can choose between IPv4 and IPv6. |
| Address Group Name |
The name of the address group whose details you want to retrieve from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"results": [
{
"name": "",
"q_origin_key": "",
"type": "",
"uuid": "",
"member": [
{
"name": "",
"q_origin_key": ""
},
{
"name": "",
"q_origin_key": ""
},
{
"name": "",
"q_origin_key": ""
}
],
"comment": "",
"exclude": "",
"exclude-member": [],
"color": "",
"tagging": [],
"allow-routing": "",
"fabric-object": ""
}
],
"vdom": "",
"path": "",
"name": "",
"mkey": "",
"status": "",
"http_status": "",
"serial": "",
"version": "",
"build": ""
}
operation: Update Address Group
Input parameters
| Parameter |
Description |
| |
Select the category of address group you want to update in Fortinet FortiGate. You can choose between IPv4 and IPv6.
If you choose IPv4, then you must specify the following parameters:
- Group Name: Name of address group you want to update in Fortinet FortiGate.
- New Group Name: (Optional) Specify a new name for the address if you want to update its name in Fortinet FortiGate.
- Add Members: List of IP addresses or URLs to add to the address group you want to update in Fortinet FortiGate.
- Remove Members: List of IP addresses or URLs to remove from the address group you want to update in Fortinet FortiGate.
- Exclude: Select this checkbox, i.e., set it to True, to enable address exclusion. If you select this checkbox, then you must specify the following parameters:
- Add Exclude Members: Specify the list of IP addresses or URLs that you want to add to the exclusion list in Fortinet FortiGate.
- Remove Exclude Members: Specify the list of IP addresses or URLs that you want to remove from the exclusion list in Fortinet FortiGate.
- Comments: (Optional) Comment to be added to the address group you want to update in Fortinet FortiGate.
- Static Route ConfigurationSelect the Enable option to enable usage of this address group in the static route configuration, else select Disable.
If you choose IPv6, then you must specify the following parameters:
- Group Name: Name of address group you want to update in Fortinet FortiGate.
- New Group Name: (Optional) Specify a new name for the address if you want to update its name in Fortinet FortiGate.
- Add Members: List of IP addresses or URLs to add to the address group you want to update in Fortinet FortiGate.
- Remove Members: List of IP addresses or URLs to remove from the address group you want to update in Fortinet FortiGate.
- Comments: (Optional) Comment to be added to the address group you want to update in Fortinet FortiGate.
|
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Delete Address Group
Input parameters
| Parameter |
Description |
| Address Group Category |
Select the category of address group that you want to delete from Fortinet FortiGate. You can choose between IPv4 and IPv6. |
| Address Group Name |
Name of address group that you want to delete from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Create Service
Input parameters
| Parameter |
Description |
| Name |
Name of the service that you want to create in Fortinet FortiGate. |
| Category |
Category of the service that you want to create in Fortinet FortiGate. For example, Email, Authentication, General, Remote Access, etc. |
| Protocol |
Type of protocol based on IANA numbers of the service that you want to create in Fortinet FortiGate. You can choose between TCP/UDP/SCTP, ICMP, ICMP6. IP, HTTP, FTP, CONNECT, SOCKS-TCP, SOCKS-UDP, or ALL
If you select 'TCP/UDP/SCTP' then you must specify the following parameters:
- Address: Type of address to associate with the service that you want to create in Fortinet FortiGate. You can choose from IP Range or FQDN
- If you choose 'IP Range', then in the IP Range field, specify the starting and ending IP addresses that constitute the IP range associated with the service. For example,
0.0.0.0-0.0.0.10
- FQDN: Specify the Fully qualified domain name associated with the service.
- TCP Port Range: Specify multiple TCP port ranges associated with the service. For example,
0-22:55-75 55-77:88-100 in the format of 'TCP Port Low-TCP Port High:Source Port Low-Source Port High'
- UDP Port Range: Multiple UDP port ranges associated with the service. For example,
0-22:55-75 55-77:88-100 in the format of 'UDP Port Low-UDP Port High:Source Port Low-Source Port High'
- SCTP Port Range: Multiple SCTP port ranges associated with the service. For example,
0-22:55-75 55-77:88-100 in the format of 'SCTP Port Low-SCTP Port High:Source Port Low-Source Port High'
If you select 'ICMP' then you must specify the following parameters:
- Type: Type of ICMP to associate with the service that you want to create in Fortinet FortiGate.
- Code: ICMP Code to associate with the service that you want to create in Fortinet FortiGate. Maximum: 255 Minimum: 0
If you select 'ICMP6' then you must specify the following parameters:
- Type: Type of ICMP6 to associate with the service that you want to create in Fortinet FortiGate.
- Code: ICMP6 Code to associate with the service that you want to create in Fortinet FortiGate. Maximum: 255 Minimum: 0
If you select 'IP' then you must specify the following parameters:
- Protocol Number: Protocol Number of the IP you want to associate with the service to be created in Fortinet FortiGate. Maximum: 254 Minimum: 0
|
| Comments |
(Optional) Comment to be added to the service that you want to create in Fortinet FortiGate. |
| Show in Service List |
Select the Enable option to enable the visibility of the service on the GUI, else select Disable.
|
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Get Services
Input parameters
Note: All the input parameters are optional. However, if you do not specify any parameter, then no filter criterion is applied and an unfiltered list (of services) is returned.
| Parameter |
Description |
| Name |
The name of the service whose details you want to retrieve from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"results": [
{
"name": "",
"q_origin_key": "",
"proxy": "",
"category": "",
"protocol": "",
"helper": "",
"iprange": "",
"fqdn": "",
"tcp-portrange": "",
"udp-portrange": "",
"sctp-portrange": "",
"tcp-halfclose-timer": "",
"tcp-halfopen-timer": "",
"tcp-timewait-timer": "",
"udp-idle-timer": "",
"session-ttl": "",
"check-reset-range": "",
"comment": "",
"color": "",
"visibility": "",
"app-service-type": "",
"app-category": [],
"application": [],
"fabric-object": ""
}
],
"vdom": "",
"path": "",
"name": "",
"mkey": "",
"status": "",
"http_status": "",
"serial": "",
"version": "",
"build": ""
}
operation: Update Service
Input parameters
| Parameter |
Description |
| Name |
Name of the service that you want to update in Fortinet FortiGate. |
| New Name |
(Optional) Specify a new name for the service if you want to update its name in Fortinet FortiGate. |
| Category |
Category of the service that you want to create in Fortinet FortiGate. For example, Email, Authentication, General, Remote Access, etc. |
| Protocol |
Type of protocol based on IANA numbers of the service that you want to update in Fortinet FortiGate. You can choose between TCP/UDP/SCTP, ICMP, ICMP6. IP, HTTP, FTP, CONNECT, SOCKS-TCP, SOCKS-UDP, or ALL
If you select 'TCP/UDP/SCTP' then you must specify the following parameters:
- Address: Type of address to associate with the service that you want to update in Fortinet FortiGate. You can choose from IP Range or FQDN
- If you choose 'IP Range', then in the IP Range field, specify the starting and ending IP addresses that constitute the IP range associated with the service. For example,
0.0.0.0-0.0.0.10
- FQDN: Specify the Fully qualified domain name associated with the service.
- TCP Port Range: Specify multiple TCP port ranges associated with the service. For example,
0-22:55-75 55-77:88-100 in the format of 'TCP Port Low-TCP Port High:Source Port Low-Source Port High'
- UDP Port Range: Multiple UDP port ranges associated with the service. For example,
0-22:55-75 55-77:88-100 in the format of 'UDP Port Low-UDP Port High:Source Port Low-Source Port High'
- SCTP Port Range: Multiple SCTP port ranges associated with the service. For example,
0-22:55-75 55-77:88-100 in the format of 'SCTP Port Low-SCTP Port High:Source Port Low-Source Port High'
If you select 'ICMP' then you must specify the following parameters:
- Type: Type of ICMP to associate with the service that you want to update in Fortinet FortiGate.
- Code: ICMP Code to associate with the service that you want to update in Fortinet FortiGate. Maximum: 255 Minimum: 0
If you select 'ICMP6' then you must specify the following parameters:
- Type: Type of ICMP6 to associate with the service that you want to update in Fortinet FortiGate.
- Code: ICMP6 Code to associate with the service that you want to update in Fortinet FortiGate. Maximum: 255 Minimum: 0
If you select 'IP' then you must specify the following parameters:
- Protocol Number: Protocol Number of the IP you want to associate with the service to be updated in Fortinet FortiGate. Maximum: 254 Minimum: 0
|
| Comments |
(Optional) Comment to be added to the service that you want to update in Fortinet FortiGate. |
| Show in Service List |
Select the Enable option to enable the visibility of the service on the GUI, else select Disable. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Delete Service
Input parameters
| Parameter |
Description |
| Name |
Name of the service that you want to delete from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Create Service Group
Input parameters
| Parameter |
Description |
| Name |
Name of the service group that you want to create in Fortinet FortiGate. |
| Members |
List of members to add to the service group you want to create in Fortinet FortiGate. |
| Comments |
(Optional) Comment to be added to the service group that you want to create in Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Get Service Groups
Input parameters
Note: All the input parameters are optional. However, if you do not specify any parameter, then no filter criterion is applied and an unfiltered list (of service groups) is returned.
| Parameter |
Description |
| Name |
The name of the service group whose details you want to retrieve from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"results": [
{
"name": "",
"q_origin_key": "",
"proxy": "",
"member": [
{
"name": "",
"q_origin_key": ""
}
],
"comment": "",
"color": "",
"fabric-object": ""
}
],
"vdom": "",
"path": "",
"name": "",
"status": "",
"http_status": "",
"serial": "",
"version": "",
"build": ""
}
operation: Update Service Group
Input parameters
| Parameter |
Description |
| Name |
Name of the service group that you want to update in Fortinet FortiGate. |
| New Name |
(Optional) Specify a new name for the service group if you want to update its name in Fortinet FortiGate. |
| Add Members |
List of members to add to the service group you want to update in Fortinet FortiGate. |
| Remove Members |
List of members to remove from the service group you want to update in Fortinet FortiGate. |
| Comments |
(Optional) Comment to be added to the service group that you want to update in Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Delete Service Group
Input parameters
| Parameter |
Description |
| Name |
Name of the service group that you want to delete from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Create Policy
Input parameters
| Parameter |
Description |
| Policy Name |
Name of policy that you want to create in Fortinet FortiGate. |
| Incoming Interface |
Names of the incoming interfaces associated with the policy that you want to create in Fortinet FortiGate. For example port1. |
| Outgoing Interface |
Names of the outgoing interfaces associated with the policy that you want to create in Fortinet FortiGate. For example port2. |
| Source |
Source IPv4 address and address group names associated with the policy that you want to create in Fortinet FortiGate. |
| Destination |
Destination IPv4 address and address group names associated with the policy that you want to create in Fortinet FortiGate. |
| Service |
Service and service group names associated with the policy that you want to create in Fortinet FortiGate. |
| Schedule |
Name of the Schedule associated with the policy that you want to create in Fortinet FortiGate. |
| Status |
Select the Enable option to enable this policy on Fortinet FortiGate, else select Disable. |
| Action |
Select the action associated with the policy that you want to create in Fortinet FortiGate. You can choose Accept, which allows sessions that match the firewall policy, or Deny, which blocks sessions that match the firewall policy.
If you choose 'Accept', then you must specify the following parameters:
- Inspection Mode: The inspection mode of the policy. You can choose between the Flow Based (default) or Proxy Based.
- NAT: Select the checkbox, i.e., set it to true, to enable NAT.
- Protocol Options: Specify the name of an existing protocol options profile.
- Security Profiles: Select one or more security profiles to enable the protocol options profile. You can choose profiles such as AntiVirus Profile, File Filter Profile, SSL inspection Profile, etc.
Note: Based on the security profiles you choose, you must specify its name in the corresponding field. For example, if you choose Antivirus Profile, then in the Antivirus Profile field, you must specify the name of an existing AntiVirus profile, or if you choose Application Control, then in the Application Control field, you must specify the name of an existing application list, etc.
- Log Traffic: Select the logging option for sessions or security profile sessions. You can choose from the following options:
- All: Logs all sessions accepted or denied by this policy.
- UTM: Logs only traffic with an associated (applied) security profile.
- Disables: Disables all logging for this policy.
|
| Comments |
(Optional) Comment to be added to the policy that you want to create in Fortinet FortiGate. |
| Additional Policy Arguments |
(Optional) Specify policy arguments in that JSON format to be added to the policy that you want to create in Fortinet FortiGate. You can enter the arguments in the following format: {"field1":value1, "field2":value2} |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Get List of Policies
Input parameters
Note: All the input parameters are optional. However, if you do not specify any parameter, then no filter criterion is applied and an unfiltered list (of policies) is returned.
| Parameter |
Description |
| Policy ID |
The ID of the policy whose details you want to retrieve from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"result": [
{
"status": "",
"path": "",
"revision": "",
"name": "",
"http_method": "",
"vdom": "",
"http_status": "",
"version": "",
"build": "",
"serial": "",
"results": [
{
"logtraffic": "",
"srcaddr": [
{
"q_origin_key": "",
"name": ""
}
],
"dstintf": [
{
"q_origin_key": "",
"name": ""
}
],
"label": "",
"scan-botnet-connections": "",
"action": "",
"capture-packet": "",
"ips-sensor": "",
"tcp-session-without-syn": "",
"av-profile": "",
"policyid": "",
"diffserv-reverse": "",
"dnsfilter-profile": "",
"send-deny-packet": "",
"profile-protocol-options": "",
"app-category": [],
"vlan-cos-fwd": "",
"diffserv-forward": "",
"wanopt-passive-opt": "",
"tags": [],
"custom-log-fields": [],
"voip-profile": "",
"users": [],
"srcintf": [
{
"q_origin_key": "",
"name": ""
}
],
"learning-mode": "",
"timeout-send-rst": "",
"wsso": "",
"fsso": "",
"spamfilter-profile": "",
"traffic-shaper-reverse": "",
"url-category": [],
"block-notification": "",
"rsso": "",
"internet-service": "",
"internet-service-custom": [],
"webfilter-profile": "",
"dsri": "",
"auth-cert": "",
"ssl-mirror": "",
"groups": [],
"diffservcode-forward": "",
"internet-service-id": [],
"firewall-session-dirty": "",
"tcp-mss-sender": "",
"dstaddr-negate": "",
"outbound": "",
"rtp-nat": "",
"dscp-value": "",
"profile-type": "",
"wccp": "",
"inbound": "",
"ssl-mirror-intf": [],
"service": [
{
"q_origin_key": "",
"name": ""
}
],
"webcache": "",
"service-negate": "",
"wanopt": "",
"dscp-negate": "",
"profile-group": "",
"status": "",
"q_origin_key": "",
"tcp-mss-receiver": "",
"rtp-addr": [],
"nat": "",
"utm-status": "",
"poolname": [],
"fsso-agent-for-ntlm": "",
"delay-tcp-npu-session": "",
"ntlm": "",
"permit-stun-host": "",
"vpntunnel": "",
"devices": [],
"schedule": "",
"permit-any-host": "",
"global-label": "",
"icap-profile": "",
"dlp-sensor": "",
"identity-based-route": "",
"logtraffic-start": "",
"redirect-url": "",
"session-ttl": "",
"diffservcode-rev": "",
"auth-path": "",
"disclaimer": "",
"application": [],
"name": "",
"wanopt-profile": "",
"schedule-timeout": "",
"internet-service-negate": "",
"traffic-shaper": "",
"ippool": "",
"wanopt-detection": "",
"natoutbound": "",
"webcache-https": "",
"fixedport": "",
"application-list": "",
"waf-profile": "",
"dstaddr": [
{
"q_origin_key": "",
"name": ""
}
],
"comments": "",
"srcaddr-negate": "",
"replacemsg-override-group": "",
"uuid": "",
"vlan-cos-rev": "",
"radius-mac-auth-bypass": "",
"wanopt-peer": "",
"natip": "",
"per-ip-shaper": "",
"dscp-match": "",
"ntlm-enabled-browsers": [],
"ntlm-guest": "",
"natinbound": "",
"captive-portal-exempt": "",
"match-vip": "",
"ssl-ssh-profile": "",
"auth-redirect-addr": ""
}
]
}
],
"vdom_not_exist": []
}
operation: Update Policy
Input parameters
| Parameter |
Description |
| Policy ID |
The ID of policy that you want to update in Fortinet FortiGate. |
| Policy Name |
(Optional) Specify a new name for the policy if you want to update its name in Fortinet FortiGate. |
| Status |
Select the status of the policy, i.e., select Enable to enable the policy, else select Disable. |
| Incoming Interface |
Names of the incoming interfaces associated with the policy that you want to update in Fortinet FortiGate. For example port1. |
| Outgoing Interface |
Names of the outgoing interfaces associated with the policy that you want to update in Fortinet FortiGate. For example port2. |
| Add Source |
Source IPv4 address and address group names to be added to the policy that you want to update in Fortinet FortiGate. |
| Remove Source |
Source IPv4 address and address group names to be removed from the policy that you want to update in Fortinet FortiGate. |
| Add Destination |
Destination IPv4 address and address group names to be added to the policy that you want to update in Fortinet FortiGate. |
| Remove Destination |
Destination IPv4 address and address group names to be removed from the policy that you want to update in Fortinet FortiGate. |
| Add Services |
Service and service group names to be added to the policy that you want to update in Fortinet FortiGate. |
| Remove Services |
Service and service group names to be removed from the policy that you want to update in Fortinet FortiGate. |
| Schedule |
Name of the Schedule associated with the policy that you want to update in Fortinet FortiGate. |
| Action |
Select the action associated with the policy that you want to update in Fortinet FortiGate. You can choose Accept, which allows sessions that match the firewall policy, or Deny, which blocks sessions that match the firewall policy.
If you choose 'Accept', then you must specify the following parameters:
- Inspection Mode: The inspection mode of the policy. You can choose between the Flow Based (default) or Proxy Based.
- NAT: Select the checkbox, i.e., set it to true, to enable NAT. If you select true, then you must specify the following parameters
- IP Pool Configuration: Select the configuration to be used for the IP Pool. You can choose between Use Outgoing Interface Address or Use Dynamic Pool.
- If you choose 'Use Dynamic Pool', then in the Pool Name field, enter the names of the IP pools in CSV or List format.
- Preserve Source Port: Select Enable to prevent source NAT from changing a session's source port.
- Protocol Options: Specify the name of an existing protocol options profile.
- Security Profiles: Select one or more security profiles to enable the protocol options profile. You can choose profiles such as AntiVirus Profile, File Filter Profile, SSL inspection Profile, etc.
Note: Based on the security profiles you choose, you must specify its name in the corresponding field. For example, if you choose Antivirus Profile, then in the Antivirus Profile field, you must specify the name of an existing AntiVirus profile, or if you choose Application Control, then in the Application Control field, you must specify the name of an existing application list, etc.
- Log Traffic: Select the logging option for sessions or security profile sessions. You can choose from the following options:
- All: Logs all sessions accepted or denied by this policy.
- UTM: Logs only traffic with an associated (applied) security profile.
- Disables: Disables all logging for this policy.
|
| Comments |
(Optional) Comment to be added to the policy that you want to update in Fortinet FortiGate. |
| Additional Policy Arguments |
(Optional) Specify policy arguments in that JSON format to be added to the policy that you want to update in Fortinet FortiGate. You can enter the arguments in the following format: {"field1":value1, "field2":value2} |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"revision": "",
"revision_changed": "",
"old_revision": "",
"mkey": "",
"status": "",
"http_status": "",
"vdom": "",
"path": "",
"name": "",
"serial": "",
"version": "",
"build": ""
}
operation: Delete Policy
Input parameters
| Parameter |
Description |
| Policy ID |
The ID of policy that you want to delete from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"mkey": "",
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"version": "",
"revision": "",
"http_method": "",
"http_status": "",
"old_revision": "",
"revision_changed": ""
}
operation: Execute Command
Input parameters
| Parameter |
Description |
| Commands |
Specify the command that you want to execute on the FortiOS console. You can provide commands in the .csv or the list format. |
| Username |
The username to access the FortiOS endpoint server to which you will connect and execute the specified command. |
| Password |
The password to access the FortiOS endpoint server to which you will connect and execute the specified command. |
| Private Key |
The private key used to perform SSH authentication on the FortiOS server. For the process of generating Public and Private keys, see the Steps to generate Public and Private keys section. |
| Port |
The port number used for connecting to the FortiOS server via SSH. By default, this is set to 22. |
| Timeout |
Time, in seconds, after which the execution of the remote command gets timed out. |
operation: Create User
Input parameters
| Parameter |
Description |
| User Type |
Select the type of user type that you want to create on Fortinet FortiGate. You can choose between Local User, Remote Radius User, or Remote TACACS+ User.
If you choose 'Local User', then you must specify the following parameters:
- Username: Specify the username for the user that you want to create in the Fortinet FortiGate server.
- Password: Specify the password for the user that you want to create in the Fortinet FortiGate server.
If you choose 'Remote Radius User', then you must specify the following parameters:
- Username: Specify the username for the user that you want to create in the Fortinet FortiGate server.
- Radius Server: Specify the name of the RADIUS server using which the user gets authenticated.
If you choose 'Remote TACACS+ User', then you must specify the following parameters:
- Username: Specify the username for the user that you want to create in the Fortinet FortiGate server.
- TACACS+ Server: Specify the name of the TACACS+ server using which the user gets authenticated.
|
| Two Factor Authentication |
Select whether you want to Enable or Disable two-factor authentication for the user you are creating in Fortinet FortiGate.
If you choose 'Enable', then you must specify the following parameters:
- Authentication Type: Select the type of two-factor authentication for the user you are creating in Fortinet FortiGate. You can choose between FortiToken or FortiToken Cloud.
- If you choose 'FortiToken', then you must specify the following parameters:
- Token: Enter the token name used to authenticate the user.
- Send Activation Code: Select whether you want to Enable or Disable sending of an activation code for two-factor authentication.
- If you choose 'Enable', then from the Activation Method drop-down list, select the method of sending the activation code. You can choose between Email or SMS. Choose SMS if you want to use an SMS-based two-factor authentication for the user.
- If you choose Email, then in the Email Address field, enter the email address of the user where the activation code must be sent.
- If you choose 'FortiToken Cloud', then you must specify the following parameters:
- Email Address: Enter the email address of the user you are creating in Fortinet FortiGate.
- SMS: Select whether you want to Enable or Disable SMS-based two-factor authentication for the user.
- If you choose 'Enable', then you must specify the following parameters:
- Country Dial Code: Enter the country code of the user for two-factor authentication.
- Phone Number: Enter the mobile phone number of the user for two-factor authentication.
|
| User Account Status |
Select the account status of the user you are creating on Fortinet FortiGate. You can choose between Enable or Disable. |
| User Group |
Select the group that you want to assign to the user you are creating on Fortinet FortiGate. You can choose between Enable or Disable.
If you choose 'Enable', then in the User Group Names field specify the group names, in CSV or in list format, that you want to assign to the user you are creating on Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes. Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"mkey": "",
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"version": "",
"revision": "",
"http_method": "",
"http_status": "",
"old_revision": "",
"revision_changed": ""
}
operation: Get Users
Input parameters
Note: All the input parameters are optional. However, if you do not specify any parameter, then no filter criterion is applied and an unfiltered list (of users) is returned.
| Parameter |
Description |
| Name |
Specify the name of the user for whom you want to retrieve data from the Fortinet FortiGate server. |
| Start |
Specify the starting entry index from where you want to retrieve users from the Fortinet FortiGate server. |
| Count |
Specify the maximum number of users to return. |
| VDOM |
Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"results": [
{
"id": "",
"name": "",
"type": "",
"q_ref": "",
"passwd": "",
"q_name": "",
"q_path": "",
"q_type": "",
"status": "",
"q_class": "",
"email-to": "",
"q_static": "",
"css-class": "",
"q_no_edit": "",
"sms-phone": "",
"fortitoken": {
"datasource": "",
"q_origin_key": "",
"serial-number": ""
},
"ppk-secret": "",
"sms-server": "",
"two-factor": "",
"authtimeout": "",
"ldap-server": "",
"passwd-time": "",
"q_mkey_type": "",
"q_no_rename": "",
"workstation": "",
"ppk-identity": "",
"q_origin_key": "",
"passwd-policy": "",
"radius-server": "",
"q_global_entry": "",
"tacacs+-server": {
"name": "",
"datasource": "",
"q_origin_key": ""
},
"sms-custom-server": "",
"auth-concurrent-value": "",
"two-factor-notification": "",
"auth-concurrent-override": "",
"two-factor-authentication": "",
"username-case-sensitivity": ""
}
],
"version": "",
"revision": "",
"http_method": "",
"http_status": ""
}
operation: Update User
Input parameters
| Parameter |
Description |
| User Type |
Select the type of user type that you want to update in Fortinet FortiGate. You can choose between Local User, Remote Radius User, or Remote TACACS+ User.
If you choose 'Local User', then you must specify the following parameters:
- Username: Specify the existing username that you want to edit in the Fortinet FortiGate server.
- New Username: Specify the new username for the user that you want to update in the Fortinet FortiGate server.
- Password: Specify a new password if you want to edit the password in the Fortinet FortiGate server.
If you choose 'Remote Radius User', then you must specify the following parameters:
- Username: Specify the existing username that you want to edit in the Fortinet FortiGate server.
- New Username: Specify the new username for the user that you want to update in the Fortinet FortiGate server.
- Radius Server: Specify the name of the RADIUS server using which the user gets authenticated.
If you choose 'Remote TACACS+ User', then you must specify the following parameters:
- Username: Specify the existing username that you want to edit in the Fortinet FortiGate server.
- New Username: Specify the new username for the user that you want to update in the Fortinet FortiGate server.
- TACACS+ Server: Specify the name of the TACACS+ server using which the user gets authenticated.
|
| Two Factor Authentication |
Select whether you want to Enable or Disable two-factor authentication for the user you want to update in Fortinet FortiGate. |
| Authentication Type |
Select the type of two-factor authentication for the user you want to update in Fortinet FortiGate. You can choose between FortiToken or FortiToken Cloud. You must specify the authentication type parameter when you are enabling two-factor authentication |
| Token |
Enter the Fortitoken used to authenticate the user for two-factor authentication. This is required if you select the authentication type as 'FortiToken'. |
| Send Activation Code |
Select whether you want to Enable or Disable sending of an activation code for two-factor authentication.
If you choose 'Enable', then from the Activation Method drop-down list, select the method of sending the activation code. You can choose between Email or SMS. |
| Email Address |
Enter the email address of the user you want to update in Fortinet FortiGate. You must specify either the email address or sms details to activate two factor authentication. |
| SMS |
Select whether you want to Enable or Disable SMS-based two-factor authentication for the user. Enable it if you wants sms based two factor authentication. Either email address or sms details required to activate two factor authentication.
If you choose 'Enable', then you must specify the following parameters:
- Country Dial Code: Enter the country code of the user for two-factor authentication.
- Phone Number: Enter the mobile phone number of the user for two-factor authentication.
|
| User Account Status |
Select the account status of the user you are updating on Fortinet FortiGate. You can choose between Enable or Disable. |
| User Group Names To Add |
Enter the user group names, in the CSV or list format, to which you want to add the user you are updating on Fortinet FortiGate. |
| User Group Names To Remove |
Enter the user group names, in the CSV or list format, from which you want to remove the user you are updating on Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"mkey": "",
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"version": "",
"revision": "",
"http_method": "",
"http_status": "",
"revision_changed": ""
}
operation: Delete User
Input parameters
| Parameter |
Description |
| Name |
Specify the name of the user that you want to delete from Fortinet FortiGate. |
| VDOM |
(Optional) Specify the Virtual Domain(s) from which results are returned or to which you want to apply these changes.
Note: You can specify the VDOM here as a configuration parameter, in the CSV or List format, or you can specify VDOMs as a function parameter, i.e., in the 'Configuration Parameters' while configuring this connector. If both are specified, then the one that is specified in this operation will overwrite the one specified in the configuration parameters. If this parameter is not provided, the management VDOM will be used. A permission error will be returned if the admin does not have access to the VDOM. You must specify the parameter from one of the following: vdom=root (Single VDOM), vdom=vdom1,vdom2 (Multiple VDOMs), vdom=* (All VDOMs). |
Output
The output contains the following populated JSON schema:
{
"mkey": "",
"name": "",
"path": "",
"vdom": "",
"build": "",
"serial": "",
"status": "",
"version": "",
"revision": "",
"http_method": "",
"http_status": "",
"old_revision": "",
"revision_changed": ""
}
operation: Get System Events
Input parameters
Note: All the input parameters are optional. However, if you do not specify any parameter, then no filter criterion is applied and an unfiltered list (of system events) is returned.
| Parameter |
Description |
| Filter Query |
Specify the query using which you want to filter system events that you want to retrieve from the Fortinet FortiGate server. For example, user=*"admin", level=*"emergency" |
| Start |
Specify the starting entry index from where you want to retrieve data from the Fortinet FortiGate server. |
| Rows |
Specify the maximum number of items to return |
Output
The output contains the following populated JSON schema:
{
"http_method": "",
"results": [
{
"date": "",
"time": "",
"eventtime": "",
"tz": "",
"logid": "",
"type": "",
"subtype": "",
"level": "",
"vd": "",
"logdesc": "",
"user": "",
"action": "",
"msg": "",
"_metadata": {
"#": "",
"logid": "",
"timestamp": "",
"roll": ""
}
}
],
"vdom": "",
"device": "",
"category": "",
"subcategory": "",
"start": "",
"rows": "",
"session_id": "",
"completed": "",
"total_lines": "",
"now": "",
"status": "",
"serial": "",
"version": "",
"build": ""
}
operation: Get User Last Login Details
Input parameters
| Parameter |
Description |
| Username |
Specify the username whose last login details you want to retrieve from the Fortinet FortiGate server. |
Output
The output contains the following populated JSON schema:
{
"date": "",
"time": "",
"eventtime": "",
"tz": "",
"logid": "",
"type": "",
"subtype": "",
"level": "",
"vd": "",
"logdesc": "",
"sn": "",
"user": "",
"ui": "",
"method": "",
"srcip": "",
"dstip": "",
"action": "",
"status": "",
"reason": "",
"profile": "",
"msg": "",
"_metadata": {
"#": "",
"logid": "",
"timestamp": "",
"roll": ""
}
}
- Generate public and private key files by running the following command from an SSH session on your FortiSOAR system:
ssh-keygen -t rsa -b 2048
This command generates two key files <id>_rsa and <id>_rsa.pub.
- Start an SSH session on your FortiGate system.
- (Optional) If the '
vdom' mode is enabled then run the following command:
config global
Else, begin with step 4.
- Run the following commands:
Config system admin Show edit admin set ssh-public-key1 “ssh public key value” End exit
- Copy the private key file (
id_rsa) to your computer using the SCP command, and then use that file as an input parameter in the Execute Command action.
Output
The output contains the following populated JSON schema:
{
"command": "",
"output": []
}
Included playbooks
The Sample - Fortinet FortiGate - 5.2.0 playbook collection comes bundled with the Fortinet FortiGate connector. This playbook contains steps using which you can perform all supported actions. You can see the bundled playbooks in the Automation > Playbooks section in FortiSOAR™ after importing the Fortinet FortiGate connector.
- Address Group: Create Address Group
- Address Group: Delete Address Group
- Address Group: Get Address Groups
- Address Group: Update Address Group
- Address: Block IP Address
- Address: Create Address
- Address: Delete Address
- Address: Get Addresses
- Address: Get Blocked IP Addresses
- Address: Unblock IP Address
- Address: Update Address
- Application: Block Application
- Application: Get Applications Detail
- Application: Get Blocked Applications
- Application: Unblock Application
- Execute Command
- Get System Events
- Host: Get Quarantine Hosts
- Host: Quarantine Host
- Host: Unquarantine Host
- Policy: Create Policy
- Policy: Delete Policy
- Policy: Get List of Policies
- Policy: Update Policy
- Service Group: Create Service Group
- Service Group: Delete Service Group
- Service Group: Get Service Groups
- Service Group: Update Service Group
- Service: Create Service
- Service: Delete Service
- Service: Get Services
- Service: Update Service
- URL: Block URL
- URL: Get Blocked URLs
- URL: Unblock URL
- User: Create User
- User: Delete User
- User: Get User Last Login Details
- User: Update User
- Users: Get Users
Note: If you are planning to use any of the sample playbooks in your environment, ensure that you clone those playbooks and move them to a different collection since the sample playbook collection gets deleted during the connector upgrade and delete.