Configuring IPsec or GRE tunnels on FortiOS
In this case, you will configure either IPsec tunnels or GRE tunnels, and not both.
To configure an IPsec tunnel:
- Go to VPN > IPsec Wizard. The VPN Creation Wizard displays.
- Enter a Name for the tunnel and select the Template type to be Custom.
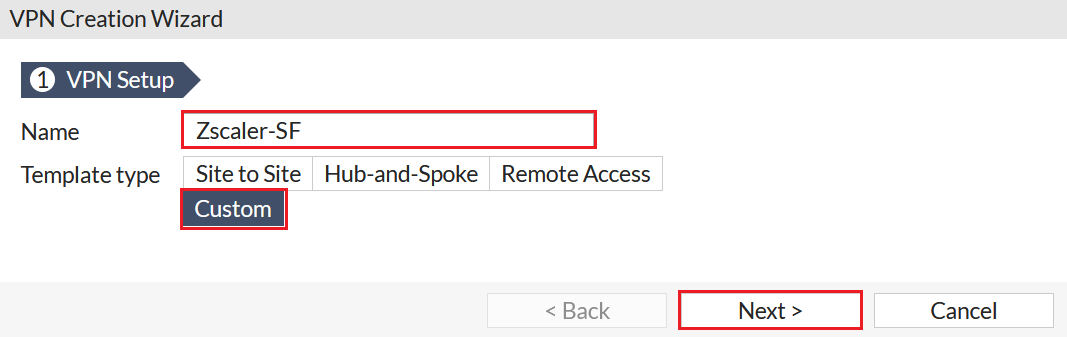
- Click Next. The New VPN Tunnel settings are displayed.
- Configure the Network settings as indicated in the table below. The Dynamic DNS field should be the Zscaler ZEN hostname that you will use.
IP Version
IPv4Remote Gateway
Dynamic DNSDynamic DNS
<Zscaler SF Host>Interface
Internet_A(port1)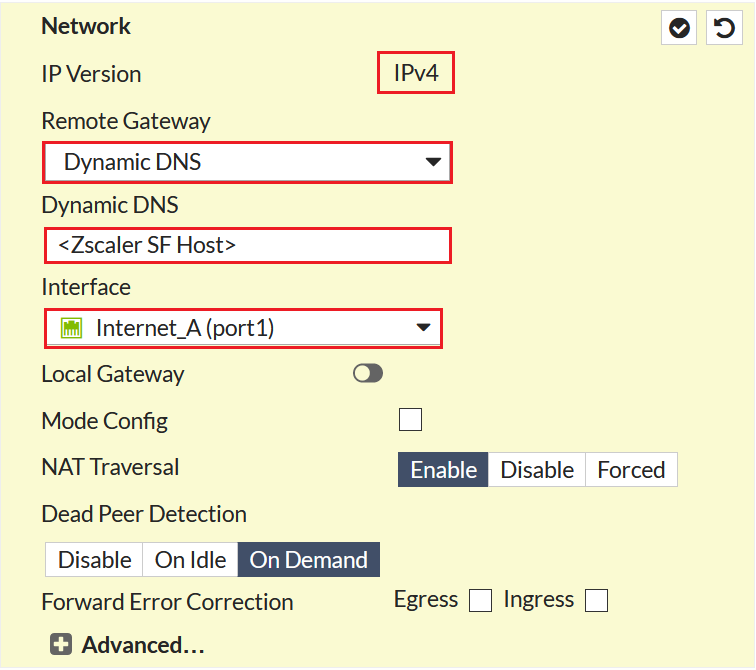
- Configure the Authentication settings with the Method to be Pre-shared Key and entering the pre-shared key (PSK). The PSK should be unique per site, and the IKE Version should be selected to be
2.
- Configure the Phase 1 Proposal settings as indicated in the table below. The Local ID field should be set to the FQDN you configured in the previous steps.
Encryption
AES256Authentication
SHA1Diffie-Hellman Group
2Key Lifetime (seconds)
86400Local ID
<Zscaler SF Host>
- Configure the Phase 2 Selectors settings as indicated in table below. Leave all other settings to their default values.
Local Address (Subnet)
0.0.0.0/0.0.0.0Remote Address (Subnet)
0.0.0.0/0.0.0.0Encryption
NULLAuthentication
MD5Enable Perfect Forward Secrecy (PFS)
Unchecked.
Key Lifetime (Seconds)
28800
- Click OK.
Similarly, configure another IPsec tunnel Zscaler-DC over the Internet_B(port2) interface.
Verify your IPsec tunnels by navigating to VPN > IPsec tunnels from the tree menu on the left side of the FortiGate GUI.
|
|
You may configure GRE tunnels, though Fortinet recommends configuring IPsec tunnels. |
To configure a GRE tunnel from the CLI:
- Create a GRE tunnel and add it as an interface:
config system gre-tunnel
edit "Zscaler-SF"
set interface "port1"
set remote-gw <Zscaler SF Host>
set local-gw <Internet_A>
next
end
- Configure the GRE tunnel interfaces:
config system interface
edit "Zscaler-SF"
set ip <ip address in a /30 subnet provided by Zscaler> 255.255.255.255
set allowaccess ping
set type tunnel
set interface "port1"
next
end
Similarly, configure another GRE tunnel Zscaler-DC over the Internet_B(port2) interface.

