About the connector
Fortinet FortiSIEM is a highly scalable multi-tenant Security Information and Event Management (SIEM) solution that provides real-time infrastructure and user awareness for accurate threat detection, analysis and reporting.
This document provides information about the Fortinet FortiSIEM Connector, which facilitates automated interactions, with your Fortinet FortiSIEM server using FortiSOAR™ playbooks. Add the Fortinet FortiSIEM Connector, as a step in FortiSOAR™ playbooks and perform automated operations such as retrieving device information for all devices configured on the Fortinet FortiSIEM server and retrieving a list of monitored organizations from the Fortinet FortiSIEM server.
Version information
Connector Version: 3.0.0
FortiSOAR™ Version Tested on: 5.1.1-58 and 6.0.0
Fortinet FortiSIEM Version Tested on: 5.2.6 and later
Authored By: Fortinet
Certified: Yes
Release Notes for version 3.0.0
Following enhancements have been made to the Fortinet FortiSIEM connector in version 3.0.0:
- Removed the "Domain" configuration parameter and added "Organization" as a configuration parameter.
- Added the "Incident ID" parameter as an input to the "List Incidents" action. If you enter the incident ID then all other parameters specified for the List Incidents action will get ignored.
- Added the following new actions and playbooks:
- Update Incident
- Get Event Details
- Change Severity
- Change Resolution
Note: Fortinet FortiSIEM supports the Change Severity and Change Resolution actions from version 5.2.8 and later.
- Enhanced data ingestion by providing flexibility to the user to pull data from Fortinet FortiSIEM either by time range (minutes) or by Incident ID. The "Fetch Data" screen of the Data Ingestion wizard has been changed and a new field named Fetch Mode has been added. Users can choose whether they want to fetch data from FortiSIEM that have been updated in the last X minutes or they want to fetch data based on an Incident ID. The data ingestion playbooks have also been updated to accommodate this change.
Important: While configuring data ingestion in FortiSOAR™ Version 5.1.1, picklists do not map correctly. For example the Severity picklist. To ensure that picklists map correctly, enter the following (considering the severity picklist) in the picklist field:
{{vars.item.incident_data.attributes.eventSeverityCat | resolveRange(vars.alerts_severity_map)}}
This issue has been resolved in FortiSOAR™ Version 6.0.0.
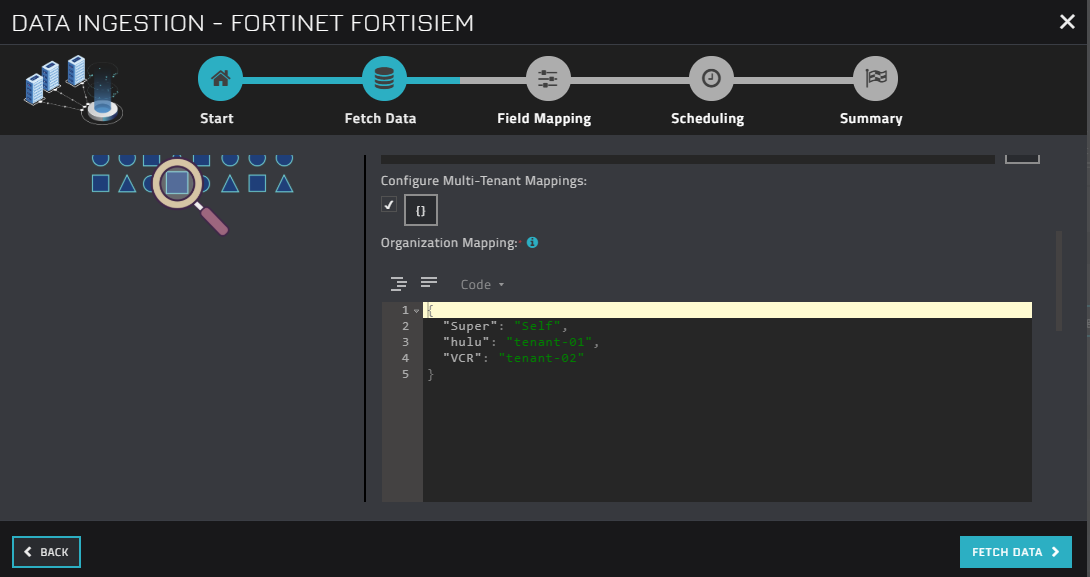
- During configuring data ingestion for MSSP systems if you have checked the Configure Multi-Tenant Mappings checkbox on the "Fetch Data" screen, then ensure that you map the organization name defined in FortiSIEM as a tenant in FortiSOAR™:
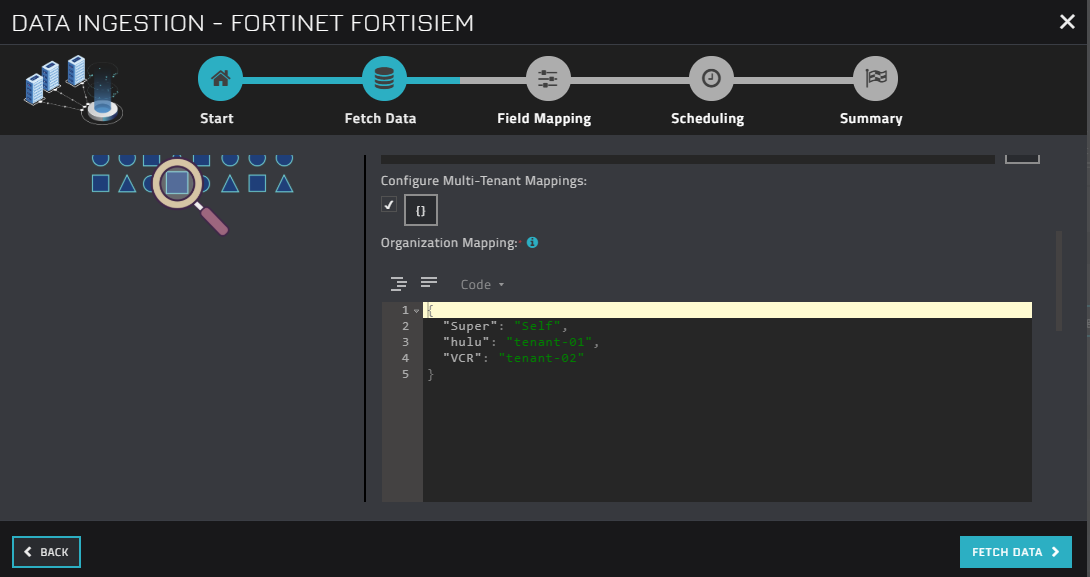 If you have not mapped or wrongly mapped an organization, then the incident record will be created as a "Self" entry.
If you have not mapped or wrongly mapped an organization, then the incident record will be created as a "Self" entry.
- Updated the output schema for the following actions:
- Get Events For Incident
- Get Device Information
- List Monitored Organizations
- Added "Page Size" and "Page Number" as input parameters to the "Get Events For Incident" action.
- Added "Report Name" as an input parameter for the "Run Report" action and removed the "Display Field / Select Clause", "Group By", and "Order By" parameters from this action.
- Removed the following actions and playbooks:
- List Report Templates
- Get Report Template Details
Installing the connector
From FortiSOAR™ 5.0.0 onwards, use the Connector Store to install the connector. For the detailed procedure to install a connector, click here.
You can also use the yum command to install connectors. Connectors provided by FortiSOAR™ are delivered using a FortiSOAR™ repository. Therefore, you must set up your FortiSOAR™ repository and run the yum command as a root user to install connectors:
yum install cyops-connector-fortinet-fortisiem
Prerequisites to configuring the connector
- You must have the URL of a Fortinet FortiSIEM server to which you will connect and perform automated operations and the credentials, such as the username and password to access that server.
- To access the FortiSOAR™ UI, ensure that port 443 is open through the firewall for the FortiSOAR™ instance.
- The minimum privileges that require to be assigned to users who are going to use this connector and run actions on FortiSIEM are "Read" and "Update" access on Incidents and access to "Run Reports".
Configuring the connector
For the procedure to configure a connector, click here.
Configuration parameters
In FortiSOAR™, on the Connectors page, click the Fortinet FortiSIEM connector row, and in the Configure tab enter the required configuration details.
| Parameter |
Description |
| Server URL |
URL of the Fortinet FortiSIEM server to which you will connect and perform the automated operations. |
| Username |
Username used to access the Fortinet FortiSIEM server to which you will connect and perform the automated operations. |
| Password |
Password used to access the Fortinet FortiSIEM server to which you will connect and perform the automated operations. |
| Organization |
Name of the organization that you will access on the Fortinet FortiSIEM server to perform the automated operations. |
| Verify SSL |
Specifies whether the SSL certificate for the server is to be verified or not.
By default, this option is set as True. |
Actions supported by the connector
The following automated operations can be included in playbooks, and you can also use the annotations to access operations from FortiSOAR™ release 4.10.0 onwards:
| Function |
Description |
Annotation and Category |
| Get All Devices |
Retrieves a short description for all devices that are configured on the Fortinet FortiSIEM server. |
get_devices
Investigation |
| Get All Devices For Specified IP Address Range |
Retrieves a short description for devices that are configured on the Fortinet FortiSIEM server, based on the IP address range that you have specified. |
get_devices
Investigation |
| Get Device Information |
Retrieves details of a specific device that is configured on the Fortinet FortiSIEM server, based on the Device IP that you have specified. |
get_devices
Investigation |
| List Monitored Devices and Attributes |
Retrieves a list and attributes of all monitored devices that are configured on the Fortinet FortiSIEM server. |
get_devices
Investigation |
| List Monitored Organizations |
Retrieves a list and details of all monitored organizations that are configured on the Fortinet FortiSIEM server. |
get_domains
Investigation |
| Get Organization Details |
Retrieves the details of a specific organization from the Fortinet FortiSIEM server based on the organization ID that you have specified. |
get_organization
Investigation |
| List Incidents |
Retrieves a list and details of incidents from the Fortinet FortiSIEM server based on the incident ID or search criteria you have specified. |
get_incidents
Investigation |
| Comment Incident |
Adds a comment to a specific incident on the Fortinet FortiSIEM server based on the incident ID you have specified. |
incident_comment
Investigation |
| Clear Incident With Reason |
Clears an incident with the reason you have specified on the Fortinet FortiSIEM server based on the incident ID you have specified. |
clear_incident
Investigation |
| Change Severity |
Changes the severity of a specific incident severity to LOW, MEDIUM or HIGH on the Fortinet FortiSIEM server based on the incident ID you have specified. |
change_incident_severity
Investigation |
| Change Resolution |
Changes the resolution of a specific incident True Positive or False Positive on the Fortinet FortiSIEM server based on the incident ID you have specified. |
change_incident_resolution
Investigation |
| Get Events For Incident |
Retrieves all associated events for a specified incident from the Fortinet FortiSIEM server, based on the incident ID you have specified. |
get_associated_events
Investigation |
| Run Report |
Runs a report on the Fortinet FortiSIEM server, based on the report name and time range you have specified. |
run_report
Investigation |
| Update Incident |
Updates the attributes of a specific incident on the Fortinet FortiSIEM server based on the incident ID and other input parameters you have specified. |
update_incident
Investigation |
| Get Event Details |
Retrieves details of a specific event from the Fortinet FortiSIEM server based on the event ID you have specified. |
get_event_details
Investigation |
operation: Get All Devices
Input parameters
None.
Output
The output contains the following populated JSON schema:
{
"devices": {
"device": [
{
"organization": {
"@id": "",
"@name": ""
},
"discoverTime": "",
"unmanaged": "",
"accessIp": "",
"approved": "",
"discoverMethod": "",
"name": "",
"deviceType": {
"version": "",
"vendor": "",
"accessProtocols": "",
"jobWeight": "",
"model": ""
},
"creationMethod": "",
"version": "",
"updateMethod": ""
}
]
}
}
operation: Get All Devices For Specified IP Address Range
Input parameters
| Parameter |
Description |
| Include IP SET |
Value of IP addresses based on which you want for retrieve device information from the Fortinet FortiSIEM server. You must provide the value of this field as a range or in the .csv format.
For example, enter, 192.168.20.1-192.168.20.100 |
| Exclude IP SET |
(Optional) Value of the range of IP addresses that you want to exclude from this search operation. You must provide the value of this field as a range or in the .csv format. |
Output
The output contains the following populated JSON schema:
{
"devices": {
"device": [
{
"organization": {
"@id": "",
"@name": ""
},
"discoverTime": "",
"unmanaged": "",
"accessIp": "",
"approved": "",
"discoverMethod": "",
"name": "",
"deviceType": {
"version": "",
"vendor": "",
"accessProtocols": "",
"jobWeight": "",
"model": ""
},
"creationMethod": "",
"version": "",
"updateMethod": ""
}
]
}
}
operation: Get Device Information
Input parameters
| Parameter |
Description |
| Device IP |
IP address of the device for which you want to retrieve details from the Fortinet FortiSIEM server. |
| Organization |
(Optional) Name of the organization for which you want to retrieve details of the device from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"device": {
"name": "",
"raidGroups": "",
"description": "",
"sanControllerPorts": "",
"storages": "",
"luns": "",
"eventParserList": "",
"systemUpTime": "",
"components": "",
"unmanaged": "",
"processors": "",
"applications": "",
"accessIp": "",
"approved": "",
"softwarePatches": "",
"ipToHostNames": "",
"organization": {
"@name": "",
"@id": ""
},
"storageGroups": "",
"softwareServices": "",
"interfaces": {
"networkinterface": {
"isTrunk": "",
"ipv4Addr": "",
"ipv4Mask": "",
"description": "",
"name": "",
"type": "",
"macAddr": "",
"isCritical": "",
"macIsVirtual": "",
"ipv4IsVirtual": "",
"inSpeed": "",
"speed": "",
"snmpIndex": "",
"isMonitor": "",
"adminStatus": "",
"outSpeed": "",
"operStatus": "",
"isWAN": ""
}
},
"deviceType": {
"model": "",
"version": "",
"category": "",
"jobWeight": "",
"vendor": ""
},
"updateMethod": "",
"discoverTime": "",
"discoverMethod": "",
"creationMethod": ""
}
}
operation: List Monitored Devices and Attributes
Input parameters
None.
Output
The output contains the following populated JSON schema:
{
"monitoredDevices": {
"eventPullingDevices": "",
"perfMonDevices": {
"device": {
"deviceName": "",
"monitors": {
"monitor": [
{
"method": "",
"category": ""
}
]
},
"deviceType": "",
"organization": "",
"accessIp": ""
}
}
}
}
operation: List Monitored Organizations
Input parameters
None.
Output
The output contains the following populated JSON schema:
{
"disabled": "",
"@lastModified": "",
"name": "",
"initialized": "",
"collectors": {
"collector": []
},
"@xmlId": "",
"custProperties": "",
"@ownerId": "",
"@id": "",
"domainId": "",
"@entityVersion": "",
"@custId": "",
"@creationTime": ""
}
operation: List Incidents
Input parameters
| Parameter |
Description |
| Incident ID |
ID of the incident based on which you want to retrieve incidents from the Fortinet FortiSIEM server.
Important: If you enter the incident ID then all other parameters specified for this action get ignored. |
| Search |
Search criteria based on which you want to retrieve incidents from the Fortinet FortiSIEM server. You can choose from the following options: Incident Status, Severity, Host, IP, or Organization.
By default, this option is set as Incident Status. |
| Search Value |
Value of the search criteria based on what you have selected in the Search parameter.
For example, in the case of Incident Status, you must select the status of the incident (Active or Cleared) based on which you want to retrieve incidents from the Fortinet FortiSIEM server.
OR
For example, if you select Host, then you must specify the hostname based on which you want to retrieve incidents from the Fortinet FortiSIEM server.
Note: From version 2.2.0 of the Fortinet FortiSIEM connector, if you have selected Organization from the Search field, then you can either explicitly add the organization name or use a jinja expression to add the value of the Organization. |
| Time Selection |
(Optional) Specify the time for which you want to retrieve the list of incidents from the Fortinet FortiSIEM server. By default, this is set as Relative Time.
If you select Absolute Time, then you must specify the time range, for which you want to retrieve the list of incidents from the Fortinet FortiSIEM server, in the From and To fields using the calendar tool.
If you select Relative Time, then you have to specify the time duration for which you want to retrieve the list of incidents from the Fortinet FortiSIEM server.
For example, if you choose Hours from the Relative Time drop-down list and provide the value 2 in the Last field, then this operation retrieves the list of incidents that have occurred in the last 2 hours from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"events": [
{
"attributes": {},
"id": "",
"receiveTime": "",
"nid": "",
"dataStr": "",
"index": "",
"eventType": "",
"custId": ""
}
],
"@queryId": "",
"@totalCount": "",
"@errorCode": "",
"@start": ""
}
operation: Get Organization Details
Input parameters
| Parameter |
Description |
| Organization ID |
ID of the organization whose details you want to retrieve from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"@custId": "",
"@creationTime": "",
"@entityVersion": "",
"@id": "",
"@lastModified": "",
"name": "",
"domainId": "",
"@xmlId": "",
"@ownerId": "",
"initialized": "",
"disabled": ""
}
operation: Comment Incident
Input parameters
| Parameter |
Description |
| Incident ID |
ID of the incident in which you want to add the comment on the Fortinet FortiSIEM server. |
| Comment Text |
Text of the comment that you want to add to the specified incident on the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"message": "",
"incident_id": ""
}
operation: Clear Incident With Reason
Input parameters
| Parameter |
Description |
| Incident ID |
ID of the incident that you want to clear from the Fortinet FortiSIEM server. |
| Reason |
Text of the reason that you want to provide which clearing the specified incident from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"message": "",
"incident_id": []
}
operation: Change Severity
Input parameters
| Parameter |
Description |
| Incident ID |
ID of the incident whose severity you want to update on the Fortinet FortiSIEM server. |
| Incident Severity |
Severity that you want to set for the specified incident on the Fortinet FortiSIEM server. You can choose from the following options: HIGH, MEDIUM, or LOW. |
Output
The output contains the following populated JSON schema:
{
"incident_id": [],
"message": ""
}
operation: Change Resolution
Input parameters
| Parameter |
Description |
| Incident ID |
ID of the incident whose resolution you want to update on the Fortinet FortiSIEM server. |
| Incident Resolution |
Resolution that you want to set for the specified incident on the Fortinet FortiSIEM server. You can choose between True Positive or False Positive. |
Output
The output contains the following populated JSON schema:
{
"incident_id": [],
"message": ""
}
operation: Get Events For Incident
Input parameters
| Parameter |
Description |
| Incident ID |
ID of the incident for which you want to retrieve all associated events from the Fortinet FortiSIEM server. |
| Page Size |
Number of objects that you want this operation to return in the response.
By default, the page size is set to 50 items.
|
| Page Number |
Page number from which you want to retrieve records.
By default, this is set as 0. |
Output
The output contains the following populated JSON schema:
{
"event_ids": "",
"event_details": [
[
{
"dataStr": "",
"index": "",
"custId": "",
"receiveTime": "",
"attributes": {
"eventSeverity": "",
"relayDevIpAddr": "",
"reptDevName": "",
"reptModel": "",
"eventParsedOk": "",
"phRecvTime": "",
"count": "",
"hostIpAddr": "",
"hostName": "",
"reptDevIpAddr": "",
"parserName": "",
"customer": "",
"eventId": "",
"eventRuleTrigger": "",
"procName": "",
"collectorId": "",
"eventName": "",
"eventType": "",
"rawEventMsg": "",
"phEventCategory": "",
"eventSeverityCat": "",
"reptVendor": ""
},
"nid": "",
"id": "",
"eventType": ""
}
]
]
}
operation: Run Report
Input parameters
| Parameter |
Description |
| Report Name |
Name of the report that you want to run on the Fortinet FortiSIEM server. |
| Report Time Range |
(Optional) Specify the time duration for which you want to search for reports that you want to run on the Fortinet FortiSIEM server. By default, this is set as Relative Time.
If you select Absolute Time, then you must specify the time range, for which you want to search for reports that you want to run on the Fortinet FortiSIEM server, in the From and To fields using the calendar tool.
If you select Relative Time, then you have to specify the time duration for which you want to search for reports that you want to run on the Fortinet FortiSIEM server.
For example, if you choose Hours from the Relative Time drop-down list and provide the value 2 in the Last field, then this operation searches for reports that are created in the last 2 hours on the Fortinet FortiSIEM server. |
Output
No output schema is available at this time.
operation: Update Incident
Input parameters
| Parameter |
Description |
| Incident ID |
ID of the incident that you want to update on the Fortinet FortiSIEM server. |
| Comment Text |
Text of the comment that you want to add to the specified incident on the Fortinet FortiSIEM server. |
| Incident Status |
Status of the incident that you want to update in the specified incident on the Fortinet FortiSIEM server. |
| External Ticket Type |
Type of the external ticket that you want to update in the specified incident on the Fortinet FortiSIEM server. |
| External Ticket ID |
ID of the external ticket that you want to update in the specified incident on the Fortinet FortiSIEM server. |
| External Ticket State |
State of the external ticket that you want to update in the specified incident on the Fortinet FortiSIEM server. |
| External Assigned User |
External assigned that you want to update in the specified incident on the Fortinet FortiSIEM server. |
Output
The output contains a non-dictionary value.
operation: Get Event Details
Input parameters
| Parameter |
Description |
| Event ID |
ID of the event whose details you want to retrieve from the Fortinet FortiSIEM server. |
Output
The output contains the following populated JSON schema:
{
"dataStr": "",
"index": "",
"custId": "",
"receiveTime": "",
"attributes": {
"eventSeverity": "",
"relayDevIpAddr": "",
"reptDevName": "",
"reptModel": "",
"eventParsedOk": "",
"phRecvTime": "",
"count": "",
"hostIpAddr": "",
"hostName": "",
"reptDevIpAddr": "",
"parserName": "",
"customer": "",
"eventId": "",
"eventRuleTrigger": "",
"procName": "",
"collectorId": "",
"eventName": "",
"eventType": "",
"rawEventMsg": "",
"phEventCategory": "",
"eventSeverityCat": "",
"reptVendor": ""
},
"nid": "",
"id": "",
"eventType": ""
}
Included playbooks
The Sample - Fortinet FortiSIEM - 3.0.0 playbook collection comes bundled with the Fortinet FortiSIEM connector. This playbook contains steps using which you can perform all supported actions. You can see the bundled playbooks in the Automation > Playbooks section in FortiSOAR™ after importing the Fortinet FortiSIEM connector.
- Device: Get All Devices
- Device: Get All Devices For Specified IP Address Range
- Device: Get Device Information
- Device: List Monitored Devices and Attributes
- Event: Get Events For Incident
- Event: Get Event Details
- > FortiSIEM > Fetch
- >> FortiSIEM > Fetch Associated Events for Incident
- FortiSIEM > Ingest
- Incident: Change Resolution
- Incident: Change Severity
- Incident: Clear Incident With Reason
- Incident: Comment Incident
- Incident: List Incidents
- Incident: Update Incident
- Organization: Get Organization Details
- Organization: List Monitored Organizations
- Run Report
Note: If you are planning to use any of the sample playbooks in your environment, ensure that you clone those playbooks and move them to a different collection since the sample playbook collection gets deleted during the connector upgrade and delete.