 DOCUMENT LIBRARY
1.0.0
DOCUMENT LIBRARY
1.0.0
 DOCUMENT LIBRARY
1.0.0
DOCUMENT LIBRARY
1.0.0
The Syslog connector sets up listeners for syslog messages, supporting both TCP and UDP transmission, and when a message is received, triggers the FortiSOAR™ playbooks for automated creation of alerts and other predefined response actions.
Connector Version: 1.0.0
FortiSOAR™ Version Tested on: 4.9.0.0-708 and later
Authored By: Fortinet
Certified: Yes
All connectors provided by FortiSOAR™ are delivered using a FortiSOAR™ repository. Therefore, you must set up your FortiSOAR™ repository and use the yum command to install connectors:
yum install cyops-connector-syslog
syslog rpm has a dependency on lsof package. If you are installing the rpm offline, you must install the lsof rpm prior configuring the syslog connector on the CyOps instance.In FortiSOAR™, on the Connectors page, select the Syslog connector and click Configure to configure the following parameters:
| Parameter | Description |
|---|---|
| Listener Protocol | Protocol of the listener protocol. Specify either TCP or UDP. |
| Listener Port | Port on which the listener starts. Since the listener is started as a non-root user, ensure that you provide a port higher than 1024. |
| CyberSponse Endpoint (/api/triggers/1/ will be prepended) | API Trigger URL for the playbook to be triggered when a Syslog message is received. |
| CyberSponse Username | Username required for authentication to forward the Syslog message to FortiSOAR™. |
| CyberSponse Password | Password required for authentication to forward the Syslog message to FortiSOAR™. |
The following automated operations can be included in playbooks:
Note: You can also restart listeners for all configurations by Deactivating and Activating the connector on the Connectors page in FortiSOAR™ (Automation > Connectors).
| Parameter | Description |
|---|---|
| Message Format | Specify whether the message to be parsed is in the RFC 3164 or RFC 5424 format. |
Note: The message complying to both the RFC 3164 or RFC 5424 specifications can be parsed.
This function parses the Syslog message and returns a JSON with the message fields.
Following image displays a sample output, when the message format is RFC 3164 :
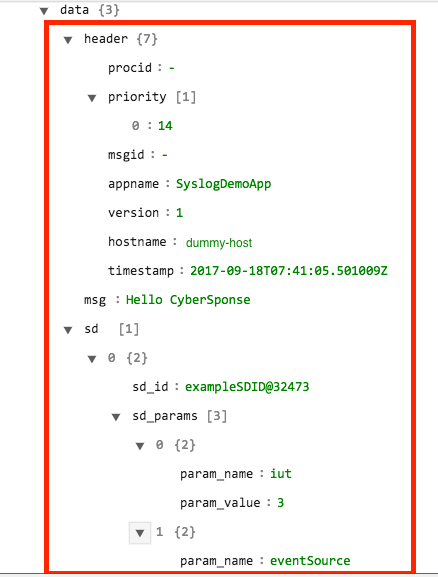
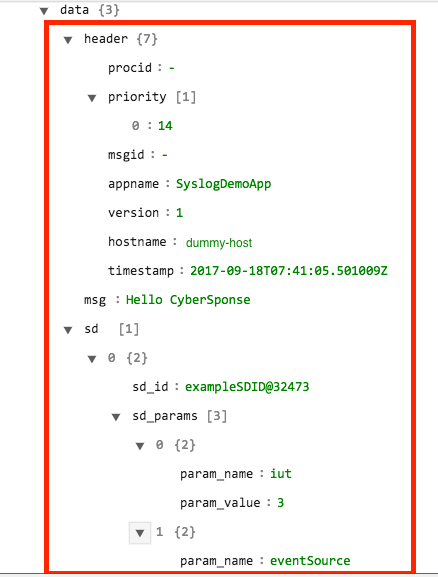
Following image displays a sample output, when the message format is RFC 5424 :
None.
Use this function to start the listener for a given configuration. Note that the listener for a configuration is started by default as soon as the configuration is added, or if connector is activated.
The JSON output contains the status code and a message.
Following image displays a sample output:
None.
Use this function to stop the listener for a given configuration. Note that the listener for a configuration is started by default as soon as the configuration is deleted, or if connector is deactivated.
The JSON output contains the status code and a message.
Following image displays a sample output:
None.
Use this function to restart the listener for a given configuration.
The JSON output contains the status code and a message.
Following image displays a sample output:
The Sample - Syslog - 1.0.0 playbook collection comes bundled with the Syslog connector. This playbook contains steps using which you can perform all supported actions. You can see the bundled playbooks in the Automation > Playbooks section in FortiSOAR™ after importing the Syslog connector.
Note: If you are planning to use any of the sample playbooks in your environment, ensure that you clone those playbooks and move them to a different collection, since the sample playbook collection gets deleted during connector upgrade and delete.
This could be due to one of the following reasons:
The listener logs are written to /var/opt/cyops-integrations/syslog/listener.log. Check this log file for the exact reason for the failure.
This happens because listeners are not configured to come up automatically after a service restart. You must Deactivate and Activate the connector to start all listeners again.
The Syslog connector sets up listeners for syslog messages, supporting both TCP and UDP transmission, and when a message is received, triggers the FortiSOAR™ playbooks for automated creation of alerts and other predefined response actions.
Connector Version: 1.0.0
FortiSOAR™ Version Tested on: 4.9.0.0-708 and later
Authored By: Fortinet
Certified: Yes
All connectors provided by FortiSOAR™ are delivered using a FortiSOAR™ repository. Therefore, you must set up your FortiSOAR™ repository and use the yum command to install connectors:
yum install cyops-connector-syslog
syslog rpm has a dependency on lsof package. If you are installing the rpm offline, you must install the lsof rpm prior configuring the syslog connector on the CyOps instance.In FortiSOAR™, on the Connectors page, select the Syslog connector and click Configure to configure the following parameters:
| Parameter | Description |
|---|---|
| Listener Protocol | Protocol of the listener protocol. Specify either TCP or UDP. |
| Listener Port | Port on which the listener starts. Since the listener is started as a non-root user, ensure that you provide a port higher than 1024. |
| CyberSponse Endpoint (/api/triggers/1/ will be prepended) | API Trigger URL for the playbook to be triggered when a Syslog message is received. |
| CyberSponse Username | Username required for authentication to forward the Syslog message to FortiSOAR™. |
| CyberSponse Password | Password required for authentication to forward the Syslog message to FortiSOAR™. |
The following automated operations can be included in playbooks:
Note: You can also restart listeners for all configurations by Deactivating and Activating the connector on the Connectors page in FortiSOAR™ (Automation > Connectors).
| Parameter | Description |
|---|---|
| Message Format | Specify whether the message to be parsed is in the RFC 3164 or RFC 5424 format. |
Note: The message complying to both the RFC 3164 or RFC 5424 specifications can be parsed.
This function parses the Syslog message and returns a JSON with the message fields.
Following image displays a sample output, when the message format is RFC 3164 :
Following image displays a sample output, when the message format is RFC 5424 :
None.
Use this function to start the listener for a given configuration. Note that the listener for a configuration is started by default as soon as the configuration is added, or if connector is activated.
The JSON output contains the status code and a message.
Following image displays a sample output:
None.
Use this function to stop the listener for a given configuration. Note that the listener for a configuration is started by default as soon as the configuration is deleted, or if connector is deactivated.
The JSON output contains the status code and a message.
Following image displays a sample output:
None.
Use this function to restart the listener for a given configuration.
The JSON output contains the status code and a message.
Following image displays a sample output:
The Sample - Syslog - 1.0.0 playbook collection comes bundled with the Syslog connector. This playbook contains steps using which you can perform all supported actions. You can see the bundled playbooks in the Automation > Playbooks section in FortiSOAR™ after importing the Syslog connector.
Note: If you are planning to use any of the sample playbooks in your environment, ensure that you clone those playbooks and move them to a different collection, since the sample playbook collection gets deleted during connector upgrade and delete.
This could be due to one of the following reasons:
The listener logs are written to /var/opt/cyops-integrations/syslog/listener.log. Check this log file for the exact reason for the failure.
This happens because listeners are not configured to come up automatically after a service restart. You must Deactivate and Activate the connector to start all listeners again.